SAML SSO for JSM Customers using Centrify as IDP
You can now allow External Customers to log in via SSO into Jira Service Management (previously Jira Service Desk or JSD). Integrate various customer portals like Atlassian Service Management and access tickets with the help of SAML SSO for JSM Customers.
Download and Installation
- Log into your Jira instance as an admin.
- Navigate to the settings and Click on Apps.
- Locate SAML/OAuth SSO for JSM Customers.
- Click on free trial to begin a new trial SAML/OAuth SSO for JSM Customers.
- On menu bar click on Apps. Locate SAML/OAuth SSO for JSM Customers.
Step 1: Set Up Centrify as Identity Provider
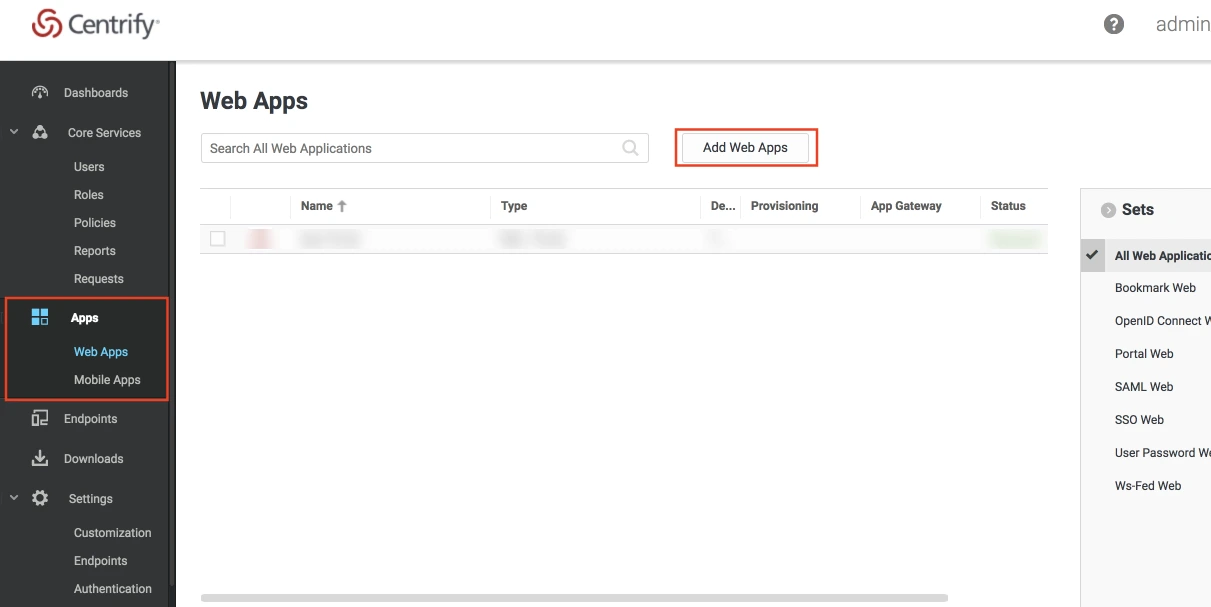
- Log into Centrify as an Administrator and click on Apps on the sidebar. Then Click on Web Apps.
- Click on the Add Web Apps button next to the search bar.
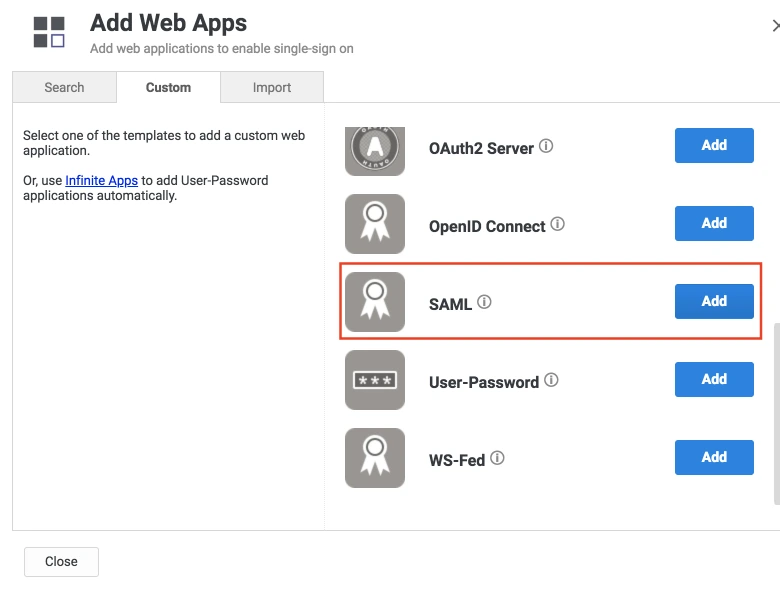
- Then select the Custom tab. Search for SAML and click on the Add button. Now press Yes to confirm.
