Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×Enable Device restriction on Google Workspace (G Suite) apps with miniOrange security solutions. Onboard your users and configure custom Device restrictions to secure your data. Find the security solution that fits your business needs for authenticating users by Device Mac Address, block user access to Google Workspace in real-time, and managing mobile and desktop device authorization.

Allow access to Google Workspace apps from authorized and whitelisted Device Mac Addresses only by authenticating with an IAM. Learn More
Setup Now

Allow access to business data stored on Google Workspace mobile apps when the users are connected to a whitelisted mobile Device with an MDM solution.
Learn More
Setup Now
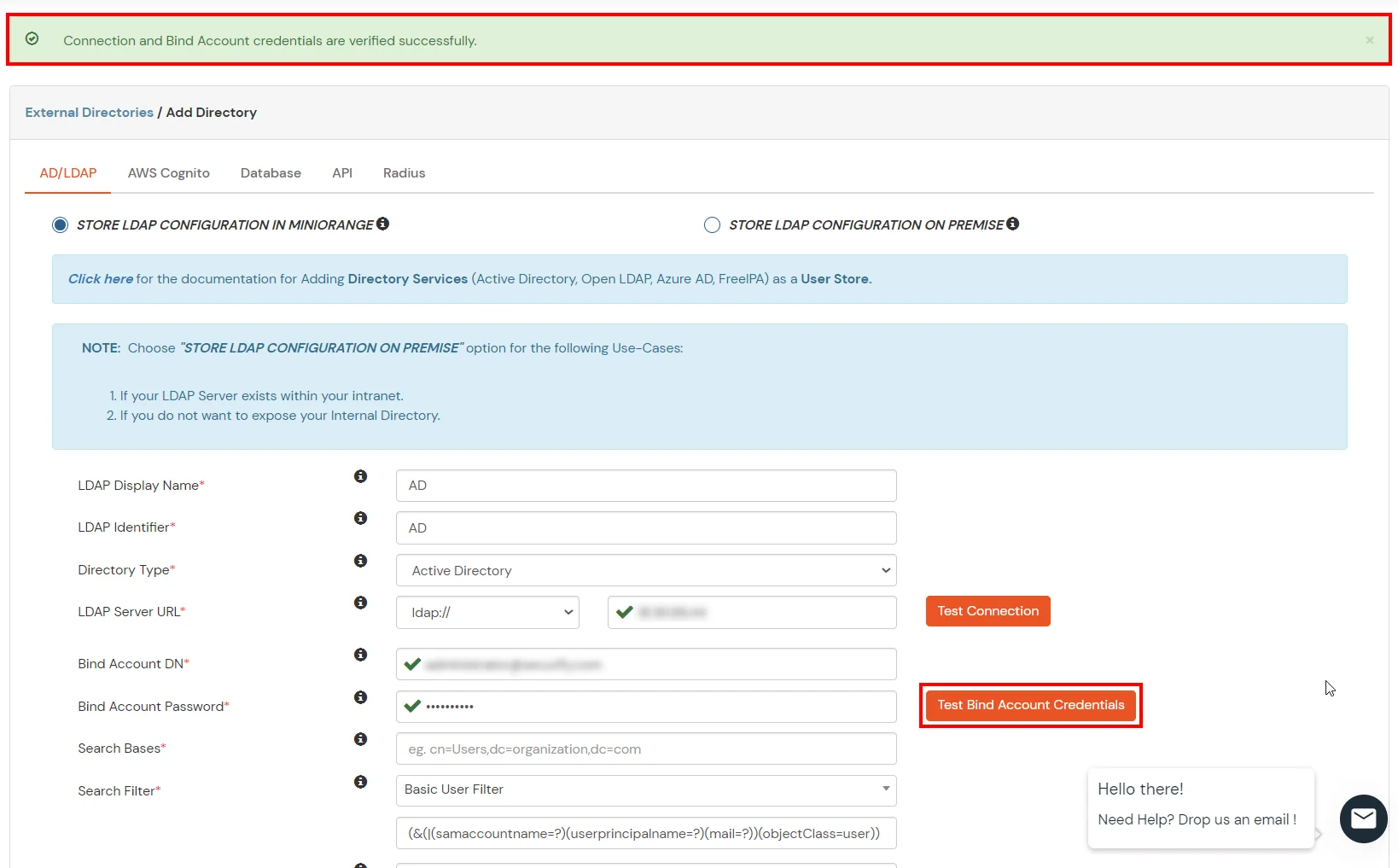
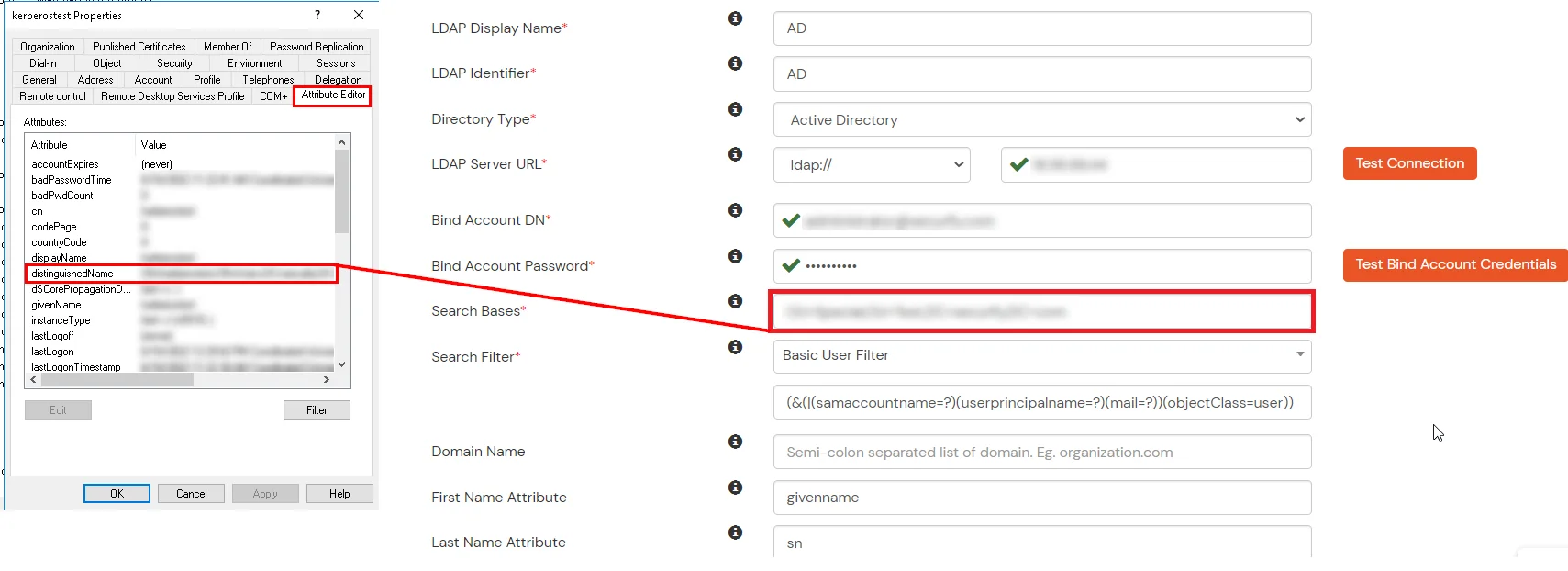
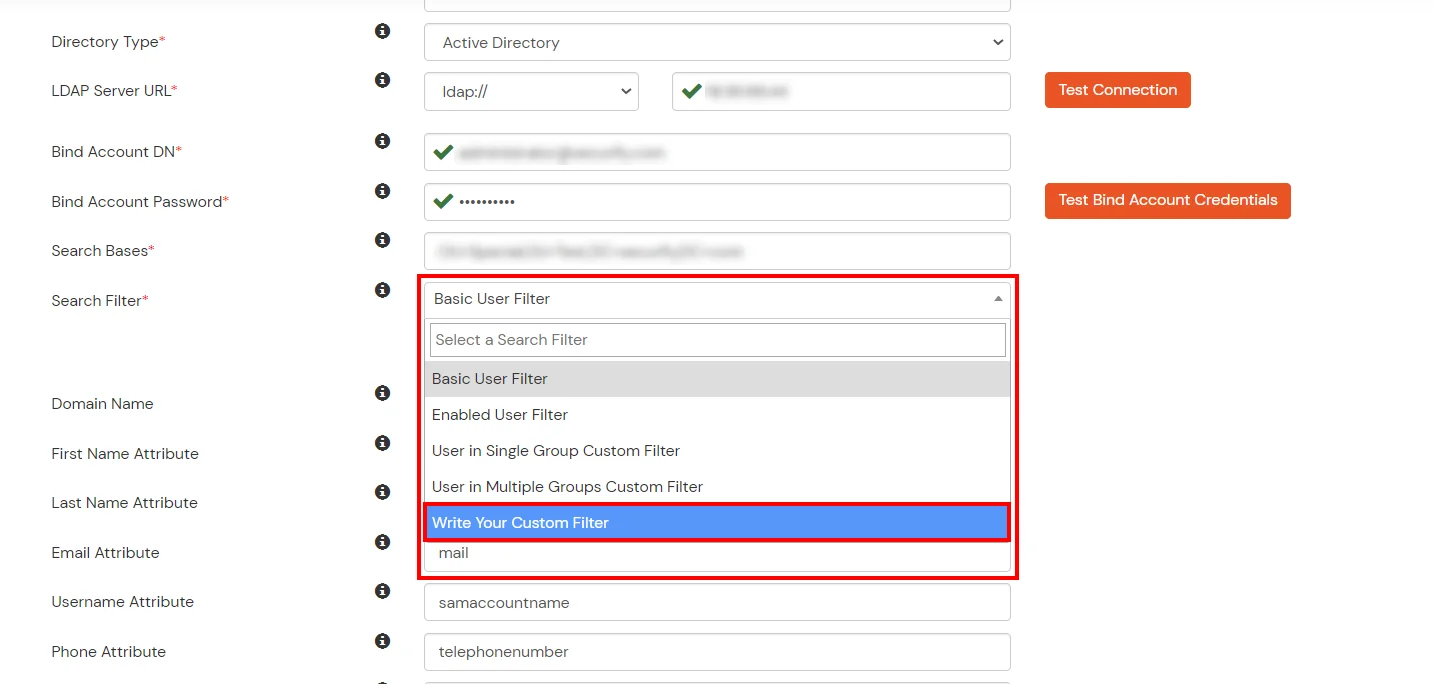
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
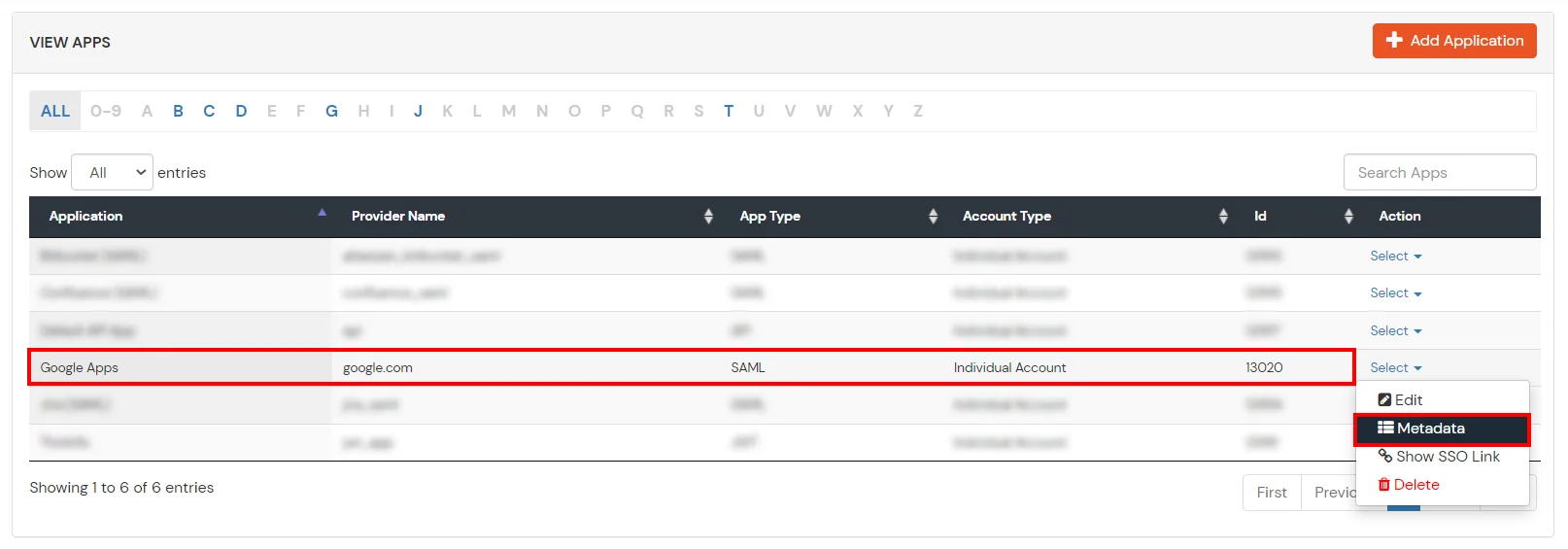
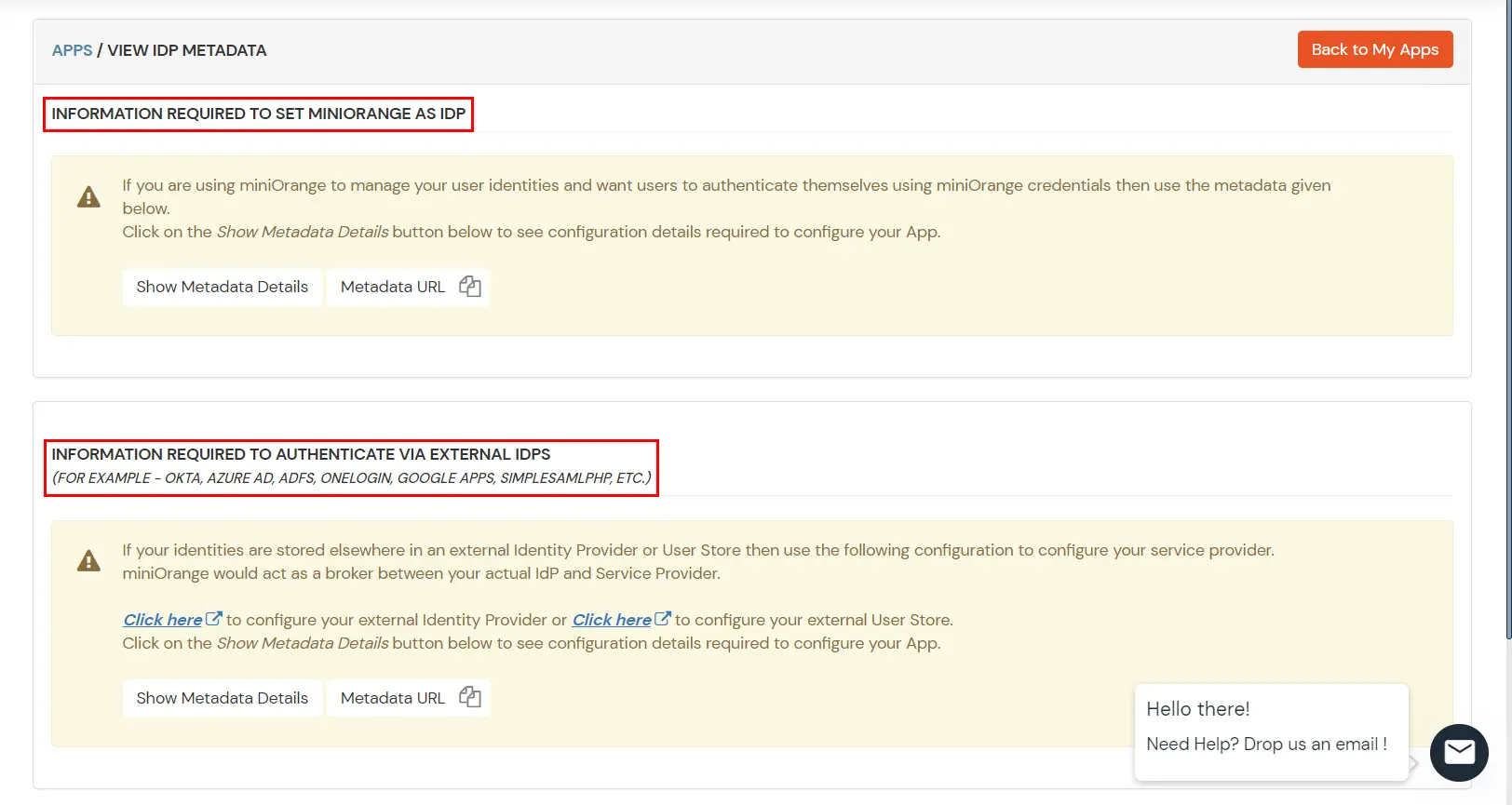
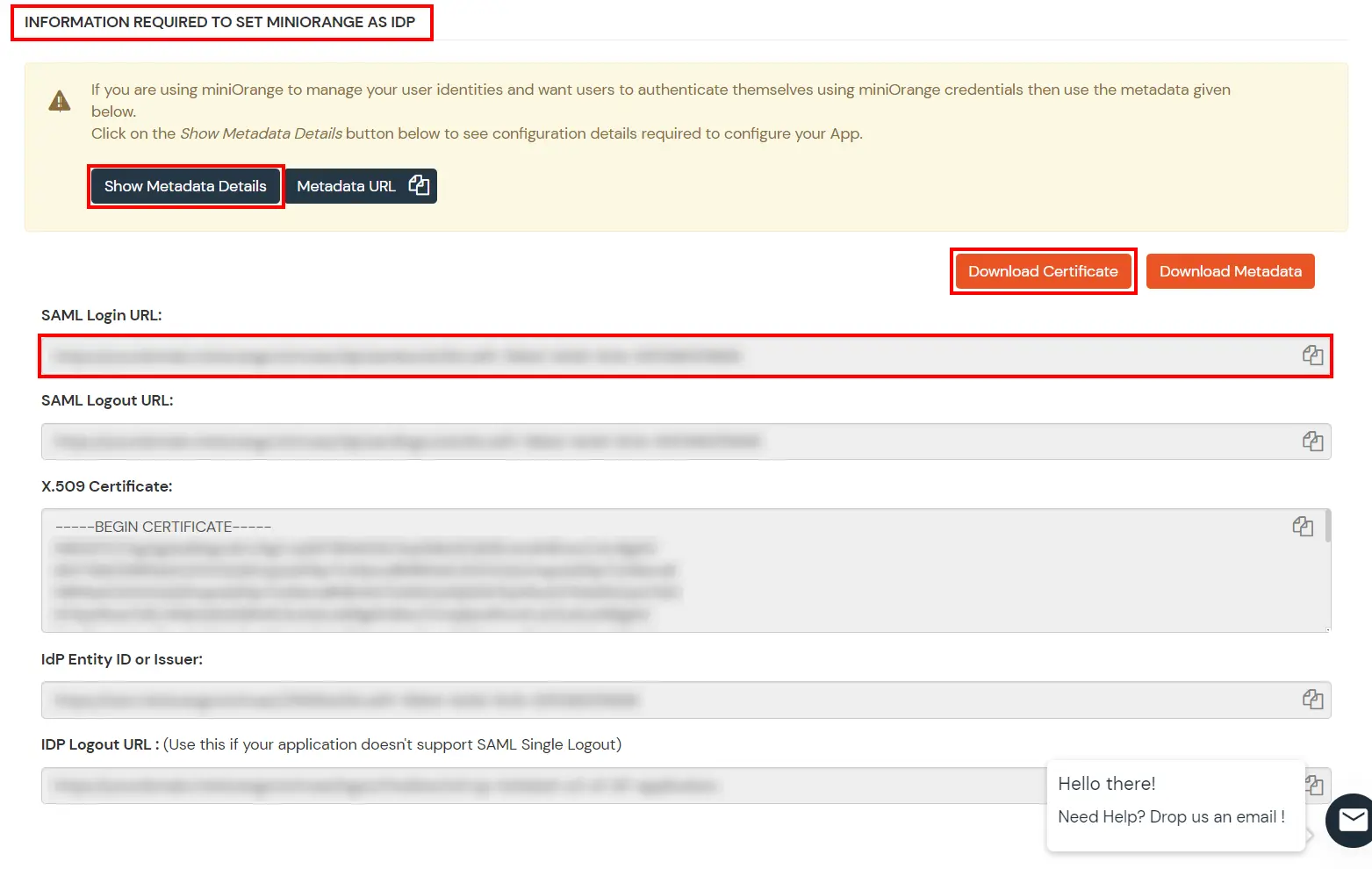
Get IdP Metadata Details to upload to Google Apps:
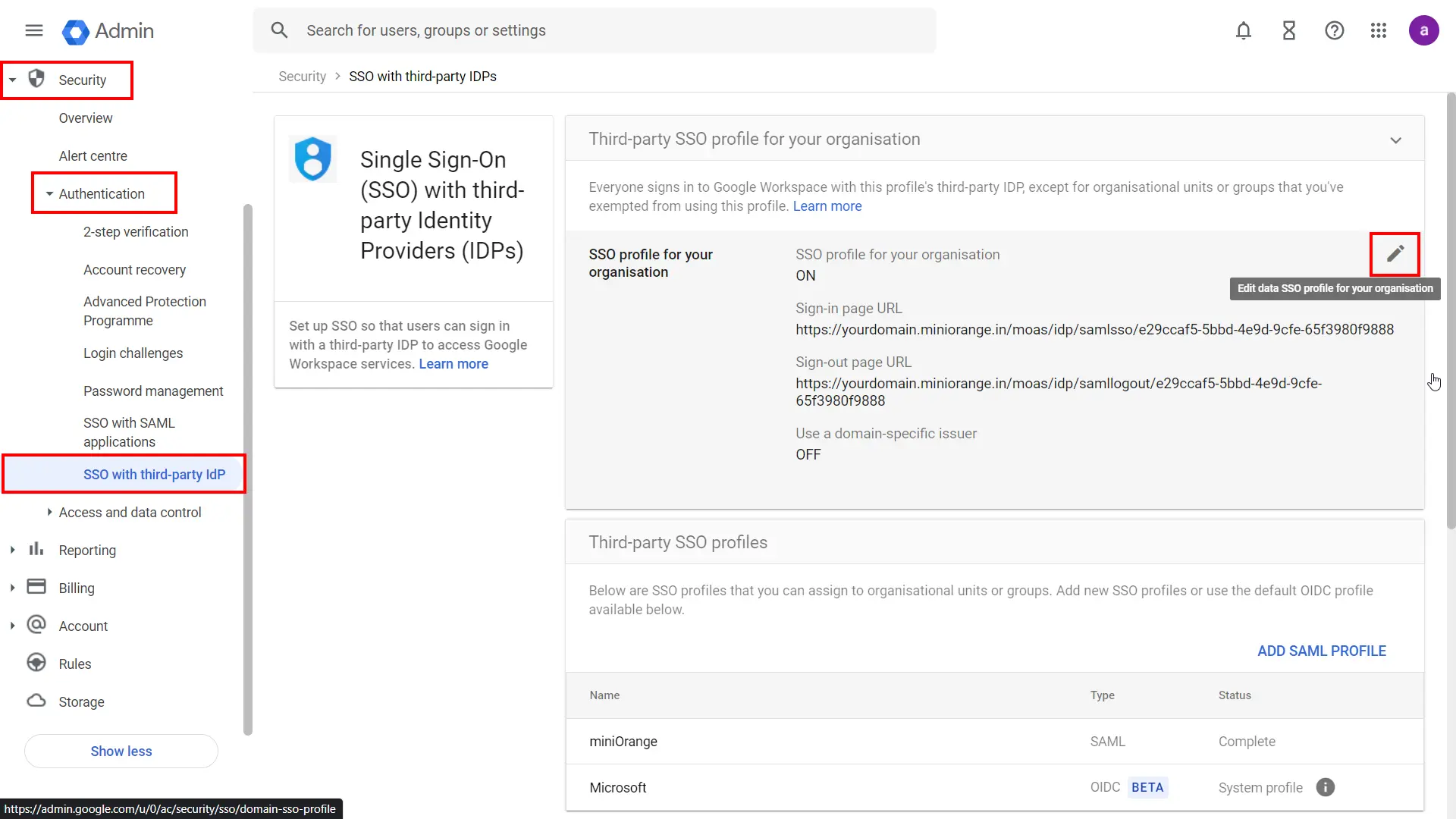
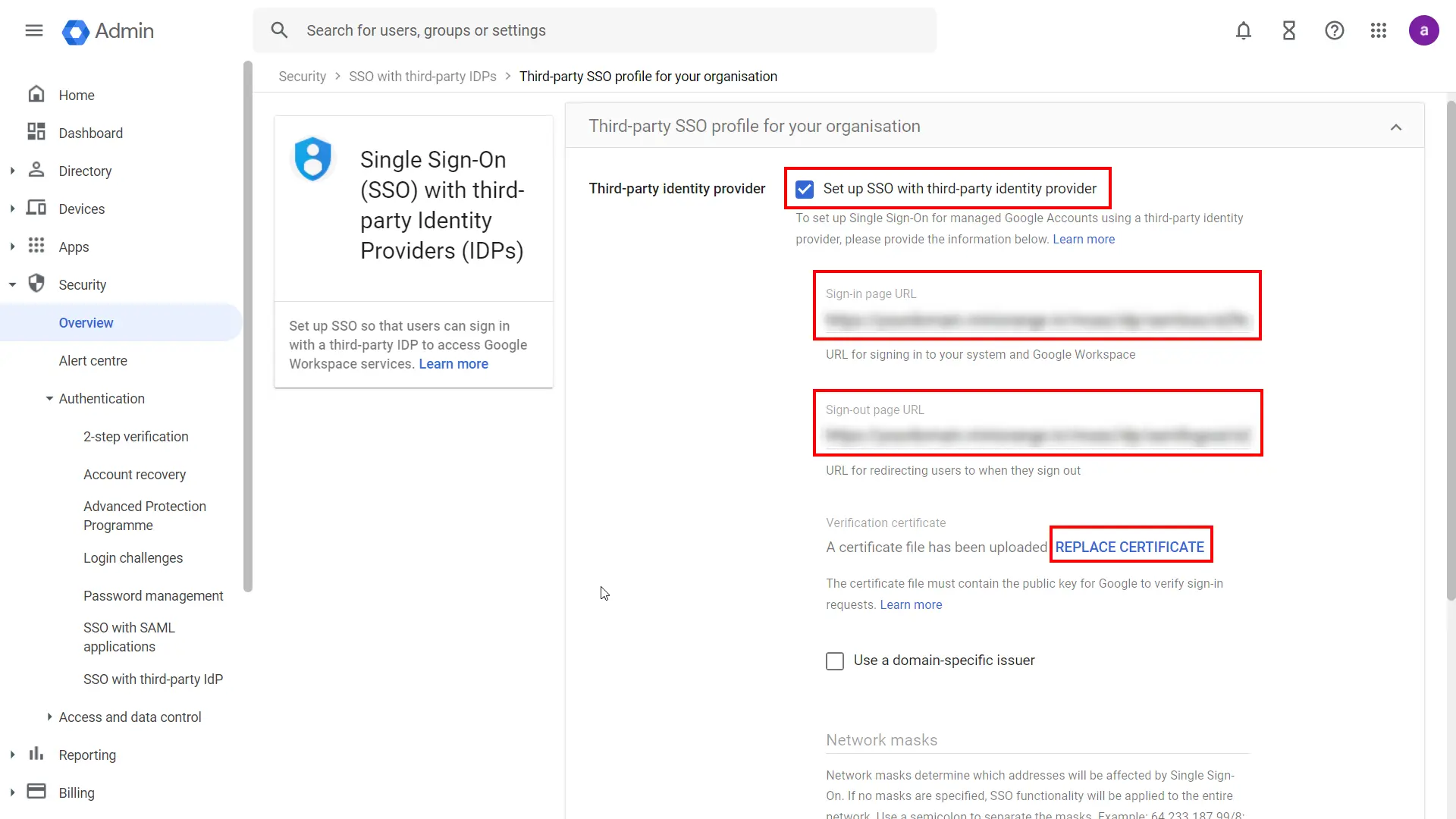
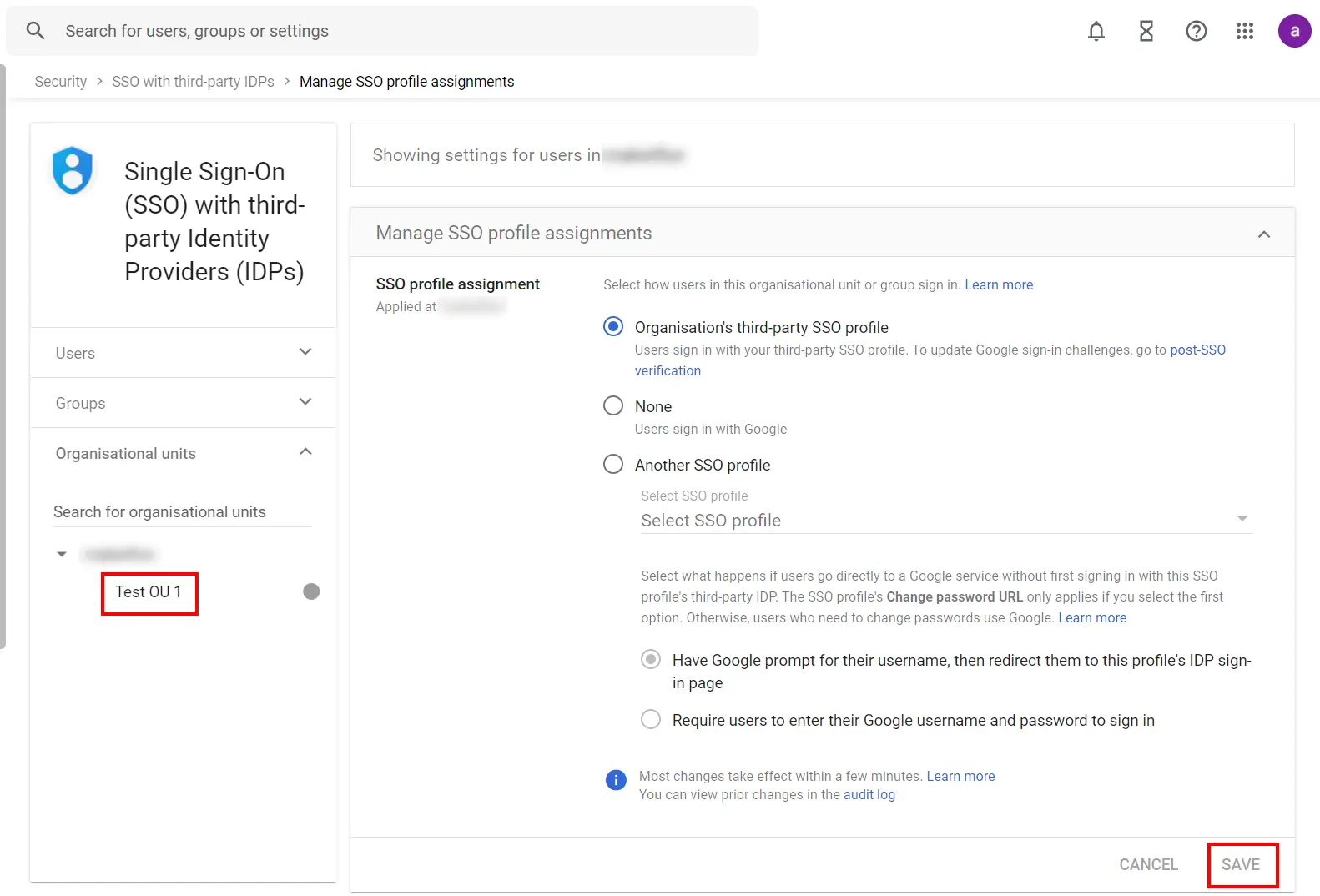
