Contents
SSO Connector for Bitbucket and Crowd
The miniOrange Crowd SSO connector expands the SAML SSO functionality from Crowd to its connected Atlassian applications.The Bitbucket Crowd SSO Connector allows users to enable SAML Authentication from any SAML compliant Identity Provider(IDP), where SAML SSO requests and responses to and from IDP will pass via the Crowd server. The IDP will perform user authentication while user permissions can still be controlled using Crowd.
You can refer the steps to configure Crowd connector from the video or documentation given below
Download And Installation
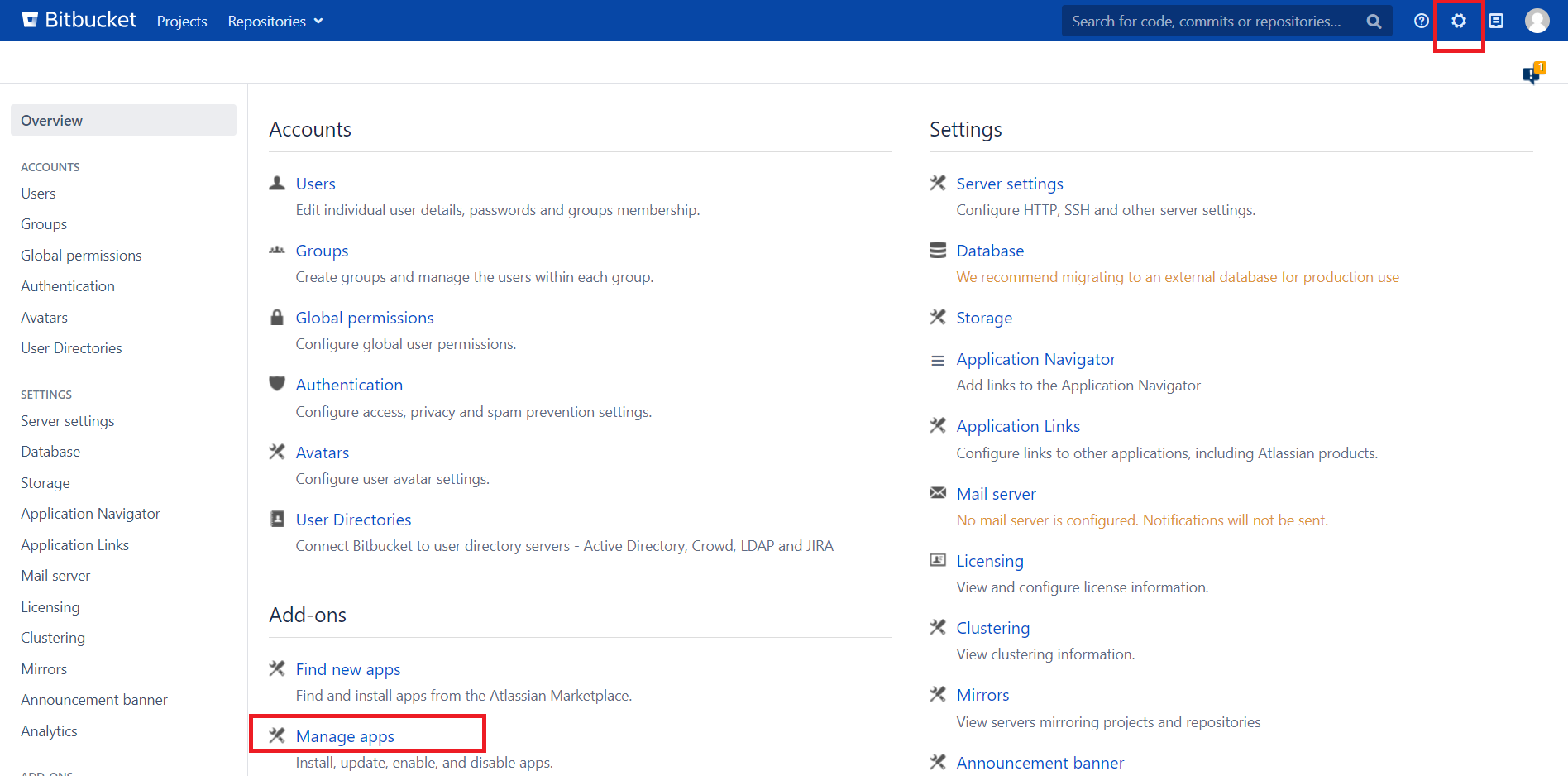
- Log into your Bitbucket instance as an admin.
