How to Set Up Two-Factor Authentication (2FA) for Confluence
The miniOrange Two-Factor Authentication (2FA) app is designed to help you enhance security for your Confluence. In this comprehensive guide, we will navigate you through the step-by-step process of configuring 2FA for Confluence. By the end of this walkthrough, you will have fortified your platform with an additional layer of security, safeguarding your registered end-users.
Video Setup Guide
Pre-requisites
- Confluence is installed and configured on your system.
- Admin credentials for Confluence.
- A valid Confluence Server or Data Center license.
Before configuring the miniOrange Two-Factor Authentication (2FA) App for Confluence, ensure you have the following:
Download and Installation
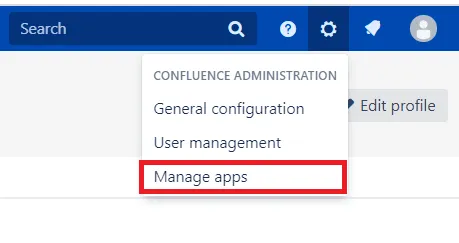
- Log into your Confluence instance as an admin.
- Navigate to the Settings menu and click on Manage Apps.
- Click on Find new apps or Find new add-ons from the left-hand side of the page.
- Use the search function to find mO Two-Factor Authentication (2FA) for Confluence.
- Click Try free to start a new trial or Buy now to purchase a license for the plugin.
- Enter your information and click Generate license when redirected to MyAtlassian.
- Click Apply license to complete the installation.
1: Configuring miniOrange 2FA
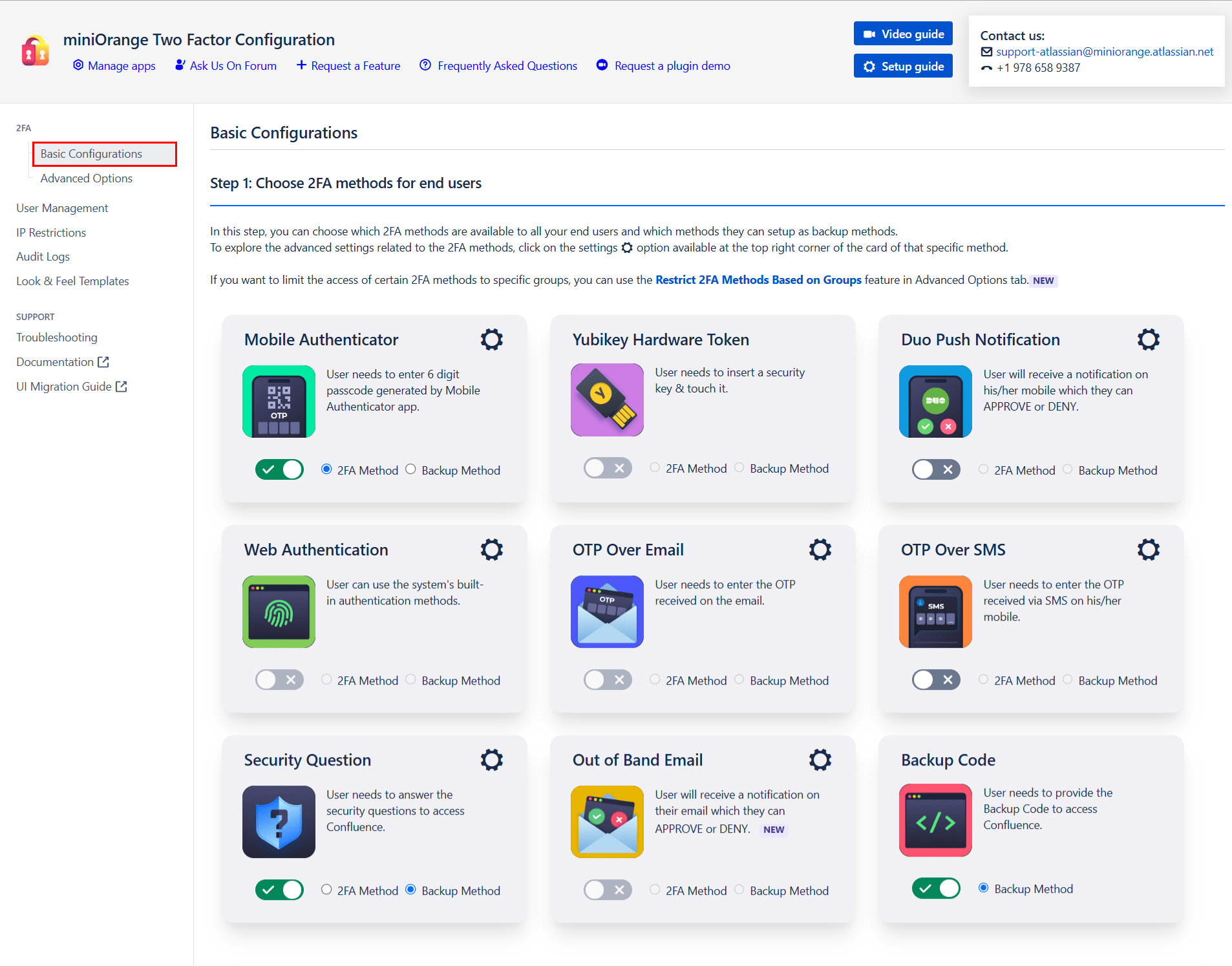
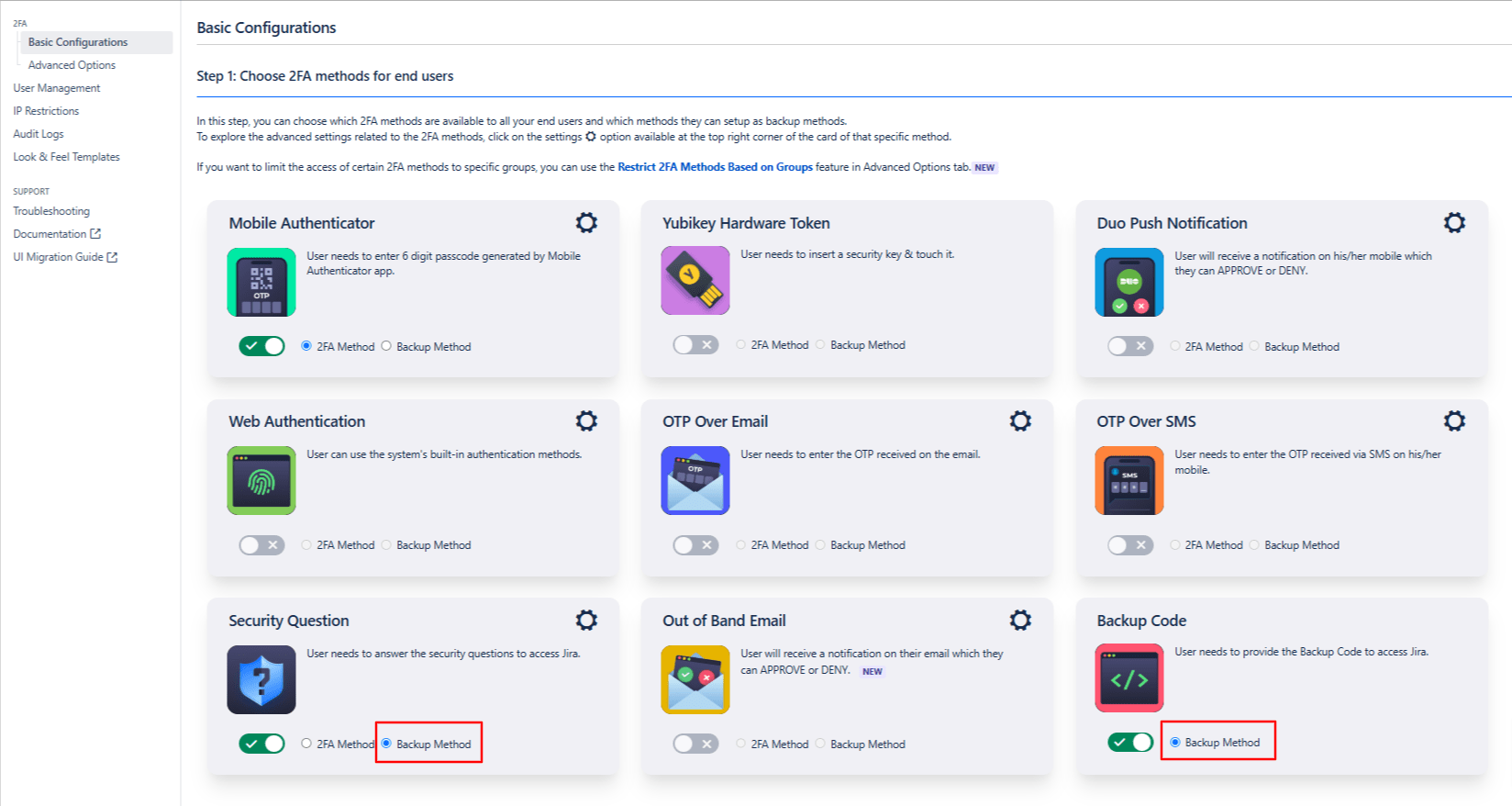
- Choose 2FA Methods: The miniOrange 2FA add-on offers users a range of 2FA methods, including OTP, KBA, TOTP, and more, for authentication. You can enable the desired 2FA methods from the provided list during plugin configuration. To enable the chosen methods for your users, you just have to select the 2FA Method option and toggle it active.
- Enable Backup Method:To ensure access during emergencies or when users cannot access their primary 2FA method, our app also provides you with a backup authentication method. You can choose any of the listed 2FA methods as your backup by selecting the Backup Method option and toggling it active.
