Secure Remote Desktop Web Access (RD Web or RDS) with Multi-factor Authentication (MFA)
Microsoft RD Web Access (RD Web) MFA configuration initiates with a user trying to login into Remote Desktop Service (RDS) either through a Remote Desktop Client (using RDP) or via the Remote Desktop Web Access (RD Web) login page from his/her browser. After logging in, a RADIUS request is sent from the miniOrange RD Web component installed on the target machine to the miniOrange RADIUS server, which authenticates the user via Local AD (Active Directory), and after a successful authentication, Two / Multi factor authentication of the user is invoked. After the user validates himself/herself, he/she is granted access to the Remote Desktop Web Service.
What is Multi-Factor Authentication (MFA)?
Multi-Factor Authentication (MFA) is an authentication method that requires the user to authenticate themselves for two or more factors, in order to gain access to company resources, applications, or servers (Remote desktop web access). Enabling Multi-Factor Authentication (MFA) means that users need to provide additional verification factors apart from their username and passwords thus increasing the security of the organization's resources.
How Remote Desktop Web Access (RD Web) 2FA/MFA Works?
- In this case, the user goes to Remote Desktop Web Access (RD Web) login page from his browser to connect to the Remote Desktop Service.He enters his username and password, and on submission, the RADIUS request from RD Web component installed on target machine is sent to the miniOrange RADIUS server which authenticates the user via local AD in the target machine.
- Once authenticated, it sends a RADIUS challenge to Remote Desktop Web Access (RD Web), and the RD Web shows OTP screen on browser now. Once the user enters the One Time Passcode (OTP), the miniOrange IdP verifies it and grants/denies access to the RDS.
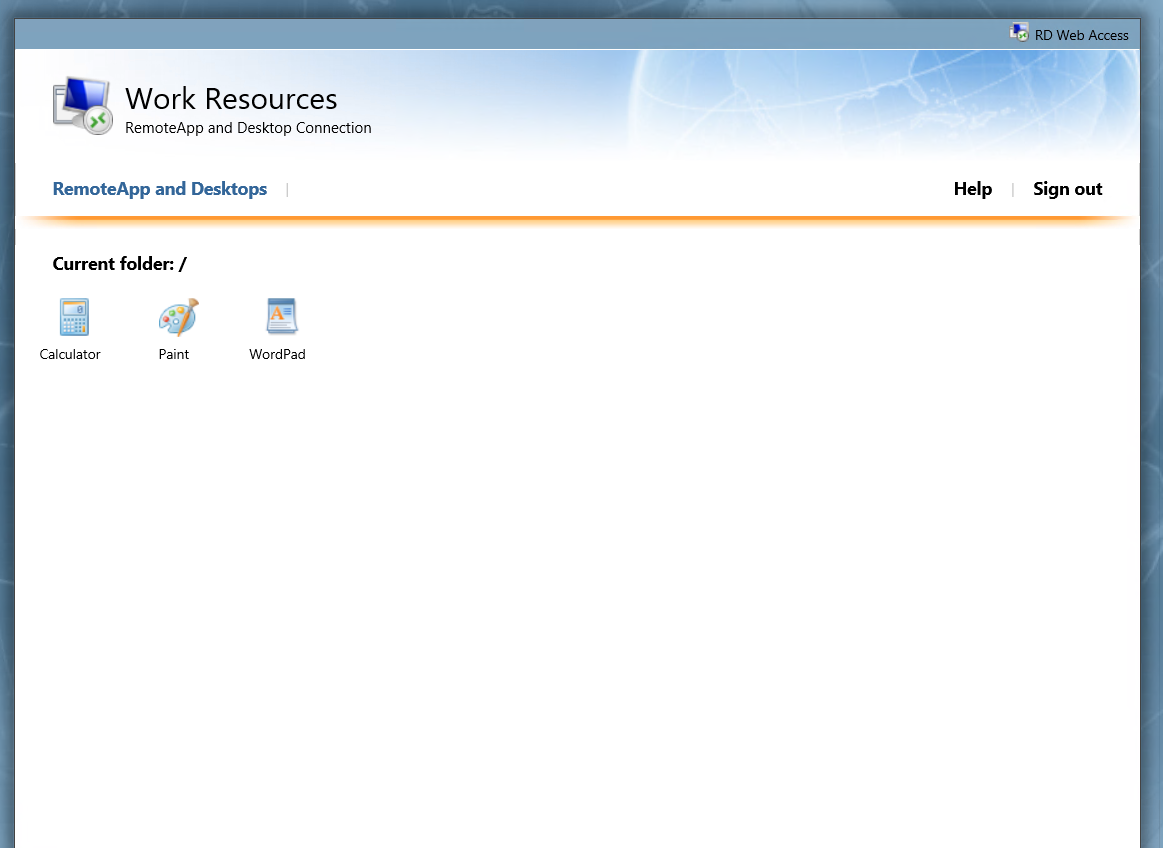
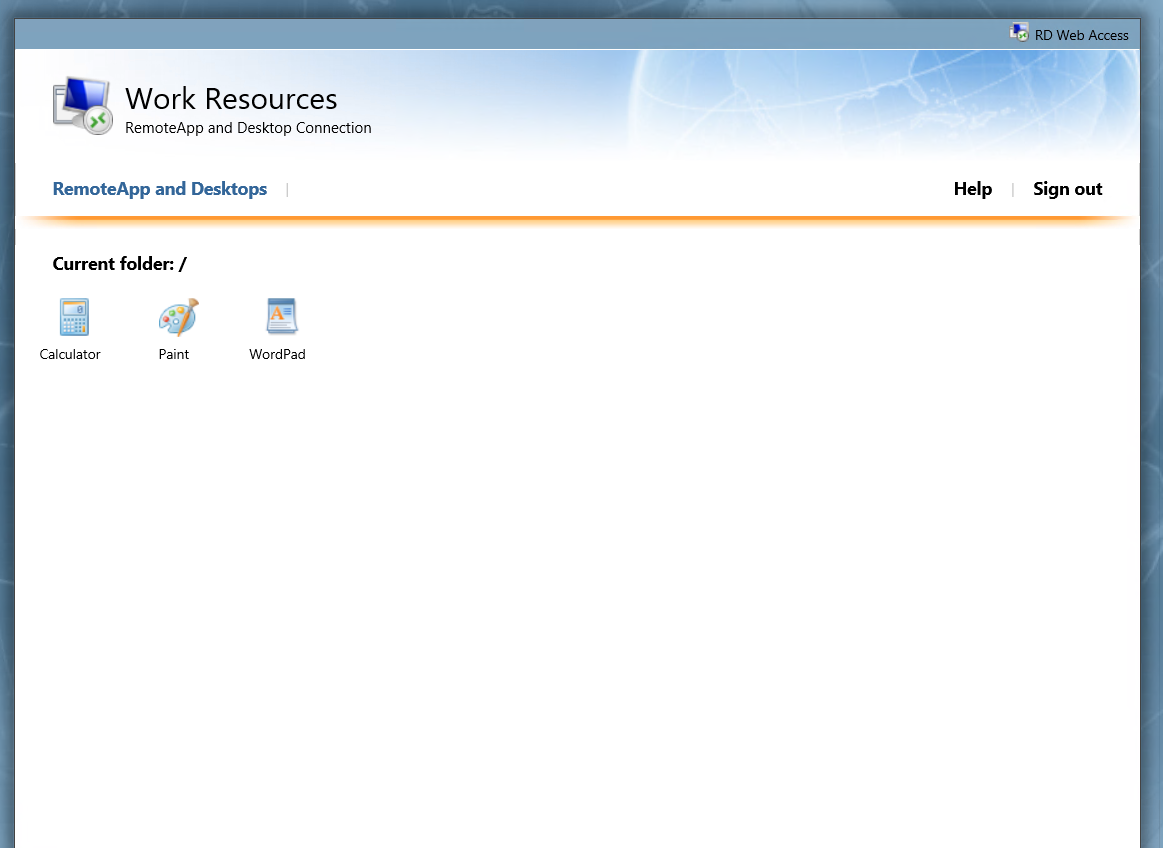
- With this, after the user is connected to the Remote Desktop Service, the user can also gain access to published remote app icons on his browser screen, since the session has already been created for the user.