- Navigate to the settings menu and Click Manage Apps.
- Click Find new apps or Find new add-ons from the left-hand side of the page.
- Locate SSO connector for Crowd and Bitbucket via search.
- Click Try free to begin a new trial or Buy now to purchase a license of SSO connector for Crowd and Bitbucket.
- Enter your information and click Generate license when redirected to MyAtlassian.
- Click Apply license.
Plugin Configuration
- To configure the plugin, firstly configure Crowd SAML Single Sign-On (SSO) plugin for your Identity Provider as mentioned in the steps.
- Now, Enable Crowd SSO for your Bitbucket instance.
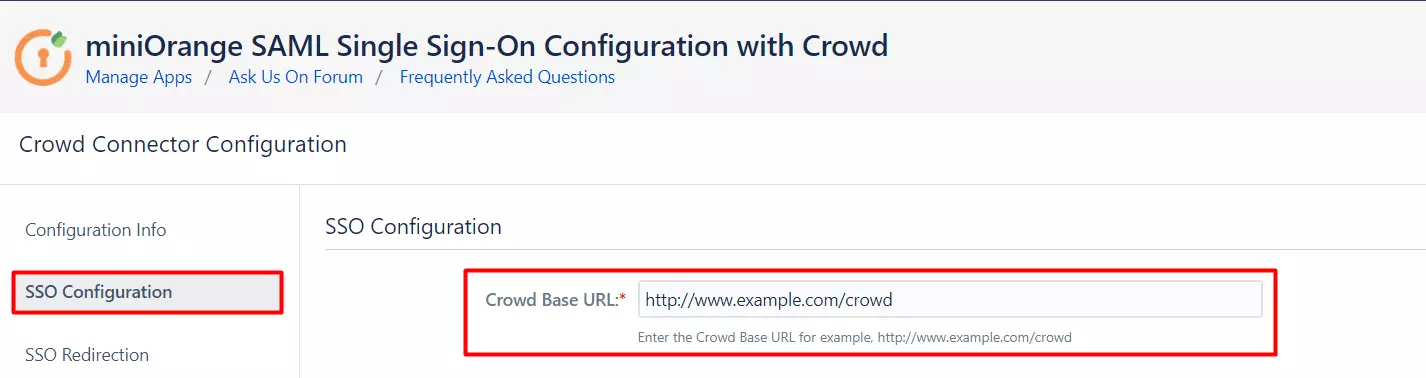
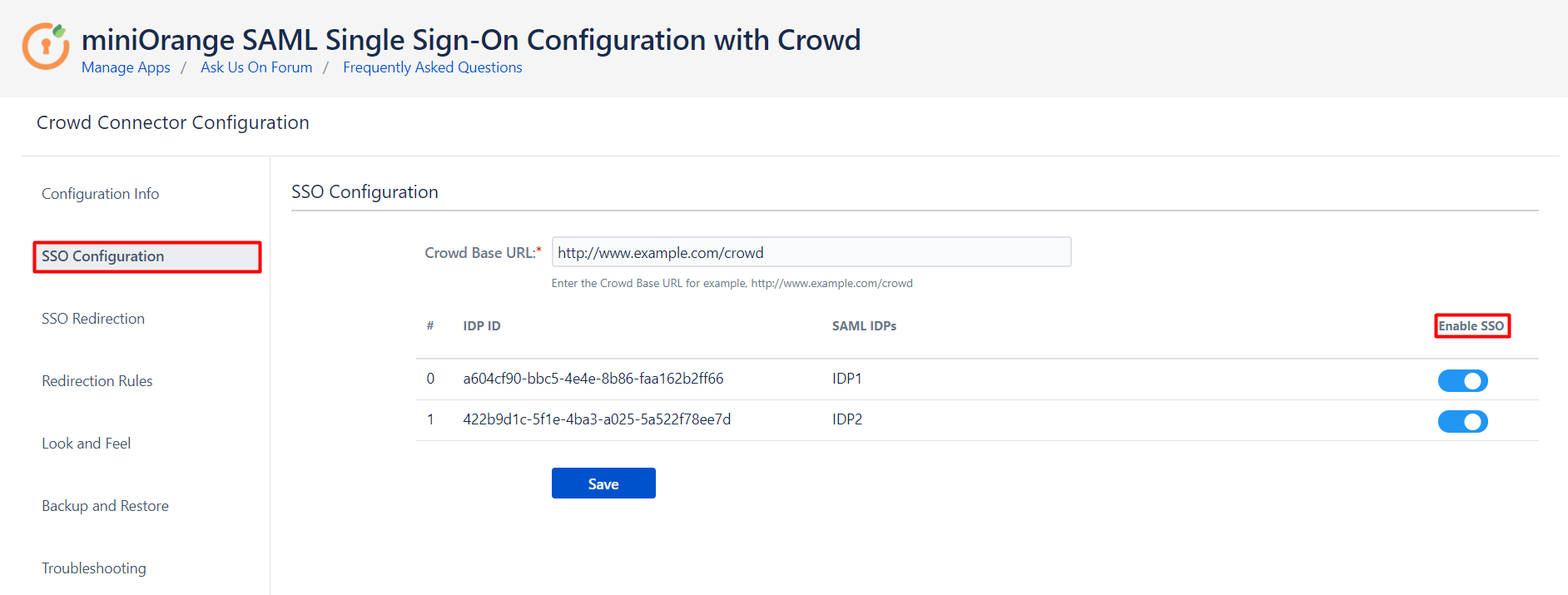
- Go to SSO Configuration tab of Bitbucket-Crowd Connector plugin.
- Enter Crowd Base URL and click on Save.
- Now, all the IdPs are listed that you have configured with SAML SSO Crowd plugin.
- The Enable SSO button is provided for every individual IdP. You can enable SSO for specific IdPs with the help of the buttons.
