SAML Single Sign On (SSO) into Jenkins using Centrify as IDP
Jenkins SAML SSO app gives the ability to enable SAML Single Sign-On (SSO) for Jenkins. Here we will go through a guide to configure Single Sign On (SSO) between Jenkins and Centrify. By the end of this guide, Centrify users should be able to log in and register to Jenkins.
Pre-requisites
To integrate your Identity Provider (IDP) with Jenkins, you need the following items:
- Jenkins should be installed and configured.
- Jenkins Server is https enabled (optional).
- Admin credentials are set up in Jenkins.
Download and Installation
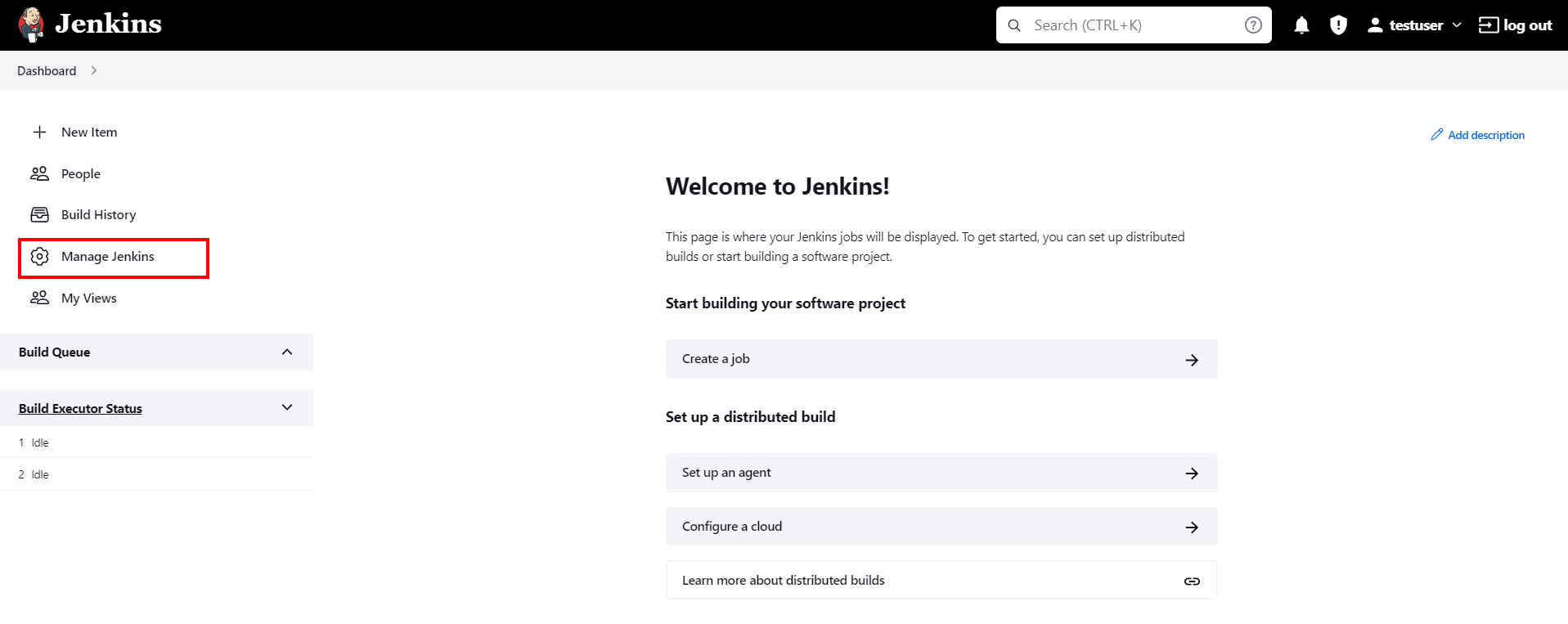
- Login to your Jenkins Admin Account.
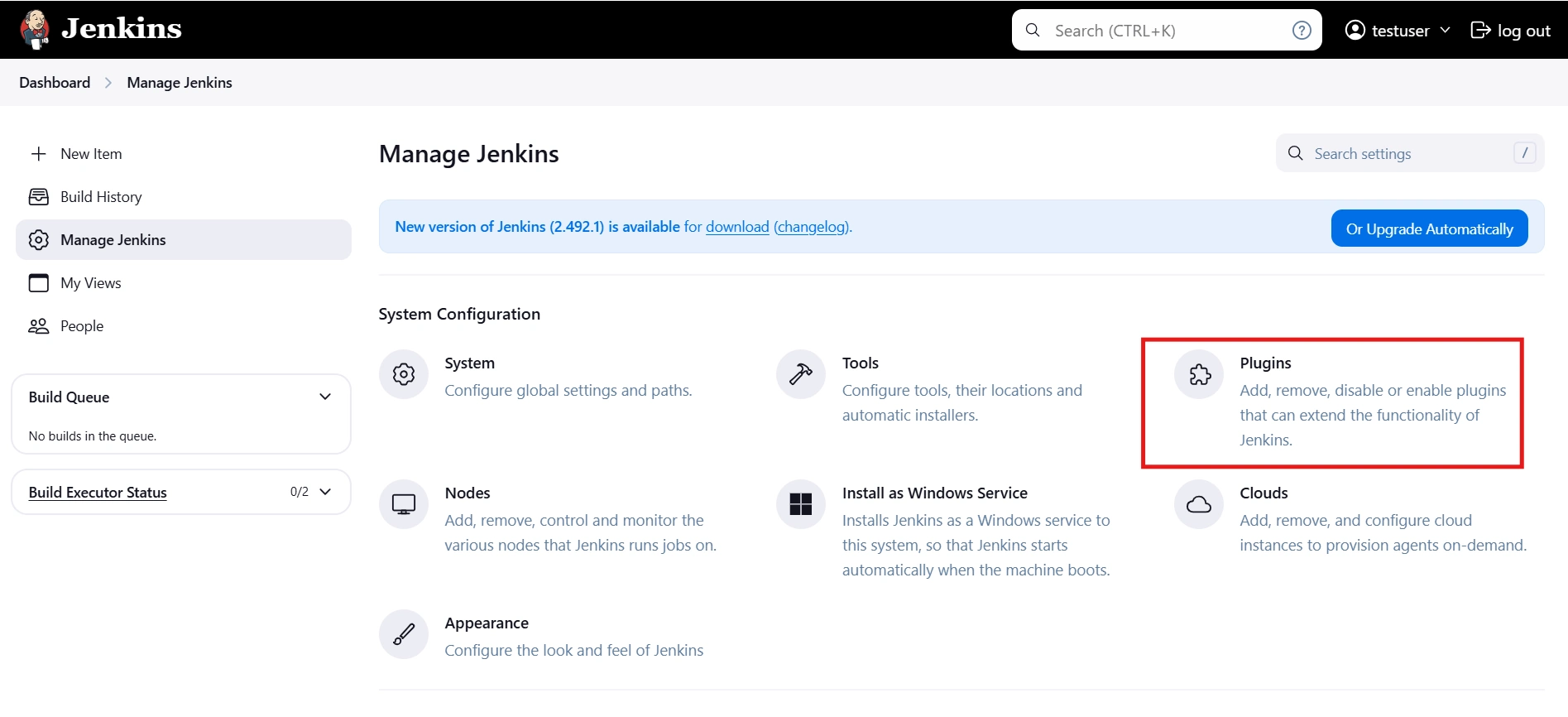
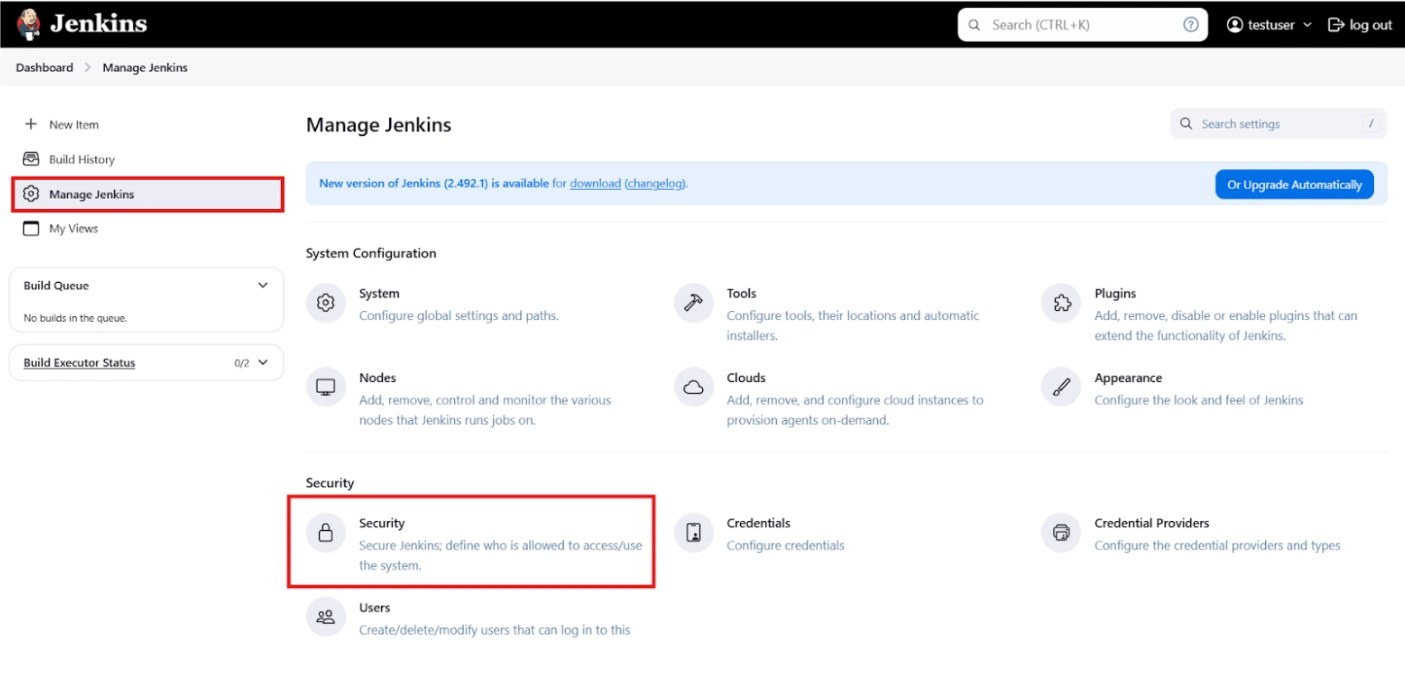
- Go to Manage Jenkins option from the left pane, and open Plugins tab.
