Introduction
Let’s face it—almost every business uses the cloud in some way. Whether it's running apps, storing data, or using popular tools like Microsoft 365, Slack, Zoom, or Google Meet, the cloud makes work faster and more flexible. But with all this convenience comes a big question: Is your business data on cloud apps really safe?
When you store or share information in the cloud, there’s always a chance it could leak—sometimes by accident, sometimes because of Shadow IT (when employees use unapproved apps), and sometimes through cyberattacks. In fact, without proper controls, sensitive data can easily slip through cracks you didn’t even know existed.
Common Ways Businesses Lose Their Data on the Cloud
1. Accidental Deletion
One of the most common causes of cloud data loss is accidental deletion by employees or administrators. During routine maintenance, file cleanups, or software updates, critical data can unintentionally be deleted. Many cloud services offer a limited recovery window, and once this period is over, the data may become irretrievable. This issue is exacerbated when businesses lack adequate data security strategies.
2. Cyberattacks (Ransomware & Hacking)
Cybercriminals frequently target cloud environments due to the vast amount of sensitive data they store. In ransomware attacks, hackers encrypt data and demand a ransom for its release. In other cases, they may steal or wipe data to damage the organization. Such attacks can exploit weak passwords, phishing scams, or unpatched software vulnerabilities.
3. Misconfigured Cloud Settings
Misconfigurations are a leading cause of data exposure in cloud environments. Many cloud platforms come with default settings that may prioritize ease of use over security. Without proper security configurations, sensitive information could be unintentionally exposed to the public or become vulnerable to overwrites.
4. Hardware or System Failures
Despite high availability and redundancy, hardware malfunctions and system failures can still lead to cloud data loss. Network outages can result in data corruption or loss. Even with backup solutions in place, there is a risk that backups could fail simultaneously.
What is Cloud DLP? How It Prevents Data Loss?
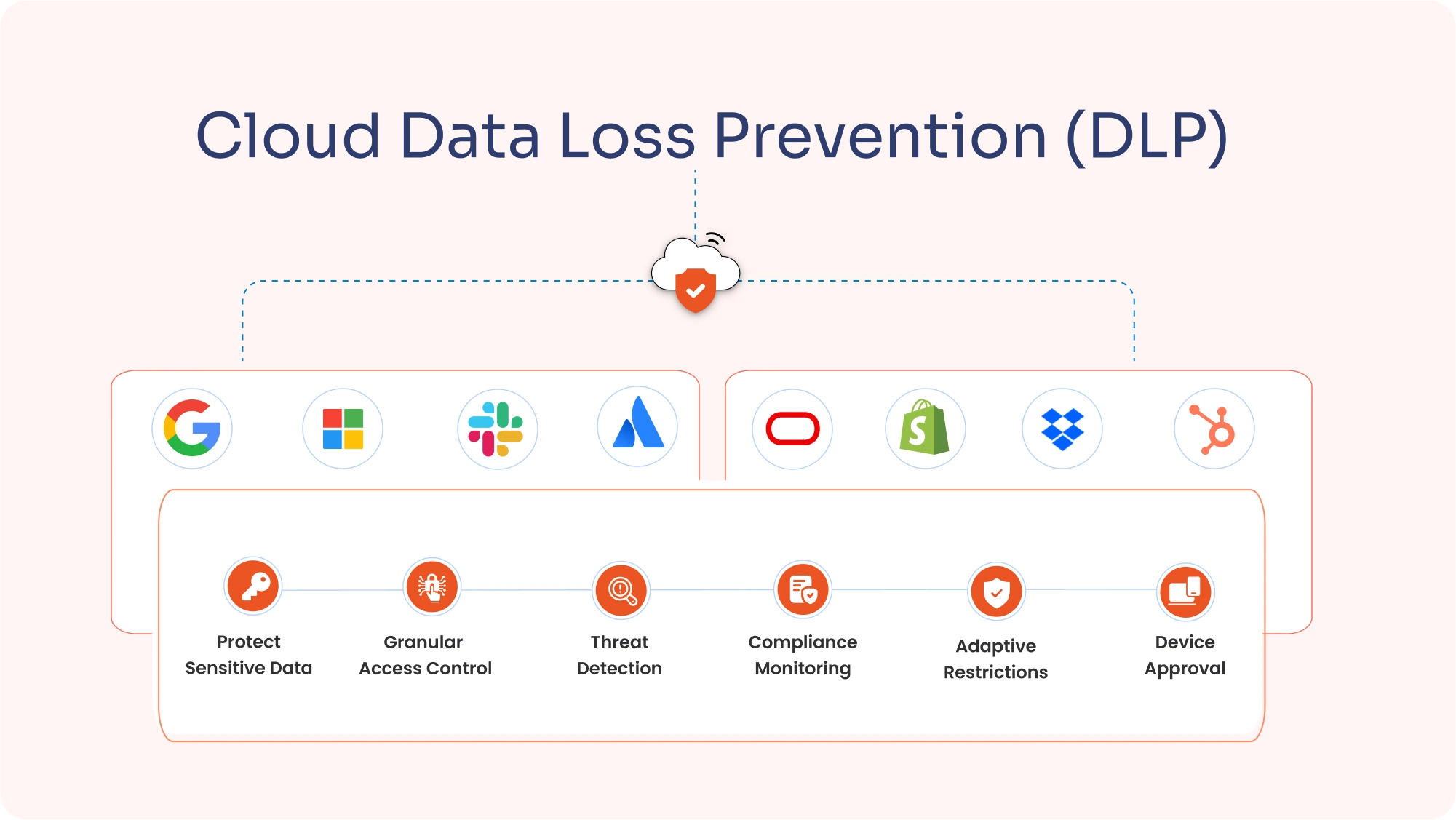
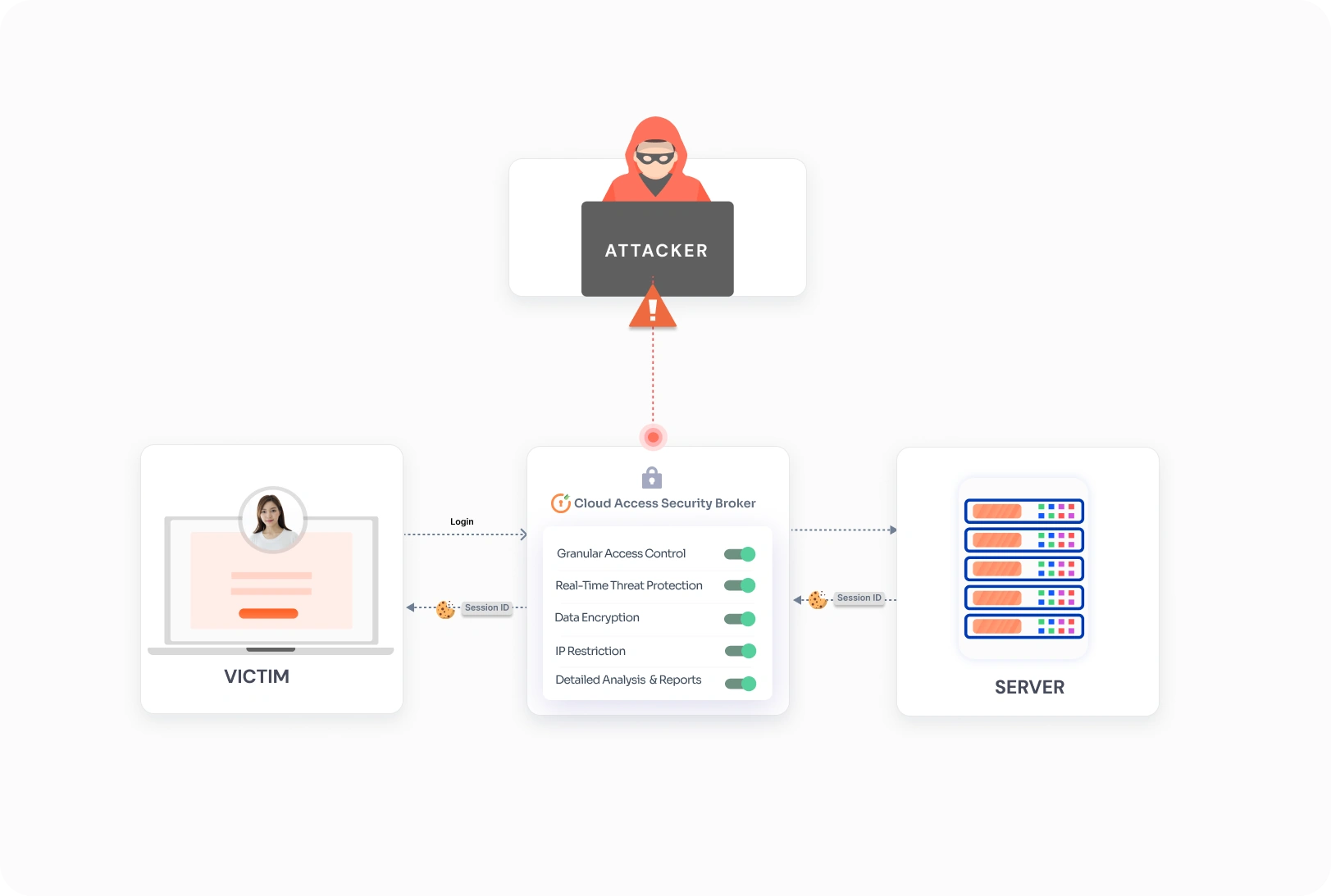
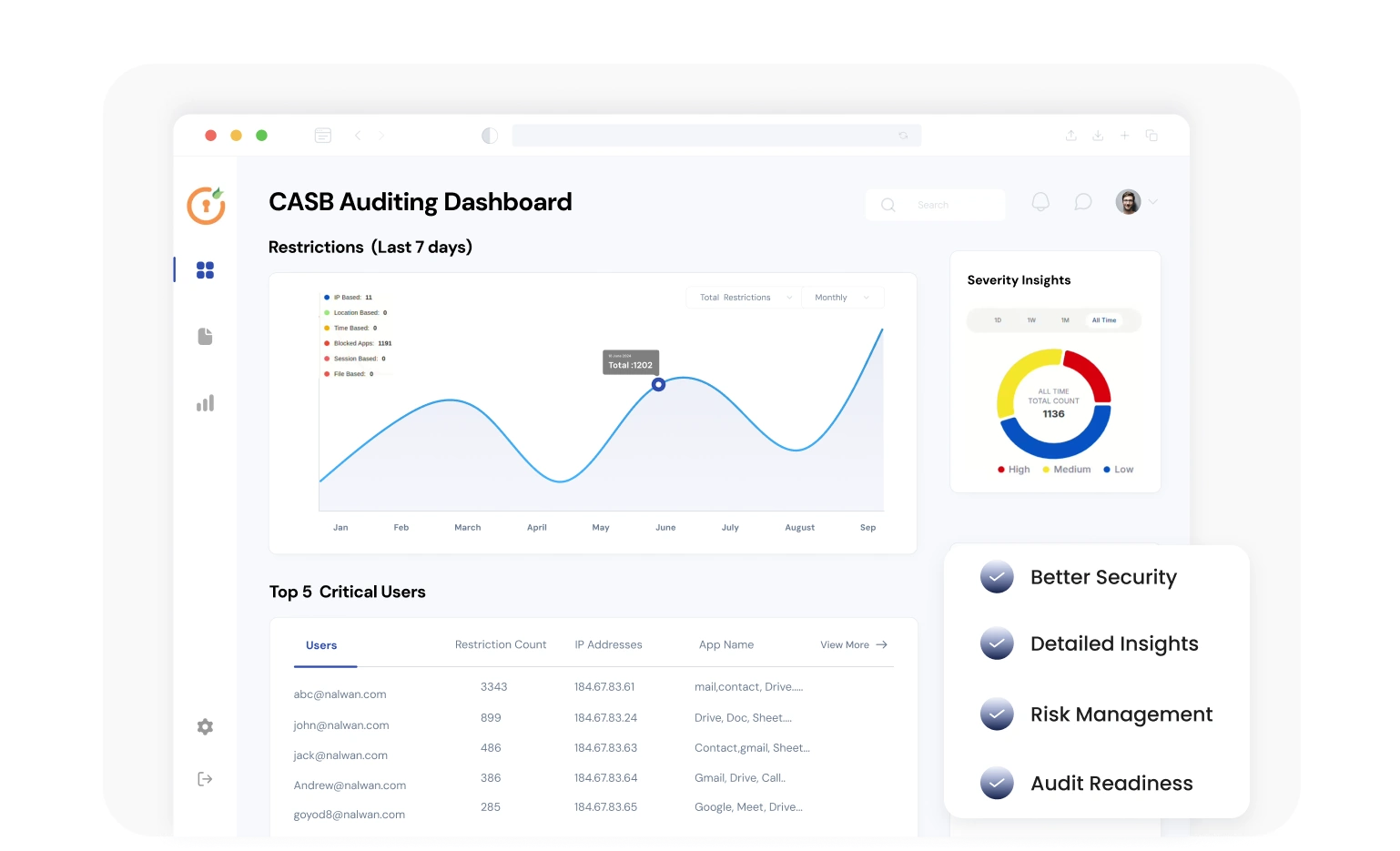