Single sign-on (SSO) with Crowd
Once the Crowd directory has been set up, you can enable Crowd SSO integration by adding the following
setting to shared/bitbucket.properties in the home directory (create this file if it
doesn't exist yet):
# Whether SSO support should be enabled or not. Regardless of this setting SSO authentication
# will only be activated when a Crowd directory is configured in Bitbucket that is configured
# for SSO.
plugin.auth-crowd.sso.enabled=truePlease note that you will need to correctly set up the domains of the applications involved in SSO.
SSO Redirection
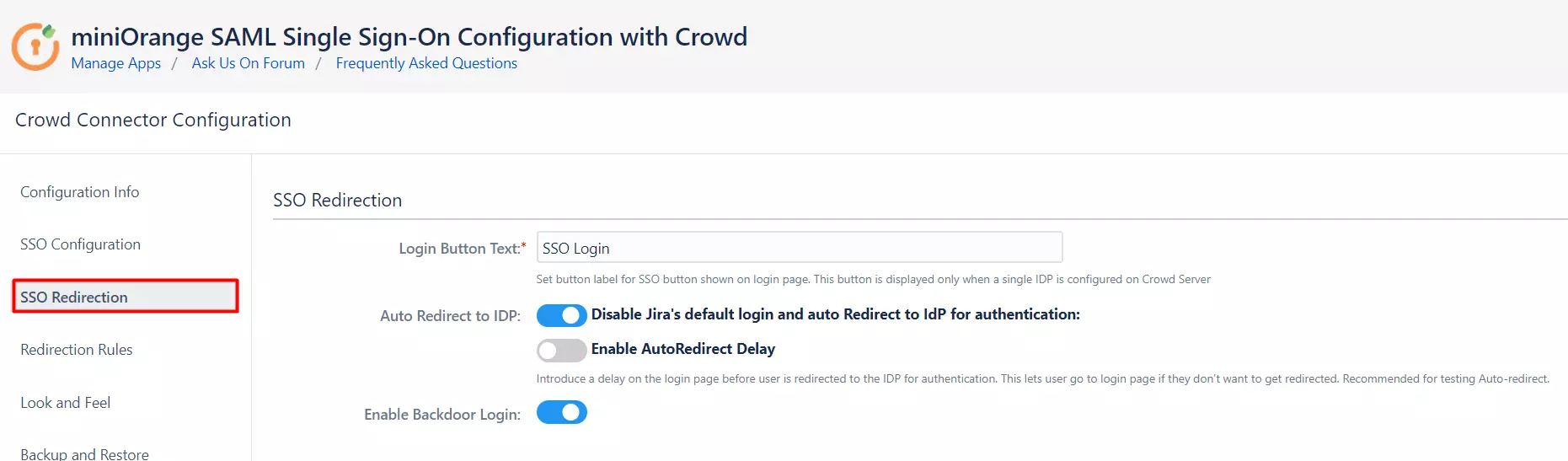
- If you have only one IDP configured, then you can use the features provided on the SSO Redirection tab and Redirection Rules tab of the plugin to manage the redirection on the login page.
- Enable the Auto Redirect to IDP option on the SSO Redirection tab if you want to allow users to log in only using IDP.
- Use the Emergency/Backdoor Login URL to allow all admins to access the Bitbucket default login page and log in using Crowd credentials.