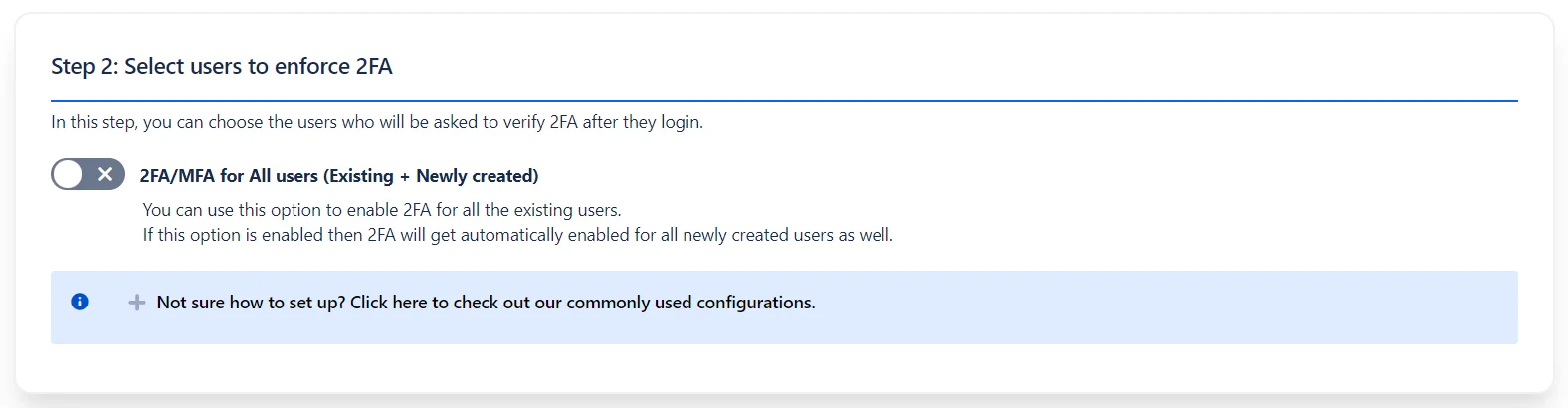
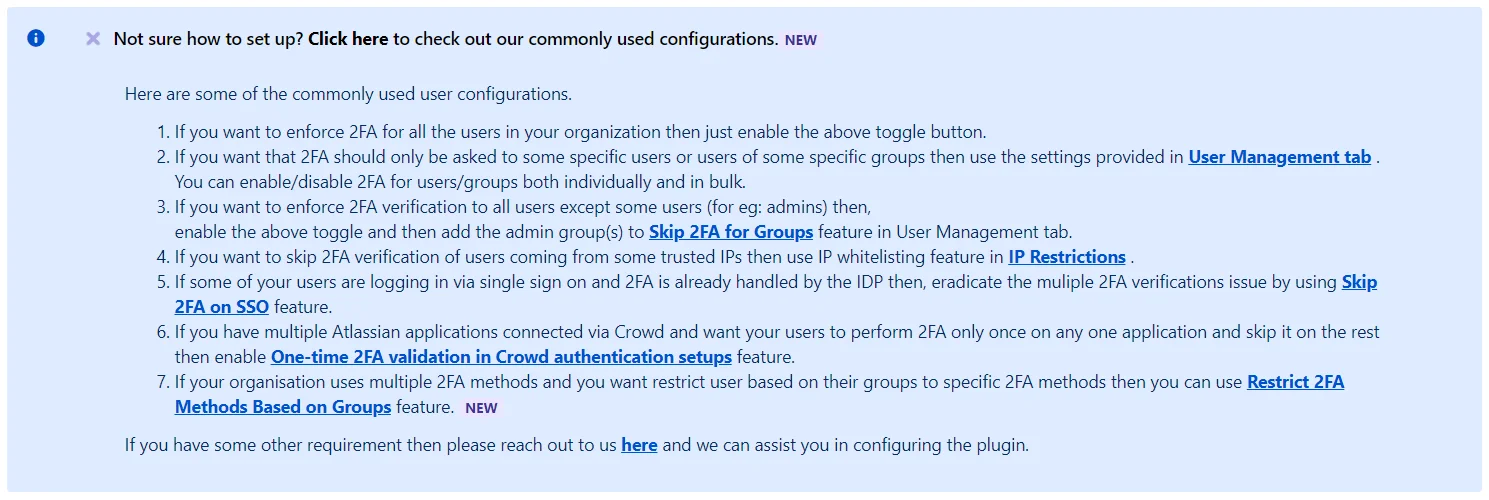
- Select Users to Enforce 2FA: Once the required 2FA methods are enabled, select the users who will be required to use 2FA.
- Use the Enable 2FA/MFA for All Users option to apply 2FA to all existing users and automatically enable it for newly created users.
- You can customize the 2FA settings based on your requirements. Enable, disable, or skip 2FA for users or groups individually, in bulk, or based on their IP addresses.
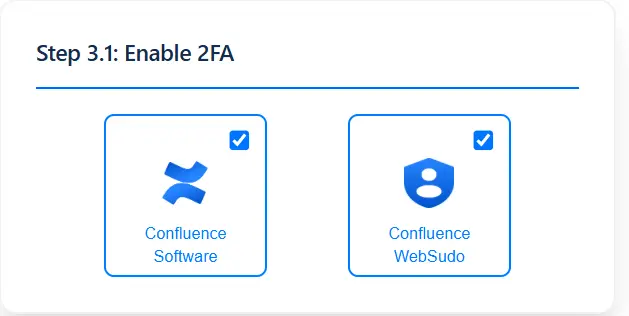
- Choose the platform where you want to enforce 2FA—Confluence Software
- To further enhance security, you can also enable 2FA for Confluence WebSudo. This feature requires administrators to complete a 2FA challenge when performing admin-level actions, even after logging in via WebSudo with their credentials.
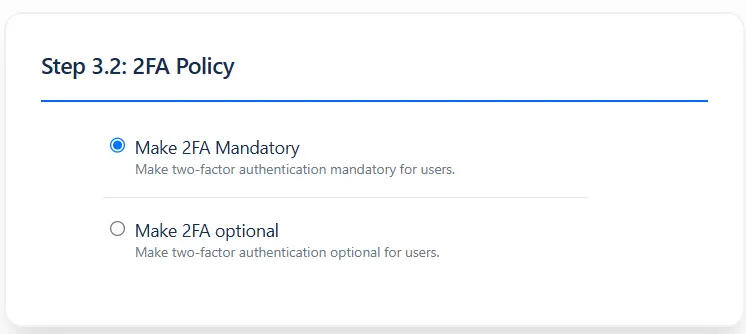
- Make 2FA Mandatory – Enforces 2FA for all users. Access is only permitted once 2FA is configured.
- Make 2FA Optional – Allows users to decide whether or not to enable 2FA on their accounts.
Follow these steps to configure and enable the miniOrange 2FA app for your Confluence users:
Choose Where to Enforce 2FA:
2FA Policy (Optional):
2: How the user can Configure the 2FA
Authentication Methods
3: Advanced Security Features
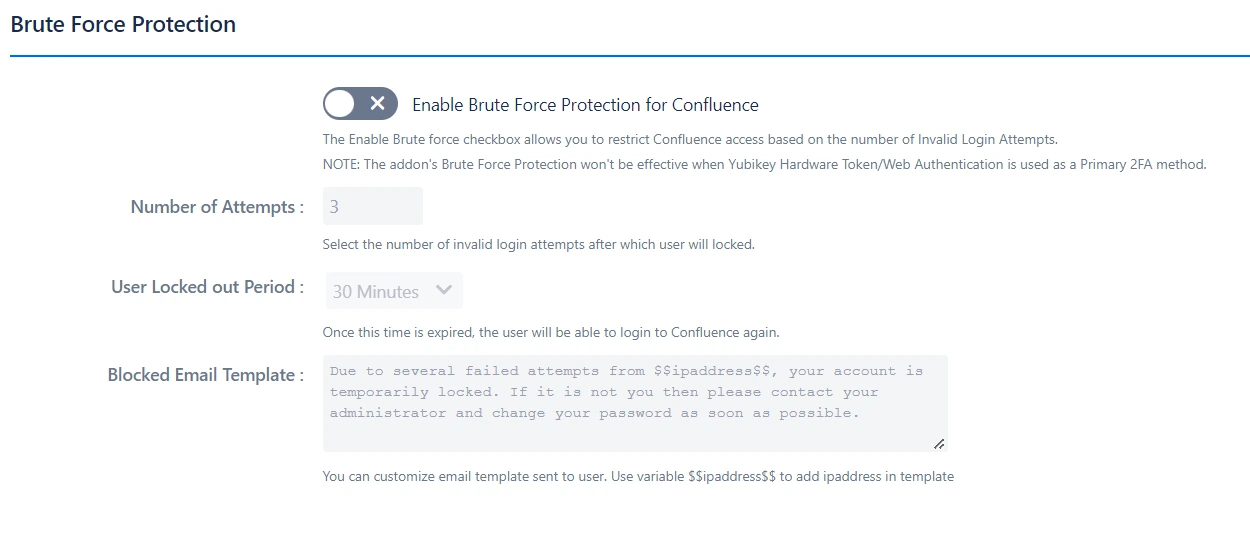
 3.1 Brute Force Configuration
3.1 Brute Force Configuration
- Check the Enable Brute Force Protection for Confluence box.
- Set the number of invalid login attempts that will trigger a lockout.
- Define the duration for which the user will remain locked out and unable to access Confluence.
Brute Force Configuration helps restrict access to your Confluence application after a specified number of invalid
2FA login attempts within a set period.