If you want some of your users to sign in to Google directly, you can move those users into an organizational unit (OU) or group. Then, manage SSO settings for the OU or group so that those users are authenticated by Google rather than using your third-party IdP. Follow the following steps:
Note: Get started is only available if you’ve already enabled your third-party SSO profile. 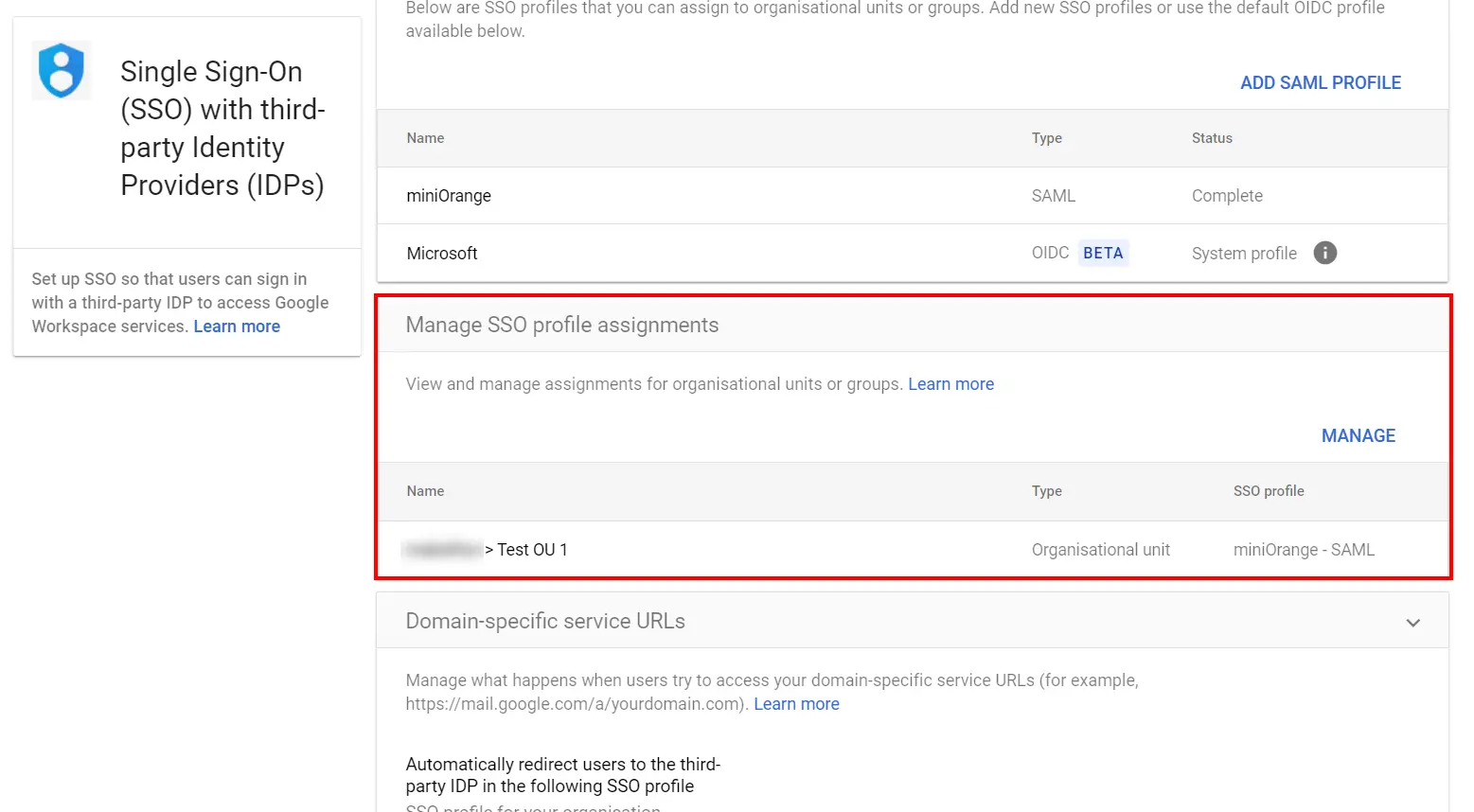
Note: If the SSO profile assignment for an OU or group differs from your domain-wide profile assignment,
an override warning appears when you select that OU or group. You can’t assign the SSO profile on a
per-user basis. The Users view let you check the setting for a specific user.