Integrate hassle-free MFA for login to stop password-based attacks. IT gets added security, and users get easy access to the apps and endpoints they need — with just their domain credentials. Always verify identities before allowing access to endpoints for increased identity assurance and reduced risk and exposure. miniOrange Credential Providers can be installed on Microsoft Windows client and server operating systems to add two-factor Authentication to Remote Desktop.
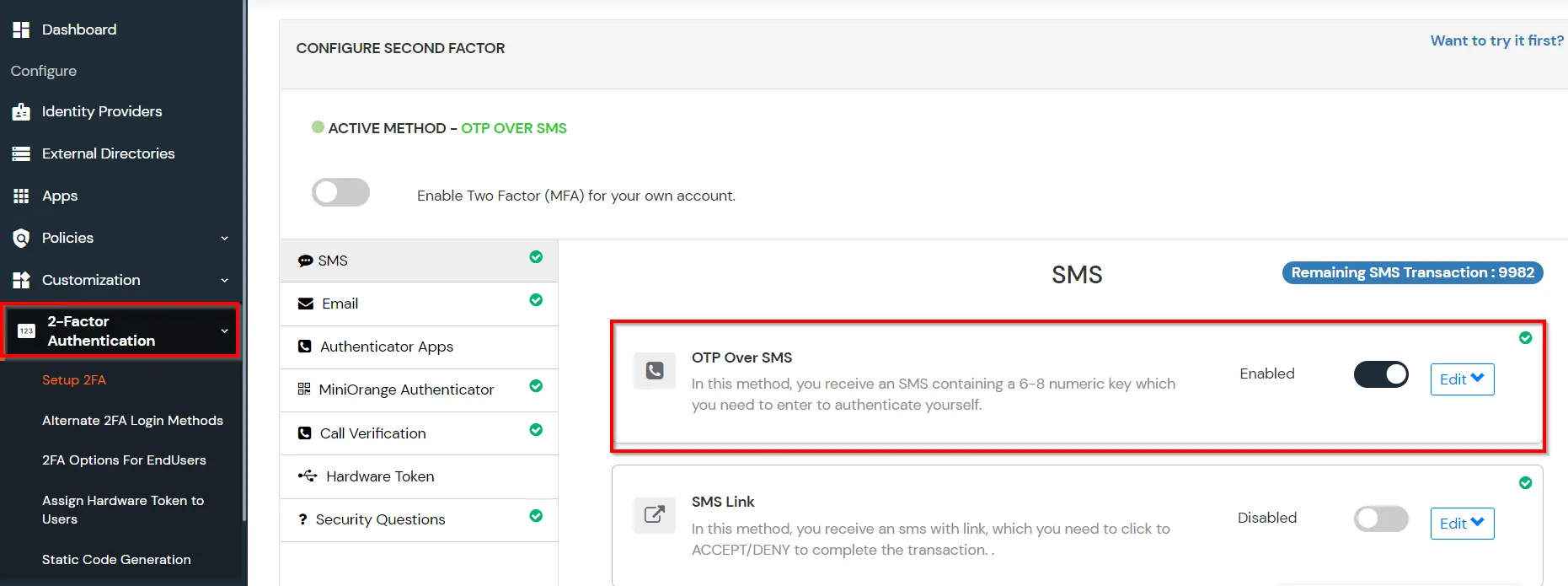