To enable this feature:
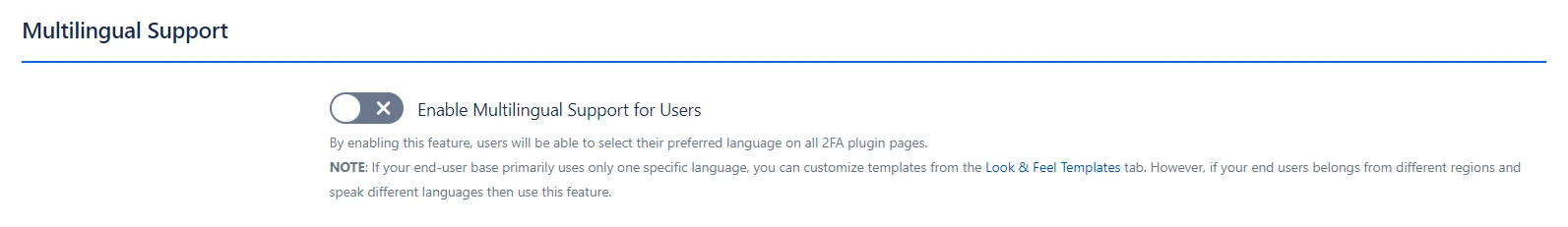
 3.2 Multilingual Support
3.2 Multilingual Support
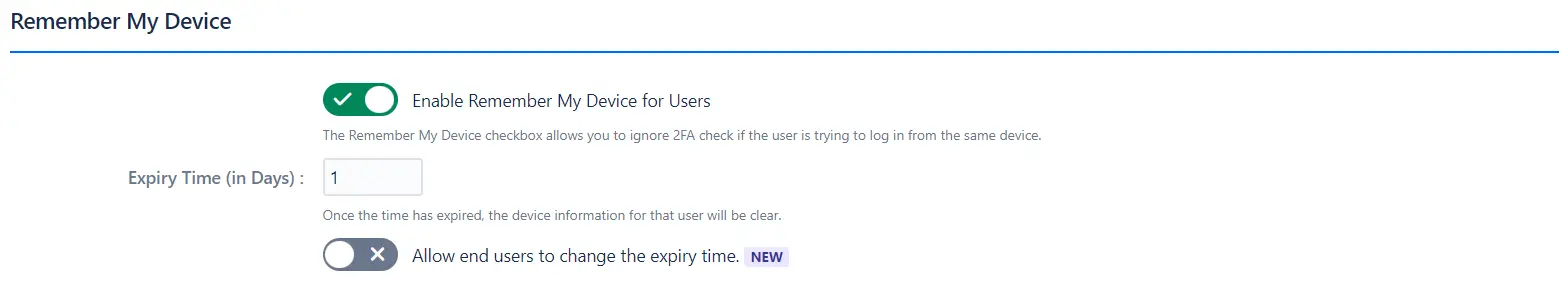
 3.3 Remember My Device
3.3 Remember My Device
- Check the Remember My Device box.
- Enter the number of days for which the device will be remembered in the Expiry Time (in Days) field.
- You also have the option to allow end users to change their respective expiry times.
This feature allows users to skip the 2FA check when logging in from the same device.
To enable:
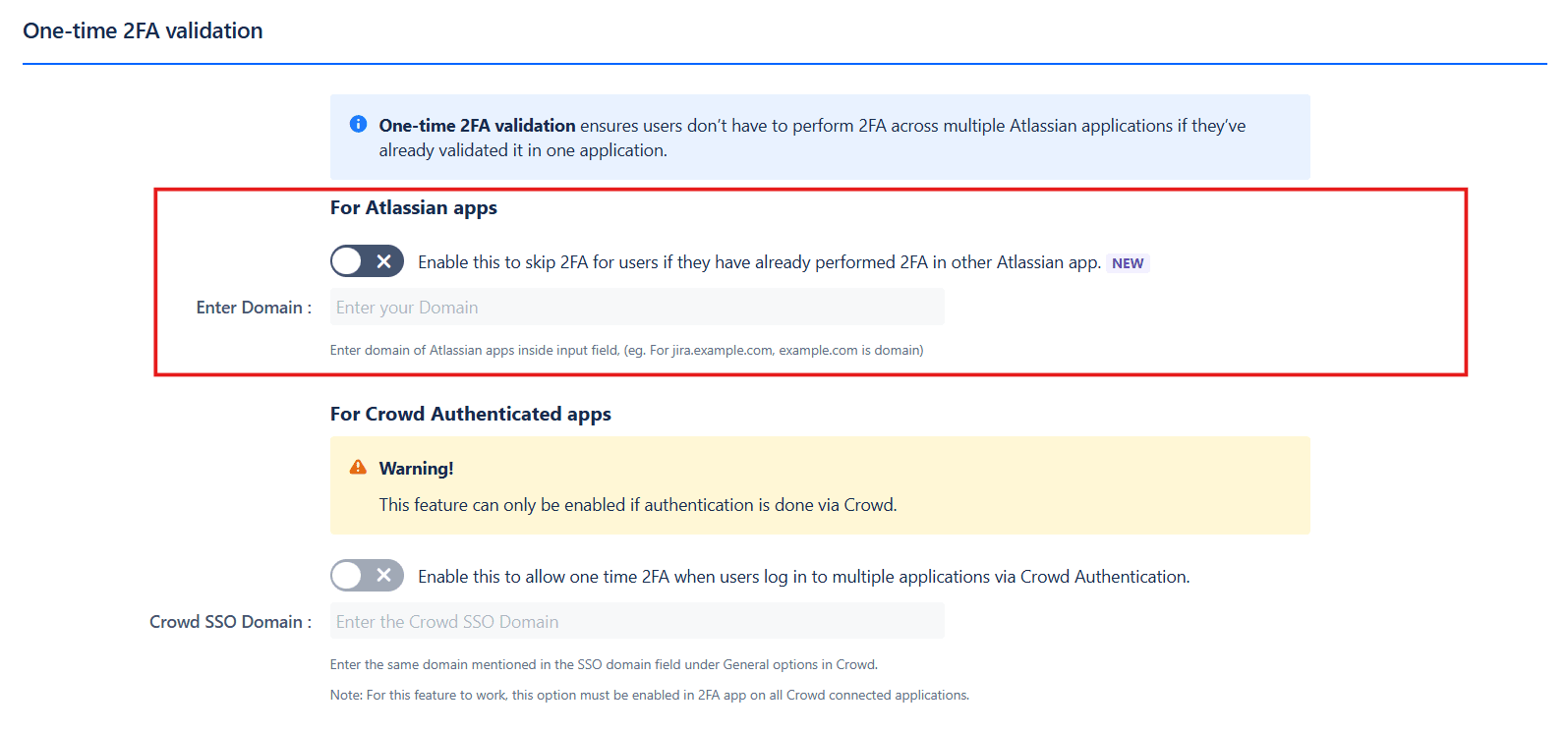
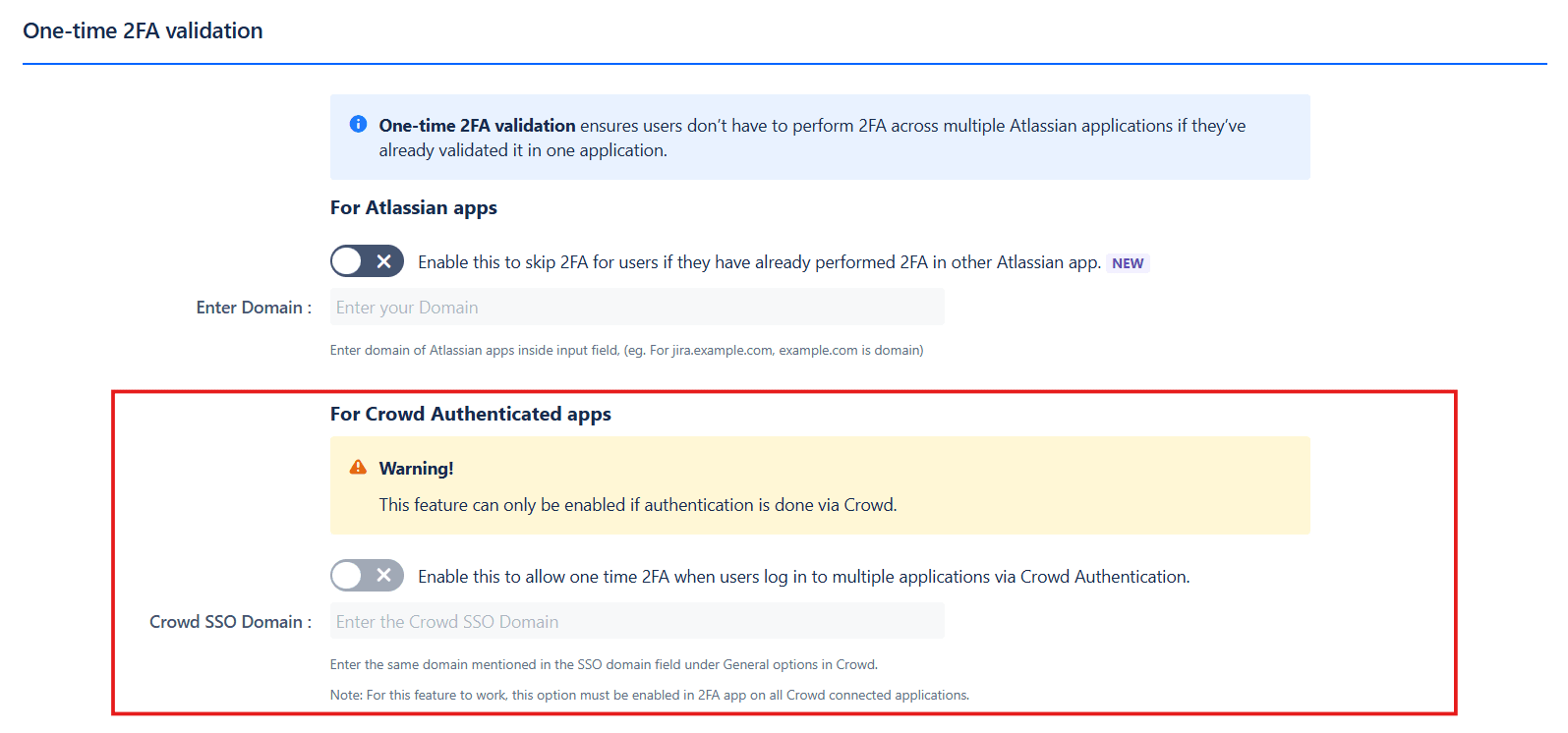
 3.4 One-Time 2FA Validation
3.4 One-Time 2FA Validation
- Enable the toggle.
- Enter the parent domain and configure the secret key.