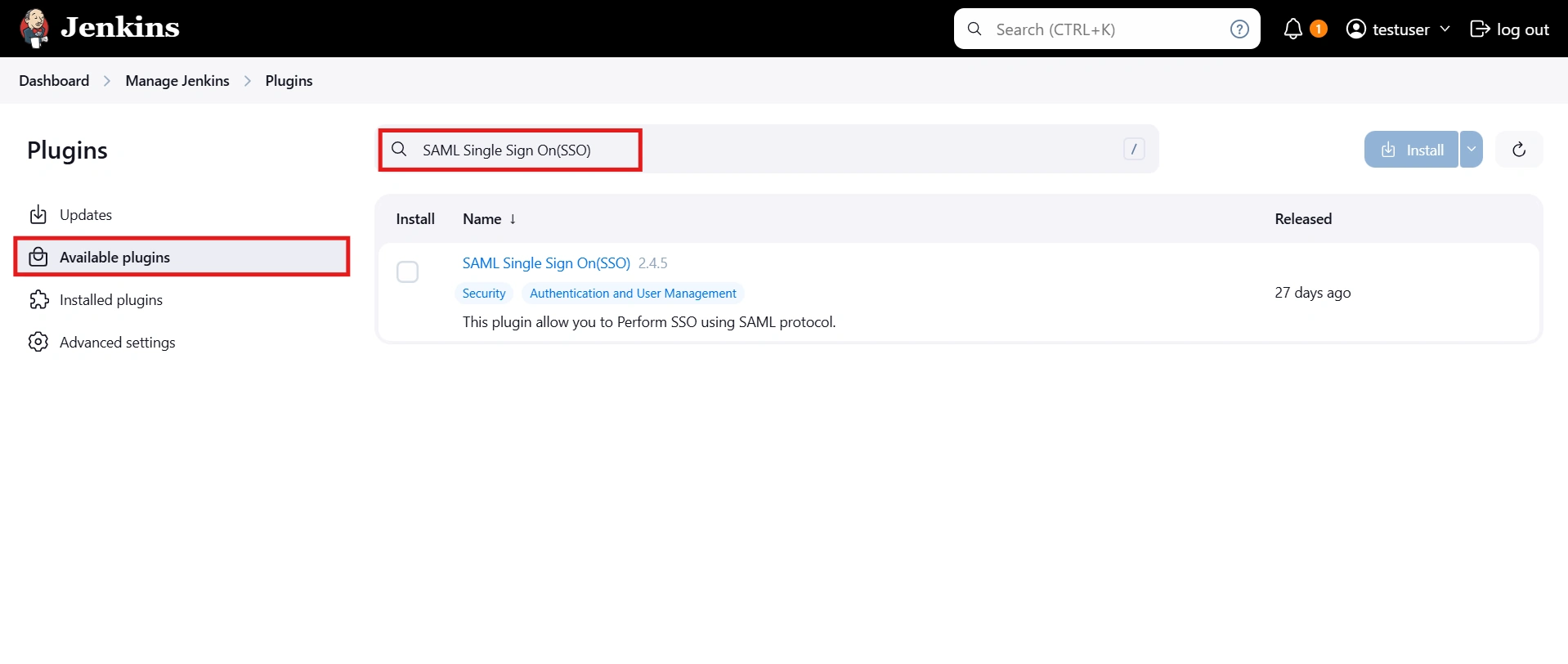
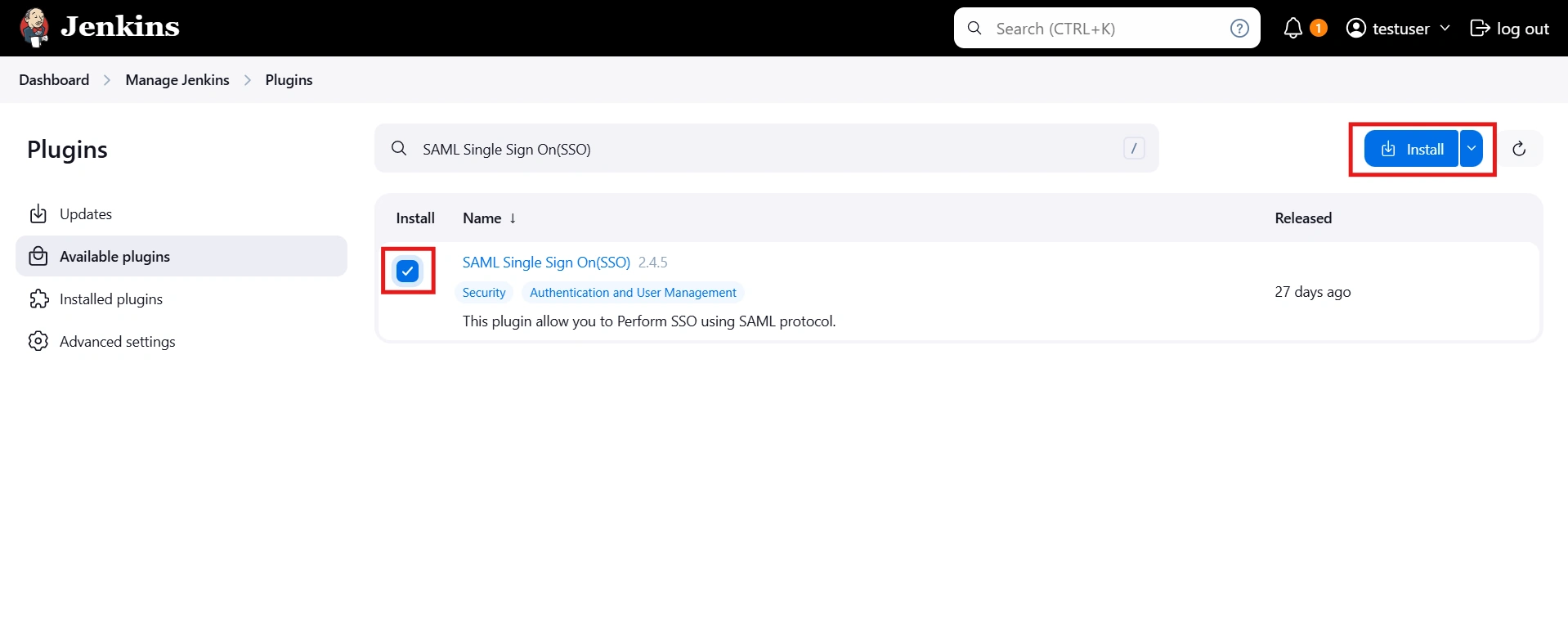
- Search for SAML Single Sign On (SSO) in the available plugins tab.
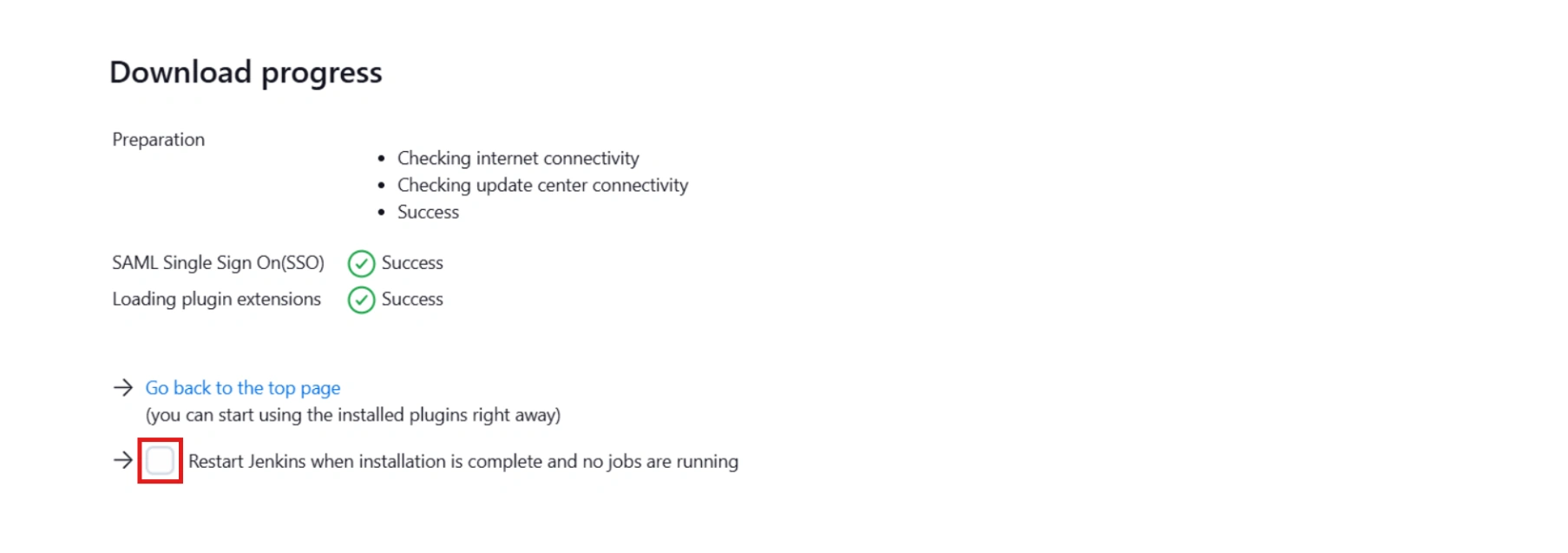
- Download and install with a restart.
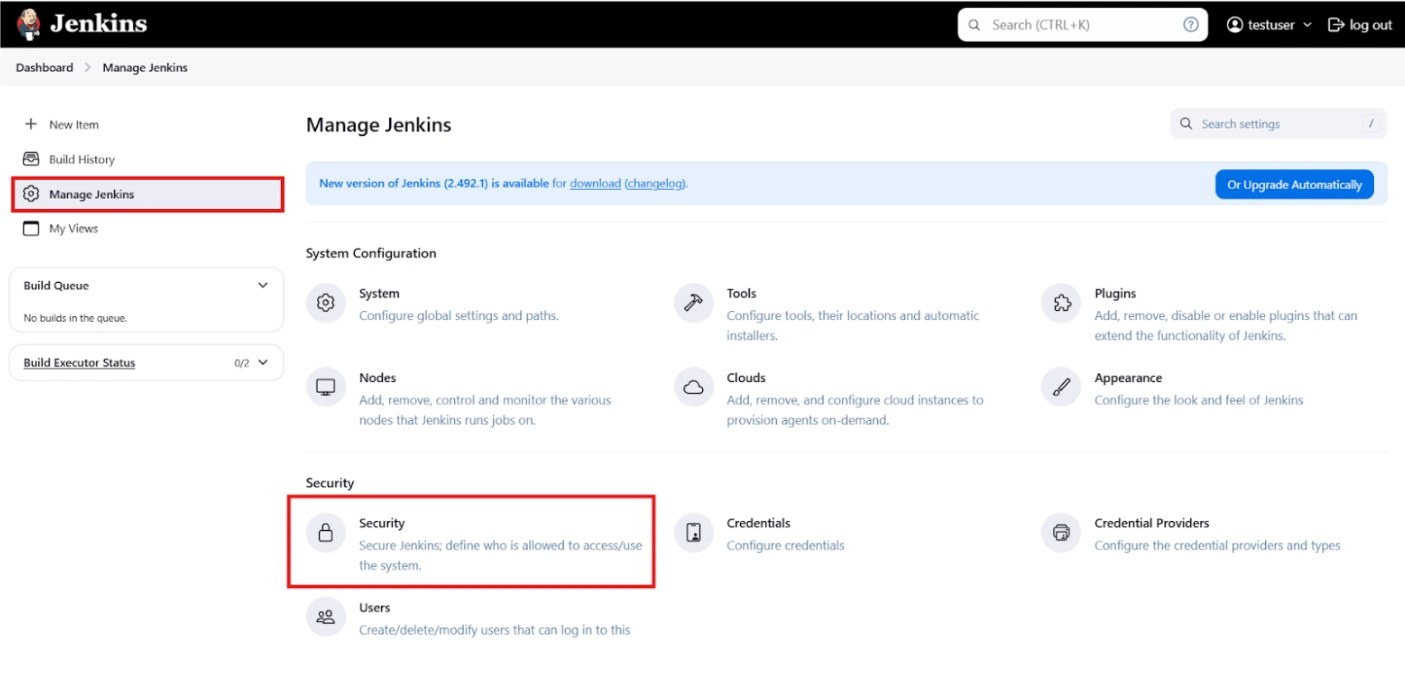
- After restarting Jenkins, navigate to Manage Jenkins and select Security.