Cloud DLP, also known as Cloud Access Security Broker (CASB), is a security solution designed to protect sensitive business data stored in the cloud. It is designed to identify and block potential exposure of sensitive data—like customer details, financial records, or intellectual property—ensuring it doesn’t end up in the wrong hands. Moreover, they can significantly mitigate the risk of data loss across networks, emails, and endpoints.
For example, sensitive information within an email could be censored, or an attachment containing sensitive data could be removed from an email. Moreover, it can stop employees from accidentally emailing credit card numbers or sharing trade secrets externally.
Traditional DLP Vs. Cloud DLP
| Feature | Traditional DLP | Cloud DLP |
|---|---|---|
| Where It Works | On-premises systems like local servers, devices, and networks. | Cloud platforms such as Google Workspace, Microsoft Office 365, Oracle, Atlassian, and other SaaS applications. |
| Deployment | Installed and managed on physical infrastructure (servers, endpoints). | Deployed in the cloud; no need for physical hardware. |
| Scalability | Limited by hardware capacity; scaling requires more infrastructure. | Highly scalable; easily adjusts to business growth. |
| Accessibility | Works best when employees are on-site using company networks. | Works from anywhere; ideal for remote and hybrid work environments. |
| Data Coverage | Primarily protects data within internal networks. | Protects data across cloud platforms, emails, file-sharing apps, and more. |
| Maintenance | Requires in-house IT team for updates and troubleshooting. | Managed by cloud providers with automatic updates. |
| Security Threats Covered | Focuses on internal threats and endpoint data loss. | Covers both internal and external threats, including accidental sharing on cloud apps. |
| Compliance | Stronger for industries where regulations require on-premises control. | Better for businesses needing flexibility and remote data protection. |
| Incident Response | Slower response; manual interventions needed. | Faster response with automated alerts and real-time monitoring. |
| Example Use Cases | Banks, healthcare, or industries with strict data regulations. | E-commerce, SaaS businesses, and remote work environments. |
How Cloud DLP Works?