- Ensure the same configuration is applied across all Atlassian applications where you want this feature enabled.
- Users will need to validate 2FA in one application, and it will be skipped in other Atlassian applications.
- Toggle this feature to enable in the crowd connected applications where you want to bypass 2FA.
- Users will need to validate 2FA in one application, and it will be skipped in other connected applications.
For Atlassian Apps:
This feature allows users to bypass 2FA in Atlassian applications after successful 2FA validation in any one of the applications.
To enable:
For Crowd Authenticated apps:
This feature lets users skip 2FA in Crowd-connected applications after a successful 2FA validation any one Atlassian application.
To enable:
Note: This feature is only available if authentication is done via Crowd.
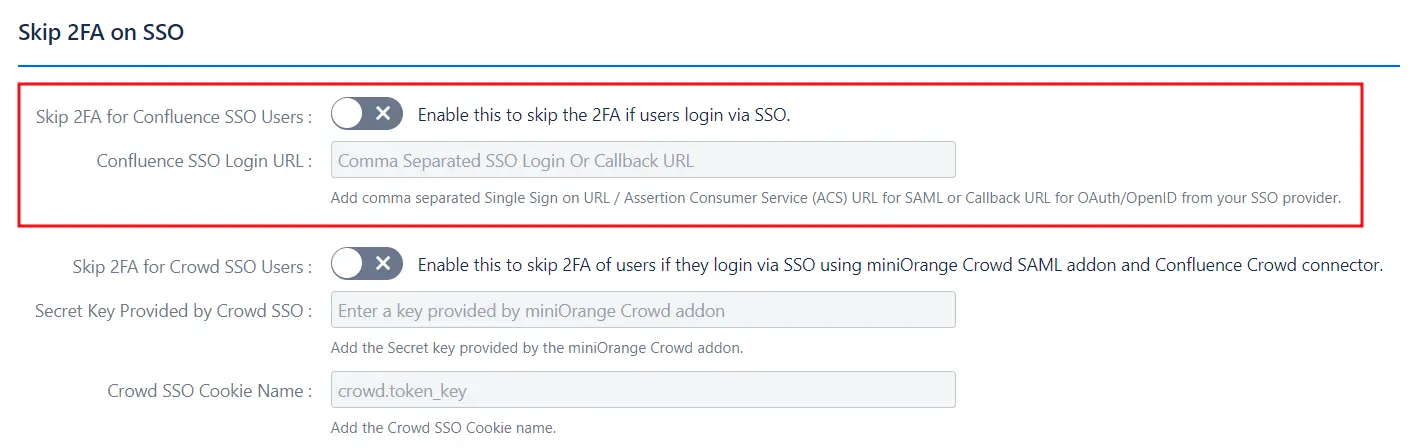
 3.5 Skip 2FA for SSO Users
3.5 Skip 2FA for SSO Users
- Add the Single Sign-On URL for SAML.
- Add the Callback URL for OAuth/OpenID from the SSO Provider.
This feature allows users to skip 2FA if they log in via Single Sign On (SSO) with any Identity Provider (IDP).
To enable this, admins need to:
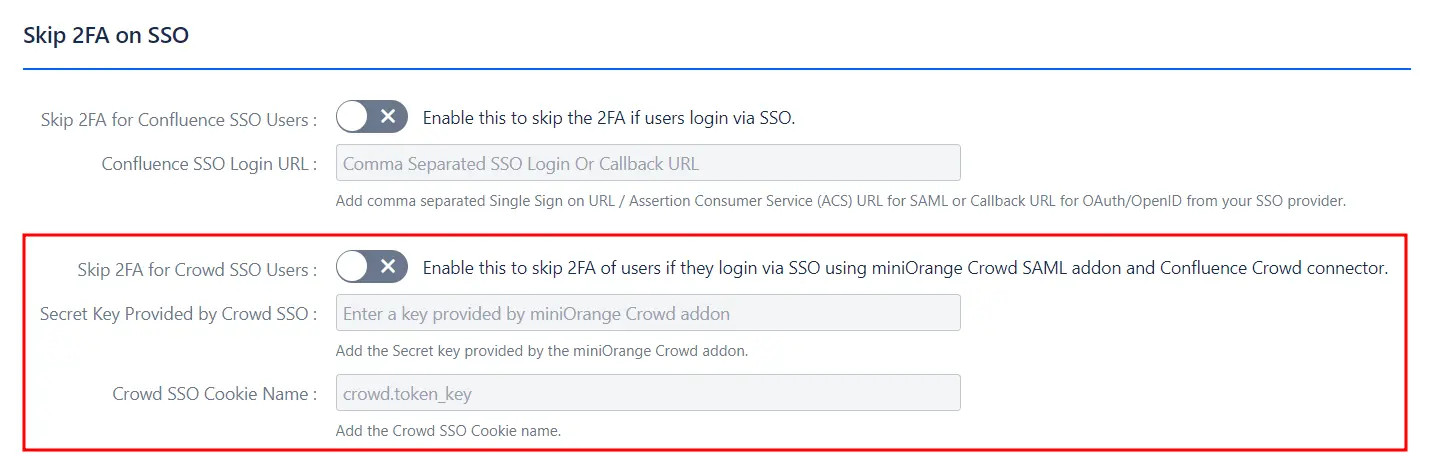
 3.6 Skip 2FA for Crowd SSO Users
3.6 Skip 2FA for Crowd SSO Users
- Add the Secret Key provided by the miniOrange Crowd add-on.
- Add the Crowd SSO cookie name.
This feature allows users to skip 2FA when logging in via SSO using the miniOrange Crowd SAML add-on and Confluence Crowd connector.
To enable this, admins need to:
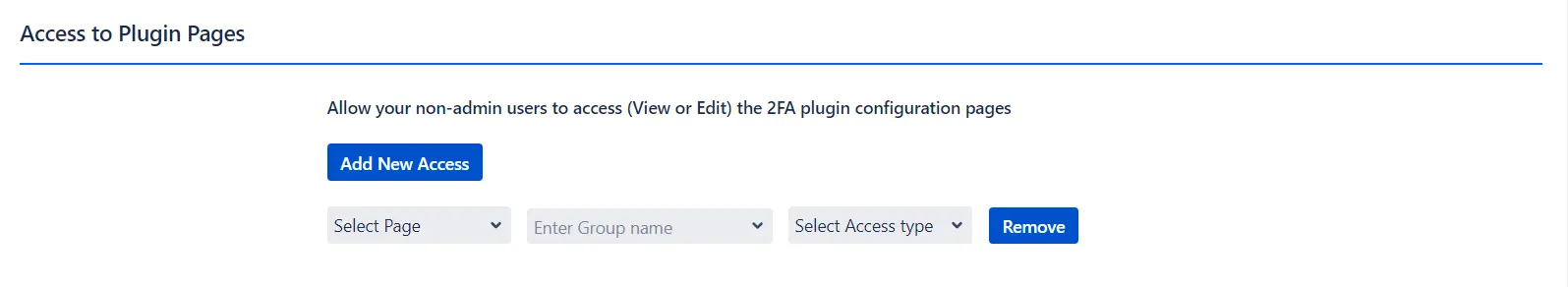
 3.7 Access to Plugin Pages
3.7 Access to Plugin Pages
- Navigate to the Advanced Options Tab and scroll down to the Access to Plugin Pages section.
- Next, specify the Page, Group Name, and Access Type from their respective drop down lists.
- To add more access permissions, click on Add New Access and follow the same process.
By default, only administrators have access to the plugin pages. This feature allows you to define and customise
access permissions for specific user groups, granting them the ability to view and manage designated plugin pages.
By configuring access settings, you can ensure that the right users have the necessary permissions to perform
their tasks, enhancing collaboration and security within your organization.
To enable this, admins need to:
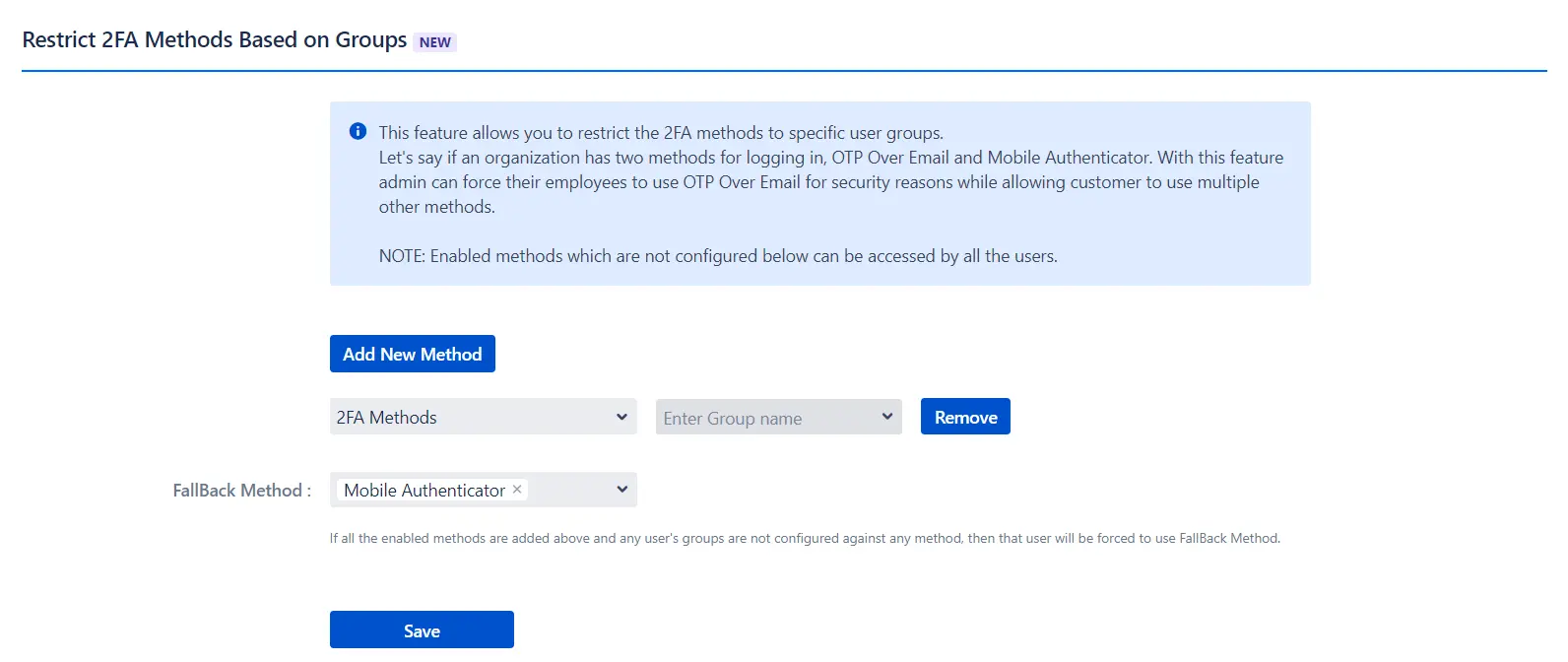
 3.8 Group Based 2FA
3.8 Group Based 2FA
- Navigate to the Advanced Options Tab and scroll down to the Restrict 2FA Methods Based on Groups section.
