SAML Single Sign On (SSO) into SonarQube using miniOrange as IDP
SonarQube SAML plugin gives the ability to enable SAML Single Sign On for the SonarQube. Here we will go through a guide to configure SSO between SonarQube and miniOrange. By the end of this guide, miniOrange users should be able to log in and register to the SonarQube Server.
Video Setup Guide
You can refer the steps from the video or documentation below to configure your IDP with SonarQube.
Step 1: Set Up miniOrange as Identity Provider
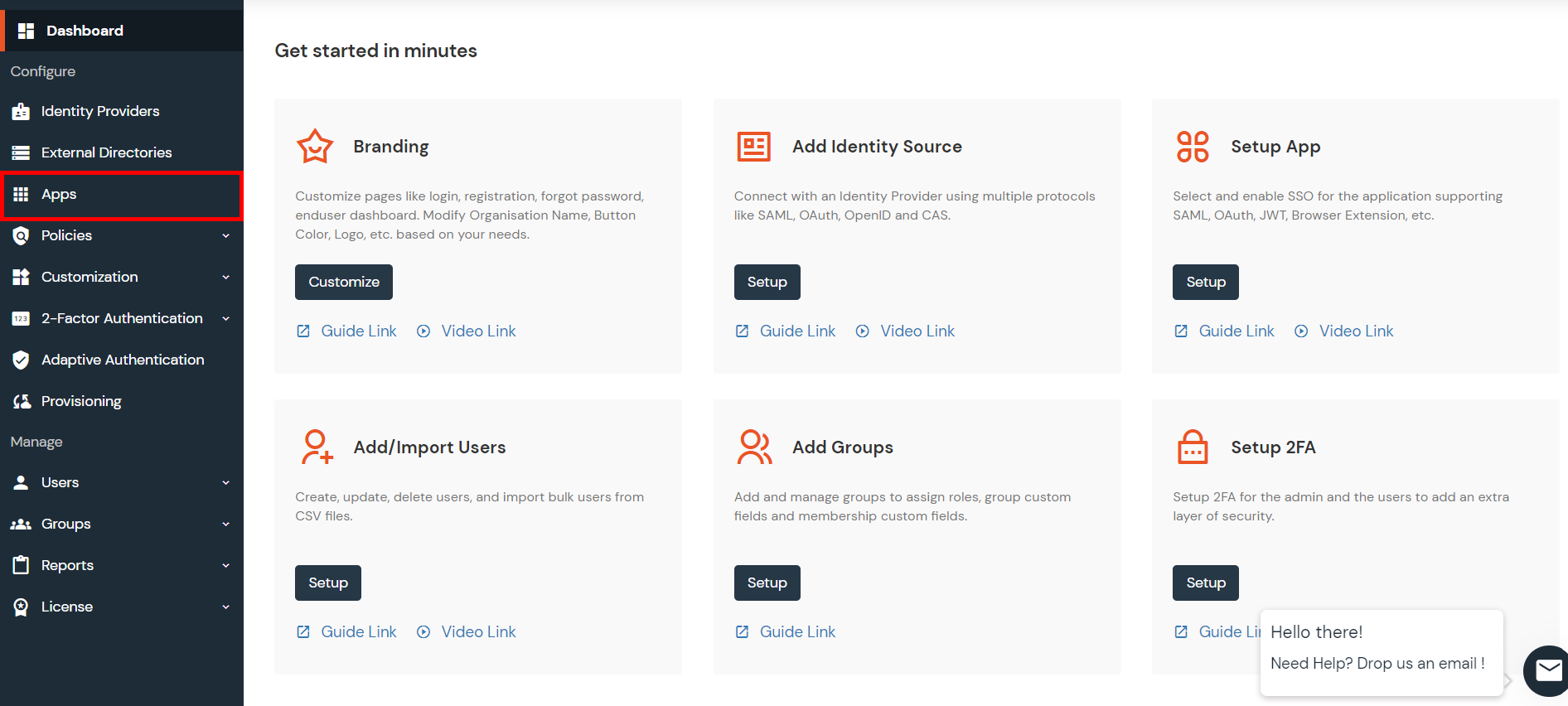
- Go to miniOrange Admin console https://login.xecurify.com/moas/login and login with your miniOrange credentials.