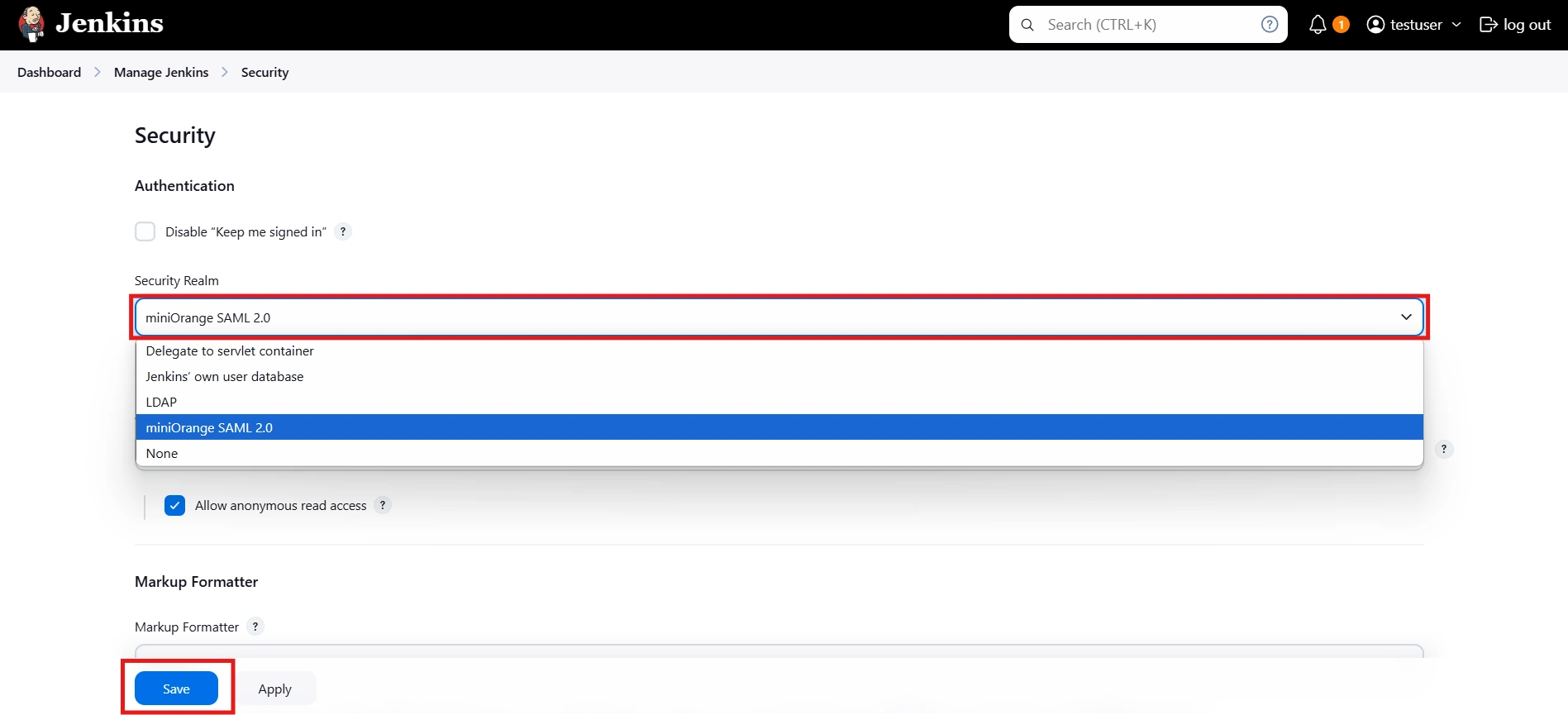
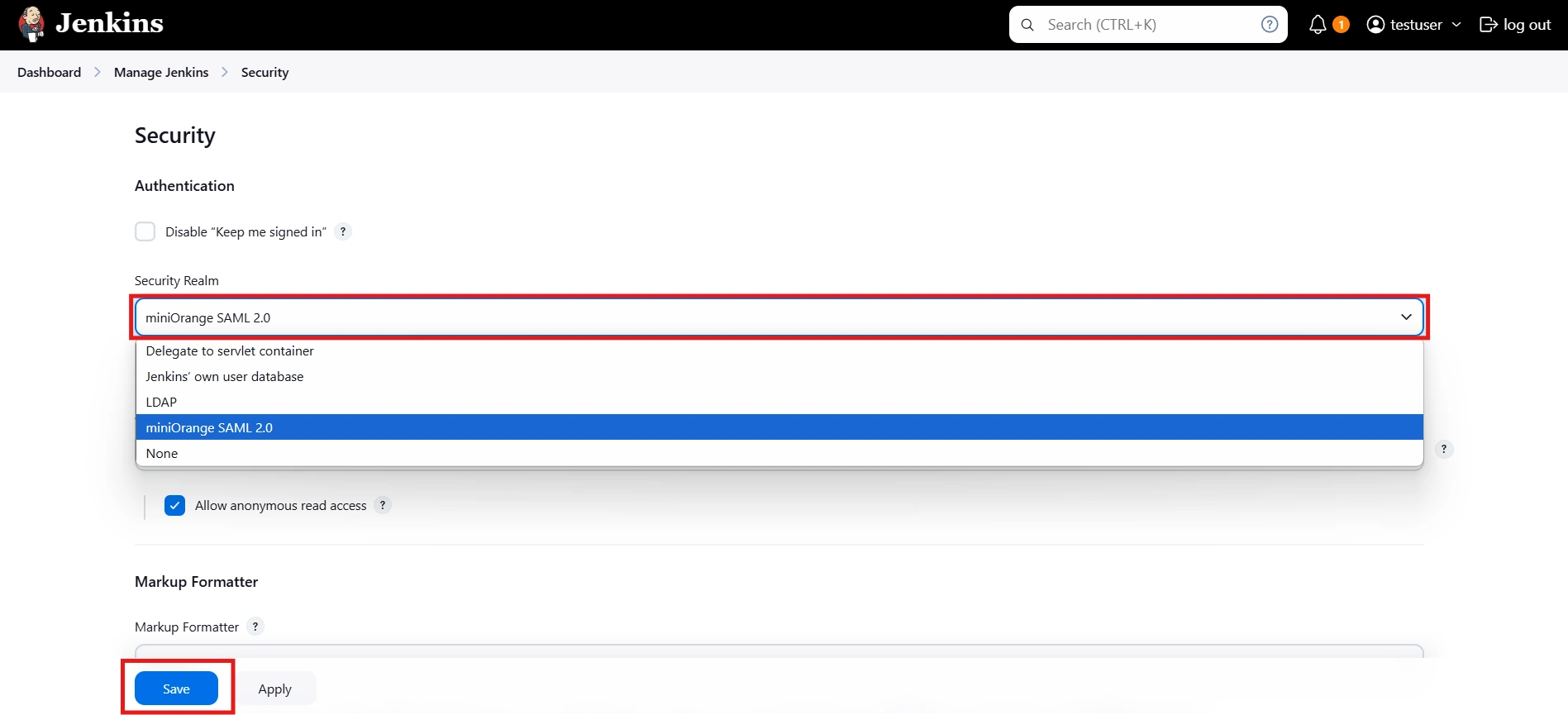
- Under the Security Realm dropdown, choose miniOrange SAML 2.0, then click the Save button.
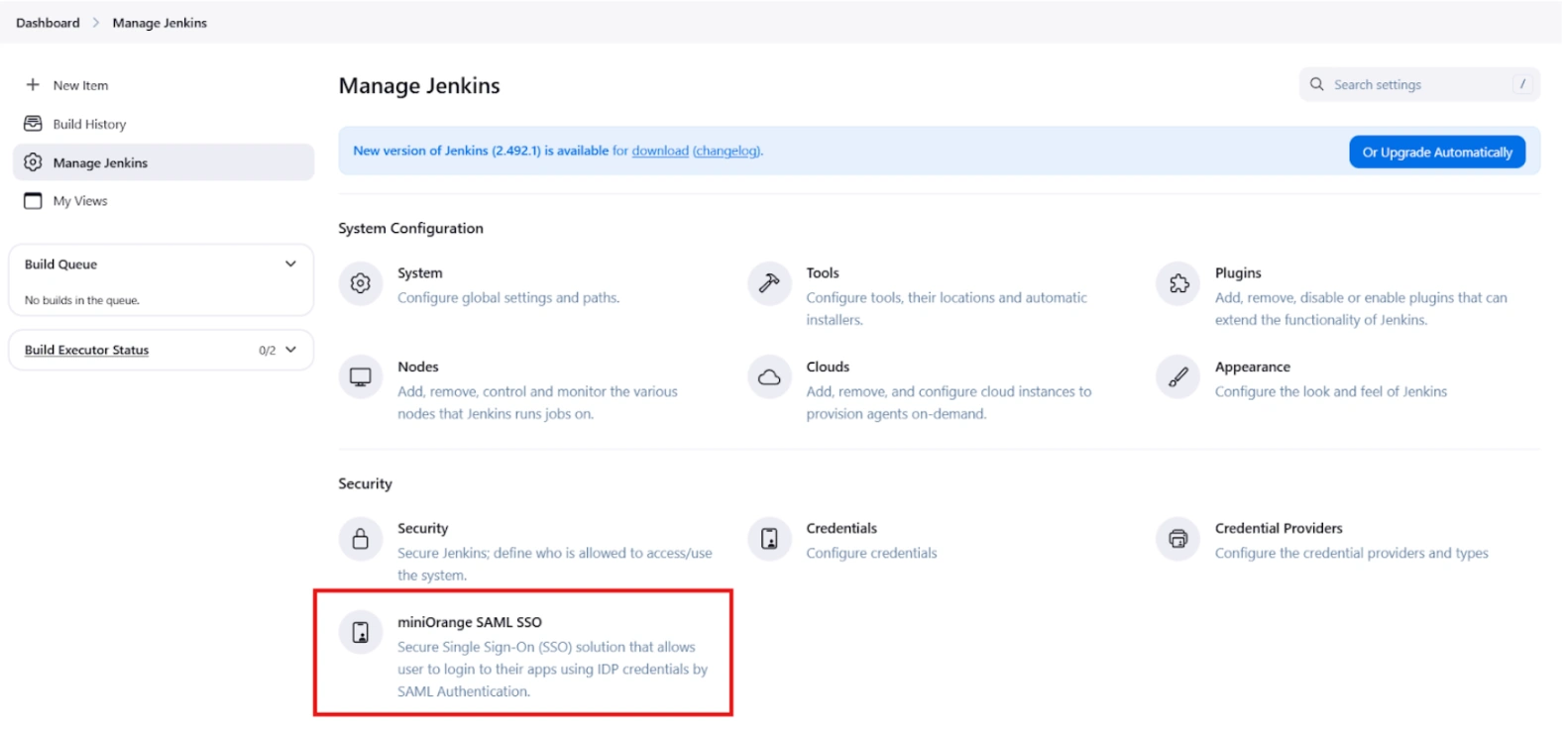
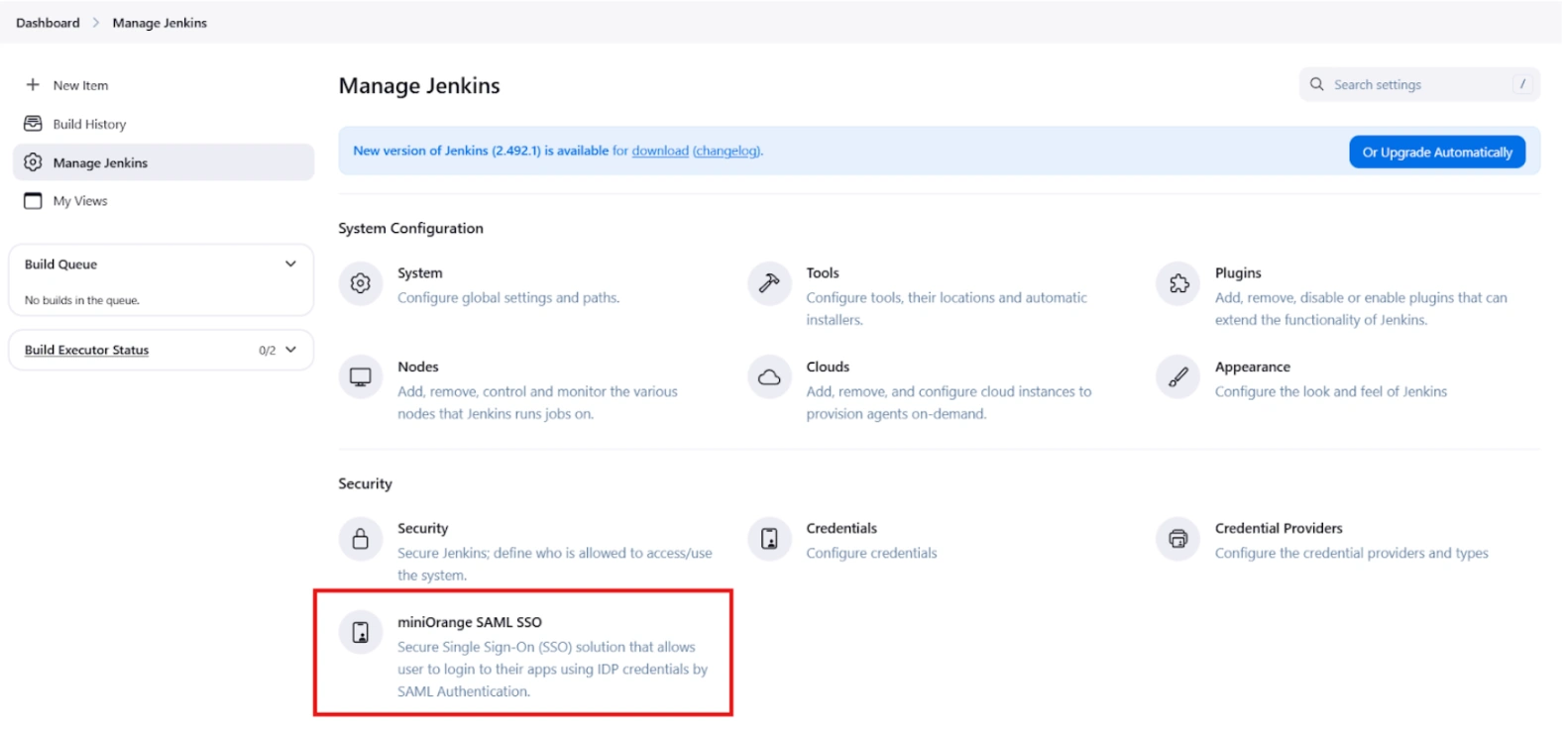
- Once saved, click on miniOrange SAML SSO under the Security section and go to the Plugin settings.
Step 1: Set Up Centrify as Identity Provider
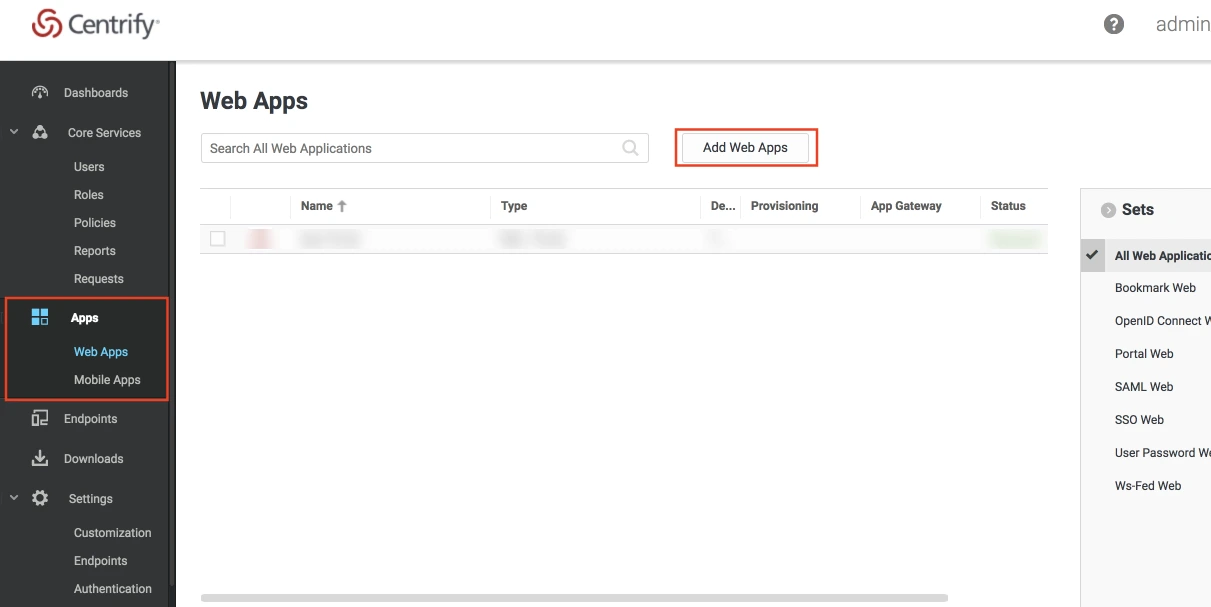
- Log into Centrify as an Administrator and click on Apps on the sidebar. Then Click on Web Apps.