- Next, click on Add New Method.
- Specify the 2FA method along with the group for which it is to be restricted.
- Finally, select a Fallback Method for the group to use if they’re not configured against any method.
This feature gives administrators the ability to limit specific 2FA methods to certain user groups. For example,
an organization might offer two login methods, such as OTP Over Email and Mobile Authenticator.
With this feature, admins can require employees to use OTP Over Email for enhanced security, while allowing
customers to select a method of their choice.
To enable this, admins need to:
Any enabled methods not specified in this configuration will remain available to all users by default.
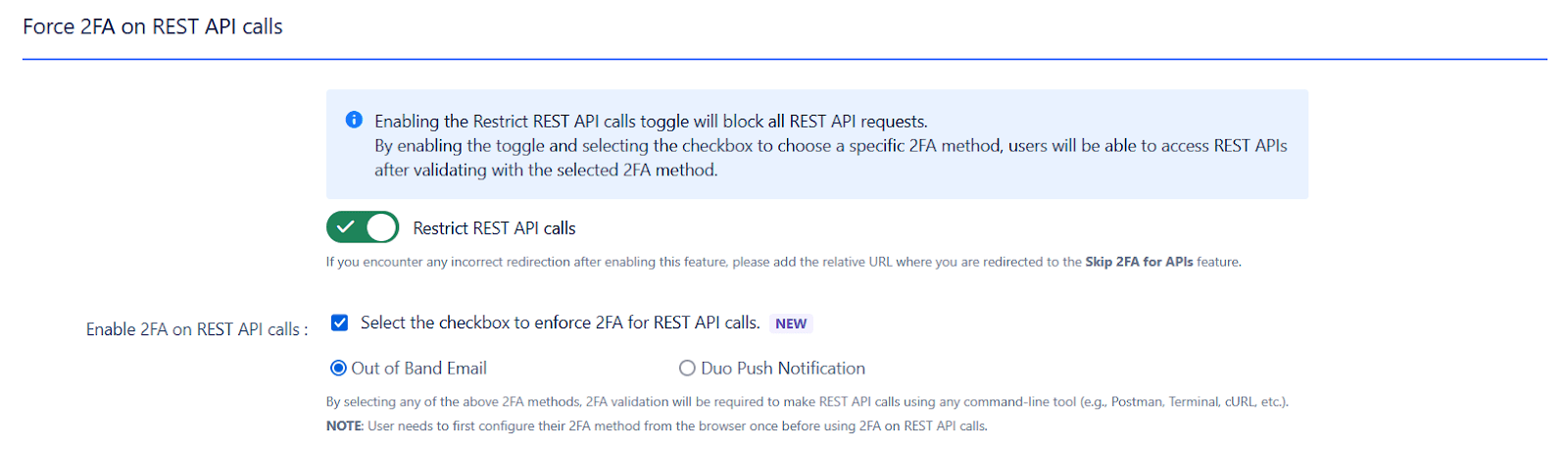
 3.9 Enable 2FA on REST API Calls
3.9 Enable 2FA on REST API Calls
- Navigate to the Advanced Options Tab.
- Scroll down to the Force 2FA on REST API calls section and enable the toggle button.
- To enforce 2FA, check the box and select preferred verification method
This feature allows you to restrict all REST API calls and enforce Multi-Factor Authentication (MFA) for enhanced security. When the "Restrict REST API Calls" toggle is enabled, all API requests are blocked. To enforce 2FA, you must check the box and select a preferred verification method. Once enabled, every API request will require validation of the selected 2FA method, reducing the risk of unauthorized access and protecting sensitive data.
To enable this, admins need to:
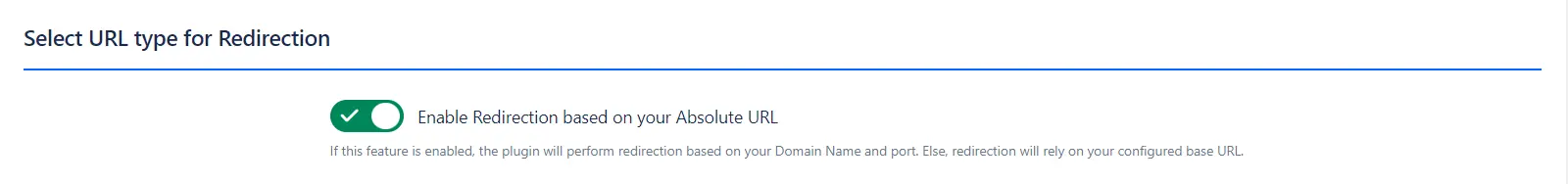
This feature allows you to configure automatic redirection after successful 2FA authentication based on your
domain name and port. If the domain name and port are not specified, the plugin will rely on the configured base
URL for redirection.
This ensures that users are seamlessly directed to the intended resource, such as a dashboard or home page,
enhancing their overall experience while navigating your application.
To enable this, admins need to:
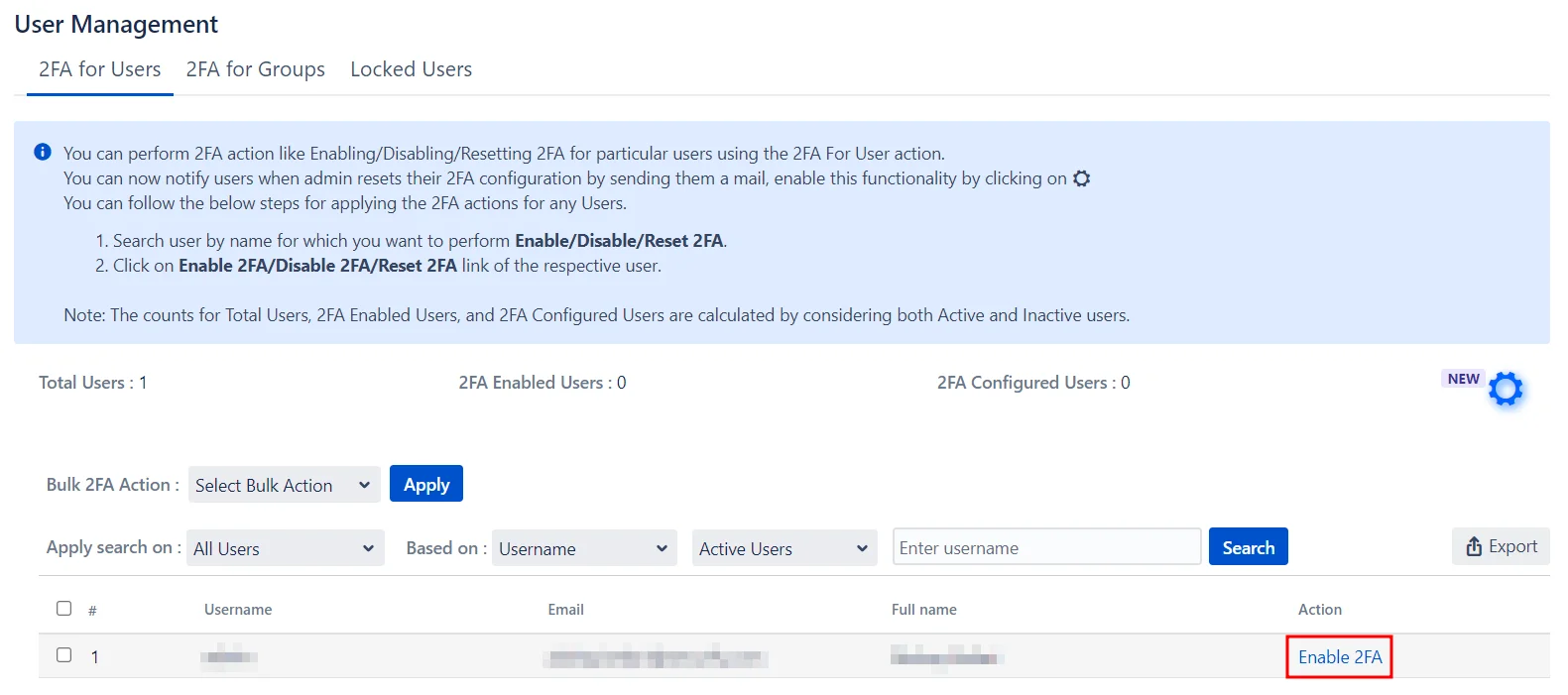
4: User Management
The miniOrange 2FA app has provisions for efficiently managing 2FA settings for individual users, multiple users,
single groups, and multiple groups.
Let's take a look at how you can manage 2FA for your users and groups.
Enabling 2FA for Single Users:
- Search for the user by their name in the search bar.
- Next, select the desired action from the Action column.