- Use the settings given on Redirection Rules tab to redirect the users on login page based on their email domains, groups and directories. This feature is more useful in case you have multiple IDPs configured. Please refer to the next section.
Managing SSO with multiple IDPs
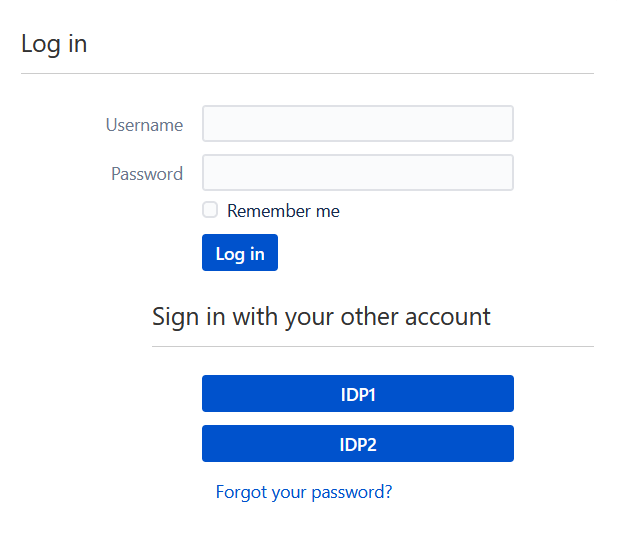
- If you have multiple IDPs configured, you can choose how you want your end users to use these IDPs to perform SSO.
- For example you can show the buttons for the different IDPs configured on the login page nad let the users decide which IDP to use for SSO.
- Or you could force certain users to use a specific IDP based on the domain of their username/email.
- You will be able to configure these rules in the Redirection Rules section, under the Redirection Rules tab.
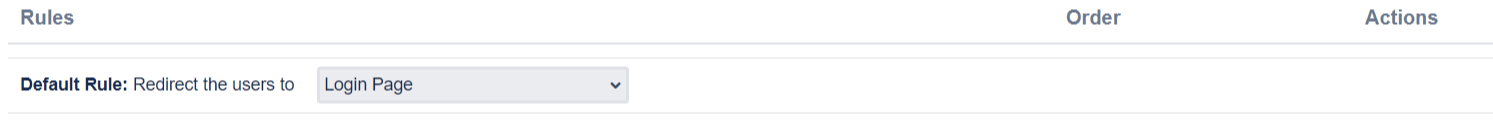
- By default one rule is always configured that will be applicable to all the users, irrespective of their user domains.