- Click on the Add Web Apps button next to the search bar.
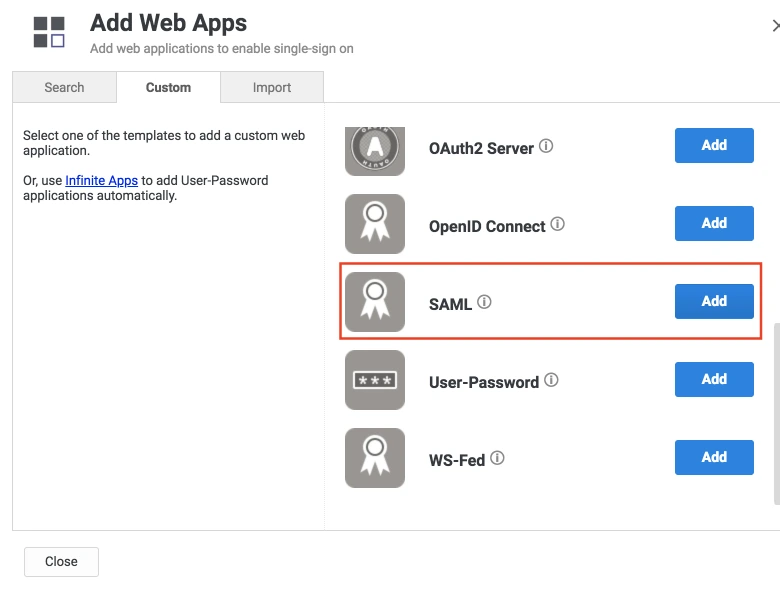
- Then select the Custom tab. Search for SAML and click on the Add button. Now press Yes to confirm.
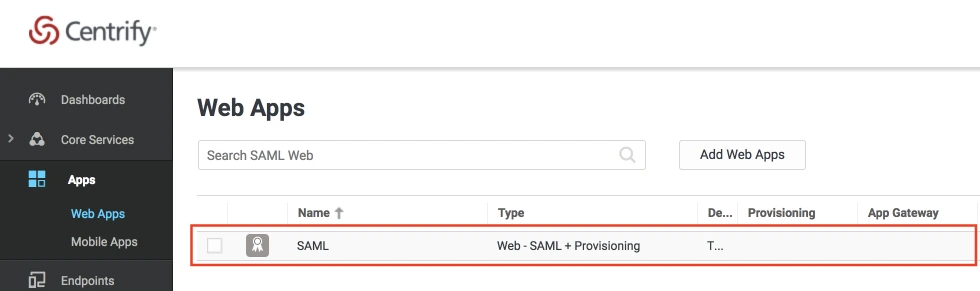
- When you create a web app, it will be listed in the Web Apps tab. Click on the newly created web app to configure.
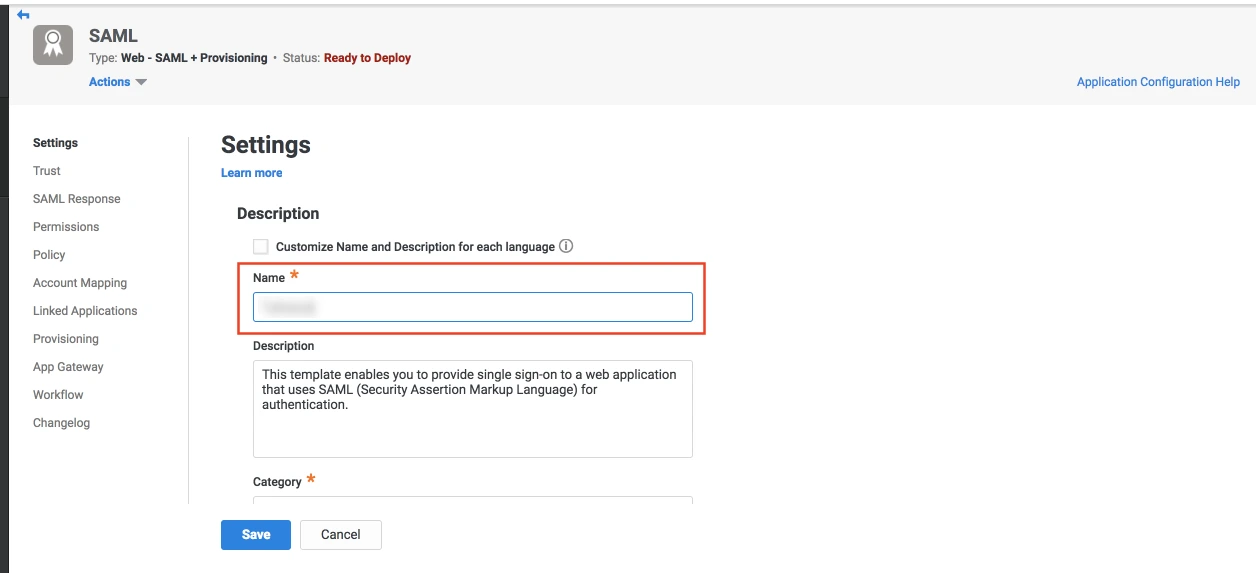
- The name and description of the web app can be updated from this settings tab.
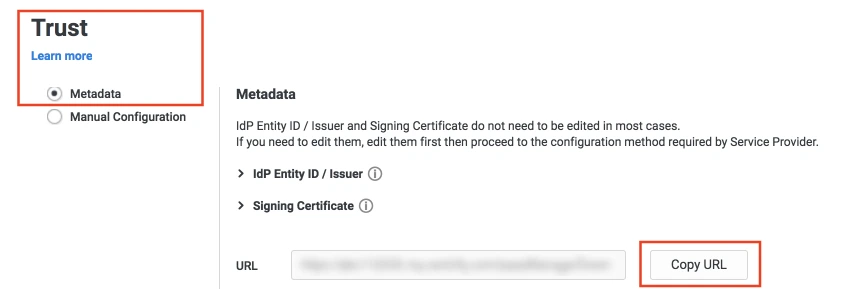
- Select the Trust tab from the sidebar. Trust tab will have metadata details for the configuration. Copy the metadata URL and save it for configuration with miniOrange.
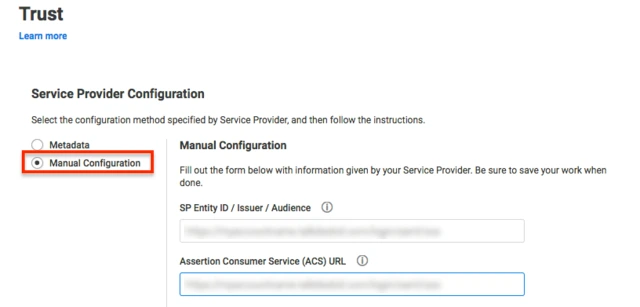
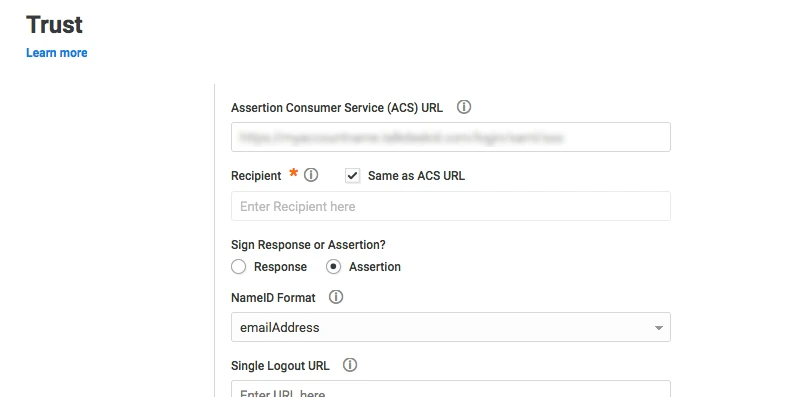
- Now scroll down until you see the Service Provider Configuration. Here you can configure the SP metadata either using the URL or manual configuration.
- Enter the configuration details and click on SAVE.
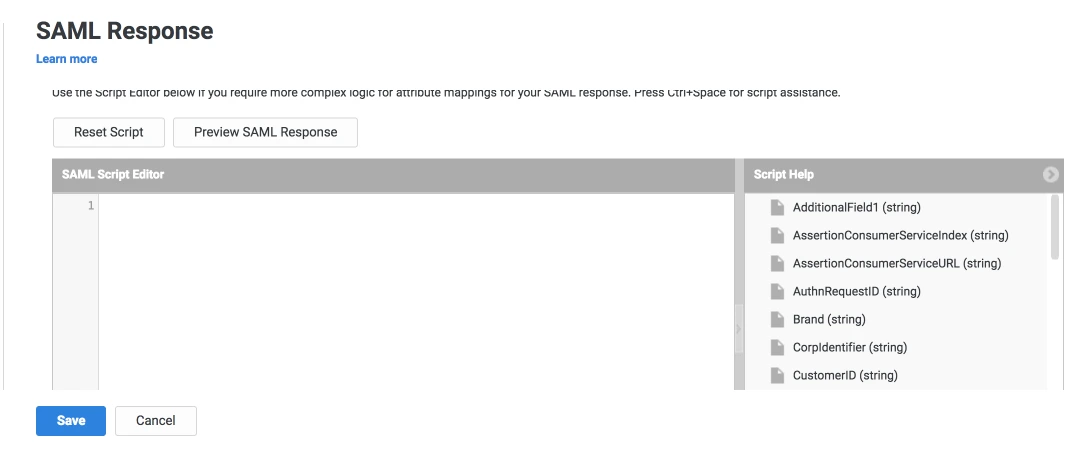
- Click on the SAML Response tab from the left sidebar.
- Here, you can map attributes from your source directory to SAML attributes that will be returned with the response.
- Also, Centrify provides a script editor under the custom logic section in the SAML Response tab to add more complex logic to map attributes.
- You will have to add below functions to the code -
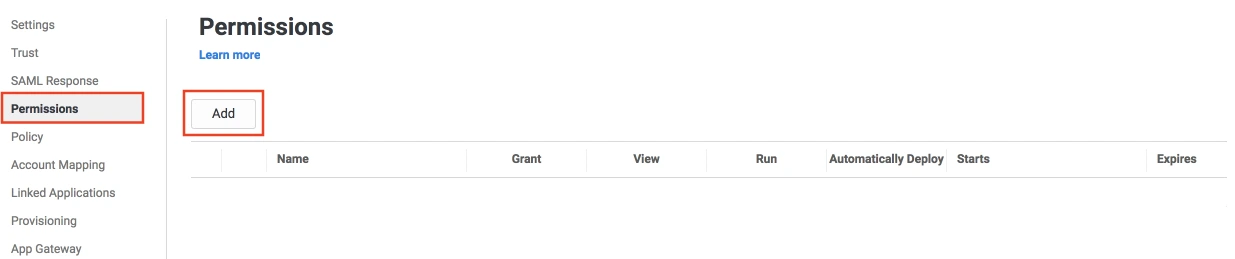
- From the left sidebar, select Permissions.
- Click on the Add button. The Select User, Group, or Role dialog will appear.
- Select the users, groups, or roles that will be accessing this web app. The role rules will be displayed on the User Access card.
- Click on the Save button.
 Create SAML App
Create SAML App
 Configure SAML App
Configure SAML App
| setAudience() | SP-EntityID / Issuer from Step 1 of the plugin under the SP Info Tab. E.g: setAudience('https://example.com') |
| setRecipient() | Recipient URL from Step 1 of the plugin under the SP Info Tab. E.g: setRecipient('https://example.com/plugins/servlet/saml/auth') |
| sethttpsDestination() | Destination URL from Step 1 of the plugin, under the SP Info Tab. E.g: sethttpsDestination('https://example.com/plugins/servlet/saml/auth') |
Step 2: Setup Jenkins as Service Provider
- Open Manage Jenkins and select Security.
- Under the Security Realm dropdown, choose miniOrange SAML 2.0, then click the Save button.
- Make sure that Enable Security checkbox is checked.
- Choose miniOrange SAML SSO from the manage Jenkins tab.