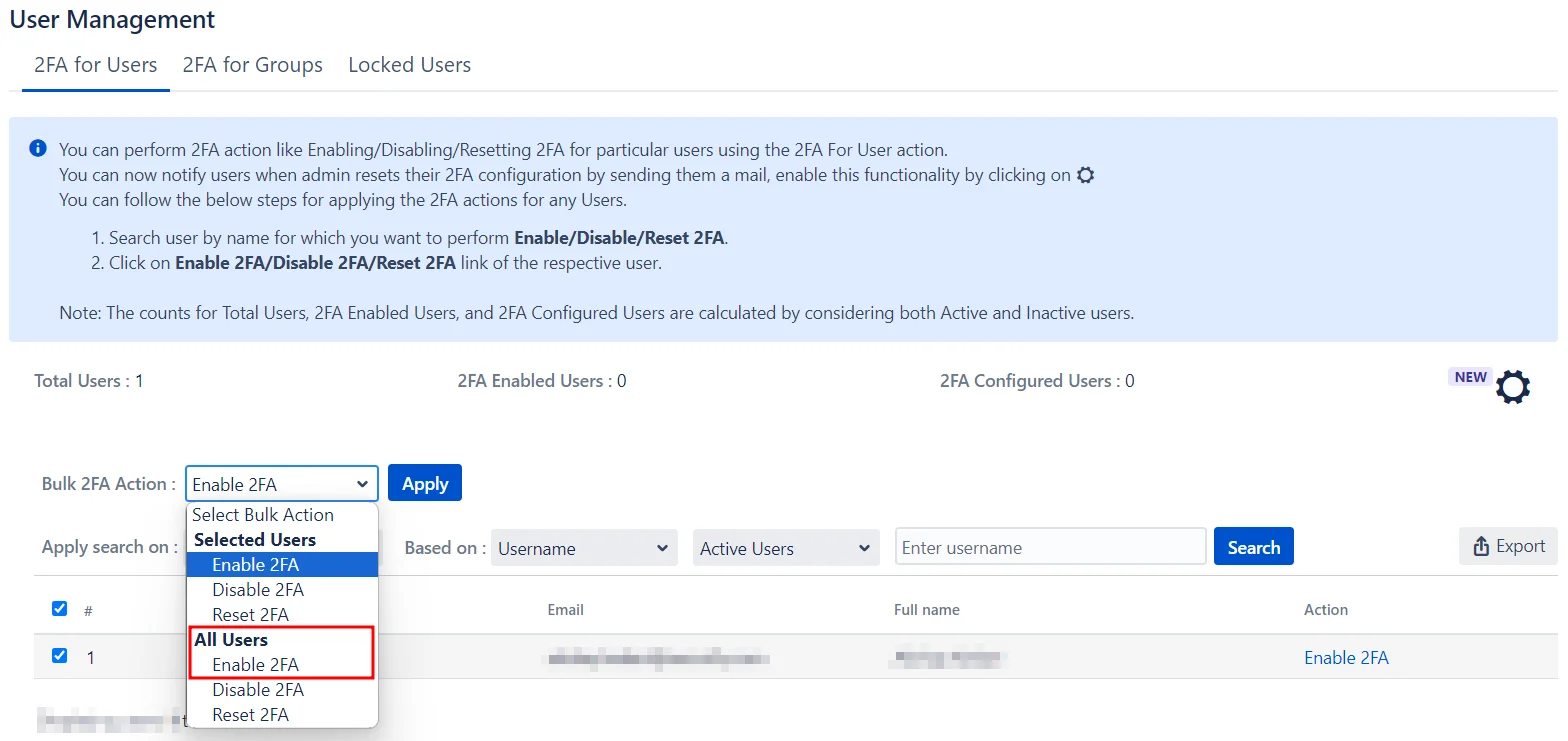
Enabling 2FA for multiple Users:
- Select the users from the list.
- Choose the desired action from the Bulk 2FA Action drop-down menu.
- Click Apply.
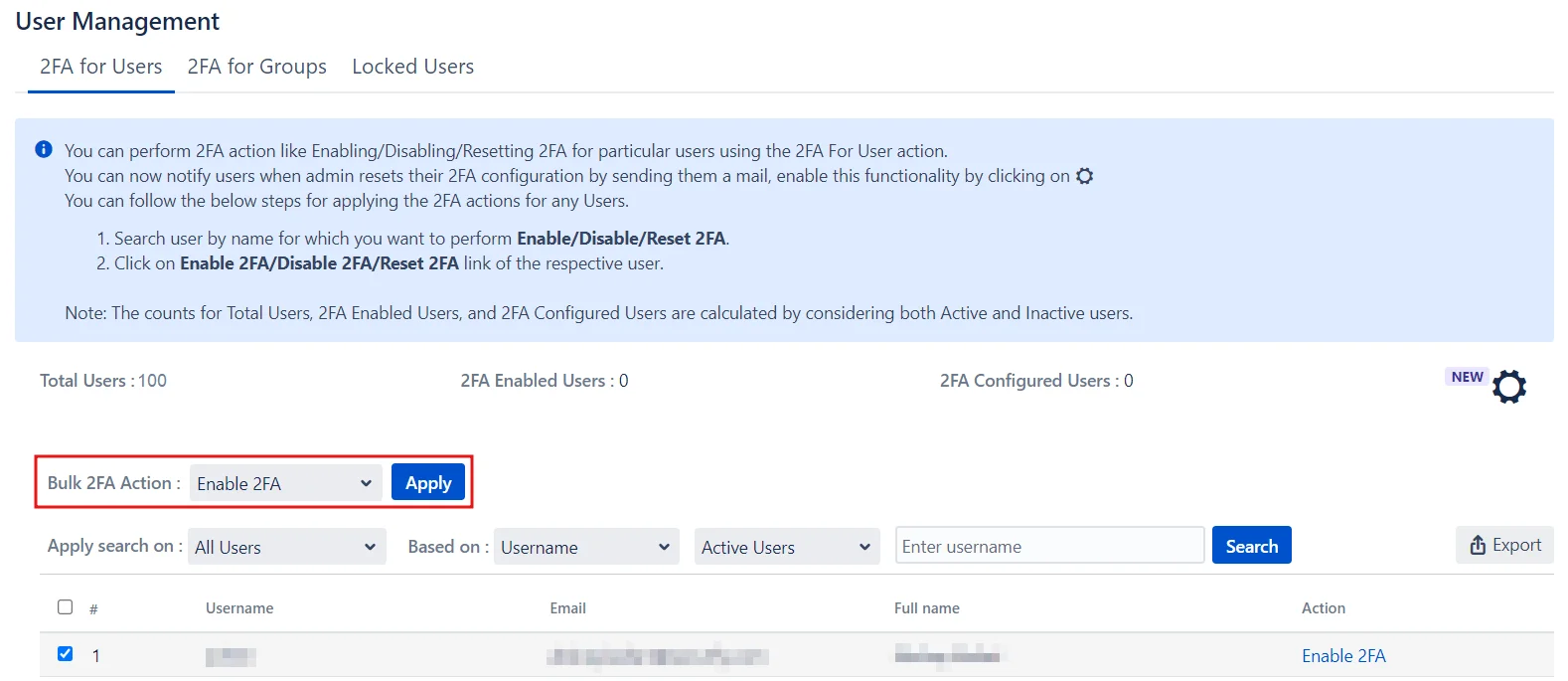
Enabling 2FA for All Users:
- Go to the Bulk 2FA Action drop-down menu under the All Users section.
- Select the required action.
- Click Apply.
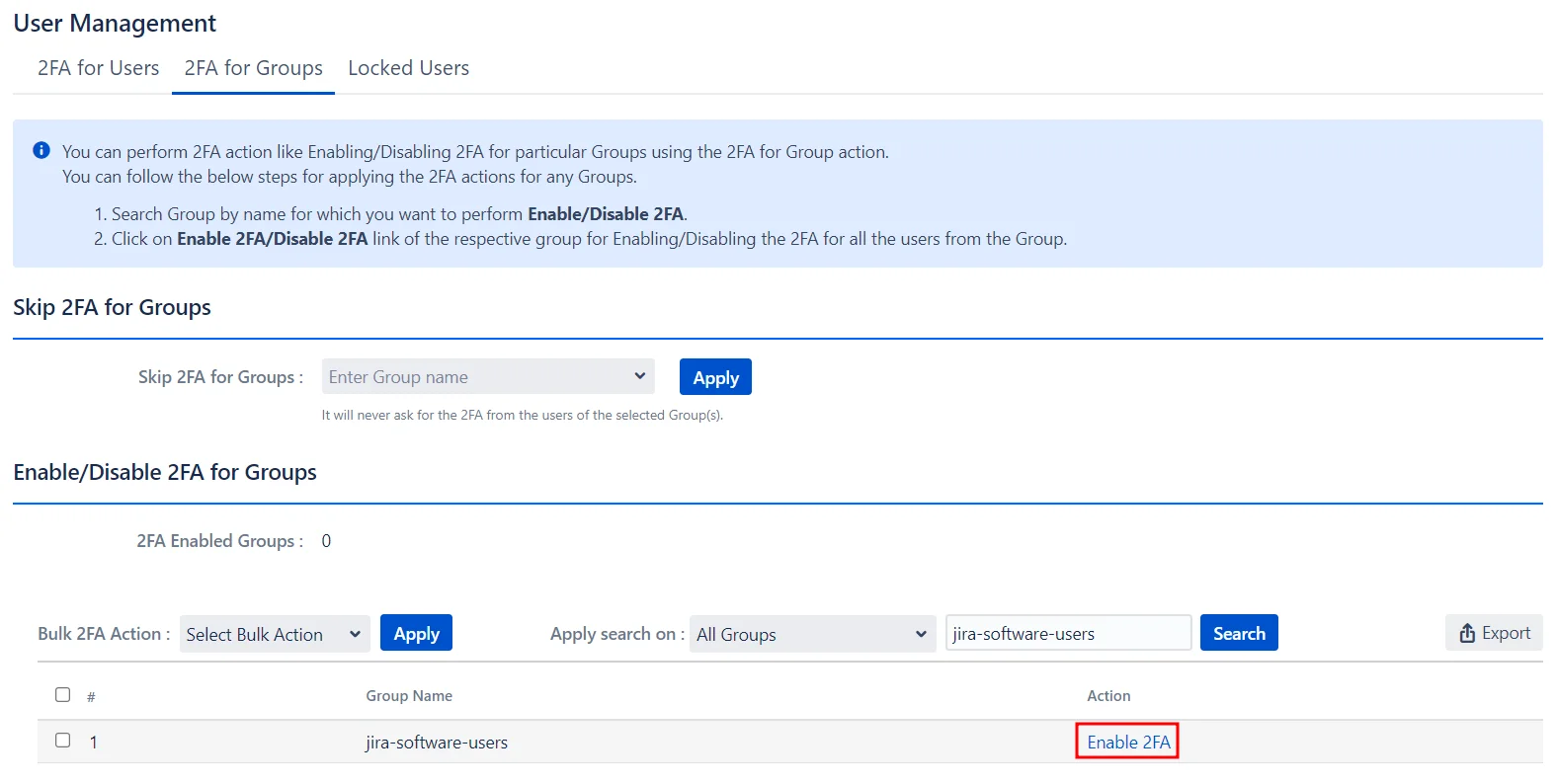
Enabling 2FA for Single Groups:
- Search for the group by its name in the search bar.