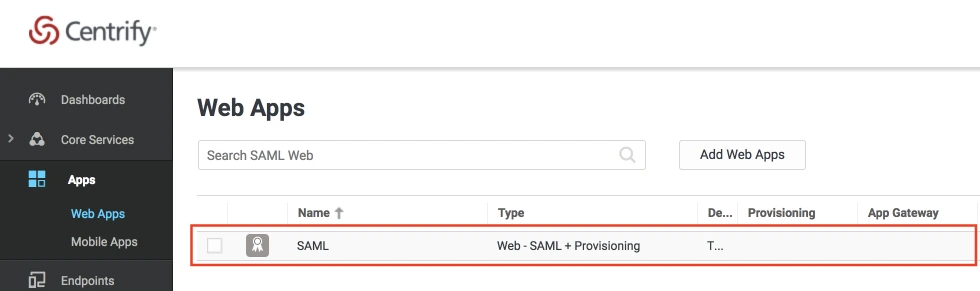
- When you create a web app, it will be listed in the Web Apps tab. Click on the newly created web app to configure.
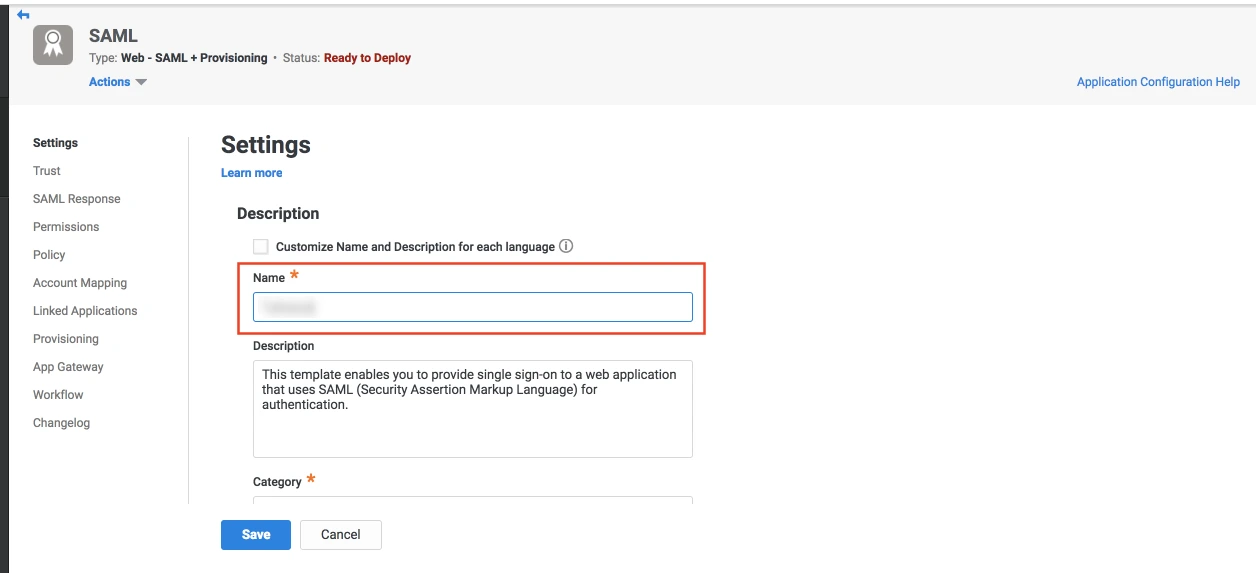
- The name and description of the web app can be updated from this settings tab.
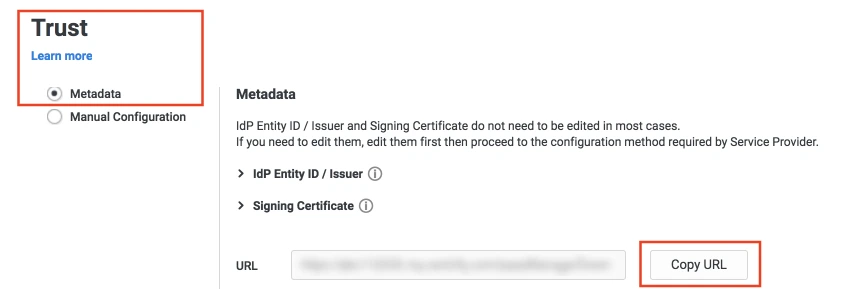
- Select the Trust tab from the sidebar. Trust tab will have metadata details for the configuration. Copy the metadata URL and save it for configuration with miniOrange.
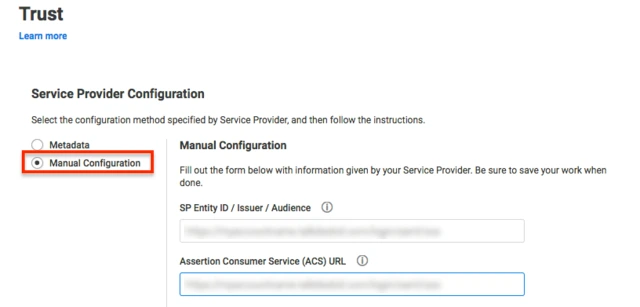
- Now scroll down until you see the Service Provider Configuration. Here you can configure the SP metadata either using the URL or manual configuration.