- For instance, if you want to display the login page with SSO buttons for each of the IDPs then your Default Rule will be as follows :
- Based on the default rule mentioned above, the login form will contain buttons for each IDP. The users will be free to choose whichever IDP they want to use to initiate SSO.
- You can also configure a rule so that your users will automatically be redirected to an IDP based on their email domains.
-
For example, if you want users with example.com as domain to be redirected to
IDP
1
you can add a rule by :
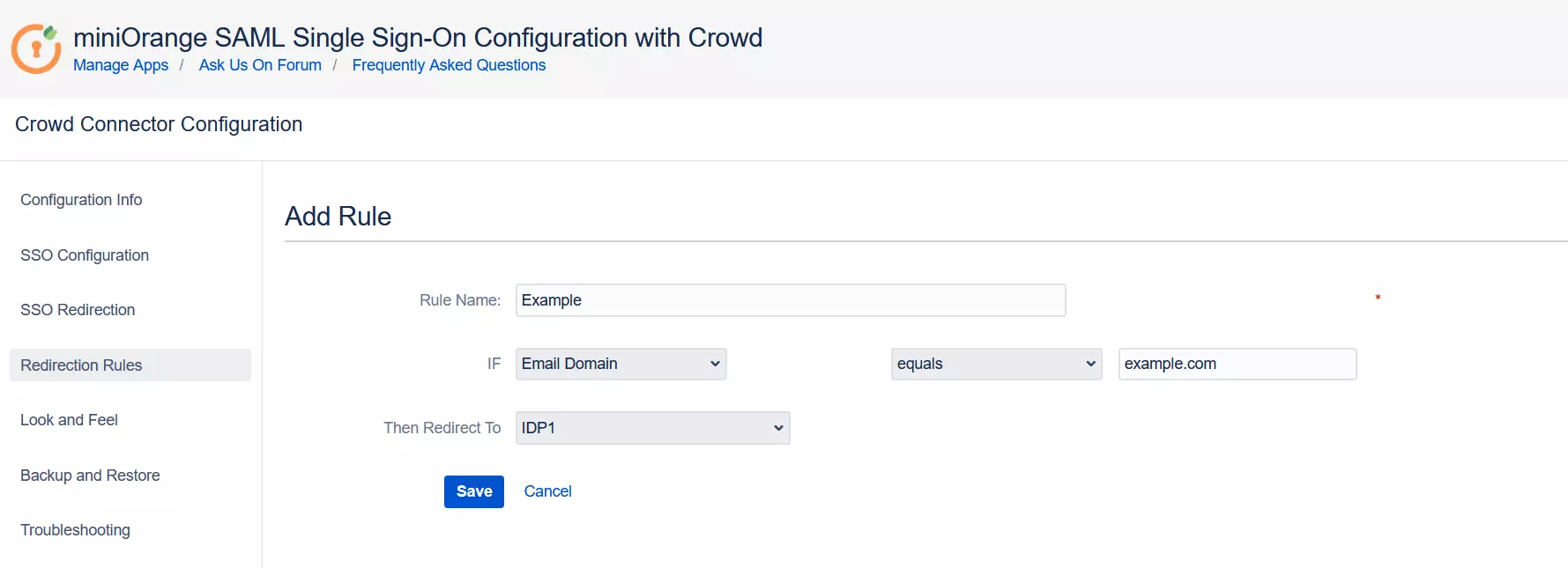
- Click on the Add Rule button in the Redirection Rules tab.
- Enter a name for your rule in Rule Name.
- In the IF statement select Email Domain in the first drop-down.
- For the same statement select equals in the second drop-down.
- In the last field of the IF statement, enter the email domain(example.com for the purpose of this example).
- In the Then Redirect To drop-down, select the IDP you want the users with example.com to be redirected to(IDP 1 in this case).
- Click on Save.