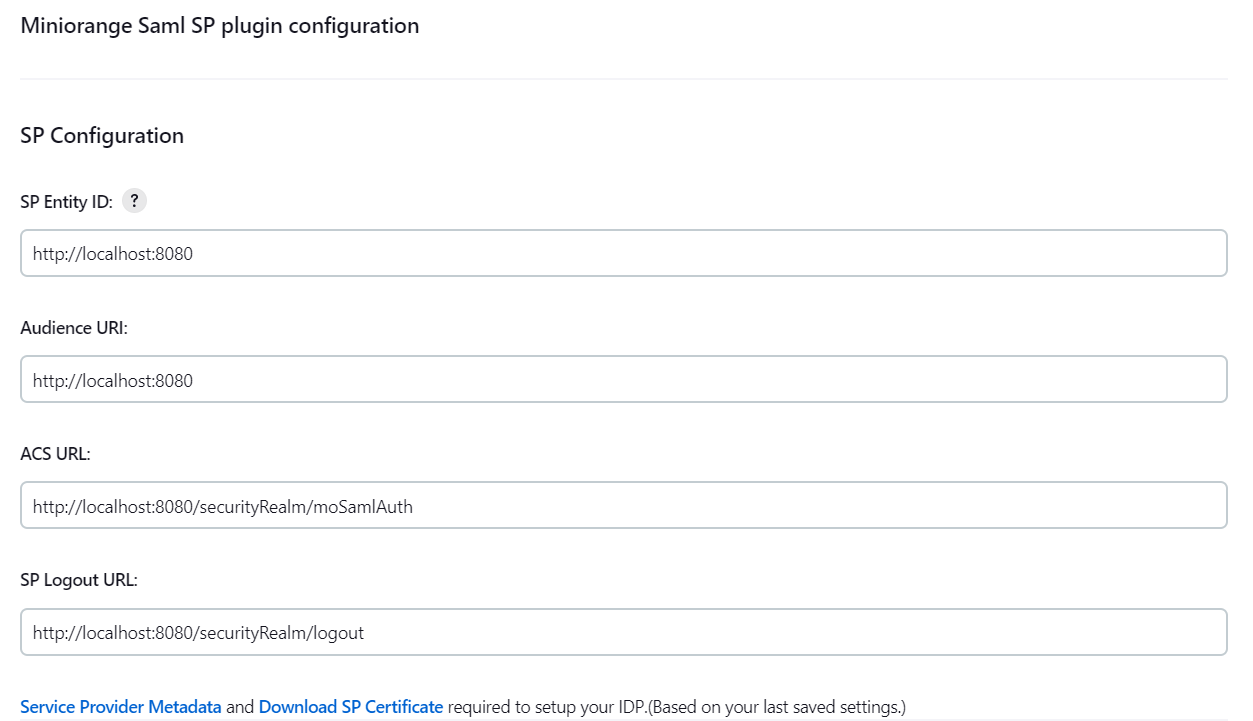
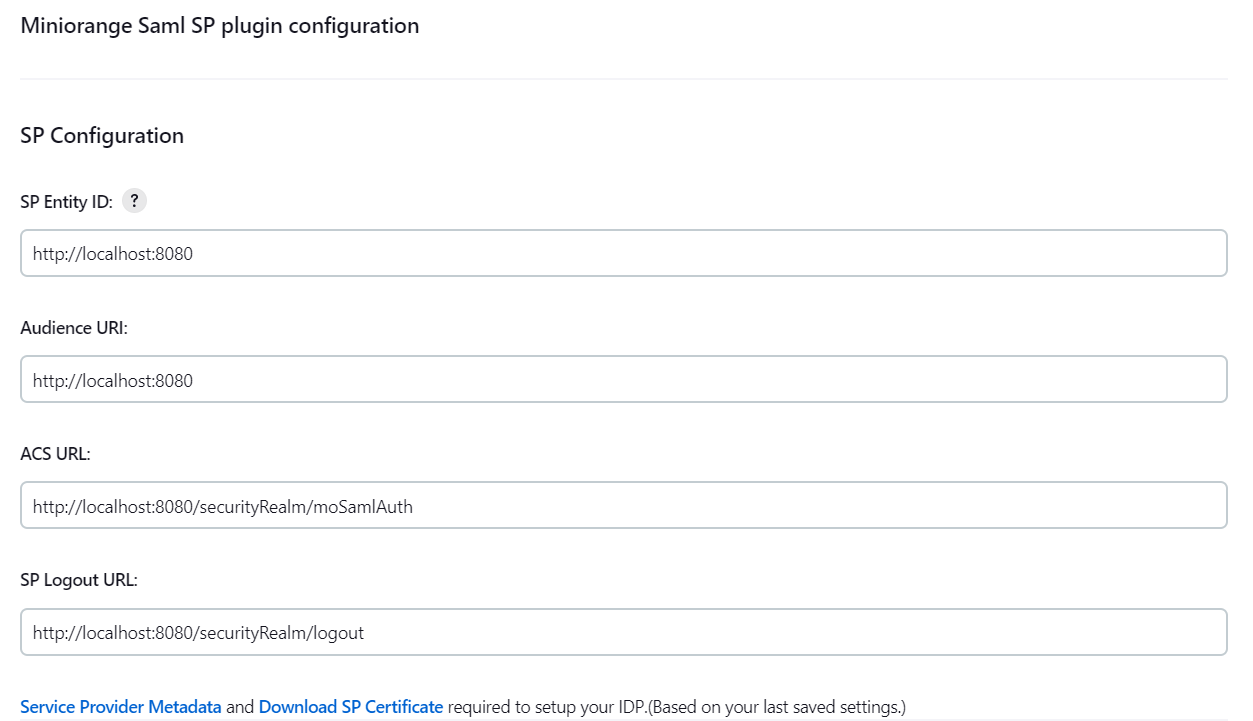
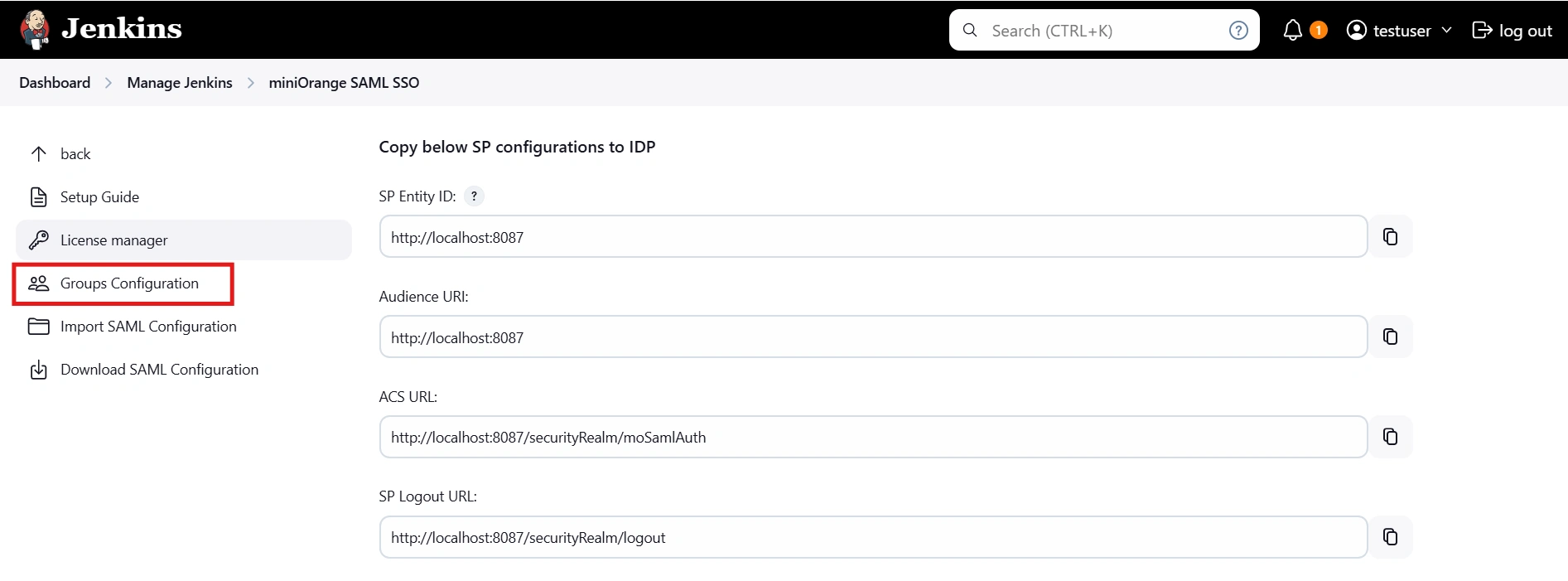
 SP Configurations
SP Configurations
You can configure SP settings in IDP in 2 ways:
- By uploading Metadata XML file
- Click on Service Provider Metadata in SP Configuration section.
- Metadata xml file will be downloaded.
- Use this file to setup IDP.
- Manual Configuration
- To Configure SP Settings at IDP copy below URL and paste in respective fields at IDP end.
- SP Entity ID: https://your-jenkins-domain
- Audience URI: https://your-jenkins-domain
- ACS URL: https://your-jenkins-domain/securityRealm/moSamlAuth
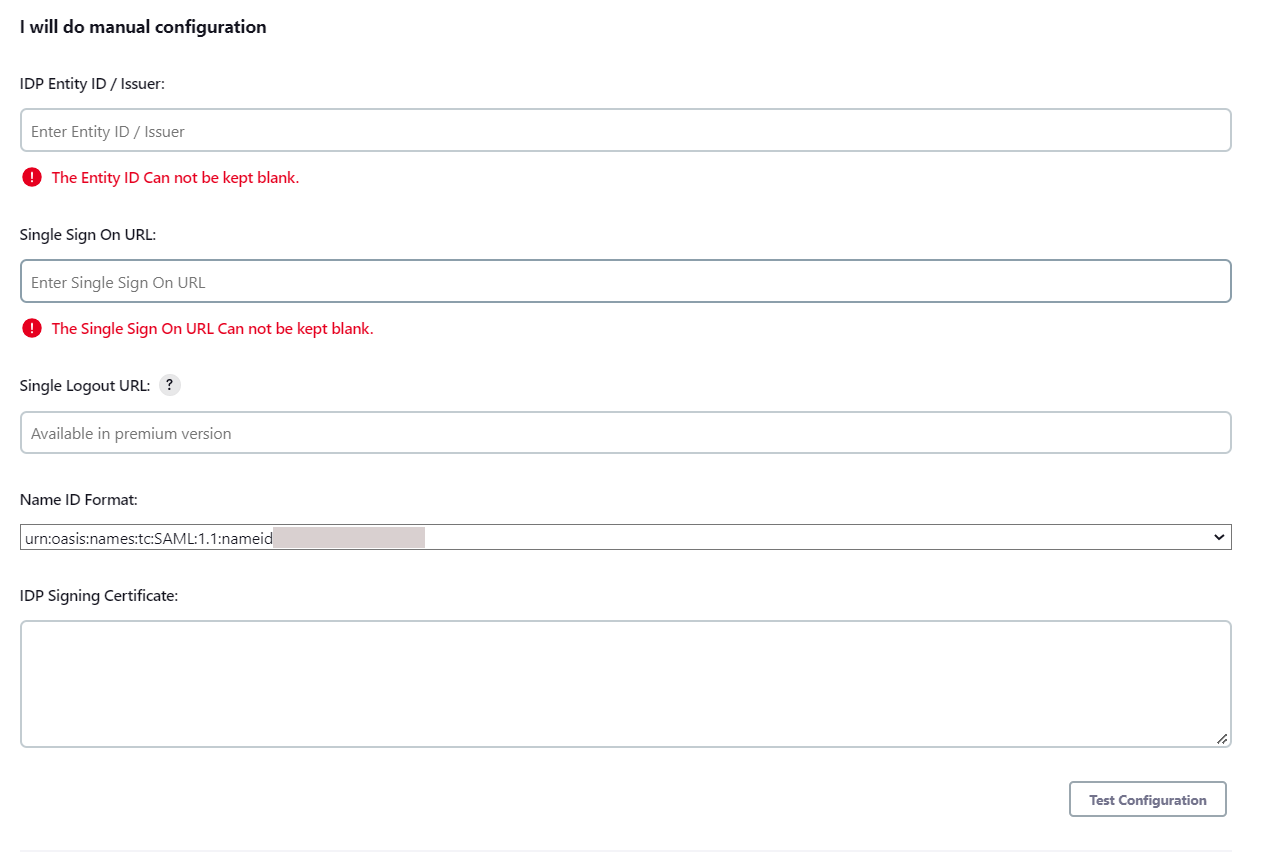
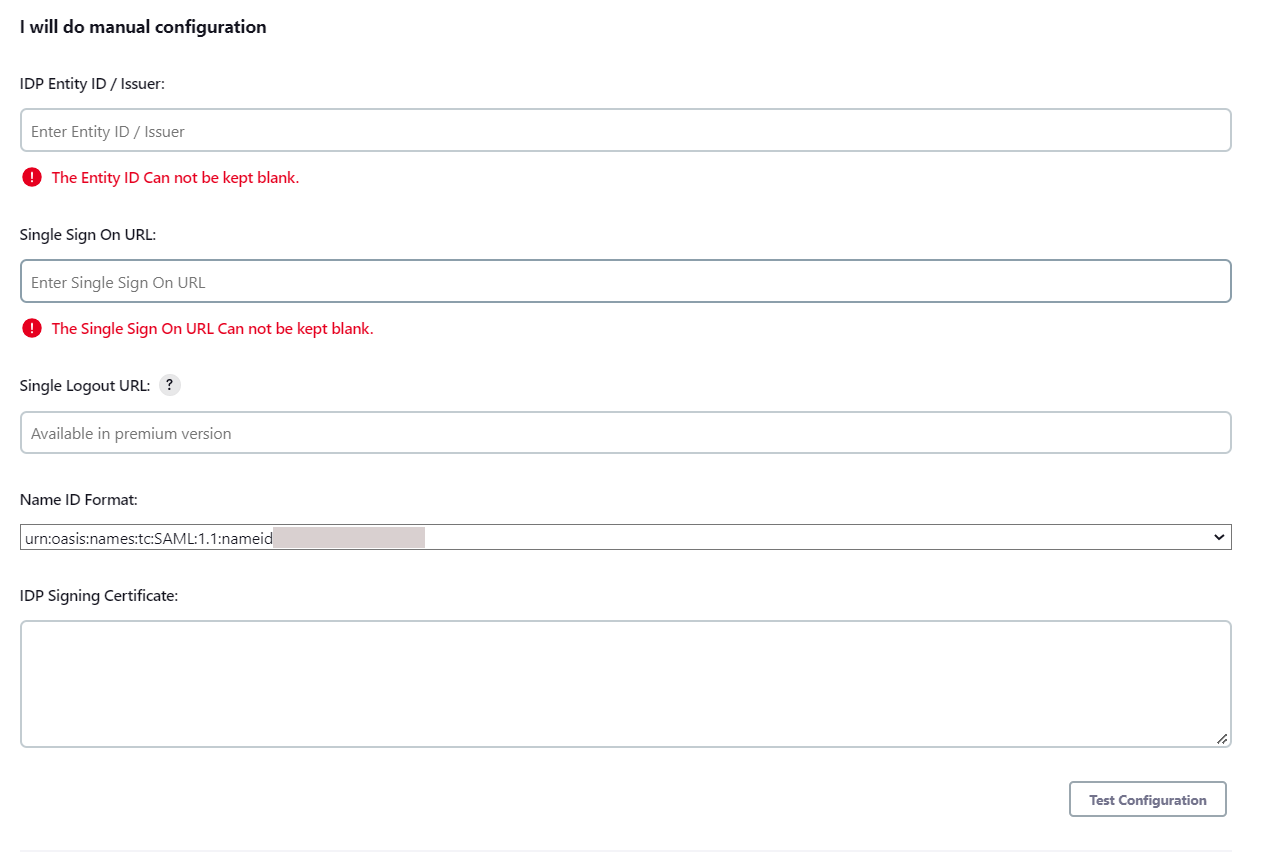
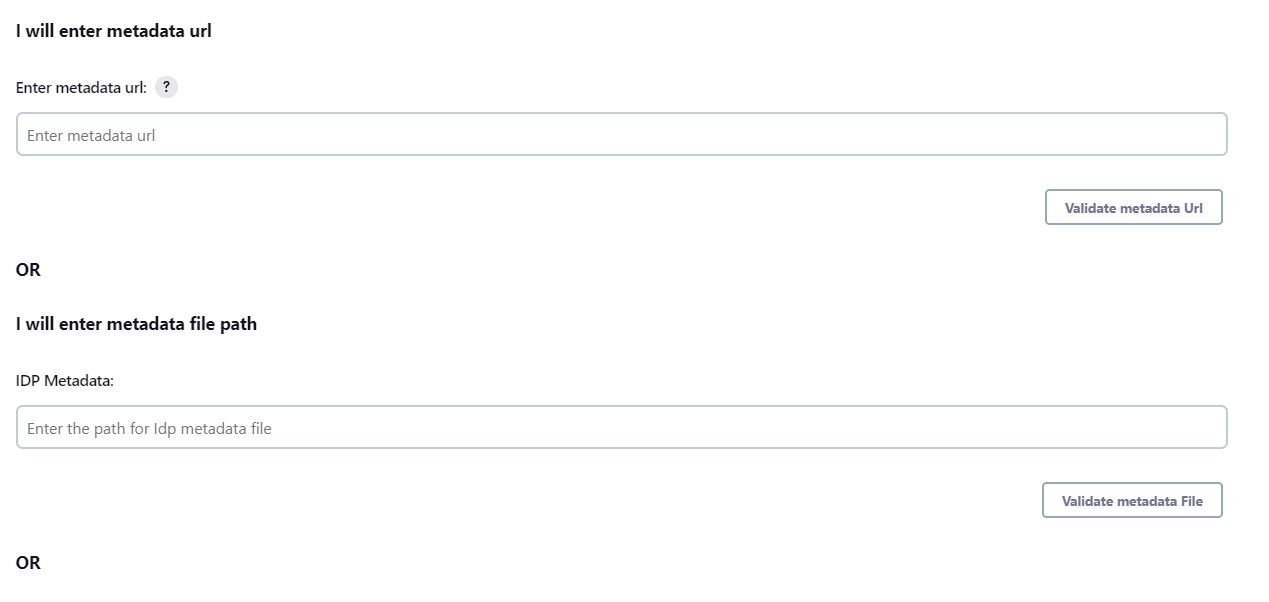
 IDP Configuration
IDP Configuration
To Configure IDP enter the following details and press apply and save the settings.
- IDP Entity ID
- Single Sign On URL
- Name ID Format
- X.509 Certificate
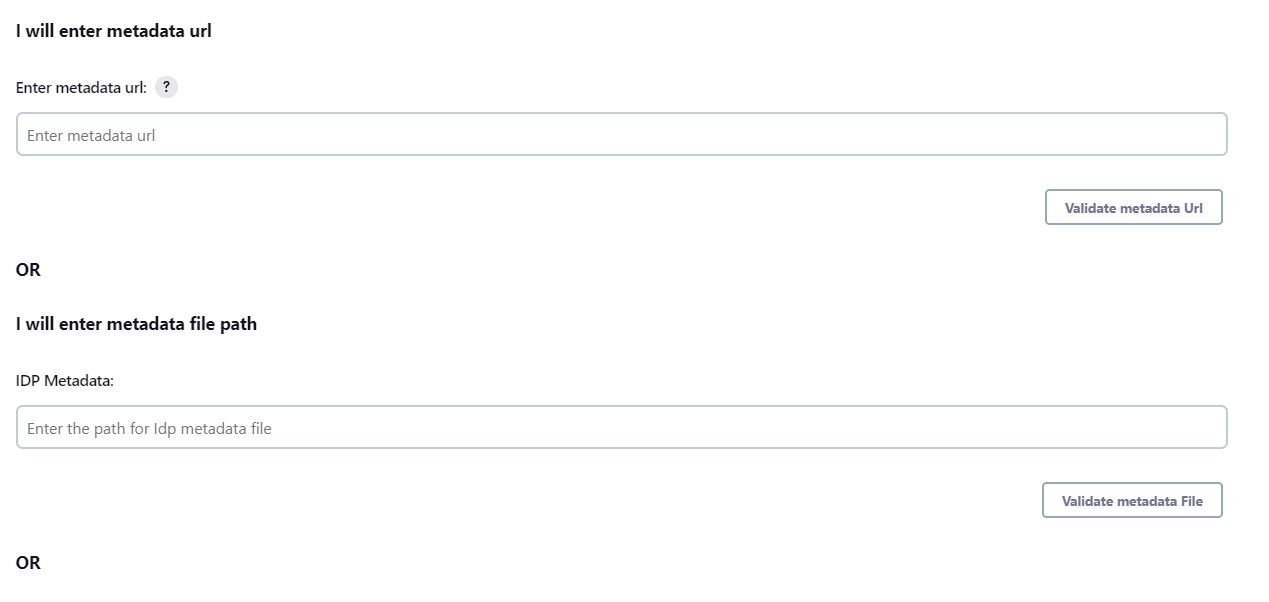
- You can either enter the metadata URL or the metadata file path.
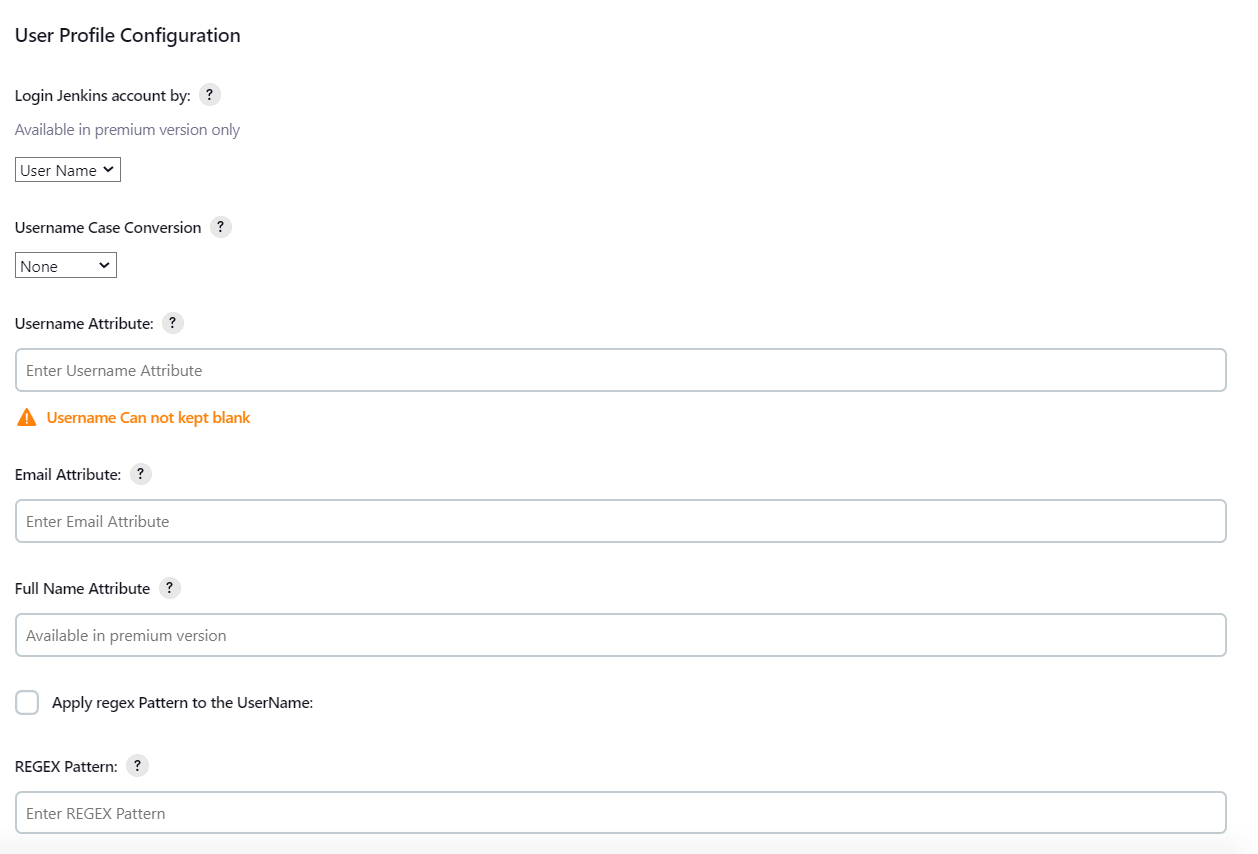
 User Profile Configuration
User Profile Configuration
- Select Username Case Conversion.
- Enter the attribute name from IDP which corresponds to Username in Username Attribute textbox.
- Enter the attribute name from IDP which corresponds to Email in Email Attribute textbox.
- Select the checkbox Apply regex Pattern to the UserName if the userID returned from SAML is not same as username of Jenkins.