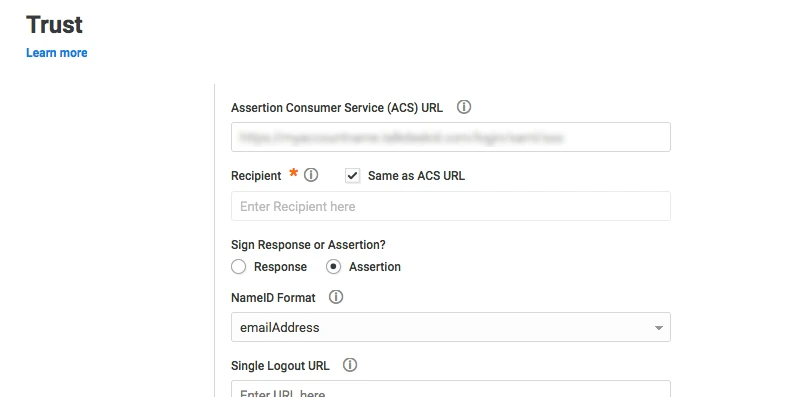
- Enter the configuration details and click on SAVE.
- Click on the SAML Response tab from the left sidebar.
- Here, you can map attributes from your source directory to SAML attributes that will be returned with the response.
- Also, Centrify provides a script editor under the custom logic section in the SAML Response tab to add more complex logic to map attributes.
- You will have to add below functions to the code -
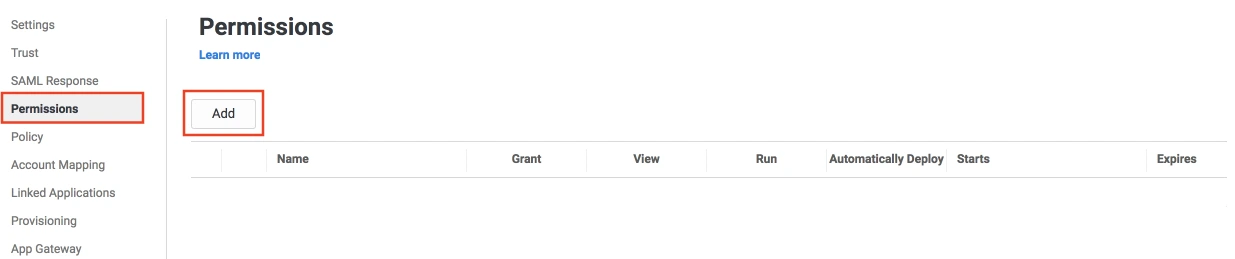
- From the left sidebar, select Permissions.
- Click on the Add button. The Select User, Group, or Role dialog will appear.
- Select the users, groups, or roles that will be accessing this web app. The role rules will be displayed on the User Access card.
- Click on the Save button.
 Create SAML App
Create SAML App