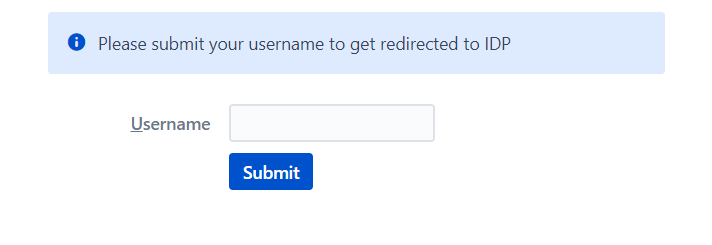
- When a rule such as an example given above is configured, a login form will be displayed to the users where they will have to input their email address.
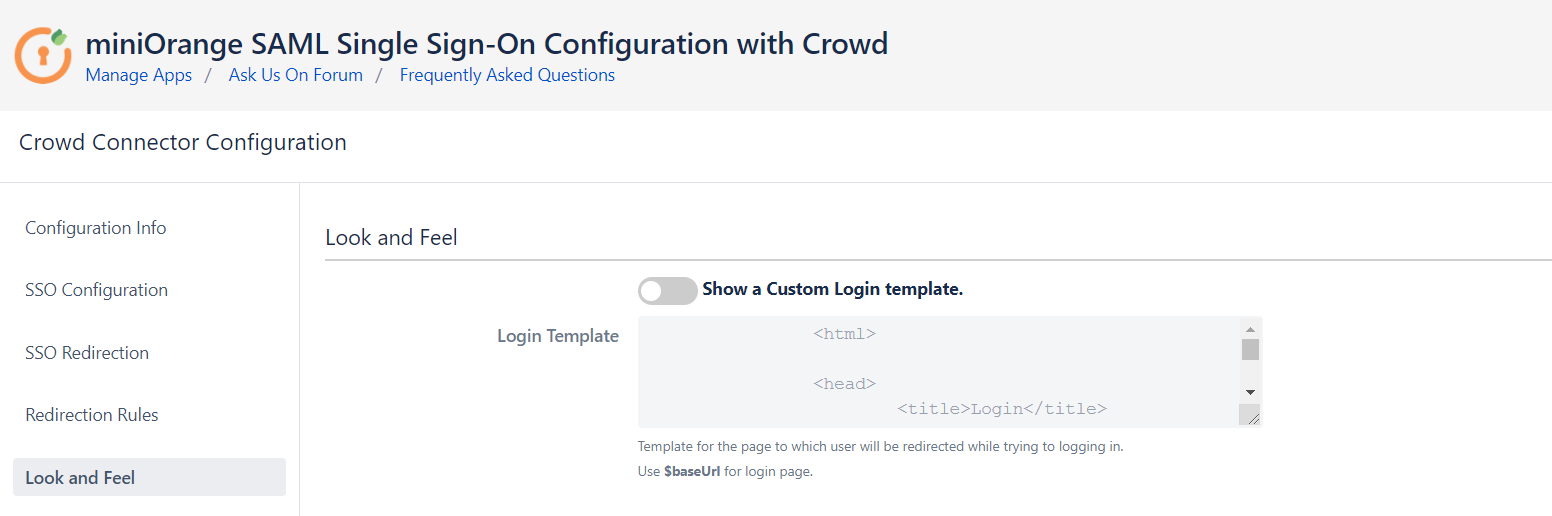
Customize your login page
- Go to the Look and Feel tab of the plugin.
- Here, you can design your own login template that will be used to initiate SSO. This will display your customized login page instead of application's default login page.
Crowd Troubleshooting
Recommended Add-Ons

Jira Crowd Connector
Crowd SAML & Connectors is the only SSO solution for Crowd SSO-enabled Atlassian apps.
Know More
Confluence Crowd Connector
Crowd SAML & Connectors is the only SSO solution for Crowd SSO-enabled Atlassian apps.
Know More
Bamboo Crowd Connector
Crowd SAML & Connectors is the only SSO solution for Crowd SSO-enabled Atlassian apps.
Know MoreBitbucket Git Authentication App | Kerberos/NTLM Apps | Word/PDF Exporter | WebAuthn | SonarQube SSO | Jenkins SSO
If you don't find what you are looking for, please contact us at support-atlassian@miniorange.atlassian.net or raise a support ticket here.