- From the left menu, go to Apps.
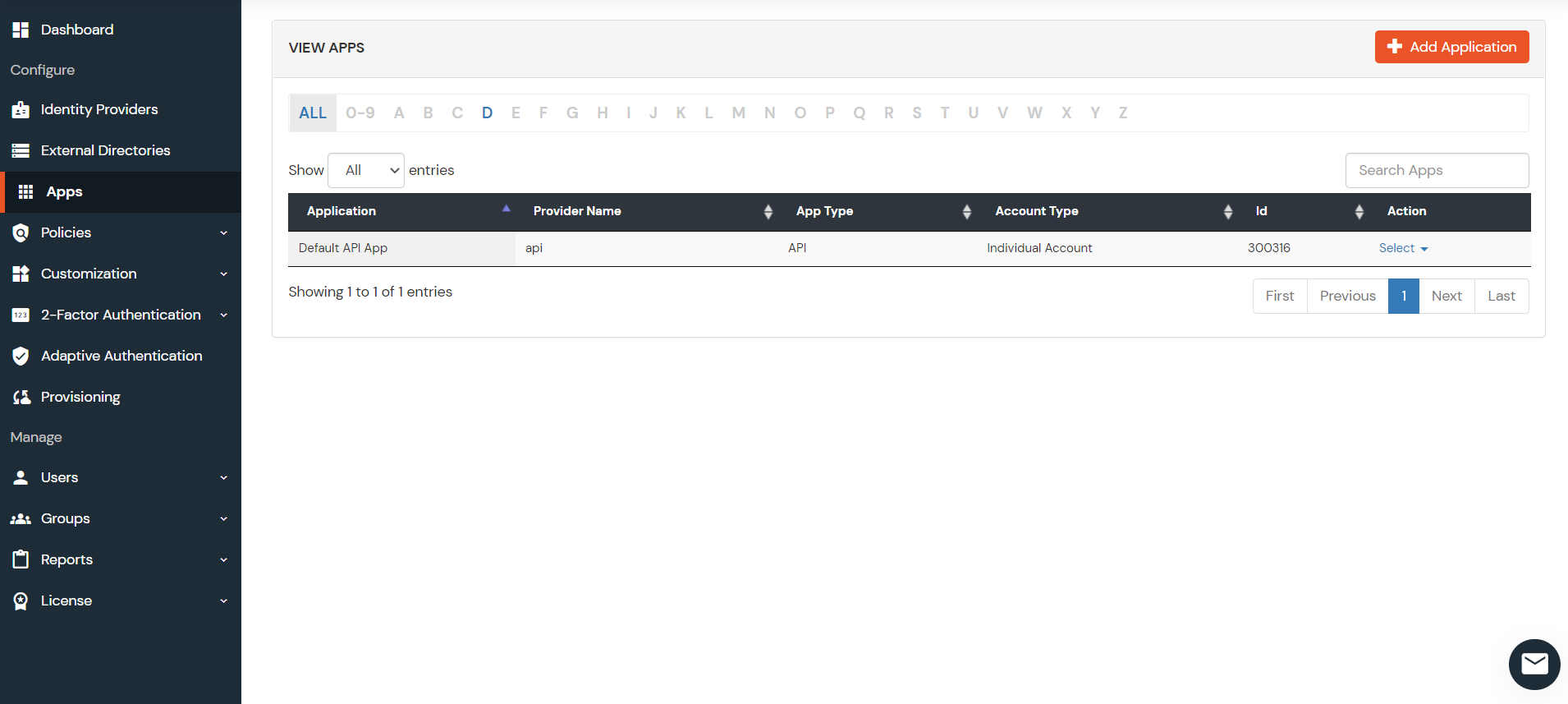
- Click on Add Applicaton button.