 Configure SAML App
Configure SAML App
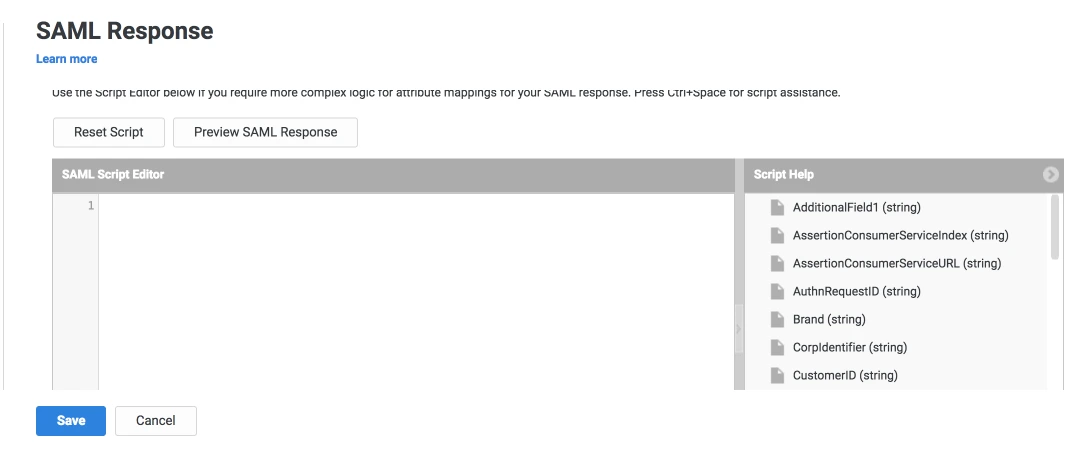
| setAudience() | SP-EntityID / Issuer from Step 1 of the plugin under the SP Info Tab. E.g: setAudience('https://example.com') |
| setRecipient() | Recipient URL from Step 1 of the plugin under the SP Info Tab. E.g: setRecipient('https://example.com/plugins/servlet/saml/auth') |
| sethttpsDestination() | Destination URL from Step 1 of the plugin, under the SP Info Tab. E.g: sethttpsDestination('https://example.com/plugins/servlet/saml/auth') |
Step 2: Setup JSM as Service provider
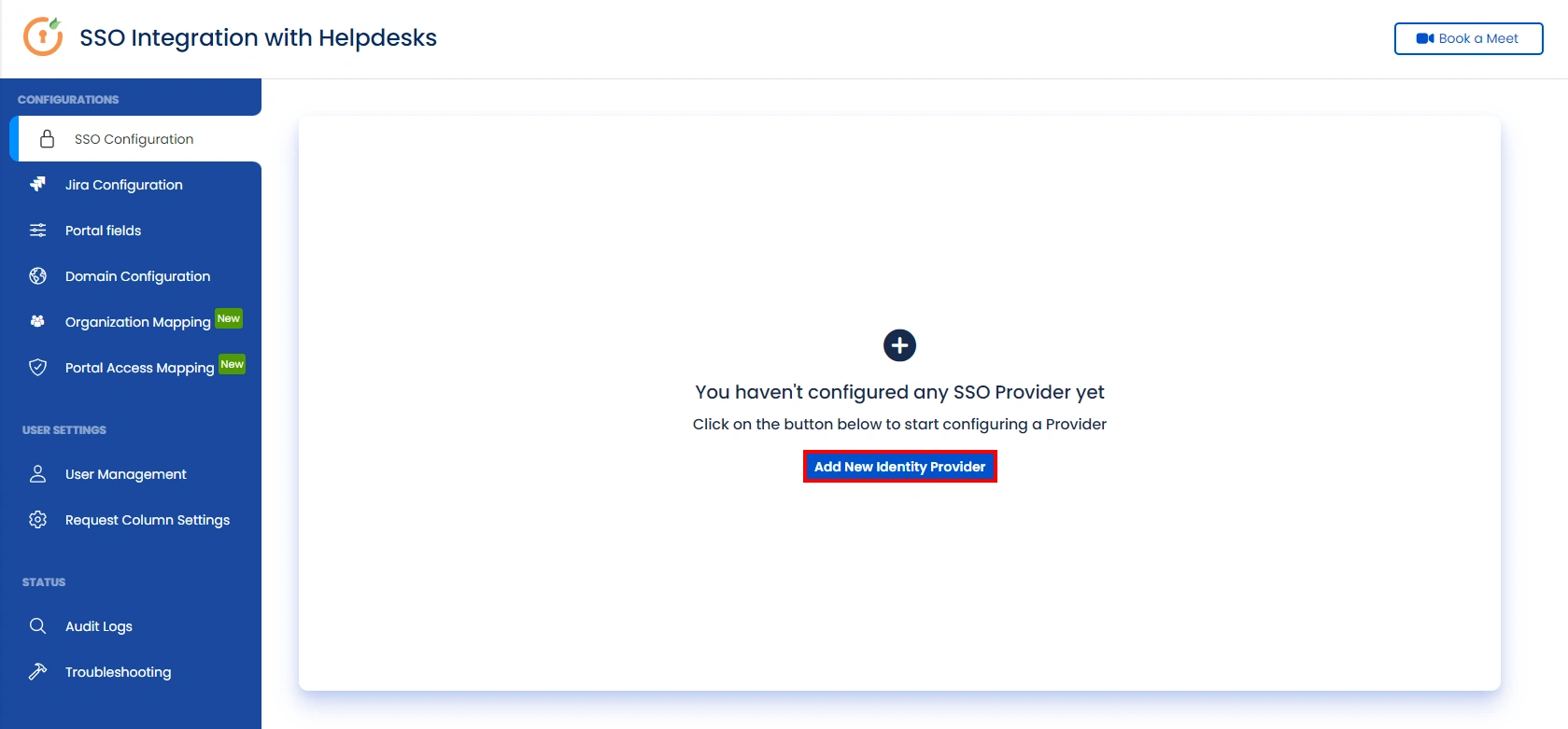
- Go to the Manage Apps -> click Getting started under SSO Integration with Helpdesk then click on the Add New Identity Provider.
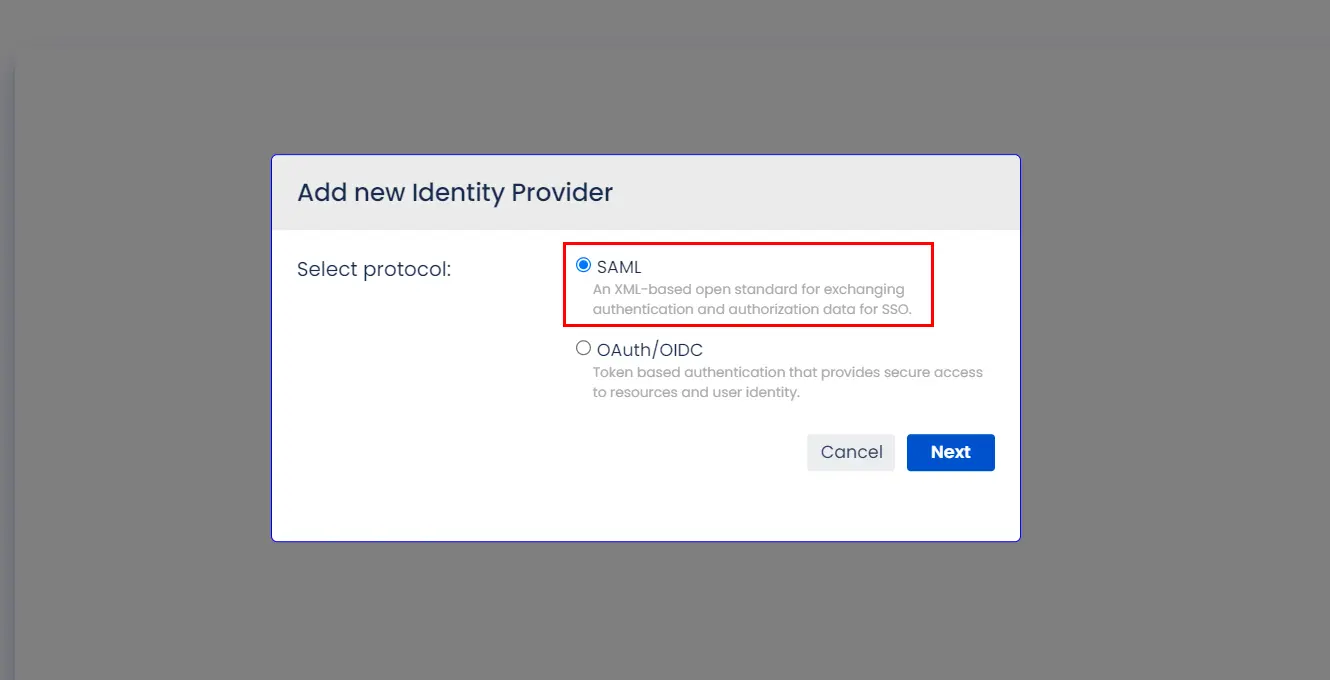
- Select SAML and click on the next button.