If you want to turn off the third-party authentication for all your users without changing the SSO profile assignment for OUs or groups, you can disable the third-party SSO profile:
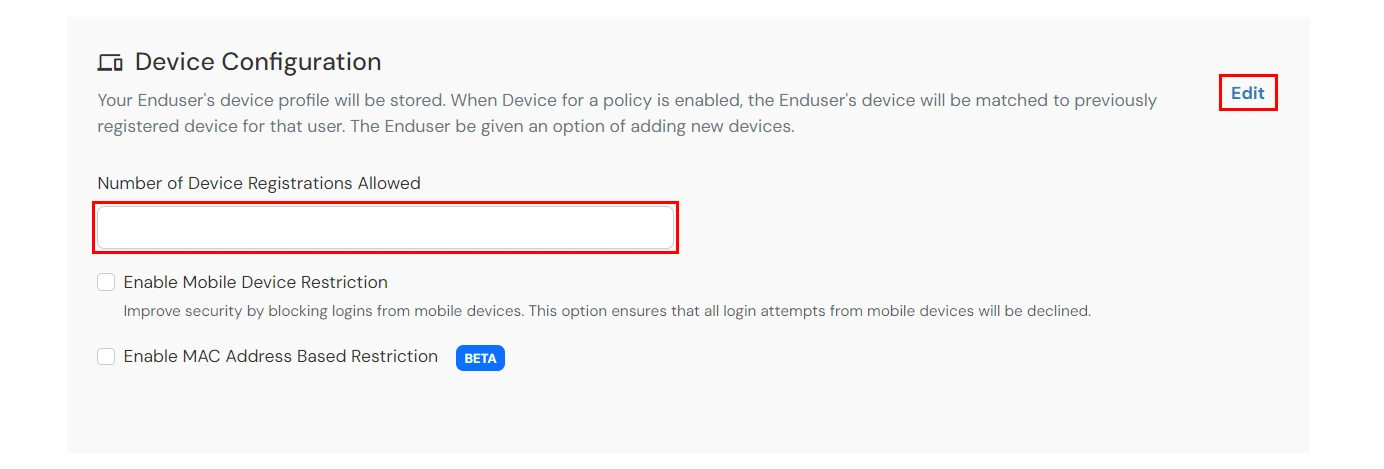
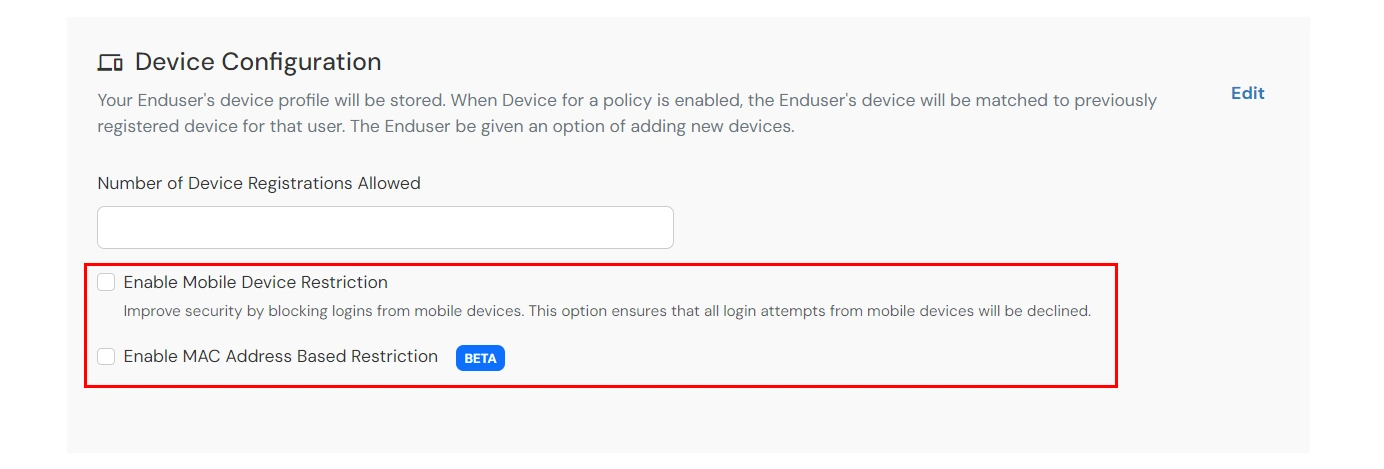
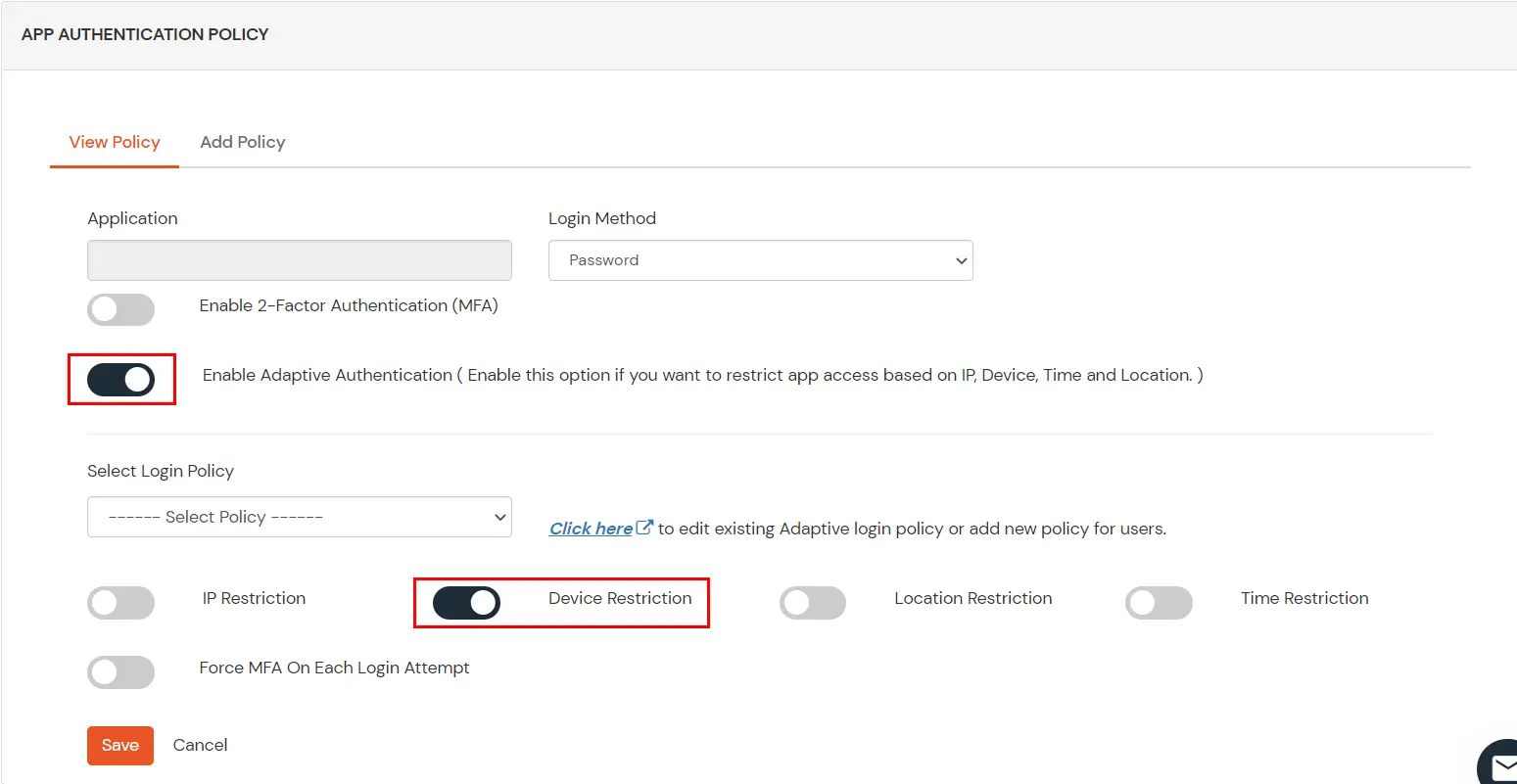
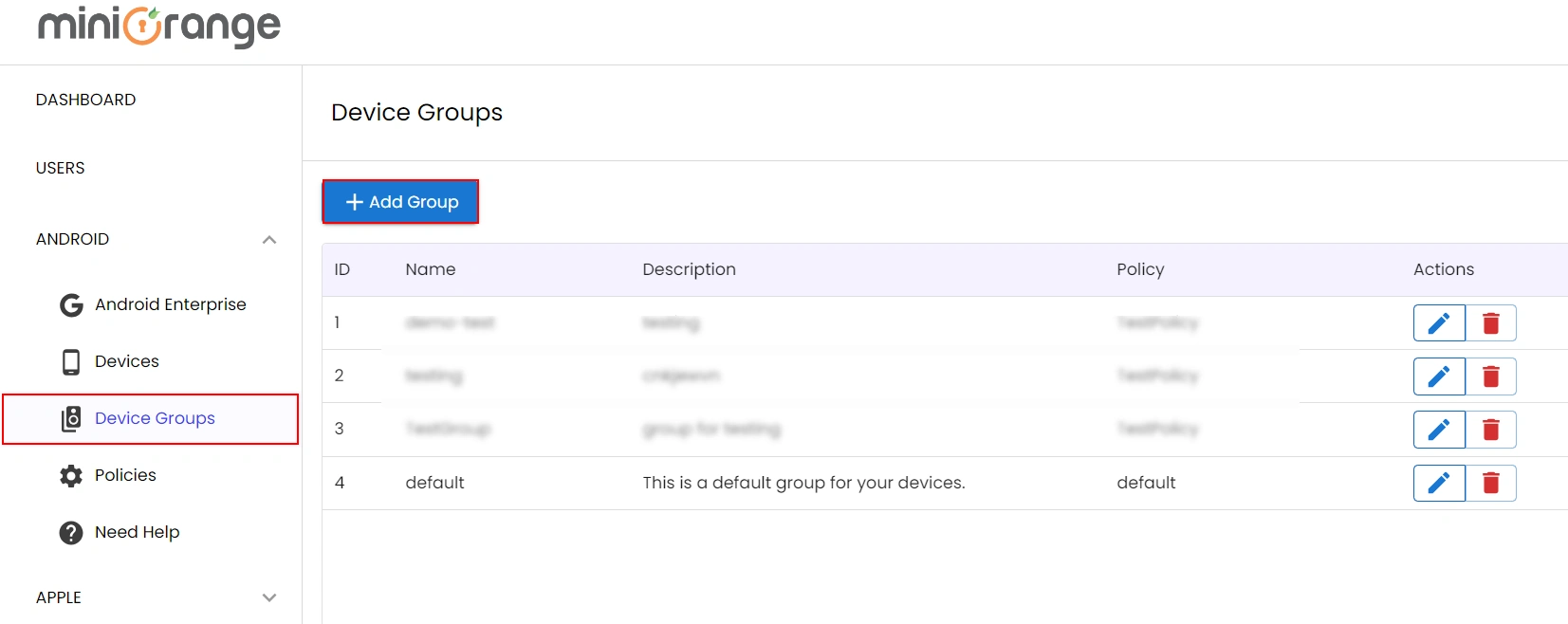
Using Adaptive Authentication you can also restrict the number of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. When Device for a policy is enabled, the Enduser's device will be matched to previously registered device for that user. The end users will be able to access services provided by us on this fixed no. of devices of that particular user.