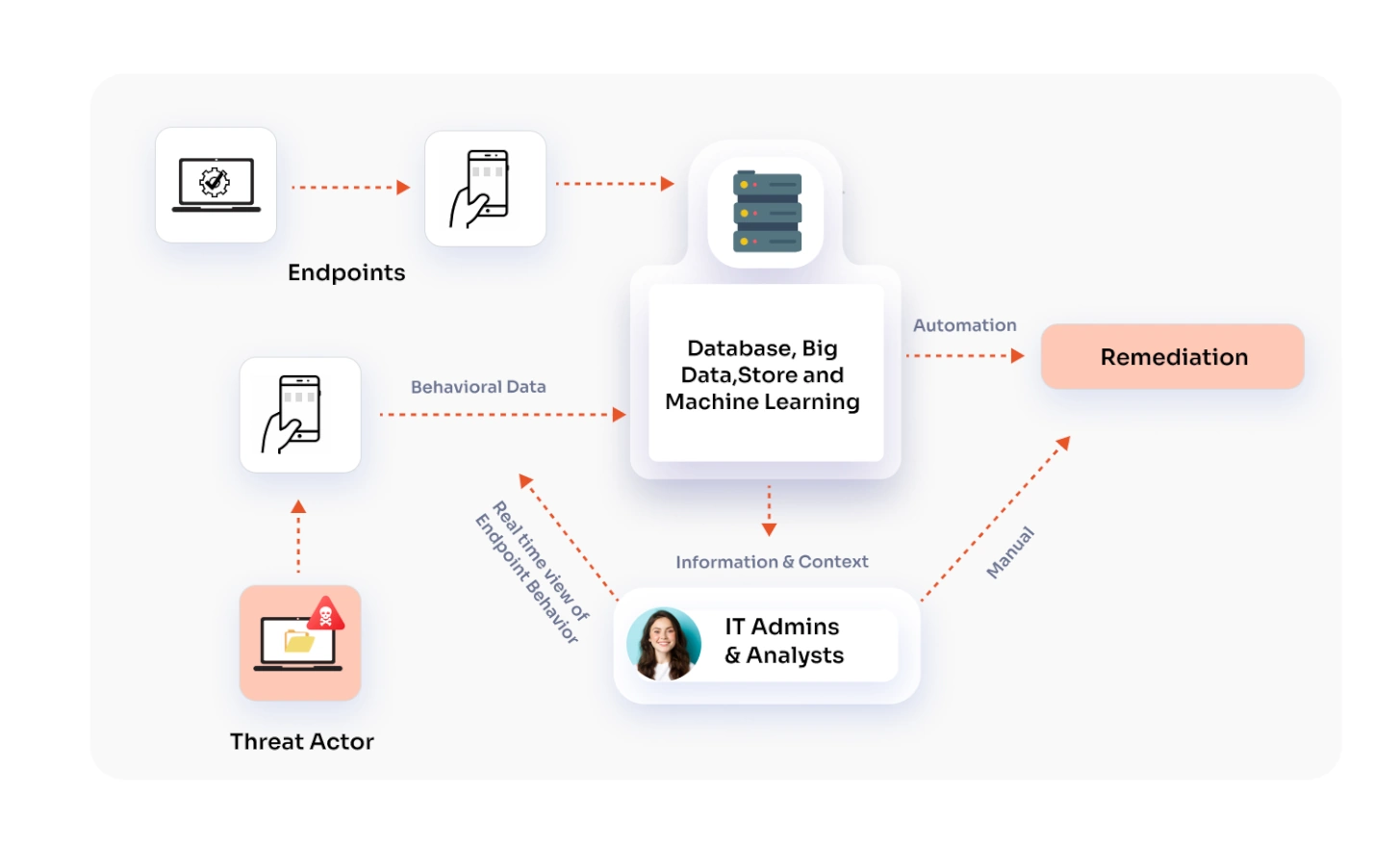
Cloud Data Loss Prevention (DLP) helps businesses keep their sensitive information safe by using smart tools and best practices. Here's how it works in simple terms:
1. Finding Sensitive Data
Cloud DLP solutions help your IT team find and understand where your data is stored. This includes scanning both cloud systems and on-site storage to get a full view of the data that needs protection.
2. Sorting and Setting Rules
Some business information, like financial records or personal customer details, are more critical and need extra care. For instance, Google Workspace CASB integration can help you sort data based on how sensitive your data is and how badly it could hurt your business if it got leaked. Once sorted, your team can create rules on how this data should be handled—who can access it, where it can be sent, and how to keep it safe.
3. Controlling Access
To keep sensitive data safe, it's important to ensure that only the right employees can see it based on their role. Tools like multifactor authentication (MFA) and access control systems make sure that unauthorized users can't get in.