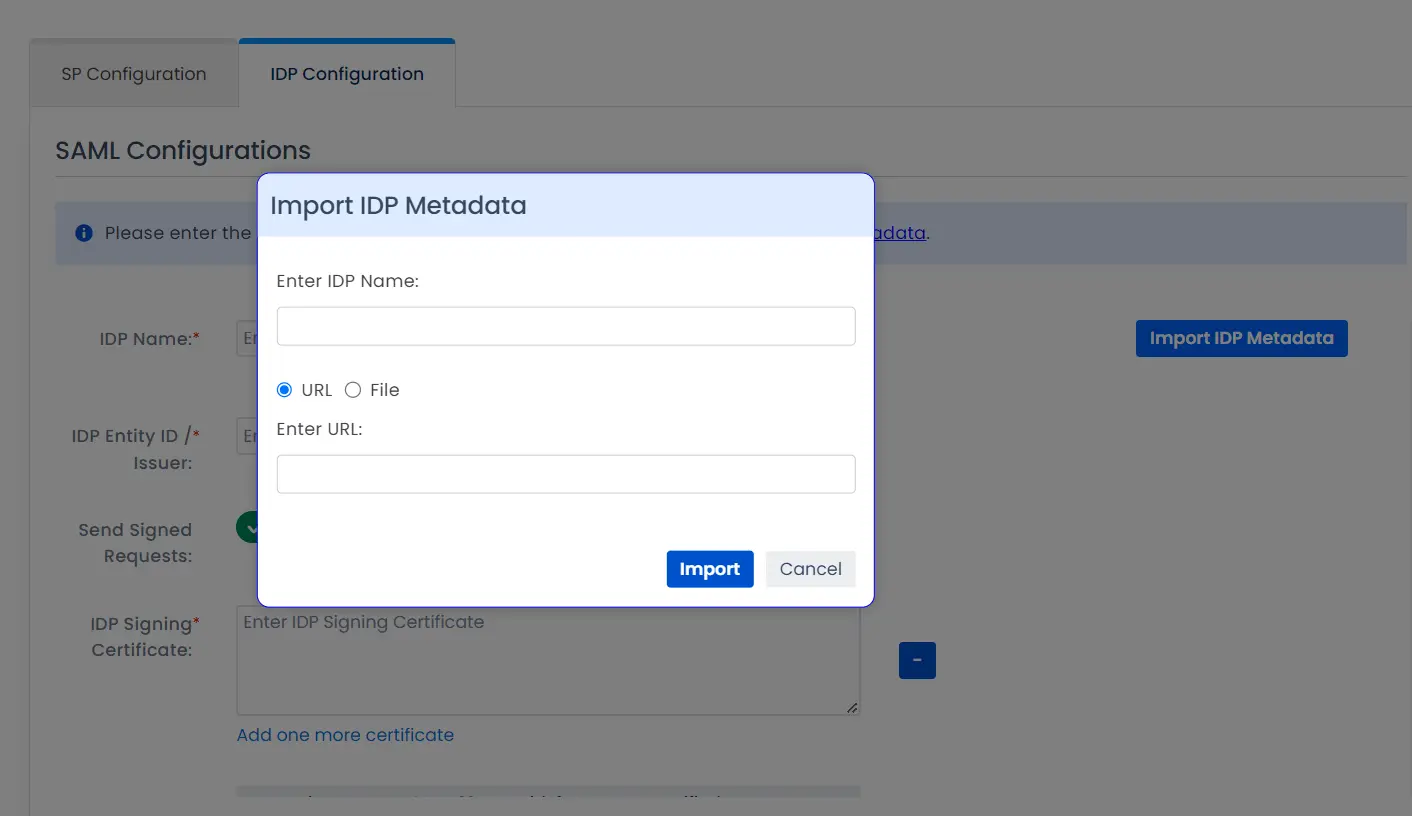
- Click on Import IDP Metadata.