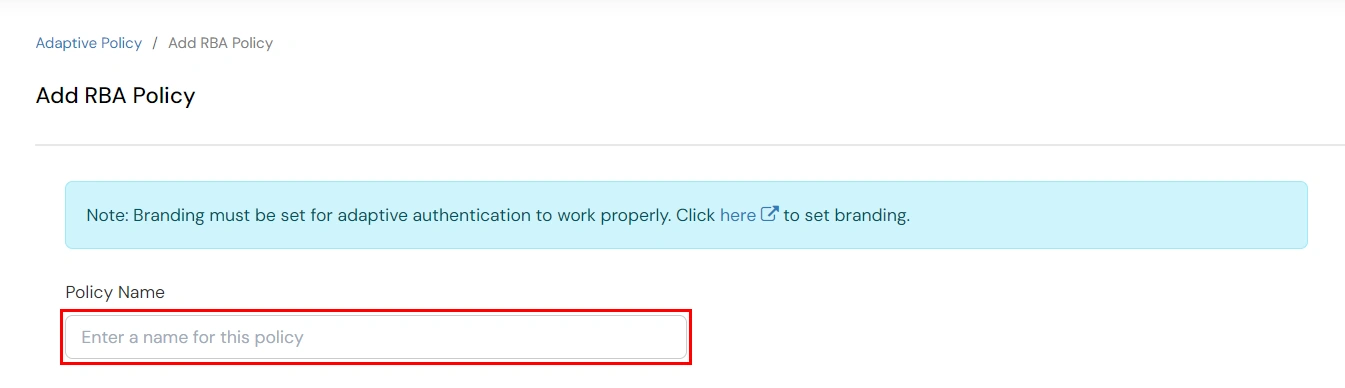
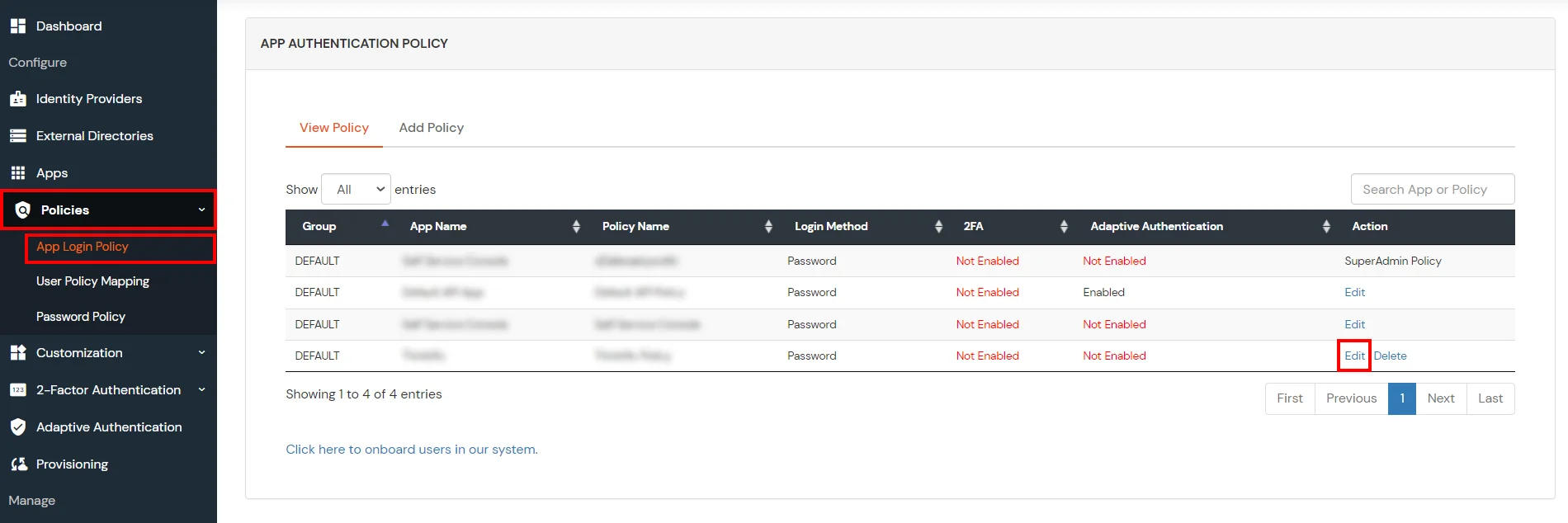
You can configure Adaptive Authentication with Device Restriction in following way: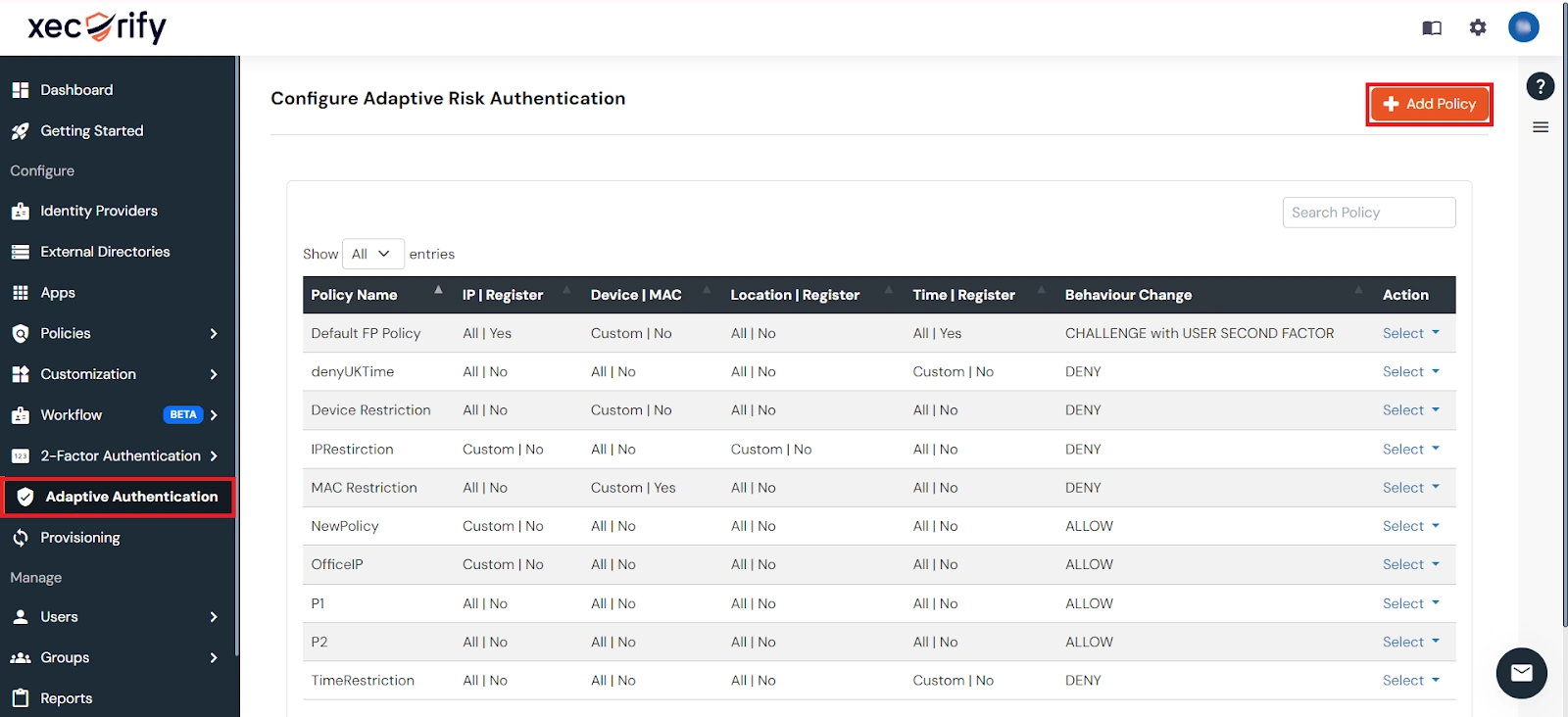
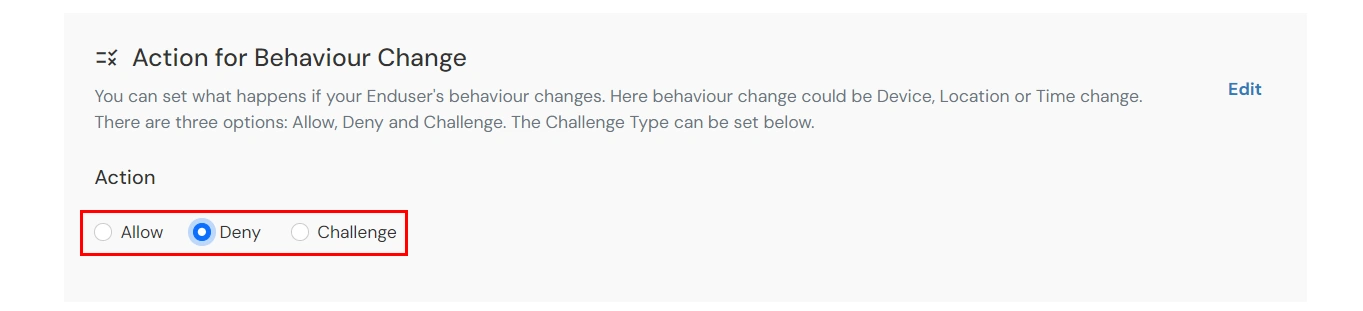
| Attribute | Description |
|---|---|
| Allow | Allow user to authenticate and use services if Adaptive authentication condition is true. |
| Challenge | Challenge users with one of the three methods mentioned below for verifying user authenticity. |
| Deny | Deny user authentications and access to services if Adaptive authentication condition is true. |
| Attribute | Description |
|---|---|
| User second Factor | The User needs to authenticate using the second factor he has opted or assigned for such as |