- Next, select the desired action from the Action column.
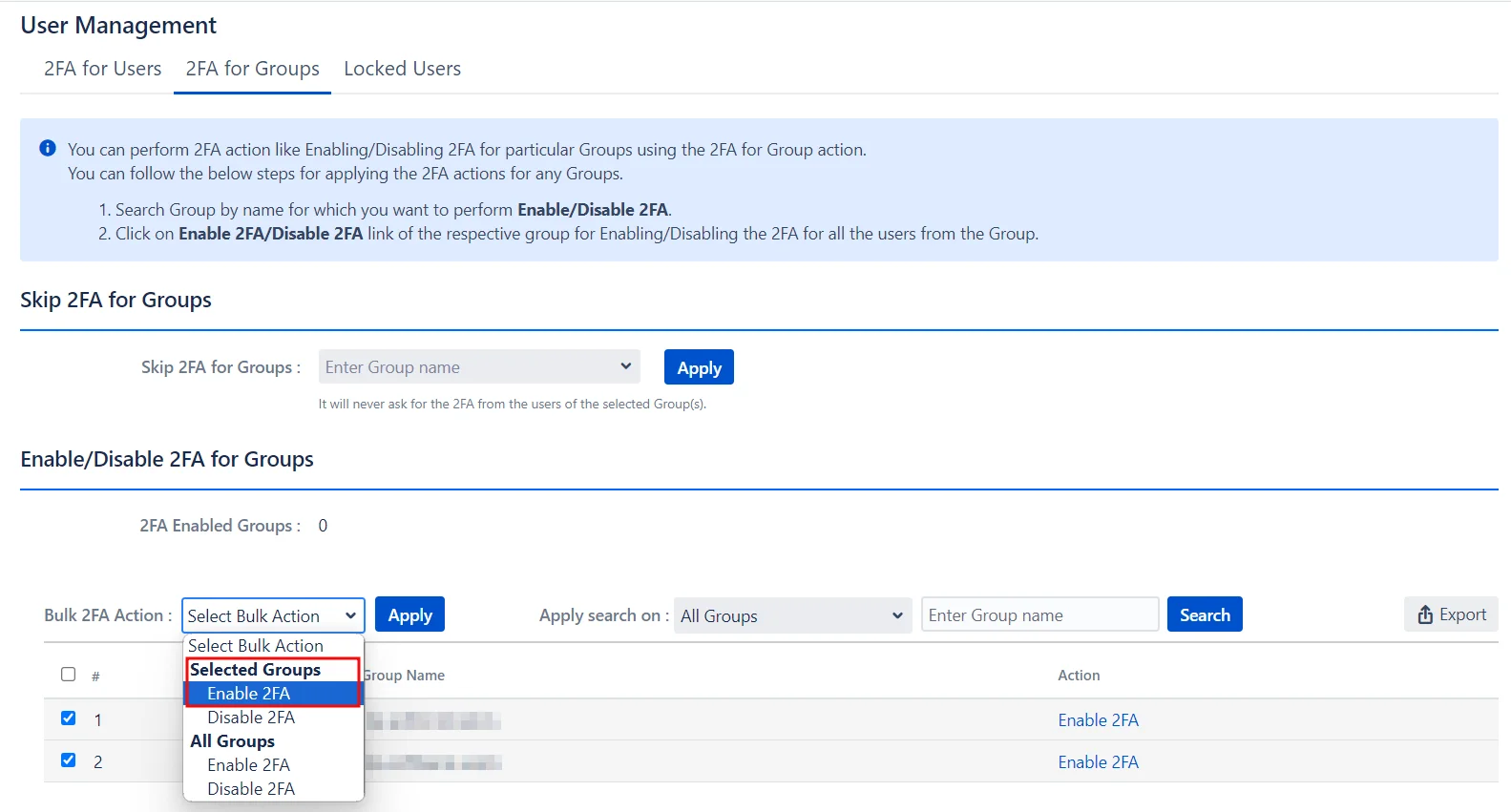
Enabling 2FA for Multiple Groups:
- Select the groups from the list.
- Choose the desired action from the Bulk 2FA Action drop-down menu.
- Click Apply.
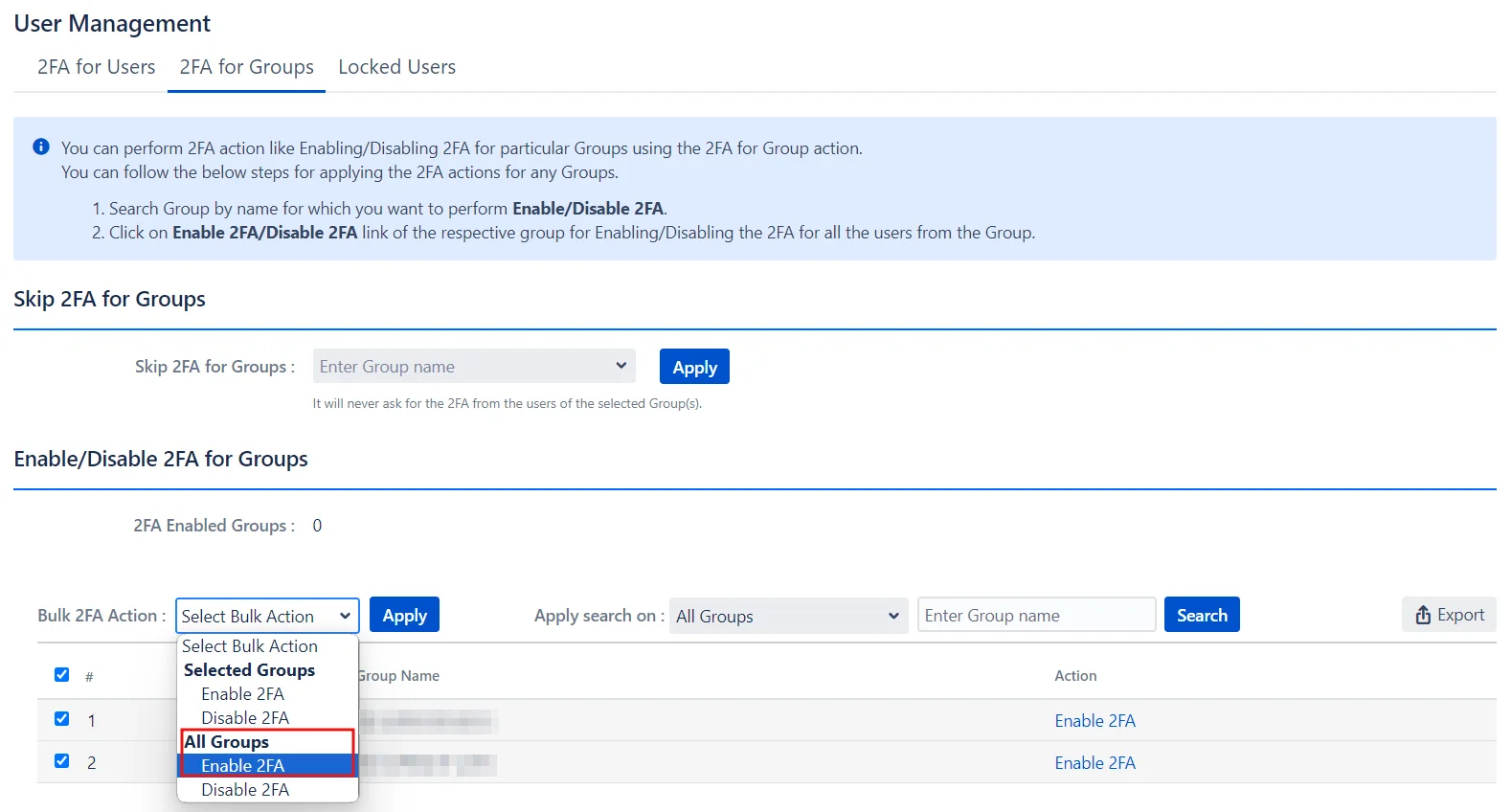
Enabling 2FA for All Groups:
- Go to the Bulk 2FA Action drop-down menu under the All Groups section.
- Select the required action.
- Click Apply.