- Enter IDP name.
- Choose IDP metadata URL / File: Enter your metadata URL / File
- Click Import
A. By Metadata URL :
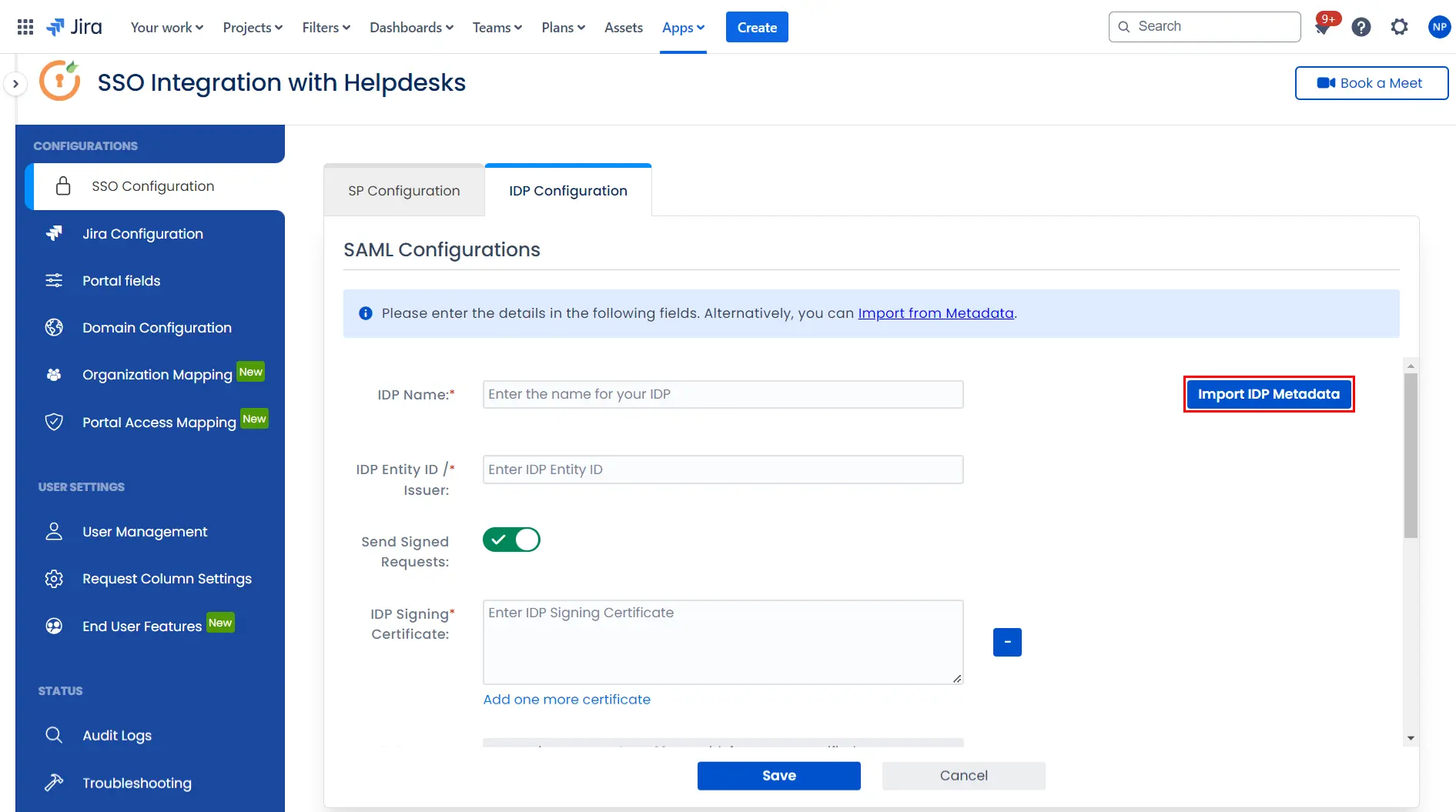
To configure the IDP manually, you will need to have the following details from your IDP's metadata.