- Enter the regular expression in REGEX Pattern textbox. It will be applied on user ID from SAML Response and will convert it into the username same as Jenkins. For example, you can use regular expression ^.*?(?=@) to extract demo from username demo@example.com
 Advanced Configurations
Advanced Configurations
- Select the SSO Binding Type.
- Select the Create new user after SSO? to allow user creation through SAML.
- Select Force Authentication.
- To Add custom Attributes select Add option.
- Set Attribute Name as the one set in IDP eg. lname
- Set display name in user proprties as one you want it appear in jenkins user's config.xml file and in user's configure tab.
 SP Configurations
SP Configurations
You can configure SP settings in IDP in 2 ways:
- By uploading Metadata XML file
- Click on Service Provider Metadata in SP Configuration section.
- Metadata xml file will be downloaded.
- Use this file to setup IDP.
- Manual Configuration
- To Configure SP Settings at IDP copy below URL and paste in respective fields at IDP end.
- SP Entity ID: https://your-jenkins-domain
- Audience URI: https://your-jenkins-domain
- ACS URL: https://your-jenkins-domain/securityRealm/moSamlAuth
 IDP Configuration
IDP Configuration
To Configure IDP enter the following details and press apply and save the settings.
- IDP Entity ID
- Single Sign On URL
- Single Logout URL
- Name ID Format
- X.509 Certificate
- You can either enter the metadata URL or the metadata file path.