miniOrange supports following Authentication Methods for 2FA:
- miniOrange Push (miniOrange Authenticator App)
- miniOrange Soft Token (miniOrange Authenticator App)
- Google Authenticator
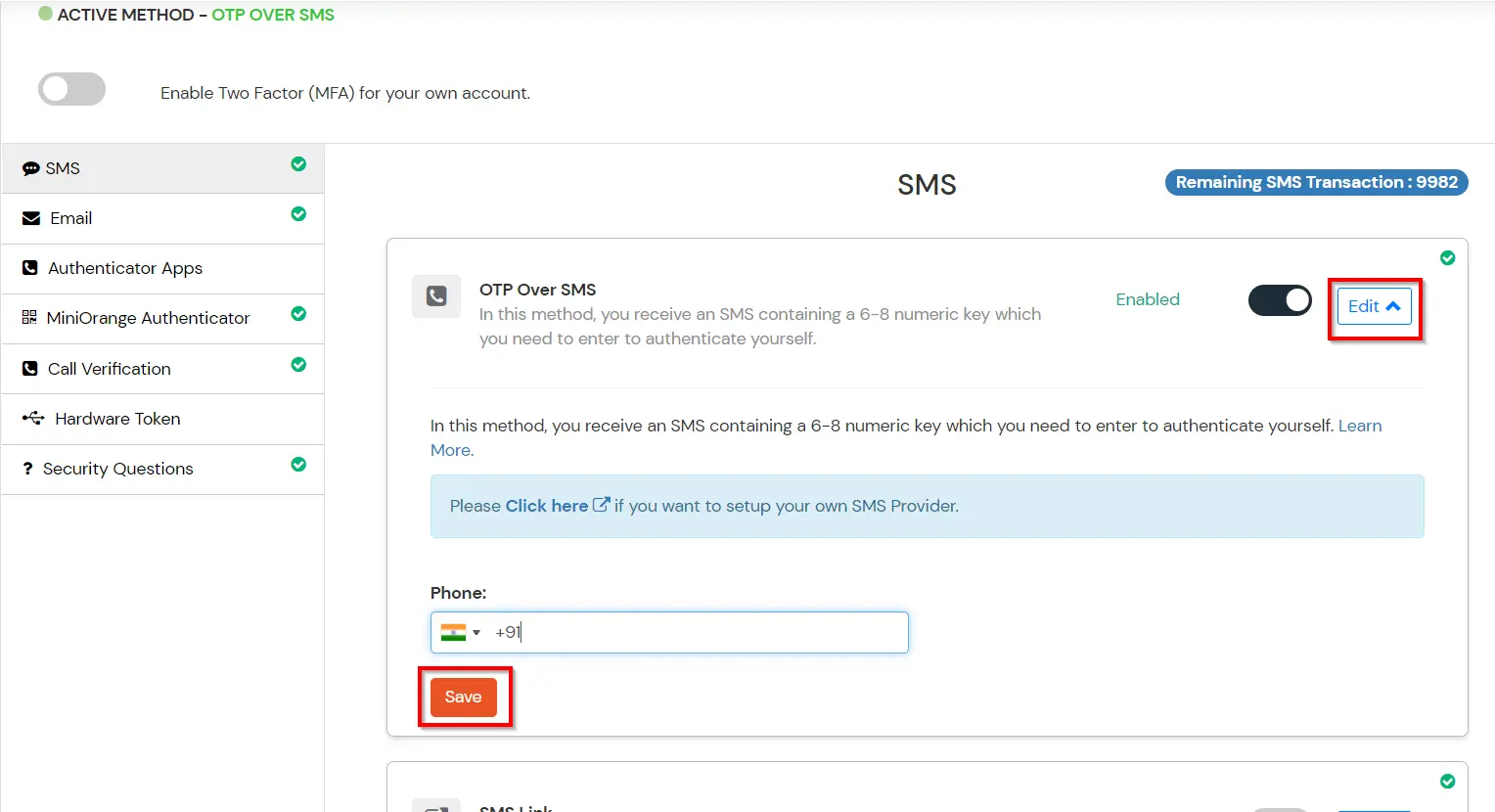
- OTP Over SMS/EMAIL
- Hardware Token
- Check out 15+ MFA/2FA methods
Get Free Installation Help - Book a Slot
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup Two-Factor Authentication for RD Web solution in your environment with 30 days trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you setting it up in no time.