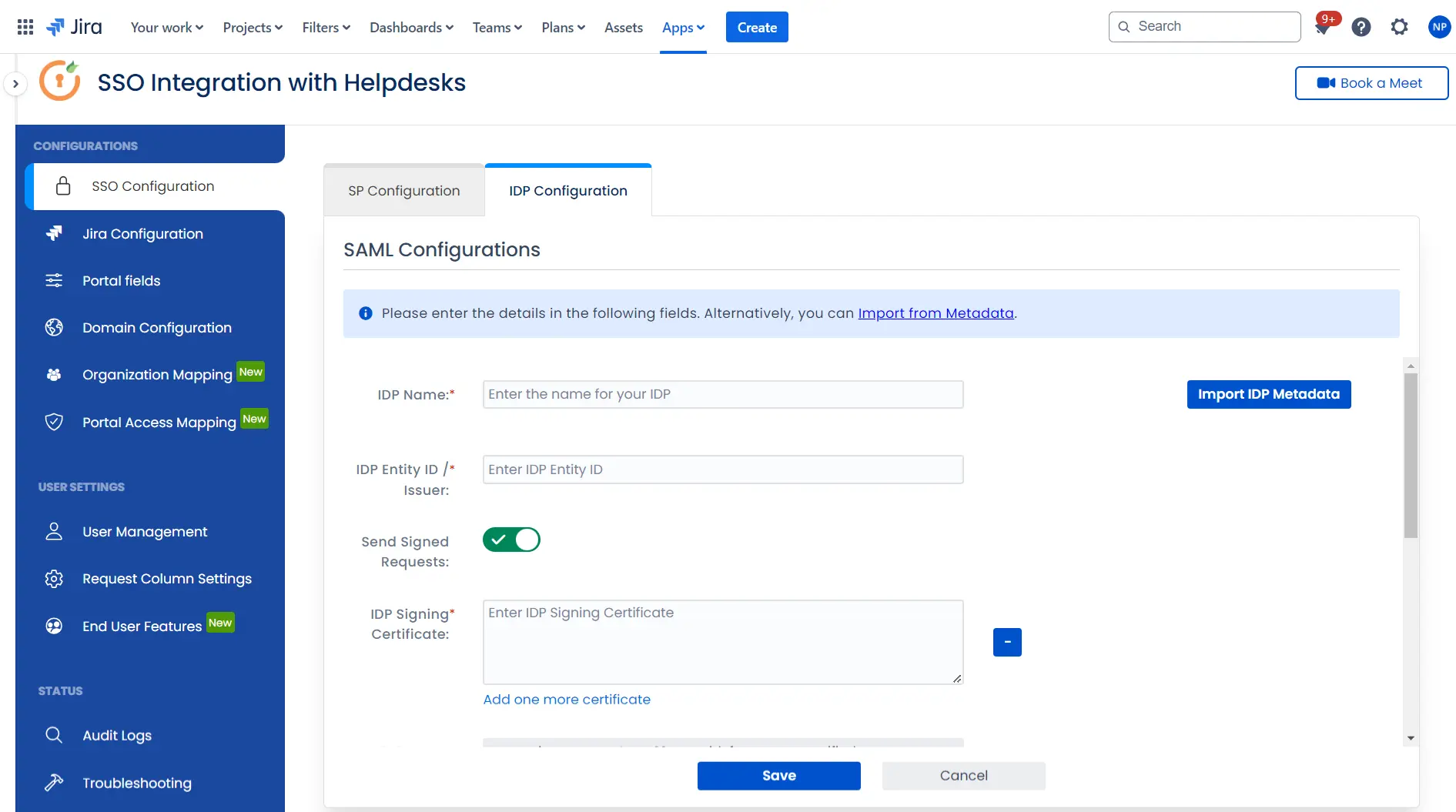
Once you have added the IDP metadata, click on Save. If the IDP has been added successfully, Click on the Test Configuration button to test if the IDP was added successfully.
Step 3: Integrate Atlassian HelpDesk with JSM SSO
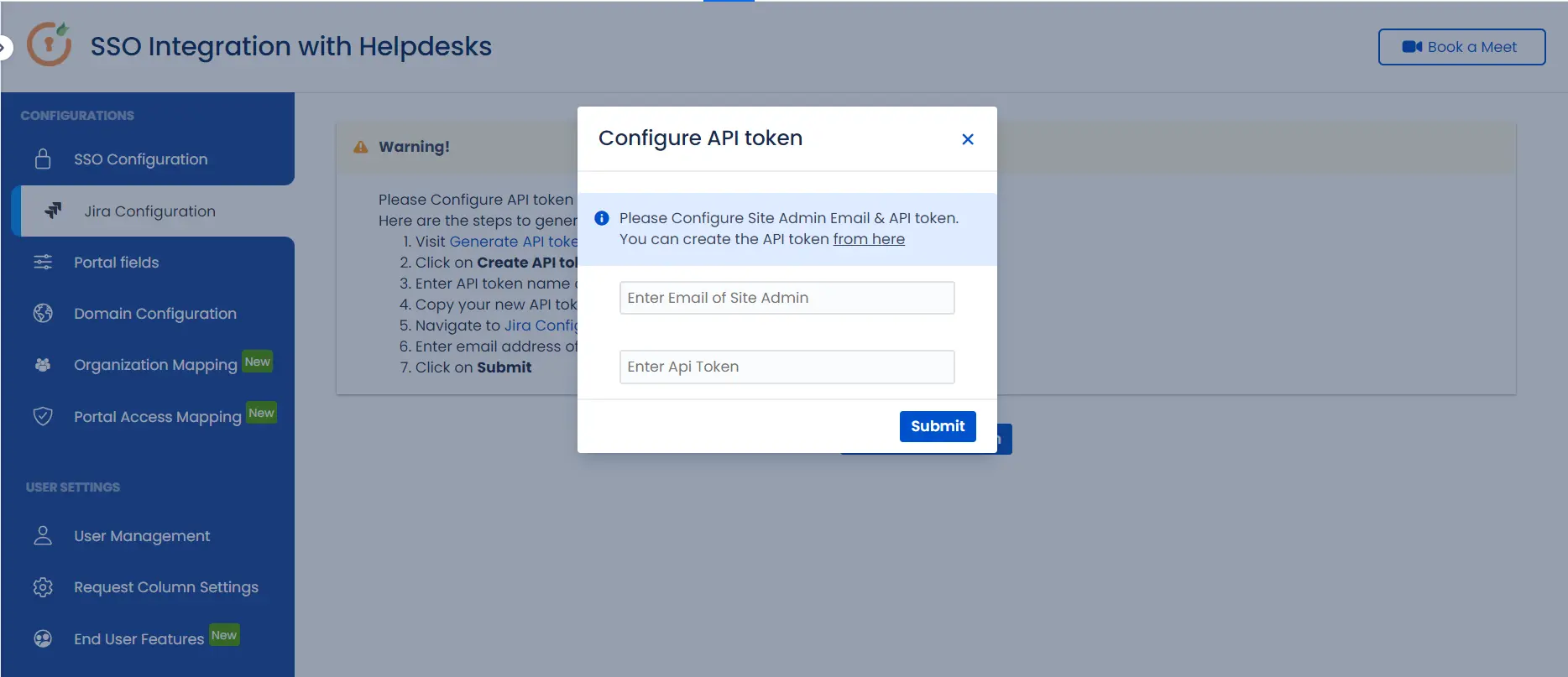
- Click on the Configure API Token and configure the Service Account API token with the email.