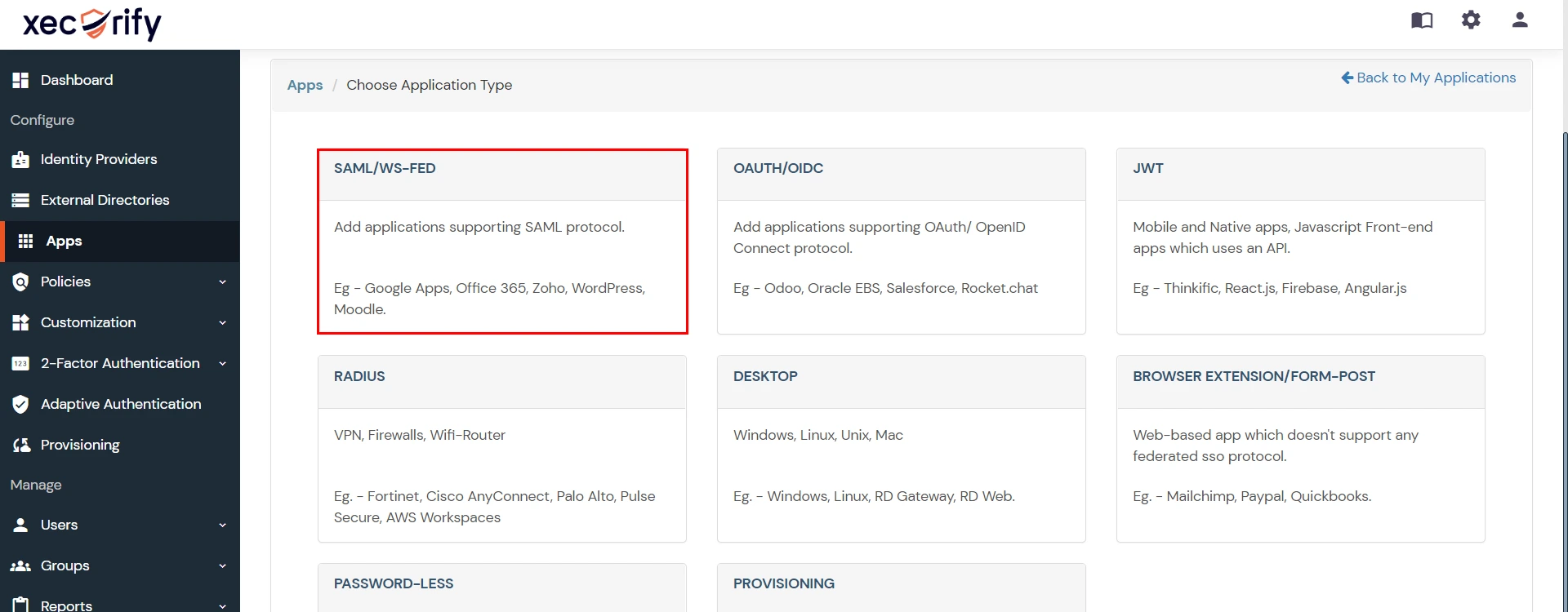
- In Choose Application Type click on Create App button in SAML/WS-FED application type.
- In the next step, search for your application from the list, if your application is not found. Search for "custom" and you can set up your app via Custom SAML App.
- Method 1: Manual Configuration
- Enter the following the textboxes:
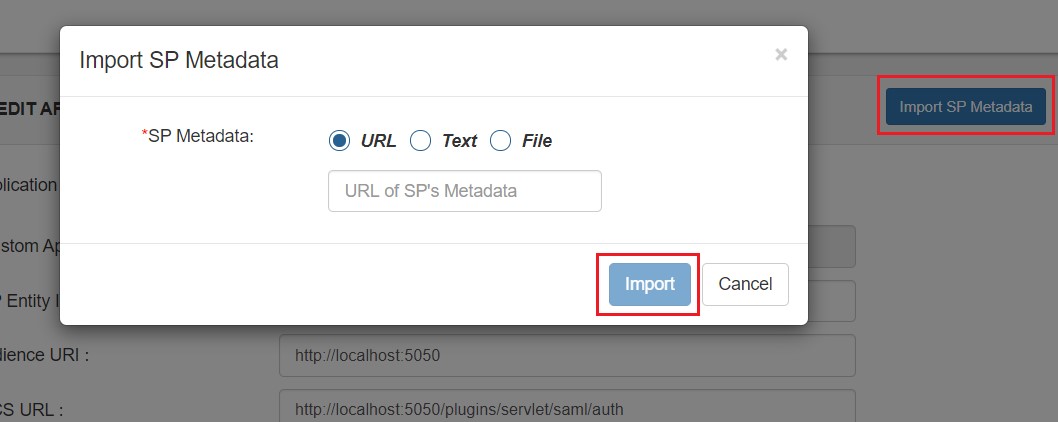
- Method 2: Import SP Metadata:
- You can also import SP metadata to configure your app.