| KBA (Knowledge-based authentication) | The System will ask user for 2 of 3 questions he has configured in his Self Service Console. Only after right answer to both questions user is allowed to proceed further. |
| OTP over Alternate Email | User will receive a OTP on the alternate email he has configured threw Self Service Console. Once user provides the correct OTP he is allowed to proceed further. |



The default MFA method setup for the end user is fetched from the miniOrange IAM dashboard and accordingly the MFA will be initiated, e.g. OTP over Email/Push Notification, etc
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
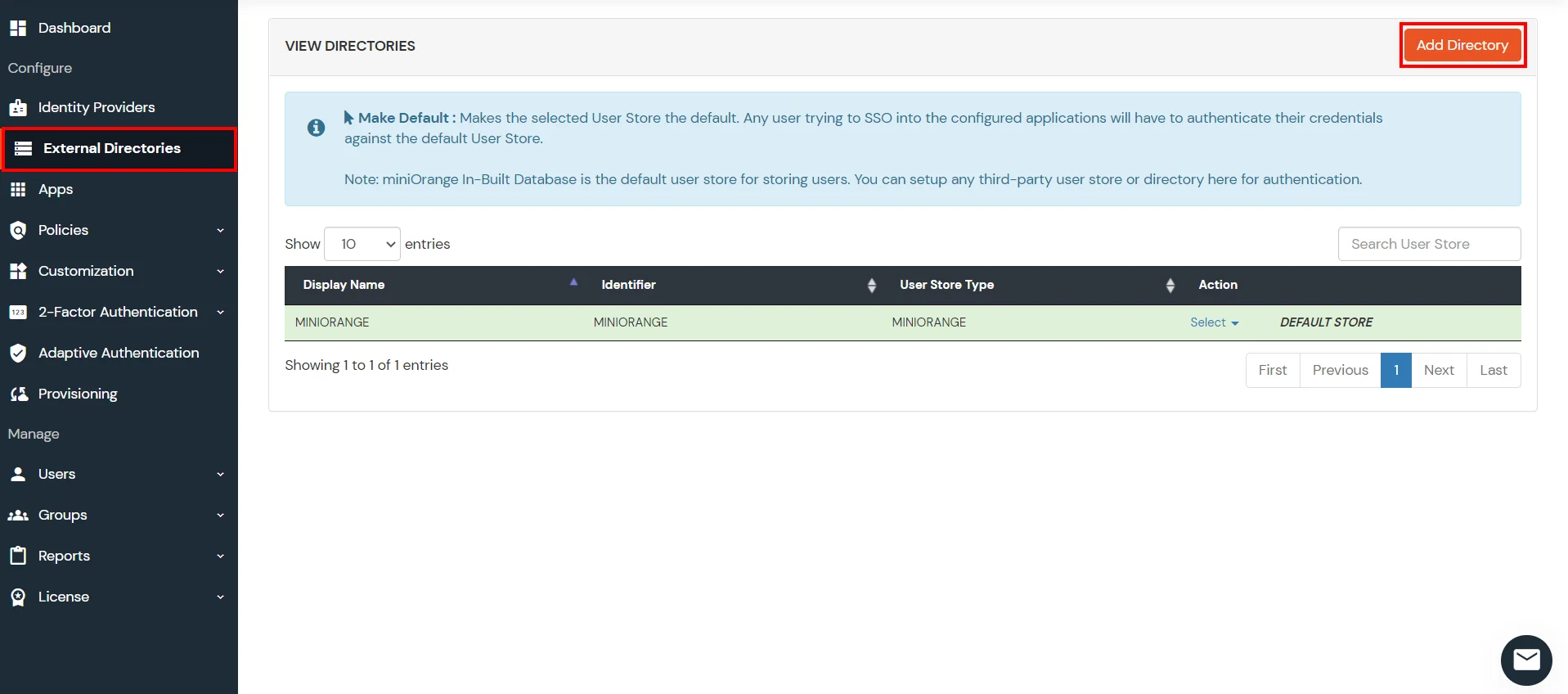
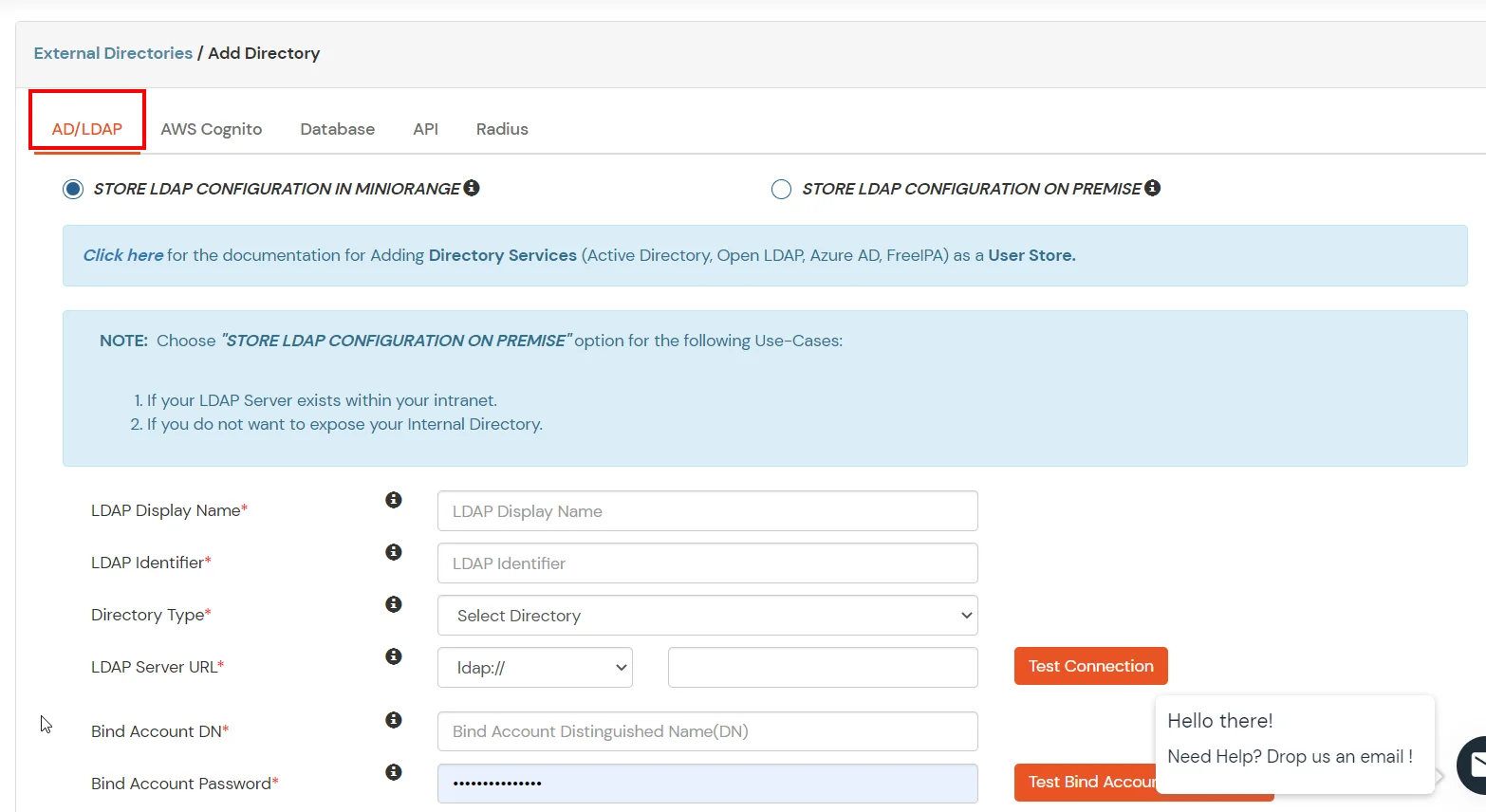
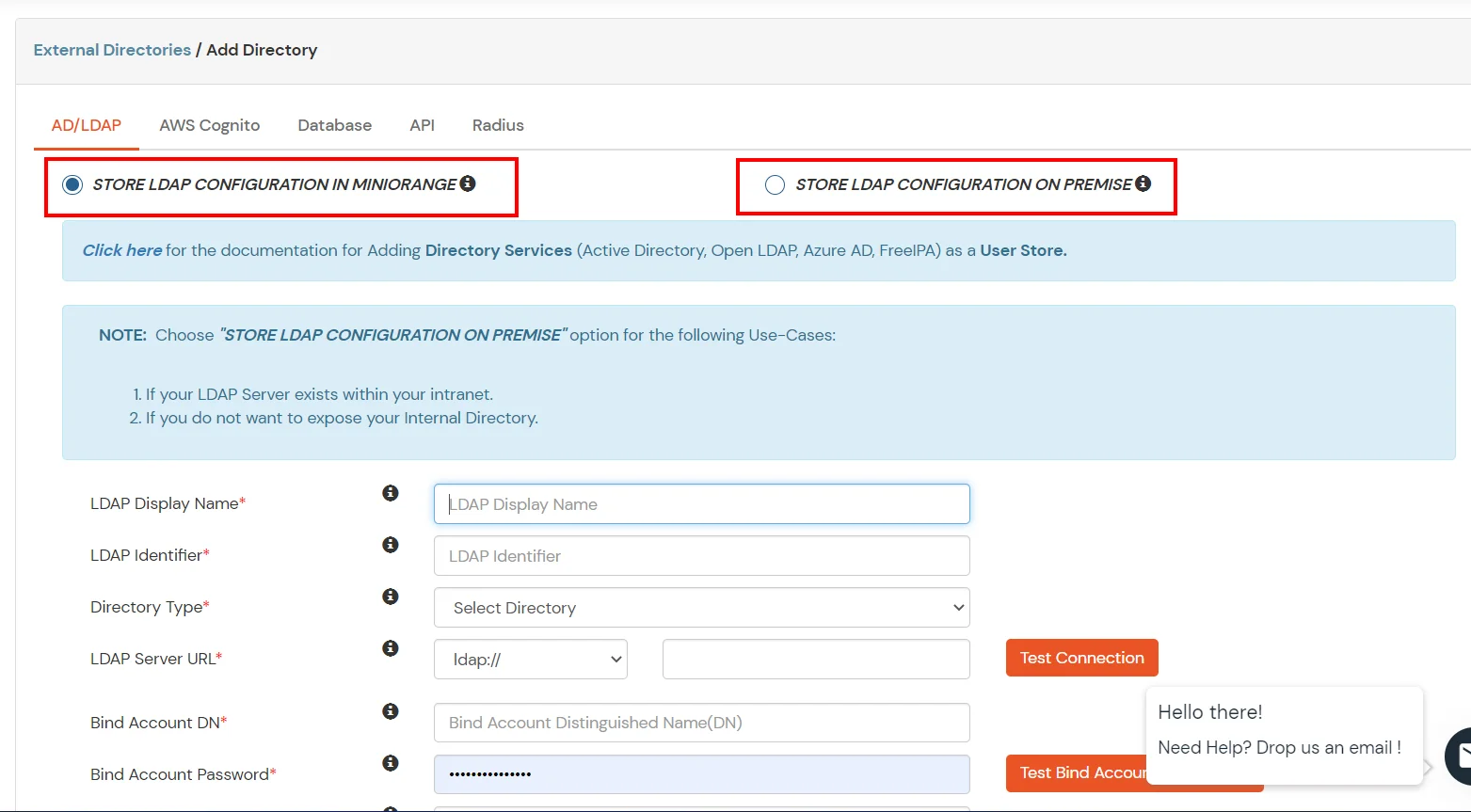
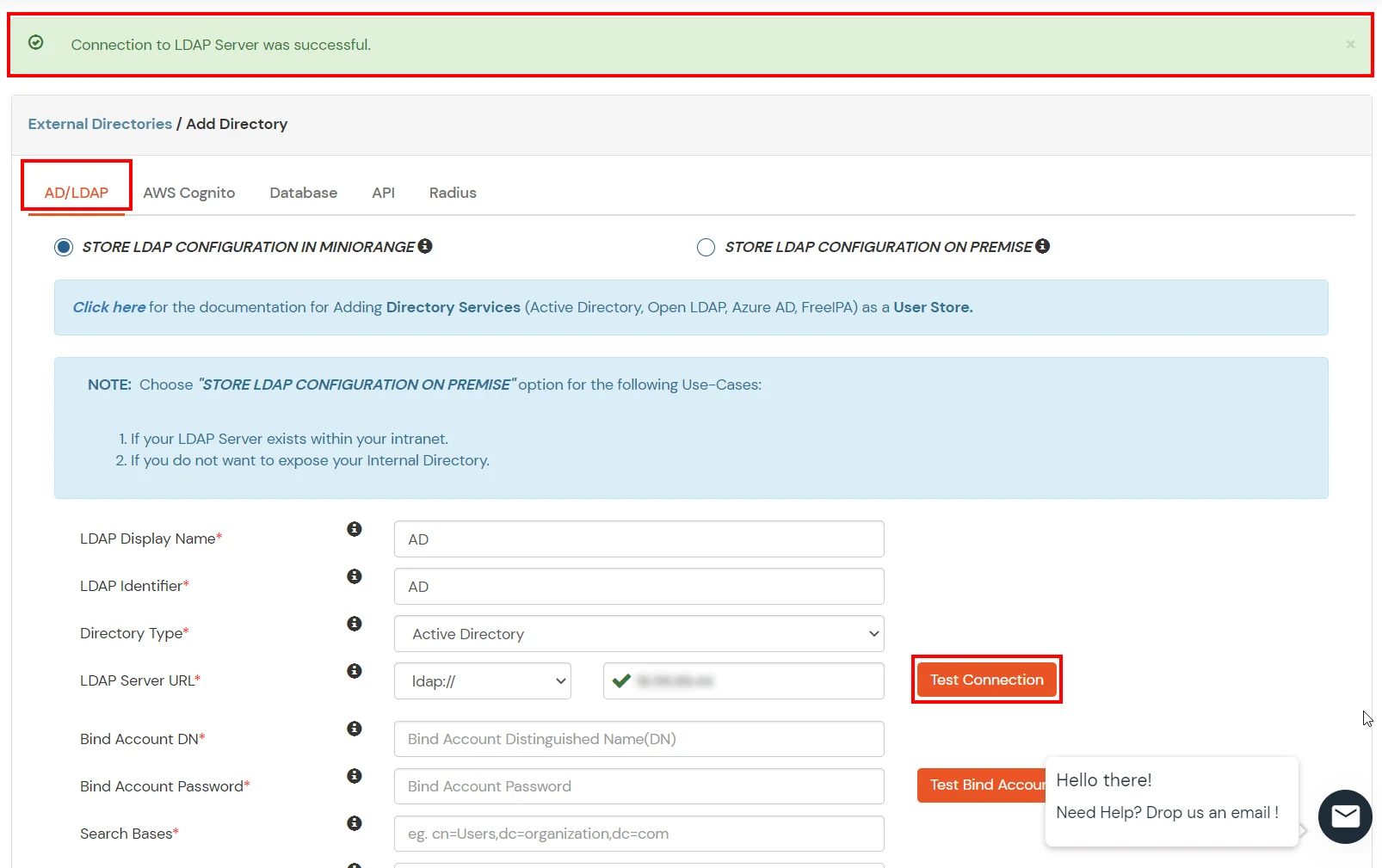