4. Watching for Threats
Cloud DLP/CASB solutions continuously monitor your data, watching for any signs of trouble. For instance, Microsoft Office 365 CASB Security can check for things like sensitive data being accessed from unauthorized public places like cafes or airports, unusual activity, or attempts to alter or destroy data. If something looks suspicious, the system can step in to protect the data by encrypting it or blocking access. It’s like having security cameras that alert you when something seems off.
By combining these steps, DLP for cloud makes sure that your business's important information stays safe from leaks, loss, or misuse.
Key Benefits of Using a Cloud DLP
Keep Your Data Safe
At its core, cloud-based DLP is all about protecting sensitive information. Cloud DLP takes this a step further by securing data stored in cloud apps and services. Whether it’s customer details or company secrets, Cloud DLP ensures that sensitive data stays where it belongs.
See Where Your Data Goes
DLP for cloud gives you a clear view of how data moves in and out of cloud services. It tracks where your company data is going—whether to approved apps or unauthorized ones. This visibility not only improves security but also helps you understand how your team uses cloud tools.
Stay Compliant with Regulations
Certain types of sensitive data, like credit card details or health records, are protected by laws such as PCI DSS, HIPAA, and GDPR. Cloud DLP helps organizations manage who can access this data, whether it’s stored on-premises or in the cloud, keeping them compliant with these regulations.
Prevent Data Loss with Automated Policies
Cloud DLP allows you to set policies that detect and block sensitive information from leaving your organization unintentionally. Whether it's through emails, file sharing, or cloud storage, these policies protect the data against accidental leakage. This reduces the risk of human error and keeps your critical information secure.
Improve Incident Response and Reporting
When a data breach or policy violation happens, quick action is essential. Cloud DLP provides real-time alerts and detailed reports, enabling your security team to respond swiftly. This helps minimize damage, identify vulnerabilities, and continuously improve your organization's data security strategy.
Types of DLP Solutions
While Cloud DLP is essential, it works best when combined with other types of DLP solutions. Here are a few other ways to protect your data:
1. Network DLP
Network DLP keeps an eye on the data flowing in and out of your network. If it spots anything that breaks security policies, it raises a red flag.