- Click on Import SP Metadata button.
- Enter your Custom Application Name in App Name text box.
- Upload plugin metadata in form of text, File or URL and Click Import.
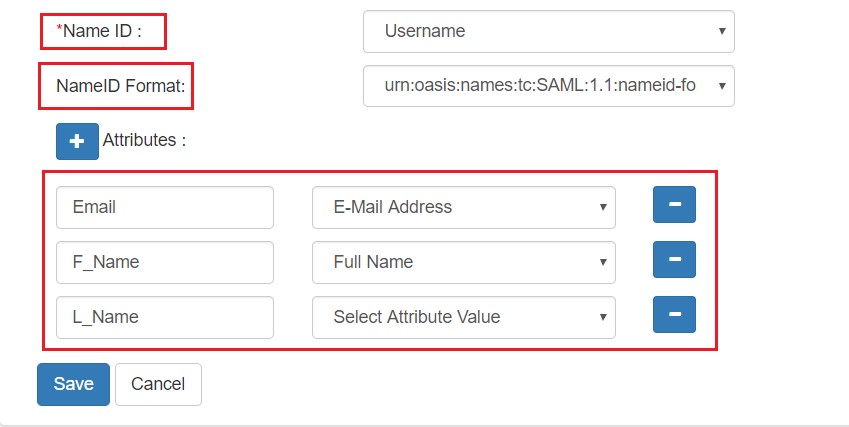
- Name ID Setup And Attribute Mapping :
- Enter the attribute name with which you want to log in your application in NameID field.. eg.Username, Email etc.
- Enter name ID format such as emailAddress, nameid etc. in Name ID Format.
- Attributes can be mapped using Add Attribute tab.
- Add attributes such as first name, last name, group Name, etc.with its corresponding value as per shown in image.
- Multiple attributes can be added using icon
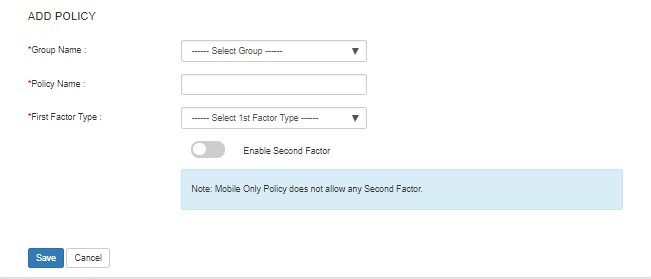
- Select Default from the Group Name dropdown.
- Enter Policy Name you would like to provide.
- Select Password from the Login Method Dropdown.
- Click on Save to add the App.
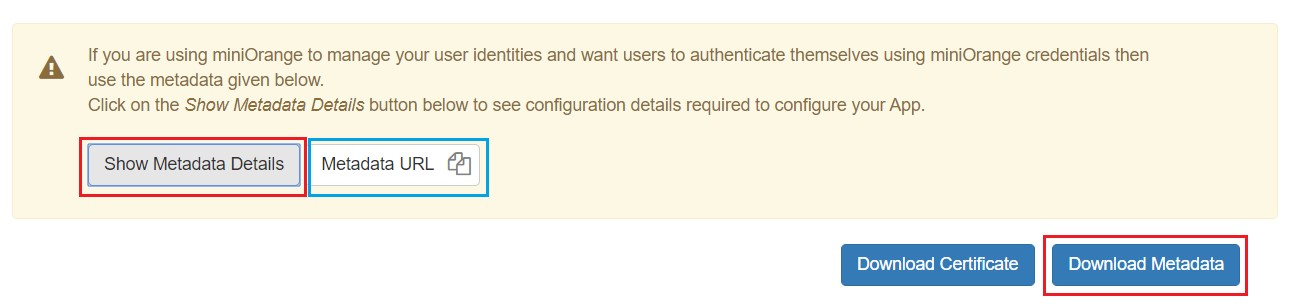
- Navigate to Apps Manage Apps.