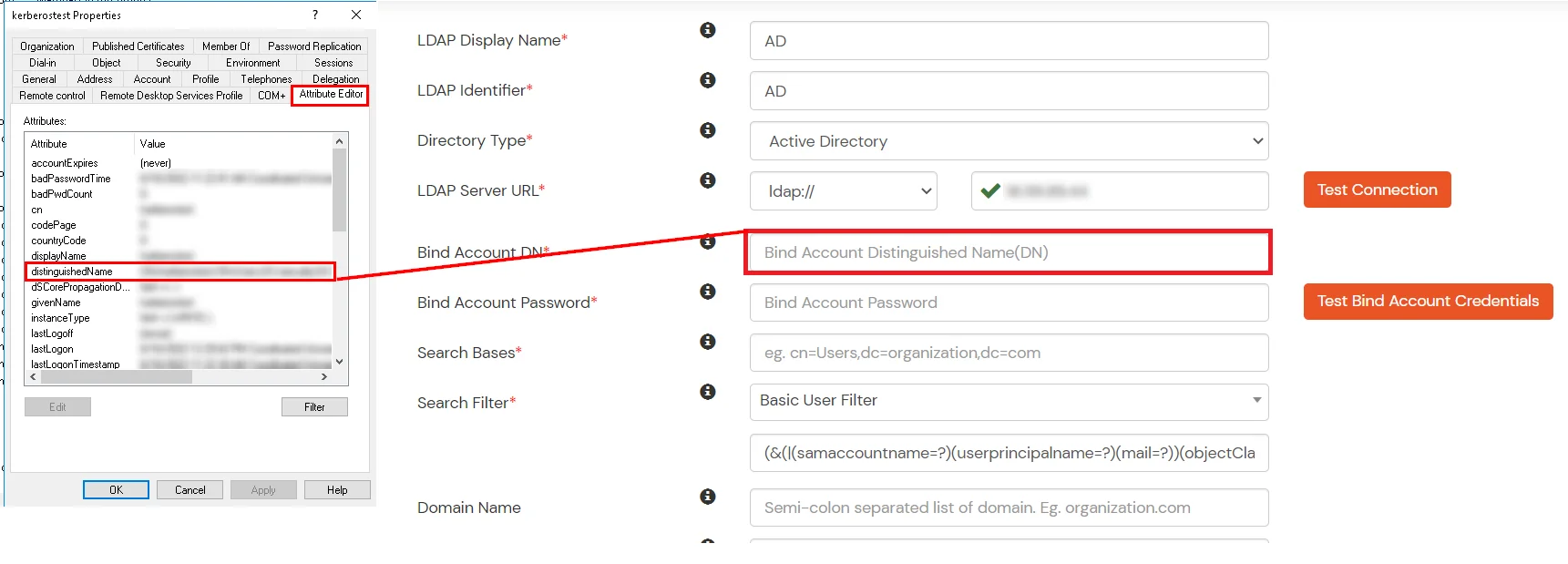
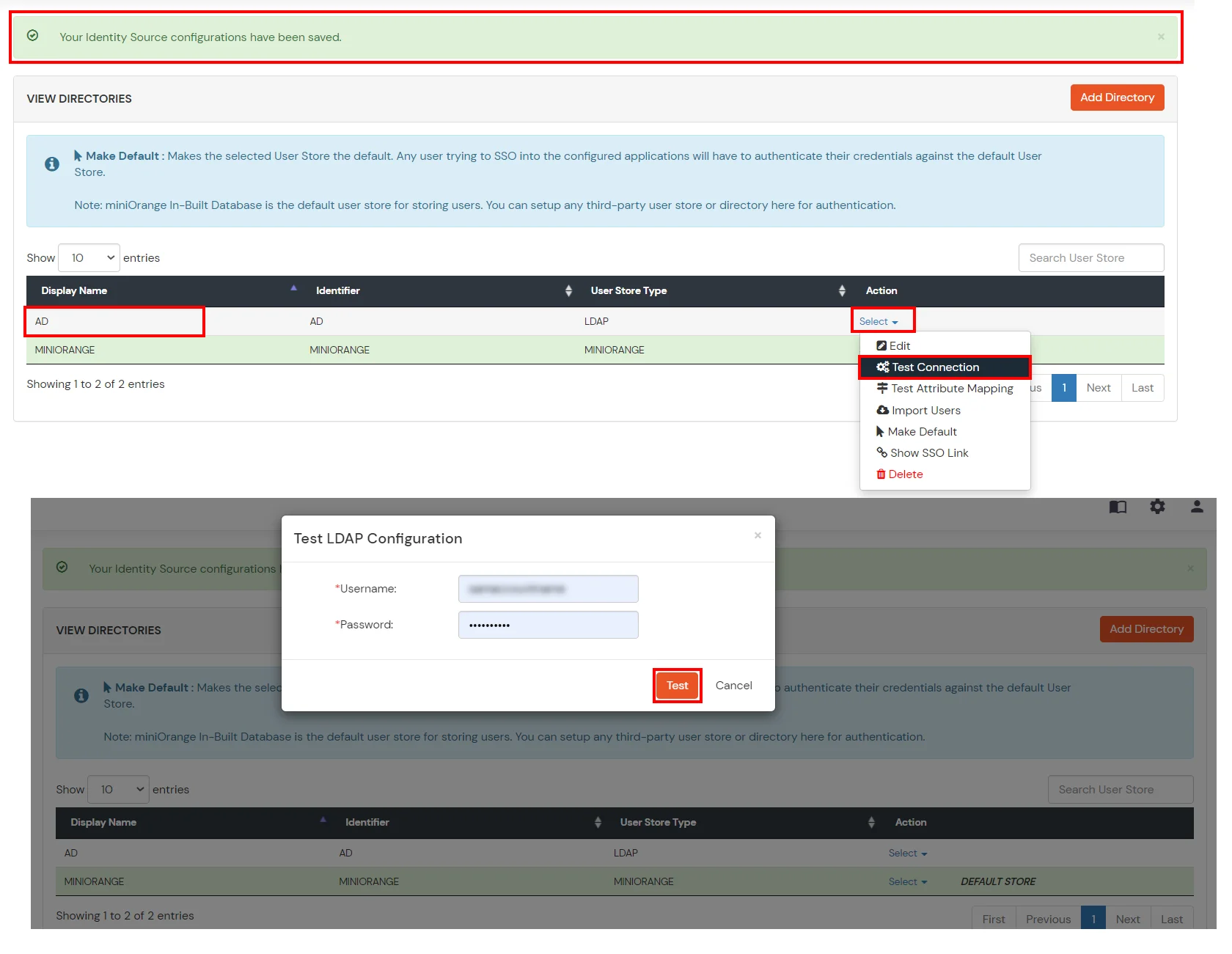
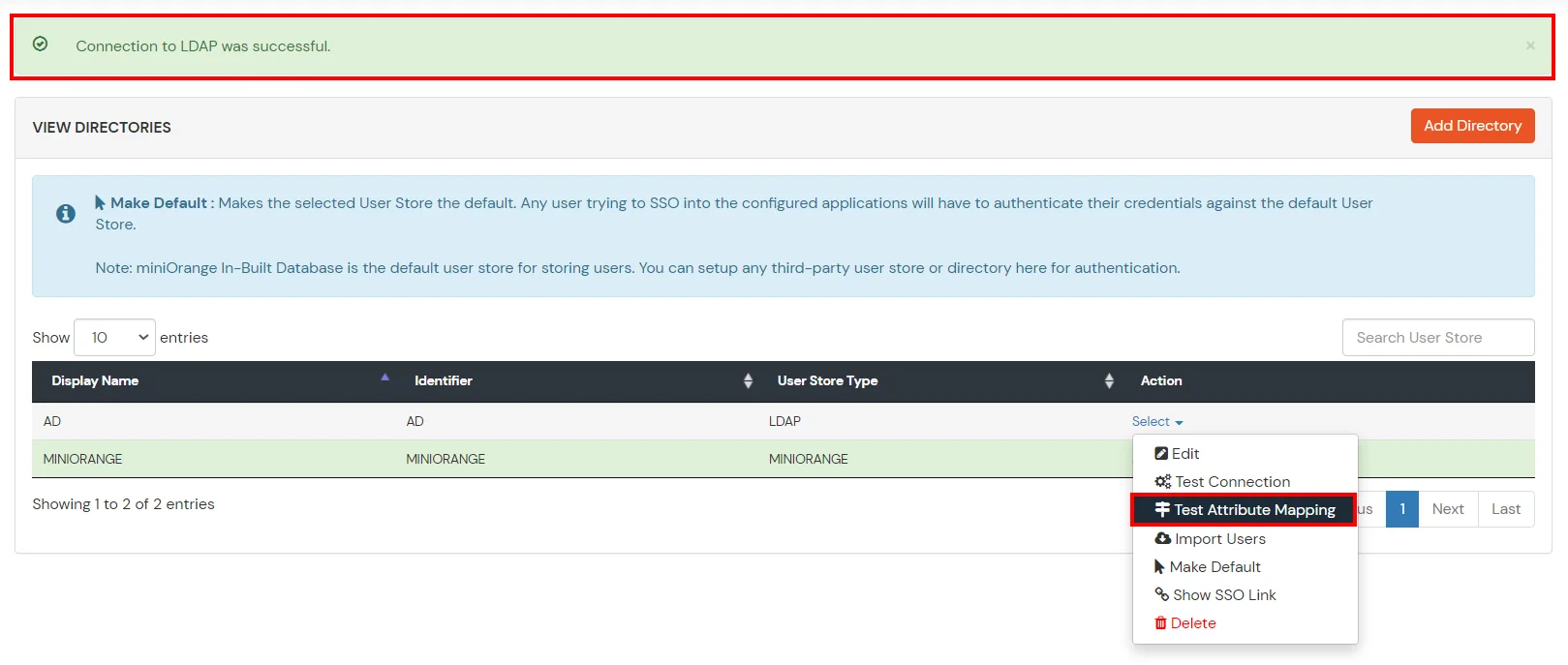
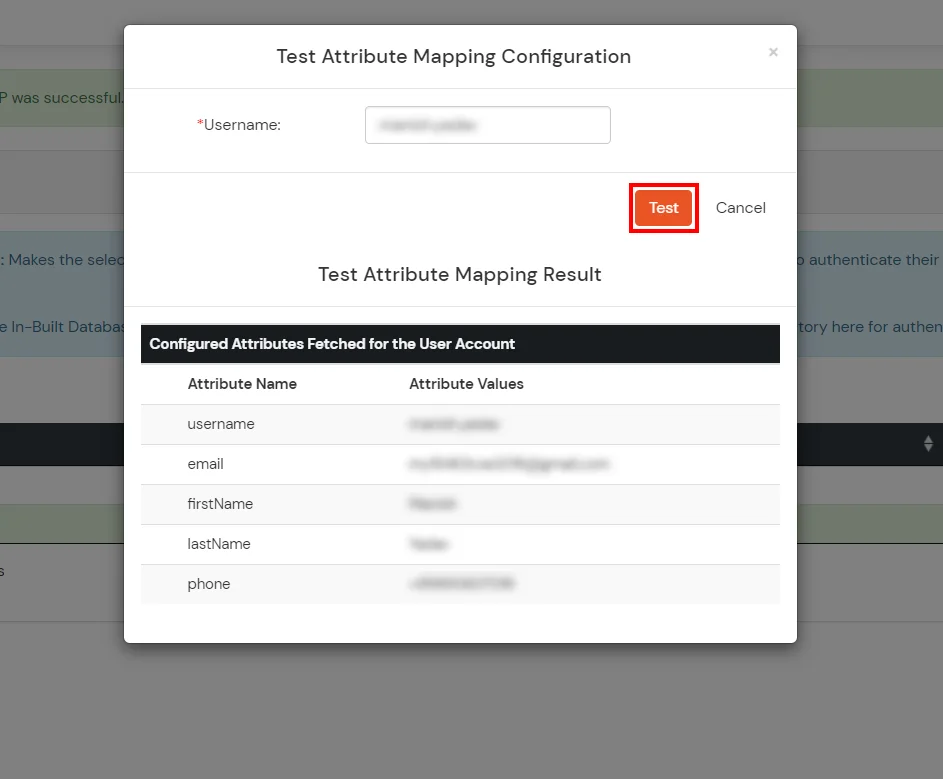
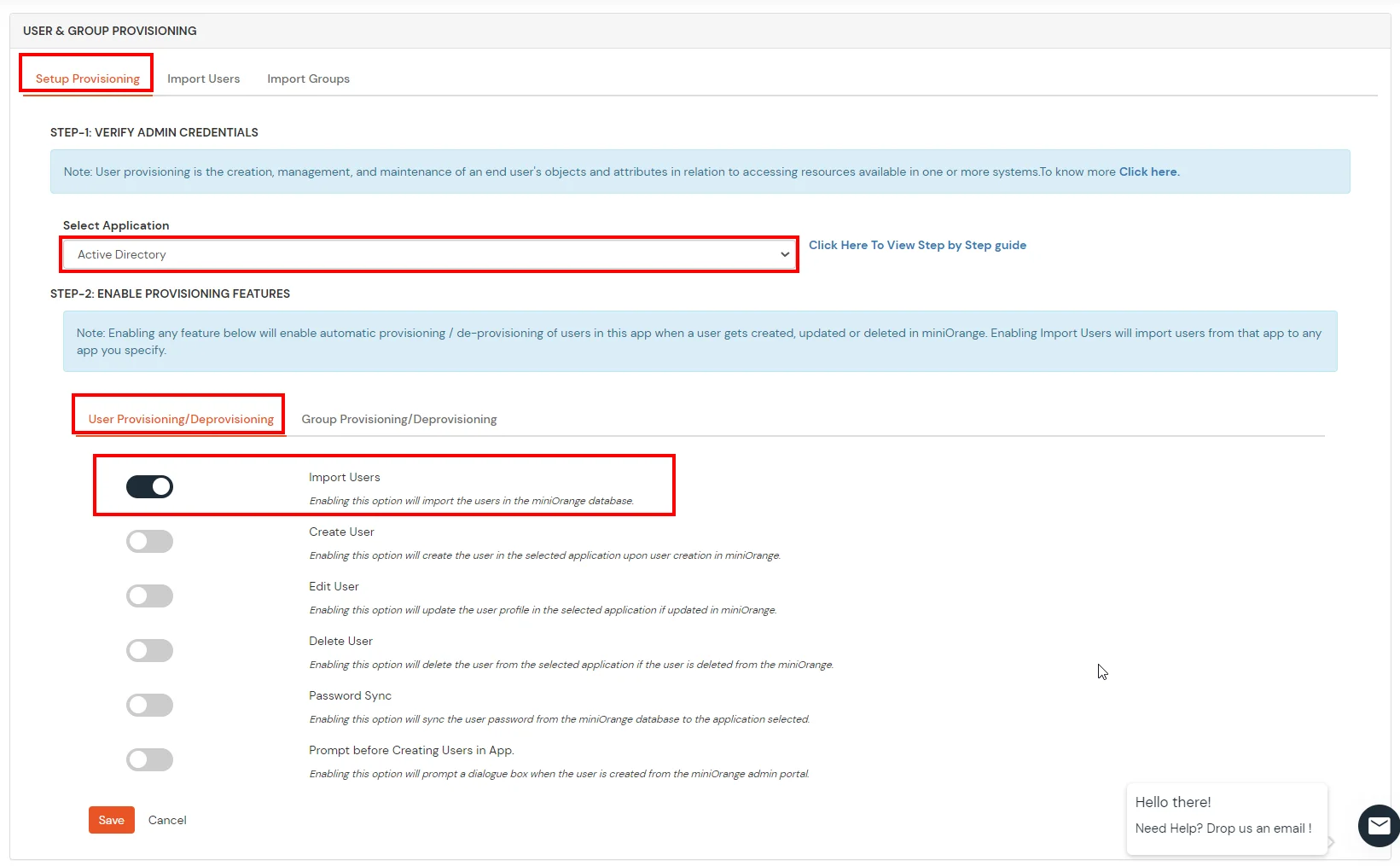
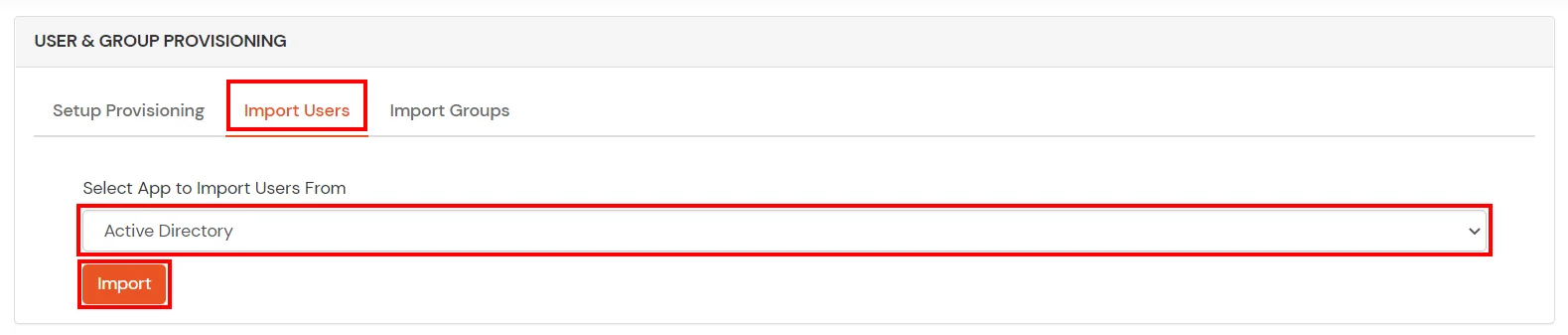
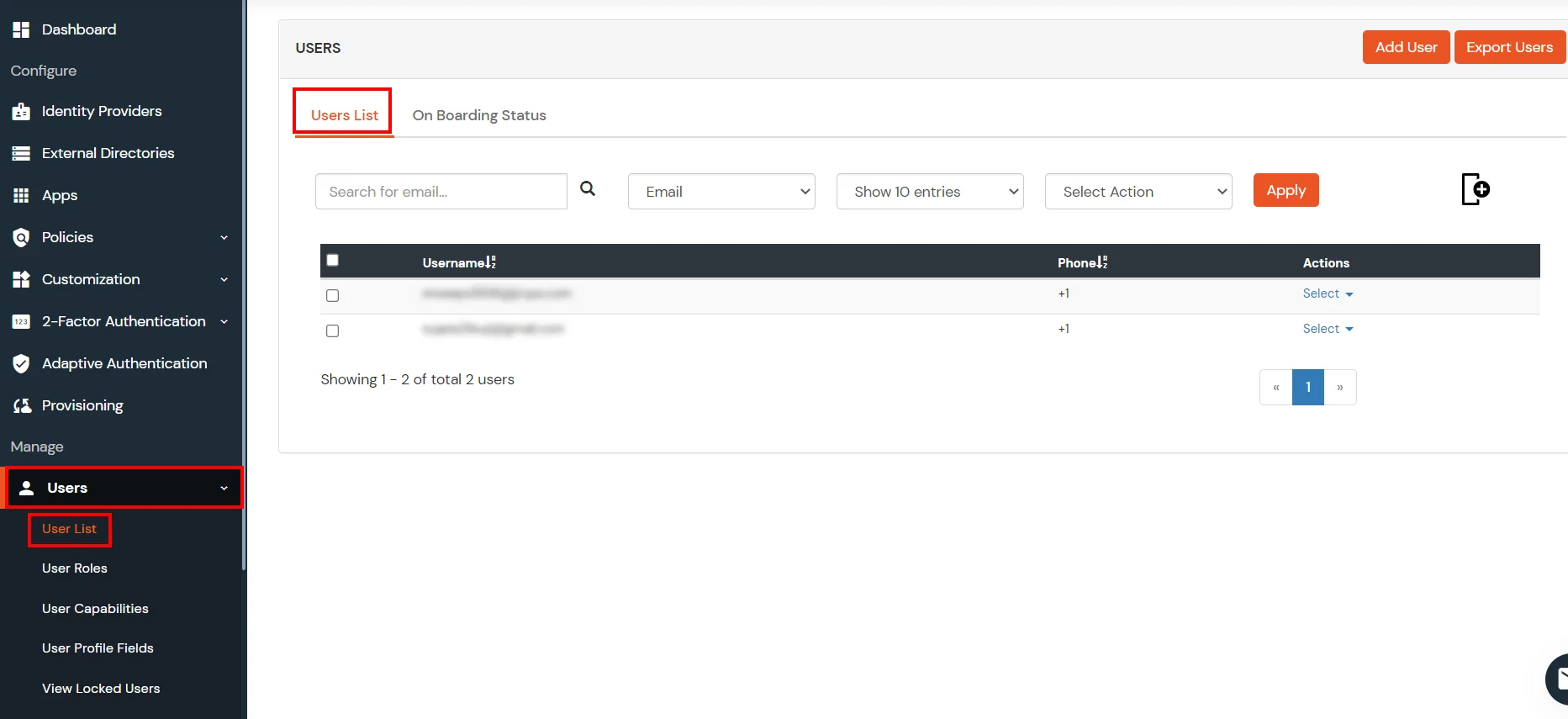
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
1. Create User in miniOrange





2. Bulk Upload Users in miniOrange via Uploading CSV File.



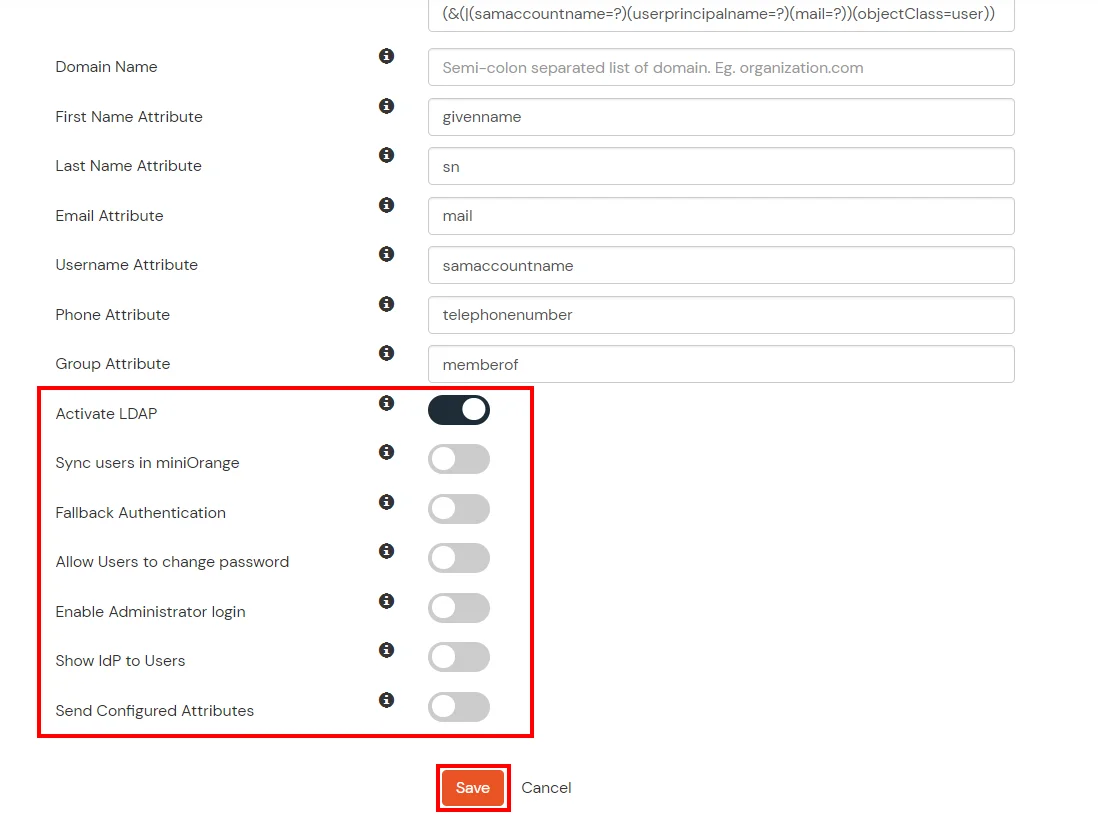
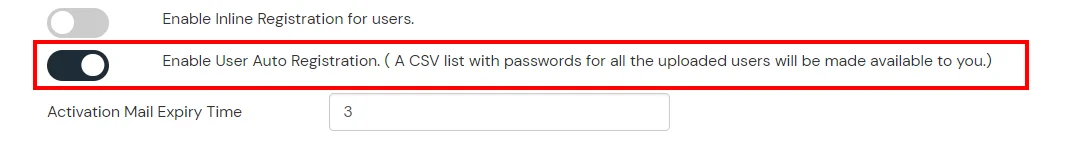
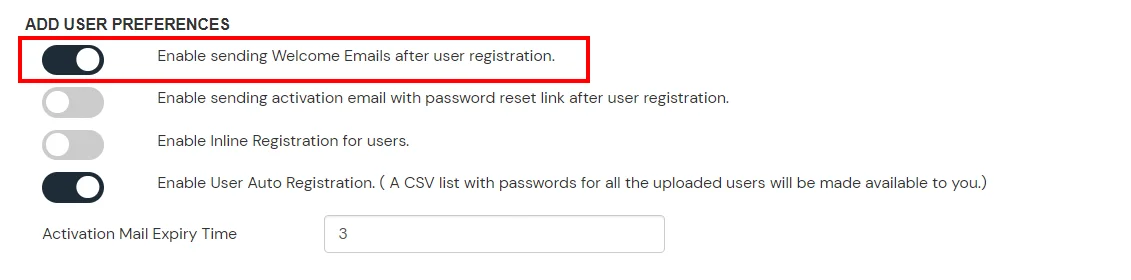
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute | Description |
|---|---|
| Activate LDAP | All user authentications will be done with LDAP credentials if you Activate it |
| Sync users in miniOrange | Users will be created in miniOrange after authentication with LDAP |