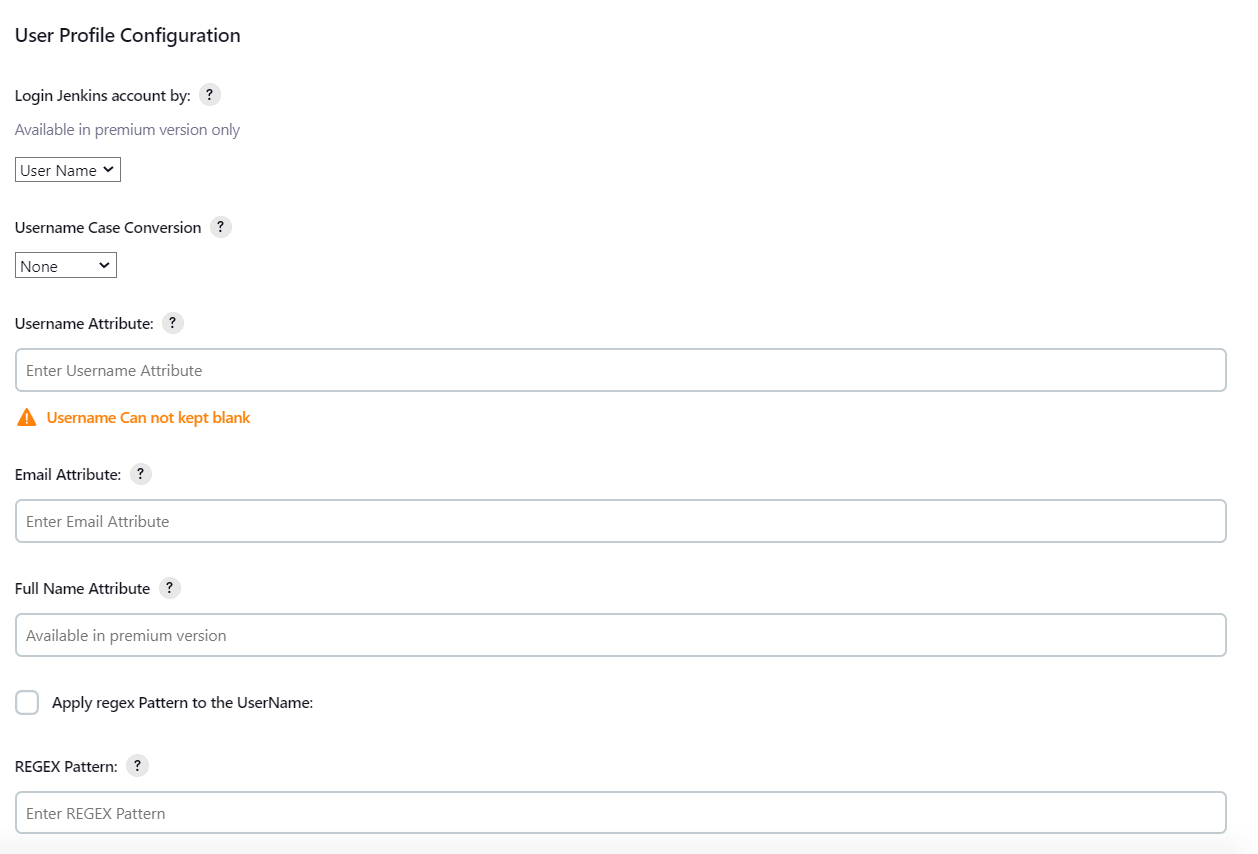
 User Profile Configuration
User Profile Configuration
- Select Username or Email for Login Jenkins account by:
- Select Username Case Conversion.
- Enter the attribute name from IDP which corresponds to Username in Username Attribute textbox.
- Enter the attribute name from IDP which corresponds to Email in Email Attribute textbox.
- Enter the attribute name from IDP which corresponds to full name in Full Name Attribute.
- Select the checkbox Apply regex Pattern to the UserName if the userID returned from SAML is not same as username of Jenkins.
- Enter the regular expression in REGEX Pattern textbox. It will be applied on user ID from SAML Response and will convert it into the username same as Jenkins. For example, you can use regular expression ^.*?(?=@) to extract demo from username demo@example.com
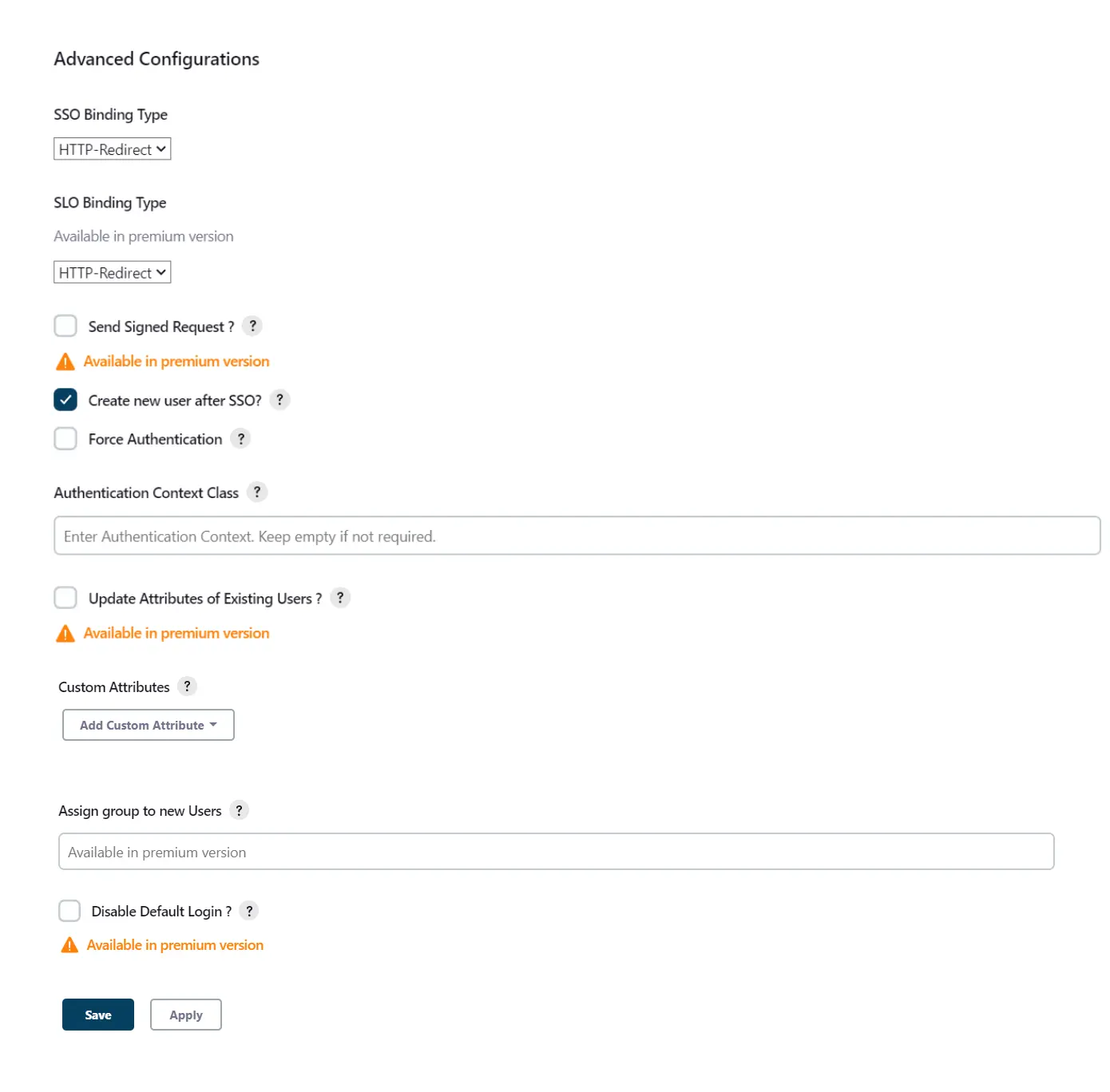
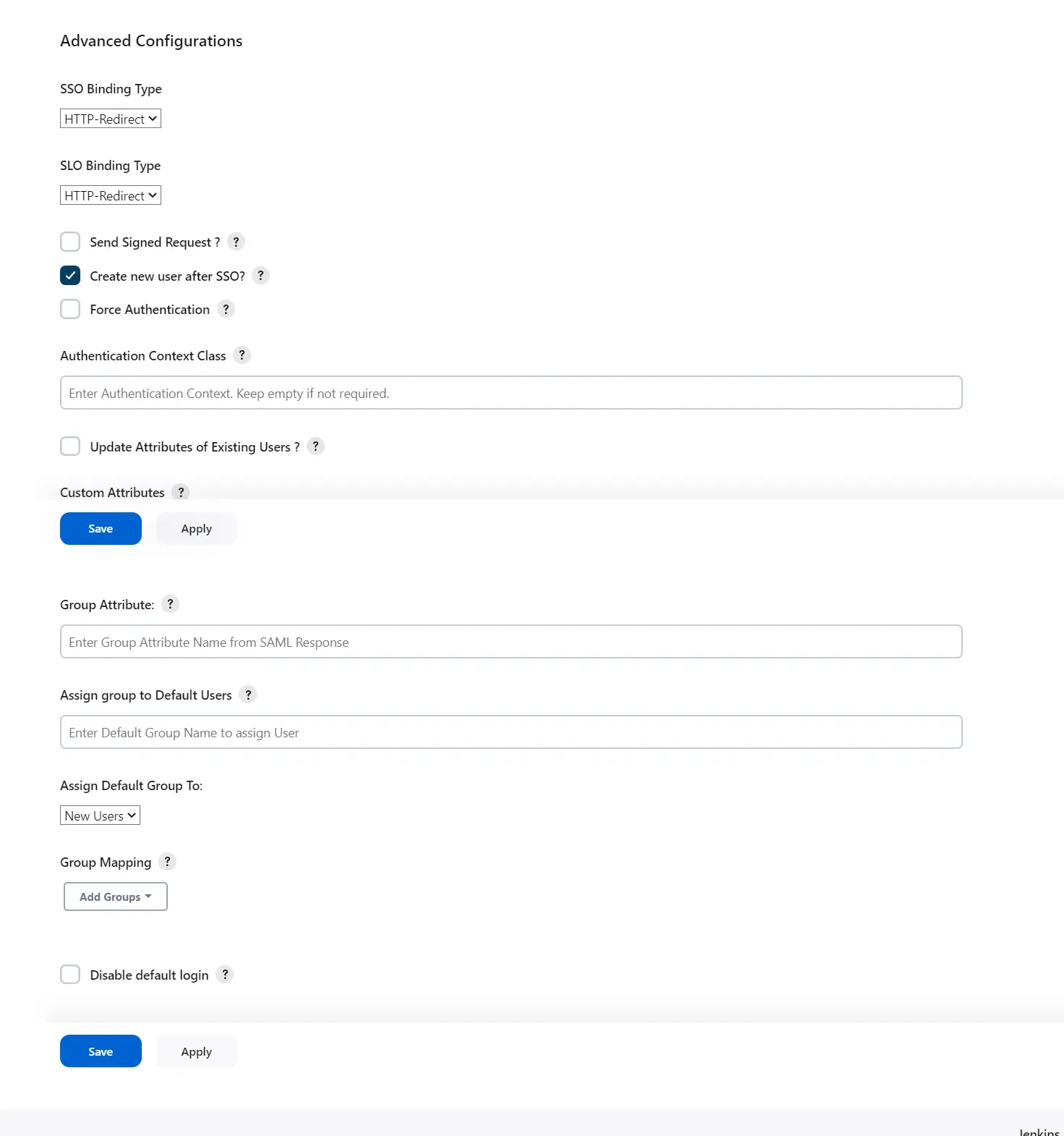
 Advanced Configurations
Advanced Configurations
- Select the SSO Binding Type.
- Select the SLO Binding Type.
- Select the Send Signed Request ? to send signed login and logout requests. Requests will be signed using public certificate from option Download SP Certificate in SP Configuration section.
- Select the Create new user after SSO? to allow user creation through SAML.
- Select Force Authentication.
- Select the Update Attributes of Existing Users ? to update attributes of existing user's each time they sign in Jenkins through SSO.
- To Add custom Attributes select Add option.
- Set Attribute Name as the one set in IDP eg. lname
- Set display name in user proprties as one you want it appear in jenkins user's config.xml file and in user's configure tab.
- If Disable Default login option is enabled, any unauthenticated user trying to access the default Jenkins login page will get redirected to the IDP login page for authentication. After successful authentication, they will be redirected back to the Jenkins base URL.
- Copy backdoor URL and save it for emergency.
Step 3: Manage permissions/Groups
Click on the Group Configuration tab from the left panel.