2. Endpoint DLP
This type of DLP monitors devices like laptops, desktops, servers, and even mobile phones. It ensures that sensitive information isn’t accessed or shared in ways it shouldn’t be.
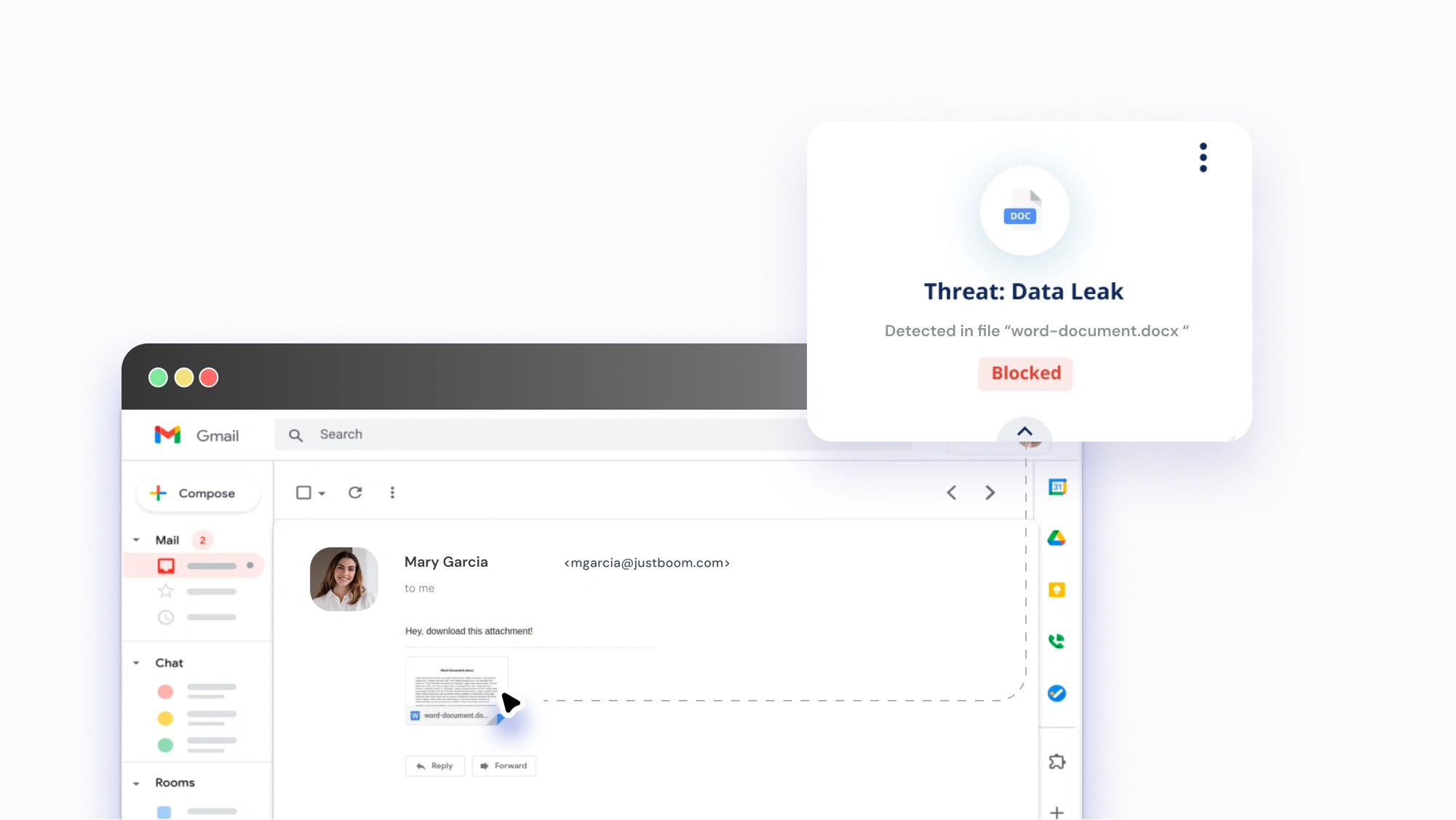
3. Email DLP
Emails are one of the most common ways data leaks happen. Email DLP checks the content and attachments in your emails. If something looks suspicious, it can warn the sender, flag the email for review, block it, or even delete it.
Business Scenario: Protecting Data in Google Workspace with Google Cloud DLP
Consider a mid-sized marketing firm that utilizes Google Workspace for collaboration. Every day, your team shares vital documents filled with client information, campaign strategies, and market research. With so much sensitive data floating around, keeping it safe is a top priority.
By integrating Google CASB / Cloud DLP, the firm can:
- Automatic Detection of Sensitive Data: Google Cloud DLP systematically scans documents in Google Docs to identify sensitive information, including client contact details and confidential market analyses.
- Email and Endpoint Data Loss Prevention (DLP): When a document containing sensitive data is shared or accessed using an unapproved device, Google Cloud DLP can enforce restrictions on sharing permissions, ensuring that only authorized personnel have access.
- Monitoring and Reporting: The solution provides detailed reports on data access and sharing activities, which support compliance audits and internal reviews.

Summary
As organizations continue to embrace cloud technologies, implementing robust Cloud DLP strategies becomes essential. By understanding how data can be compromised and employing effective prevention techniques, businesses can safeguard their sensitive information, maintain client trust, and ensure compliance with regulatory standards.
Remember, protecting your data in the cloud isn't just about deploying the right tools—it's about fostering a culture of security awareness and continuous improvement.
Additional Resources
- CASB vs DLP: Understanding the Differences
- What are the 4 Pillars of CASB?
- CASB for Salesforce: Data Security, Compliance, and User Visibility
- ITAR Compliance for Cloud Services with CASB
- Google App TTL Restrictions: Using Google Workspace CASB Security
- Google Drive Security for Education: Prevent Unauthorized Sharing
- ServiceNow CASB Cloud Security: Compliance and Granular Access Control
- Microsoft 365 CASB for SharePoint: Business Data Security and Compliance
- Microsoft Office 365 CASB: An Overview
- Protecting Google Workspace Apps: Based on User Roles/Groups
Author

Leave a Comment