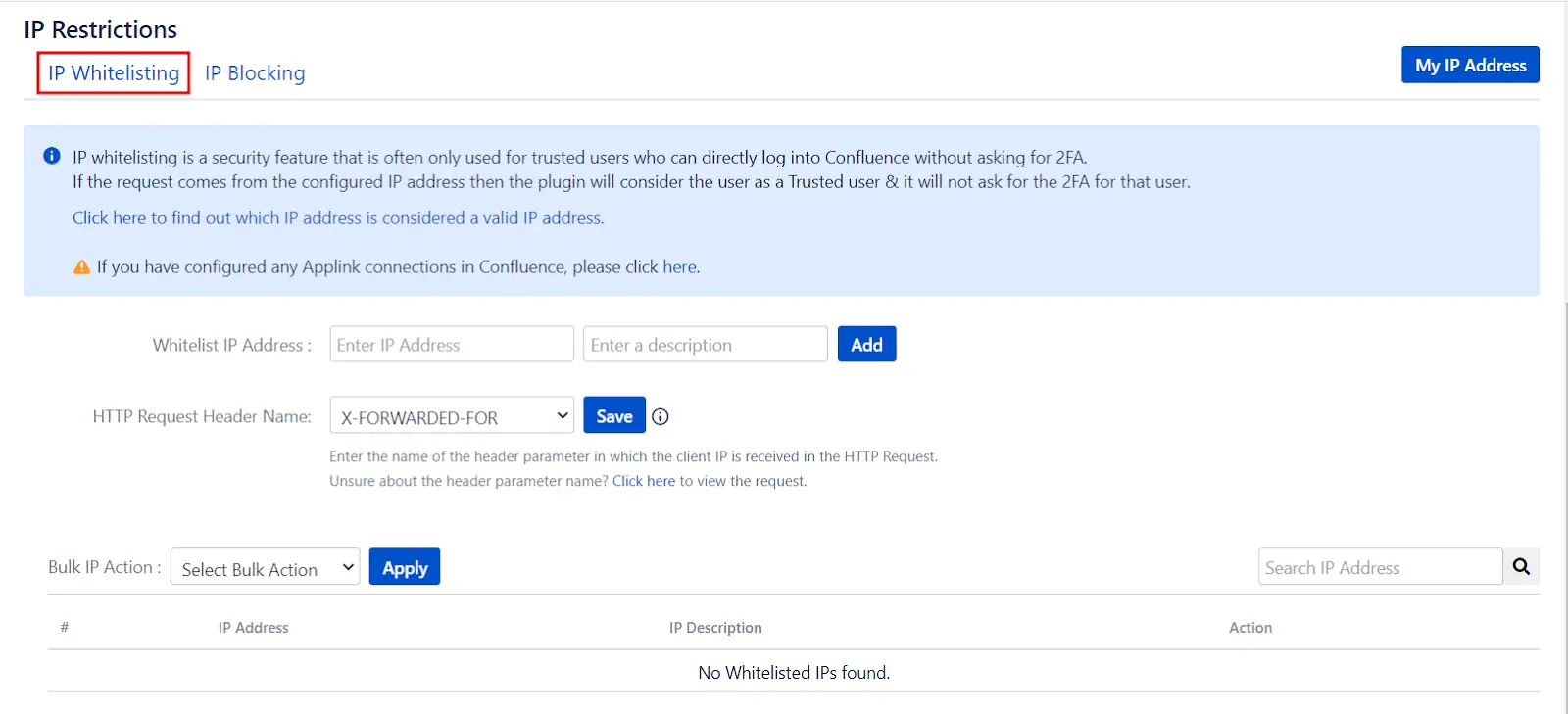
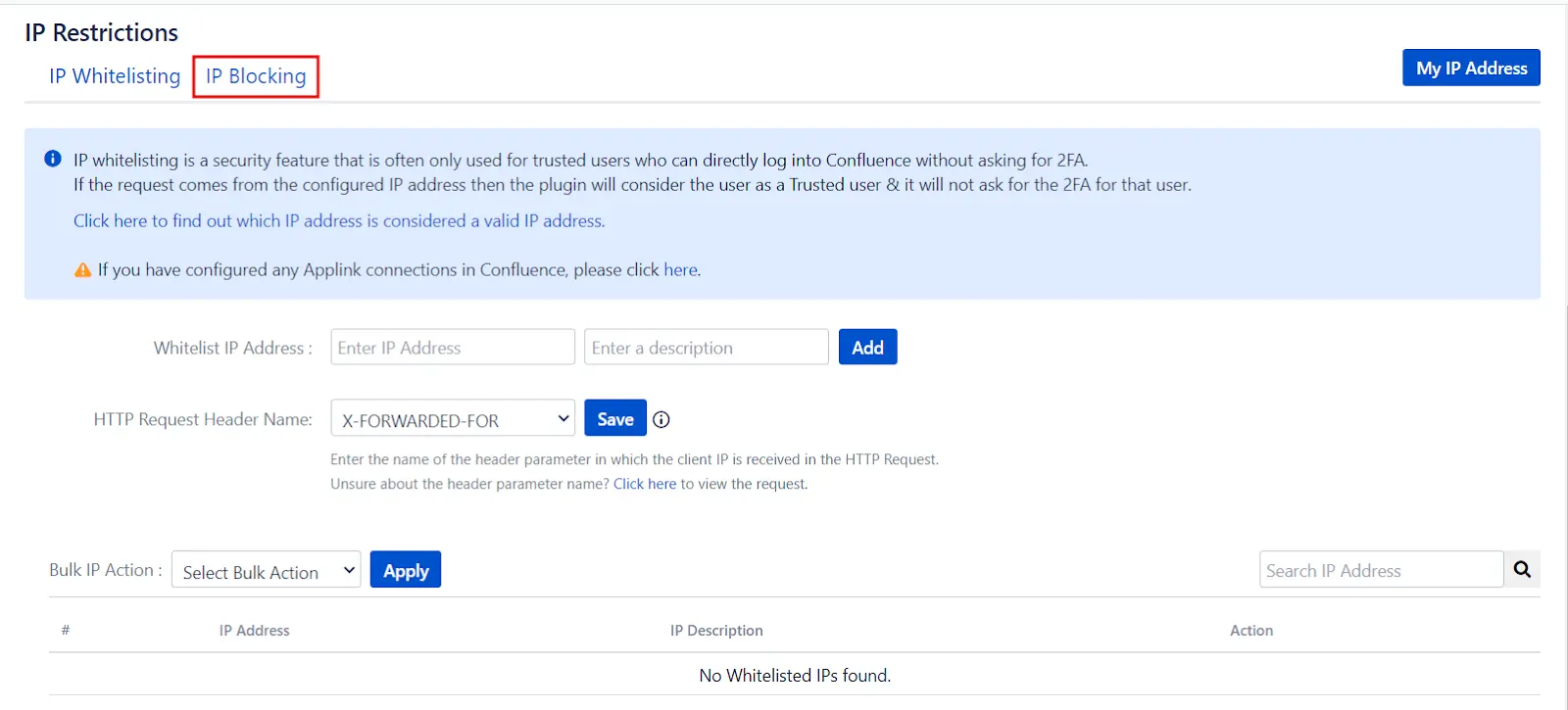
5: IP Restrictions
- IP Whitelisting is a security feature that allows trusted users to log into Confluence without 2FA. To enable IP Whitelisting, enter the trusted IP addresses in the Whitelist IP Address textbox and click Add.
- IP Blocking is an access control mechanism that denies Confluence access to specified IP addresses. Enter the IP addresses you want to block in the Blacklist IP Address textbox, and customize the message for blocked users in the Blocked User Message textbox. Click Save once you’re done to apply these settings.
IP Whitelisting:
IP Blocking:
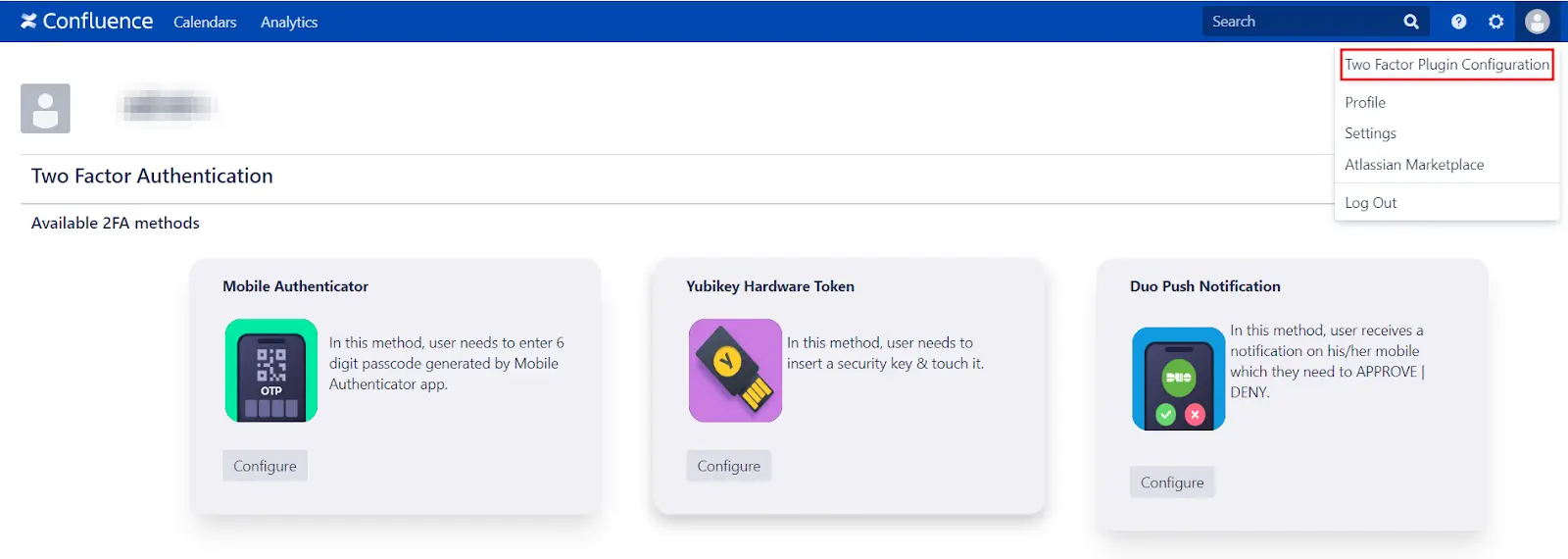
6: Reconfigure 2FA
- End-users can reconfigure their 2FA by navigating to User Profile → Two-factor Plugin Authentication, and accessing the Configure Two Factor (2FA) window. Once inside, they can click on Reset to reconfigure the 2FA method. Users can also configure additional 2FA methods from this window if they haven't done so previously.
Additional Resources
Did this page help you?

 Try it for free
Try it for free