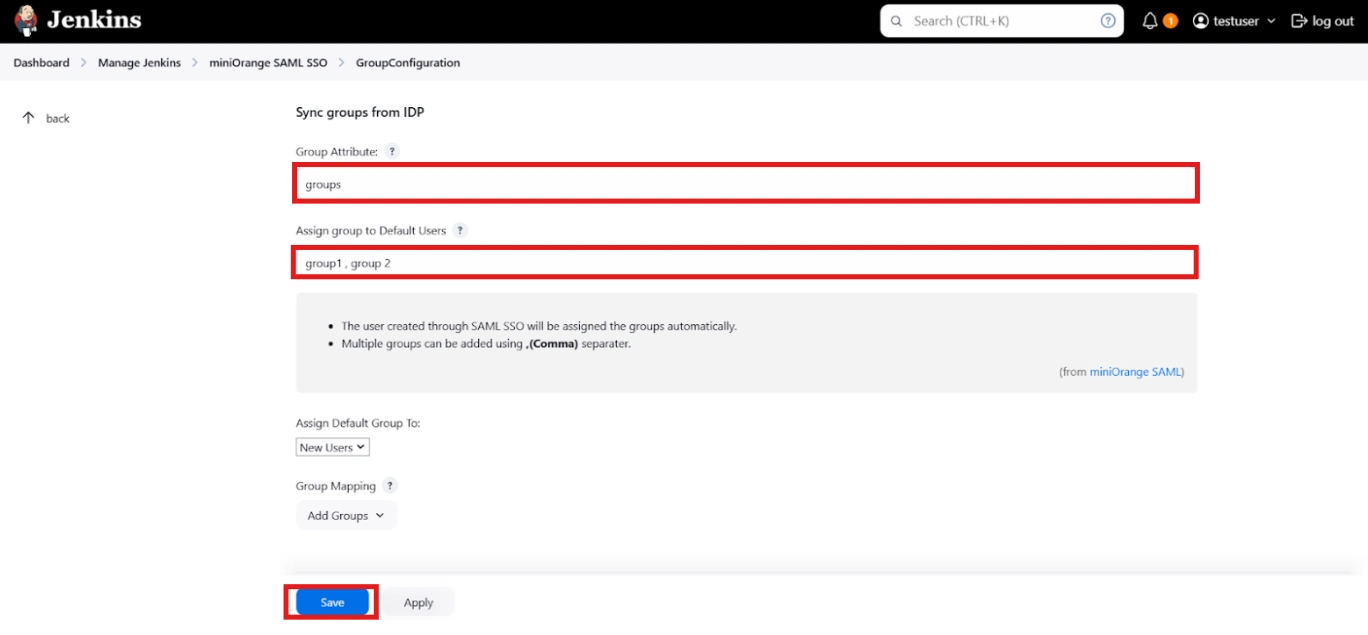
 3.1 Sync groups from IDP
3.1 Sync groups from IDP
- You can assign groups from IDP to users created through SSO by adding the name of the group attribute that contains the IDP groups in the SAML response in the Group Attribute field in the plugin configuration. You can find out the group attribute name by performing the test configuration from the test configuration button under the I will do manual configuration tab.
- To assign a default group to users created through SSO add the group name in the Assign group to new Users option. Multiple groups can be added using a comma (,) separator.
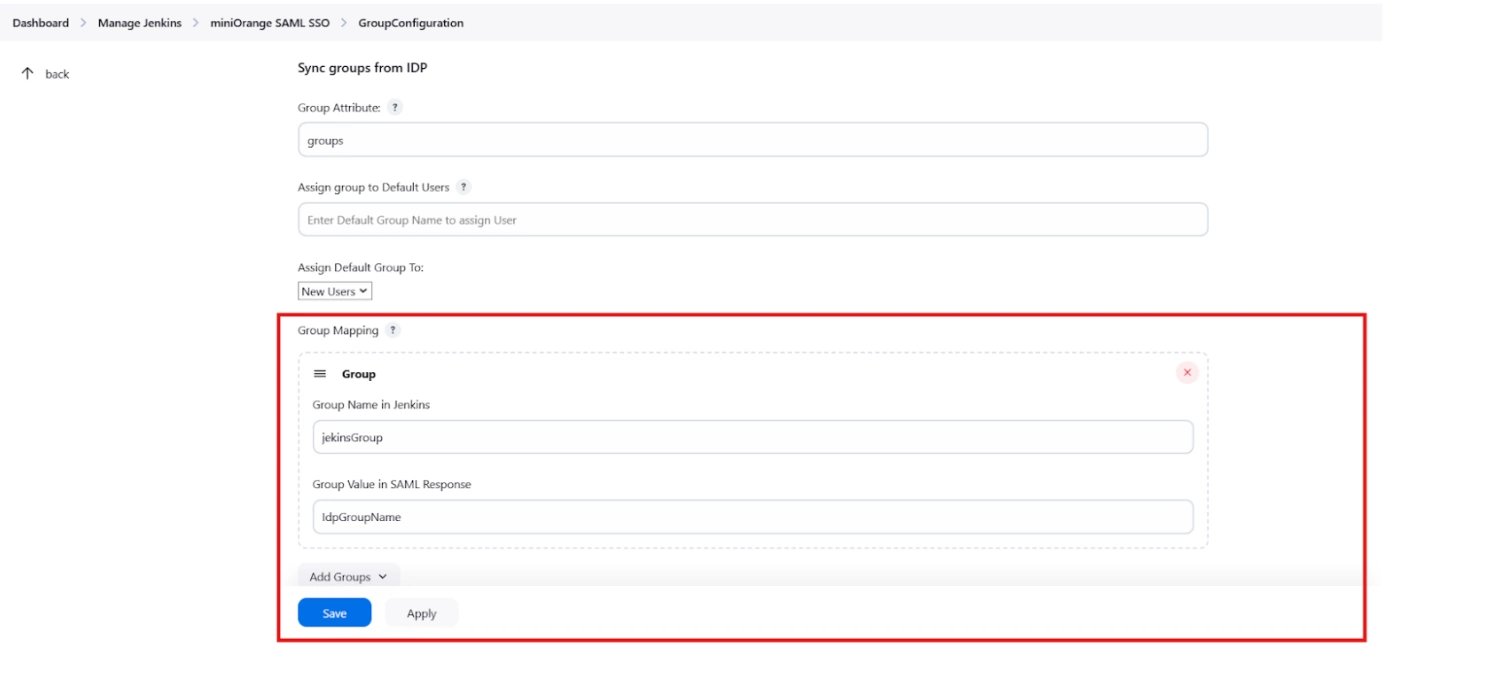
- Group Mapping allows you to align user groups from your identity provider (IdP) with the corresponding groups in Jenkins. This is especially useful when the group names in your IDP differ from those in Jenkins. By configuring group mappings, you can ensure that users are assigned the correct roles and permissions within Jenkins based on their IdP group membership.
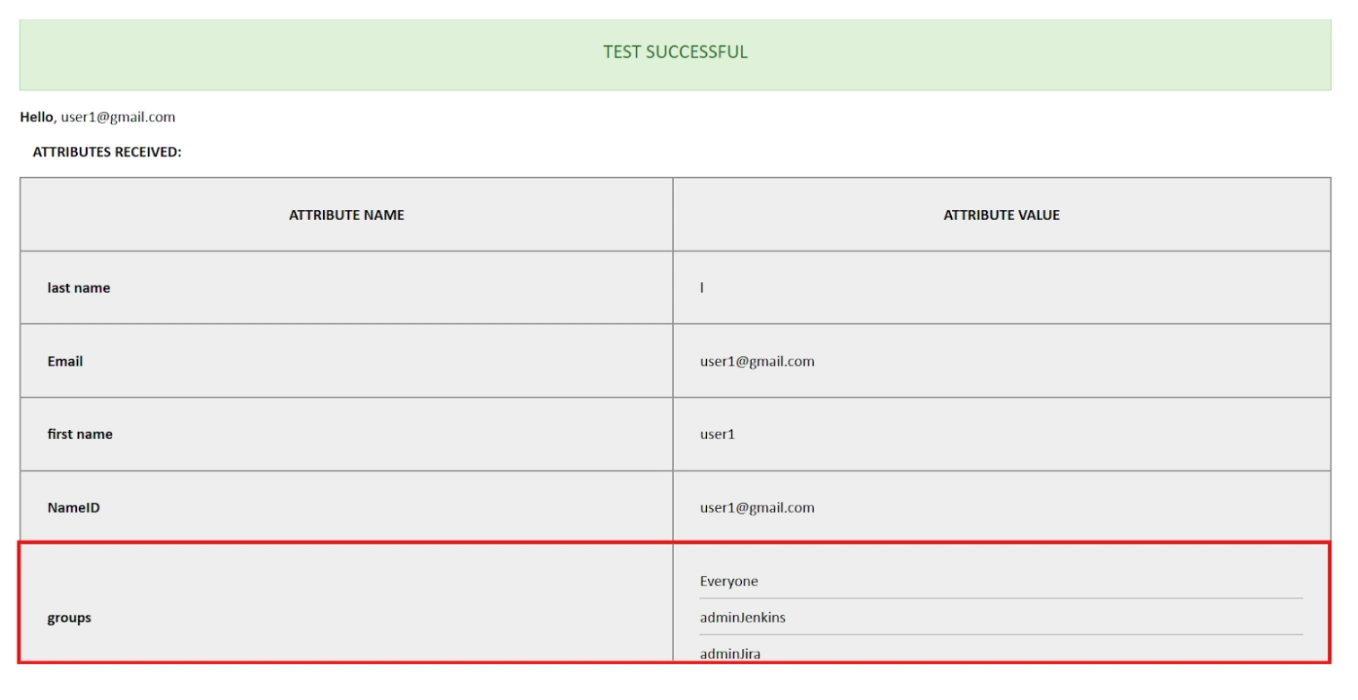
For example, if your IdP group is named "idpGroupName" but the corresponding group in Jenkins is "jenkinsGroup", you can map idpGroupName to jenkinsGroup to maintain consistent access control.
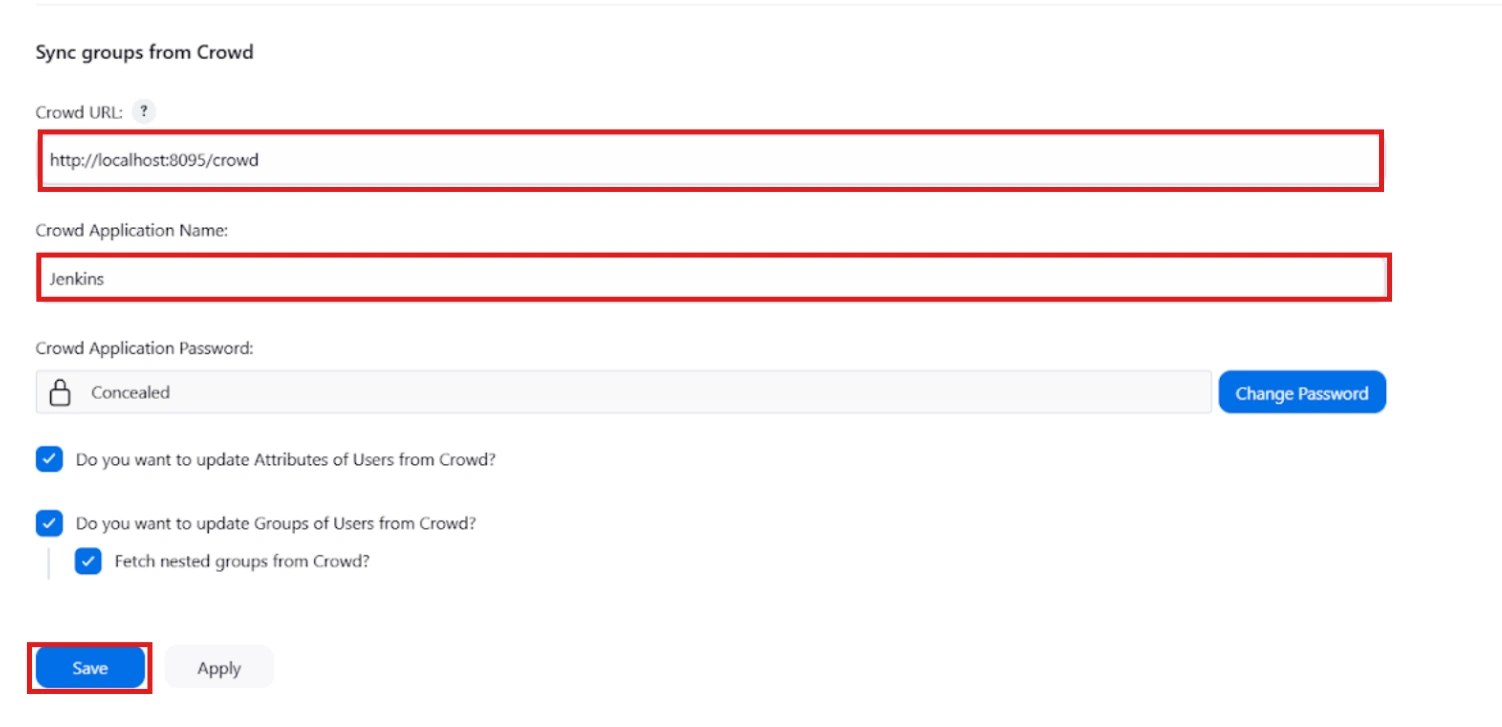
 3.2 Sync groups from crowd
3.2 Sync groups from crowd
- To Assign groups from the crowd just enter your crowd instance url and crowd application name and password as shown below.
- You can refer to this guide to add a jenkins application to your crowd instance.
- If you want to update user details or want to fetch groups or nested groups check the options accordingly.
Additional Resources
Did this page help you?

 Try it for free
Try it for free