- Click on the metadata link against your app.
- Download the Metadata XML File or note down the given information and keep it handy to configure the add-on.
- You can also provide Metadata URL in plugin settings.
 Creating App in miniOrange
Creating App in miniOrange
| Custom Application Name | App name you like to provide. |
| SP Entity ID or Issuer | Enter SP Entity ID / Issuer from Service Provider Info tab of the plugin |
| ACS URL | Enter ACS (Assertion Consumer Service) URL from Service Provider Info tab of the plugin |
| Single Logout URL | Enter Single Logout URL from Service Provider Info tab of the plugin |
Step 2: Set Up SonarQube as Service Provider
 Fetch the Identity Provider (IdP) Details
Fetch the Identity Provider (IdP) Details
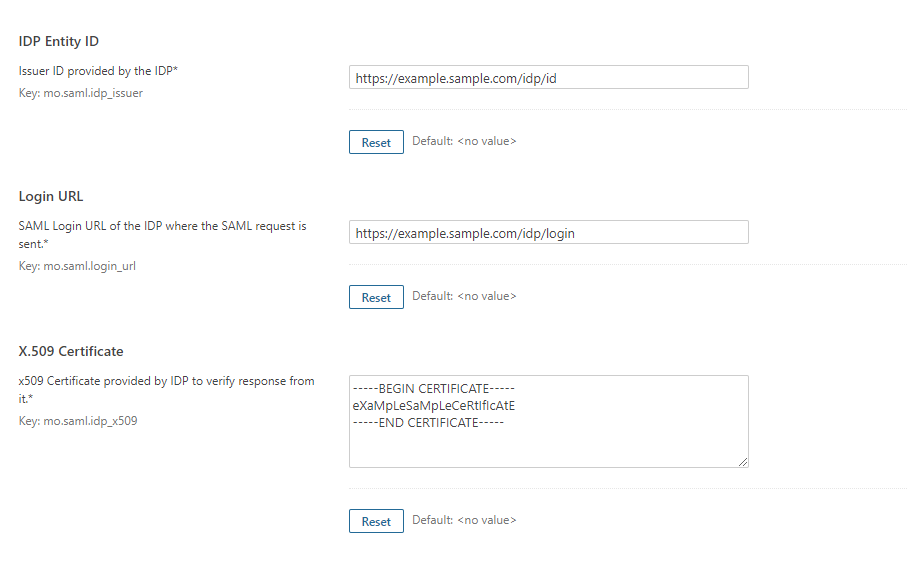
- After configuring the IdP, get its metadata to configure SonarQube as a Service Provider(SP).
-
Copy the following details from the IdP metadata and paste them
into the corresponding text fields in the SonarQube plugin.
- IdP Entity ID
- Login URL
- X.509 Certificate
- Save all the details.