| Fallback Authentication | If LDAP credentials fail then user will be authenticated through miniOrange |
| Allow users to change password | This allows your users to change their password. It updates the new credentials in your LDAP server |
| Enable administrator login | On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users | If you enable this option, this IdP will be visible to users |
| Send Configured Attributes | If you enable this option, then only the attributes configured below will be sent in attributes at the time of login |
Refer our guide to setup LDAPS on windows server.
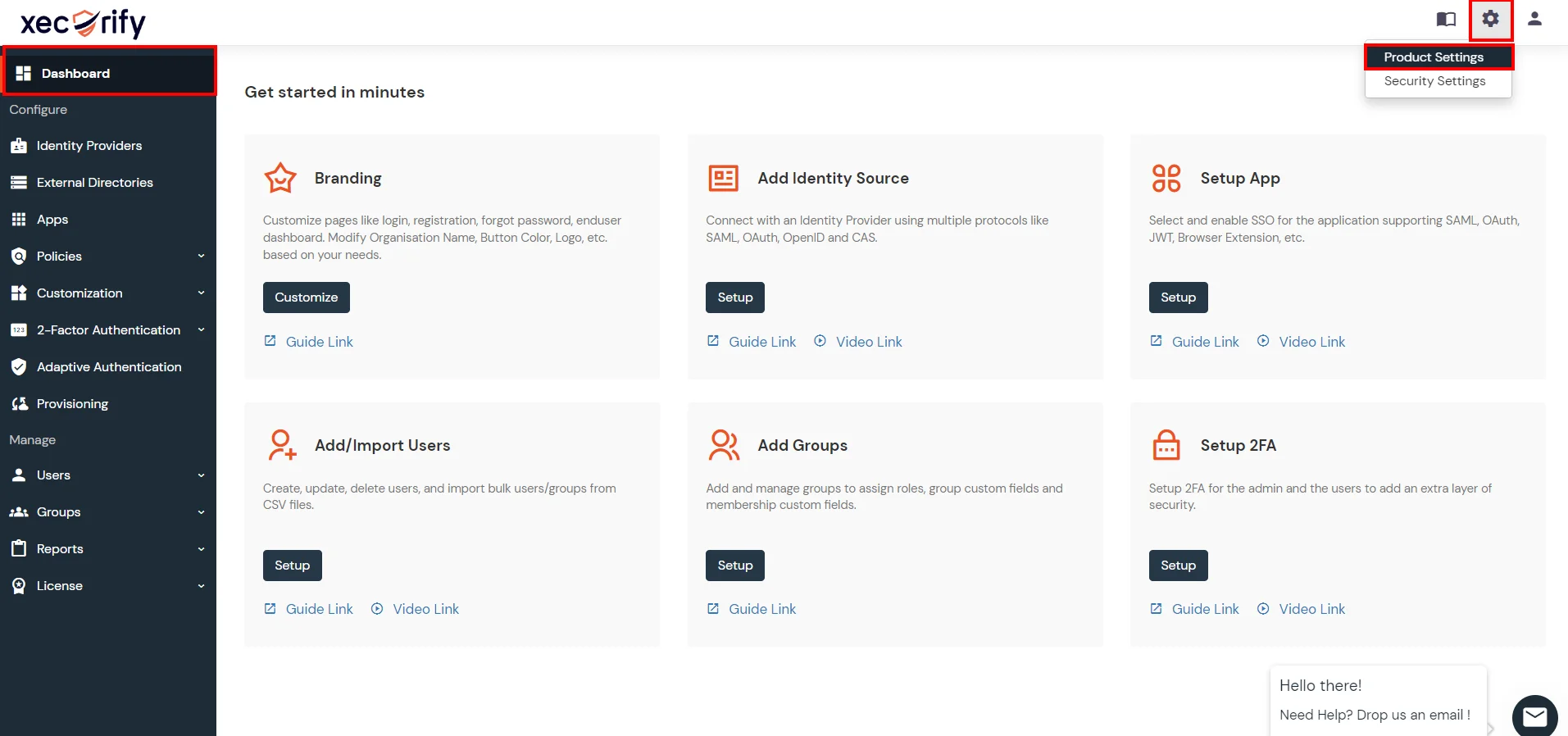
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.

Our Other Identity & Access Management Products