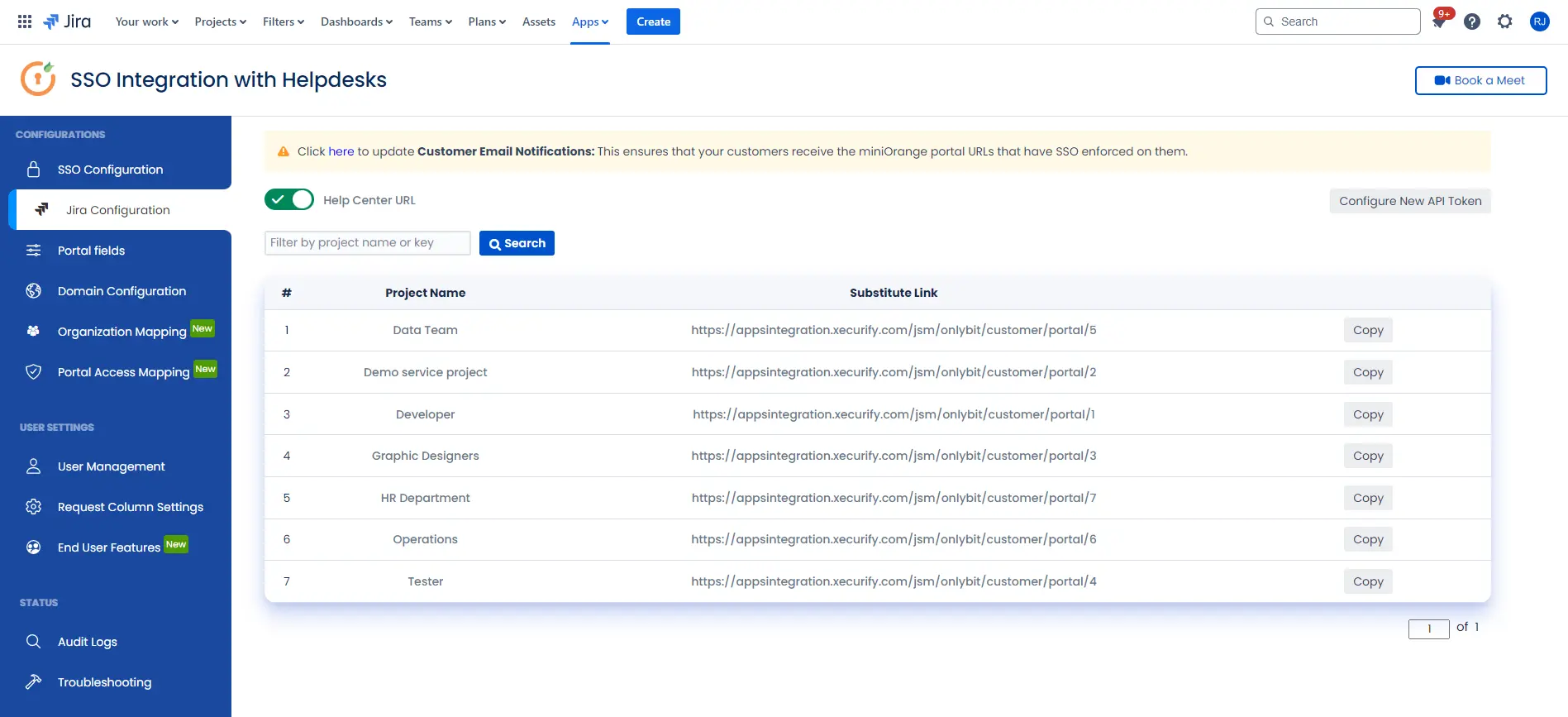
- After successful configuration of API token all the service desk projects with respective links will be displayed. These substituted links will be used by customers for accessing particular projects with SSO.
- Copy any of the substitute links you see for your portals and try accessing it in a private browser window. You would be automatically redirected to your Identity Provider for authentication and would be allowed access to the portal only after successful authentication.
It is necessary to have admin permissions for the service account.
Additional Resources
Did this page help you?

 Try it for free
Try it for free