 Test Configuration
Test Configuration
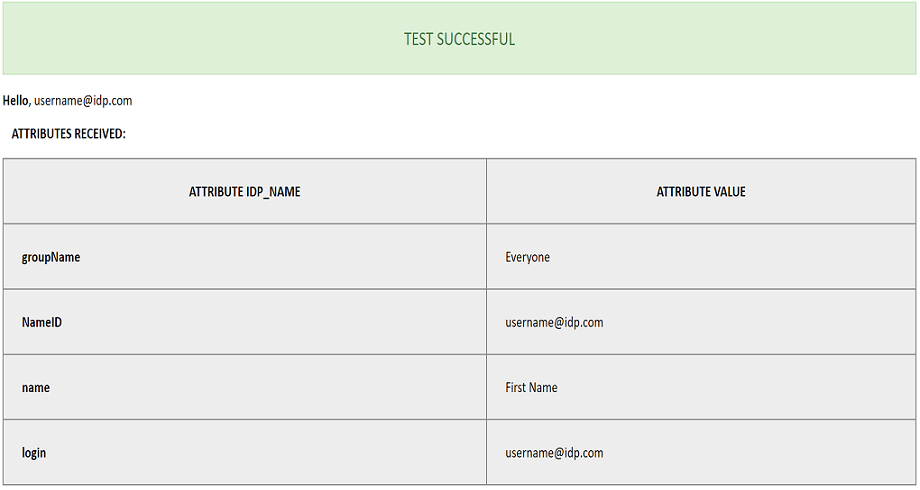
- Once you have filled all the IdP details, go to Administration >>Configuration >>miniOrange SAML Support and then click on the Test Configuration tab.
- It will show you the IdP login page. Enter your IdP credentials and log in.
- If all the configurations are correct, it will show you the user details received from the IdP.
- If the test fails, check if you have missed out any steps or try to debug through SonarQube .
- To be able to troubleshoot through logs, first you'll have to set a higher log level in your SonarQube application.
- To do so, go to the SonarQube Dashboard >> Administration >> System.
- Under the system settings, you'll find an option to change the log's level. Select DEBUG and save it. Now try to configure the plugin.
- If you face any problem during configuration, go to %SONARQUBE_HOME% / logs directory.
- Find and open the web.log file. Go through the logs recorded.
- You'll find the stacktrace of performed actions, along with date and time information.
 Attribute & Group Mapping
Attribute & Group Mapping
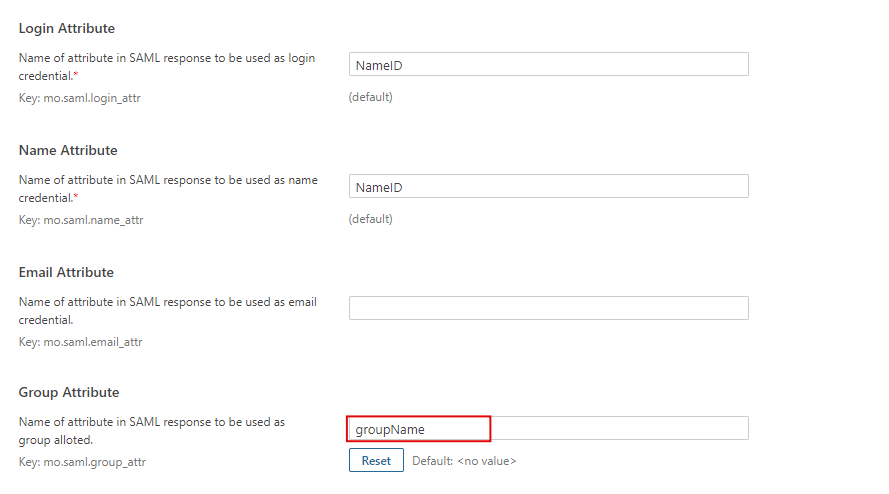
- In order to map attributes from the Identity Provider to the application, the attribute names received in the SAML response need to be entered in their corresponding fields.
- To view these attribute names, click on the Test Configuration tab in the plugin support page.
-
Attributes used in SonarQube Application are described briefly as
below:
- Login Attribute is a unique name assigned to the user to identify them uniquely within the SonarQube system. It's a required attribute.
- Name Attribute is the full name of the user, to be mapped from the IdP to the SonarQube. It's a required attribute.
- Email Attribute is an optional attribute and represents an email address of the user, to be mapped from the IdP to the SonarQube.
- Group Attribute mapping requires the group names, in the application, to be same as the group names in the Identity Provider. Otherwise, the default SonarQube Group is assigned to the user.
- Eg. To map group value Everyone from SAML response we have to paste groupName in Group Attribute field.
Additional Resources
Did this page help you?

 Try it for free
Try it for free