Follow the Step-by-Step Guide given below to configure RD Web MFA
1. Download 2FA for RD Web Module
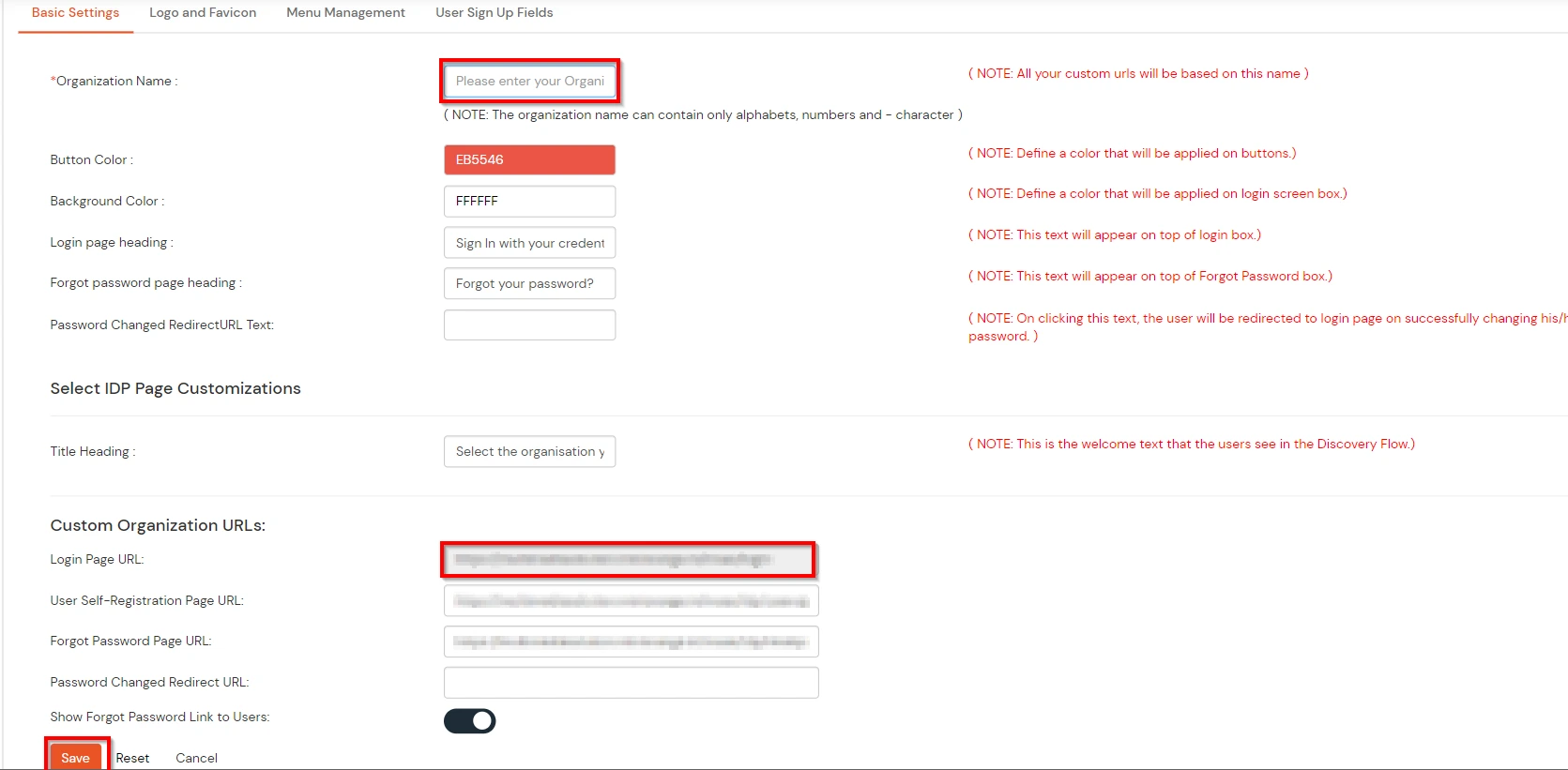
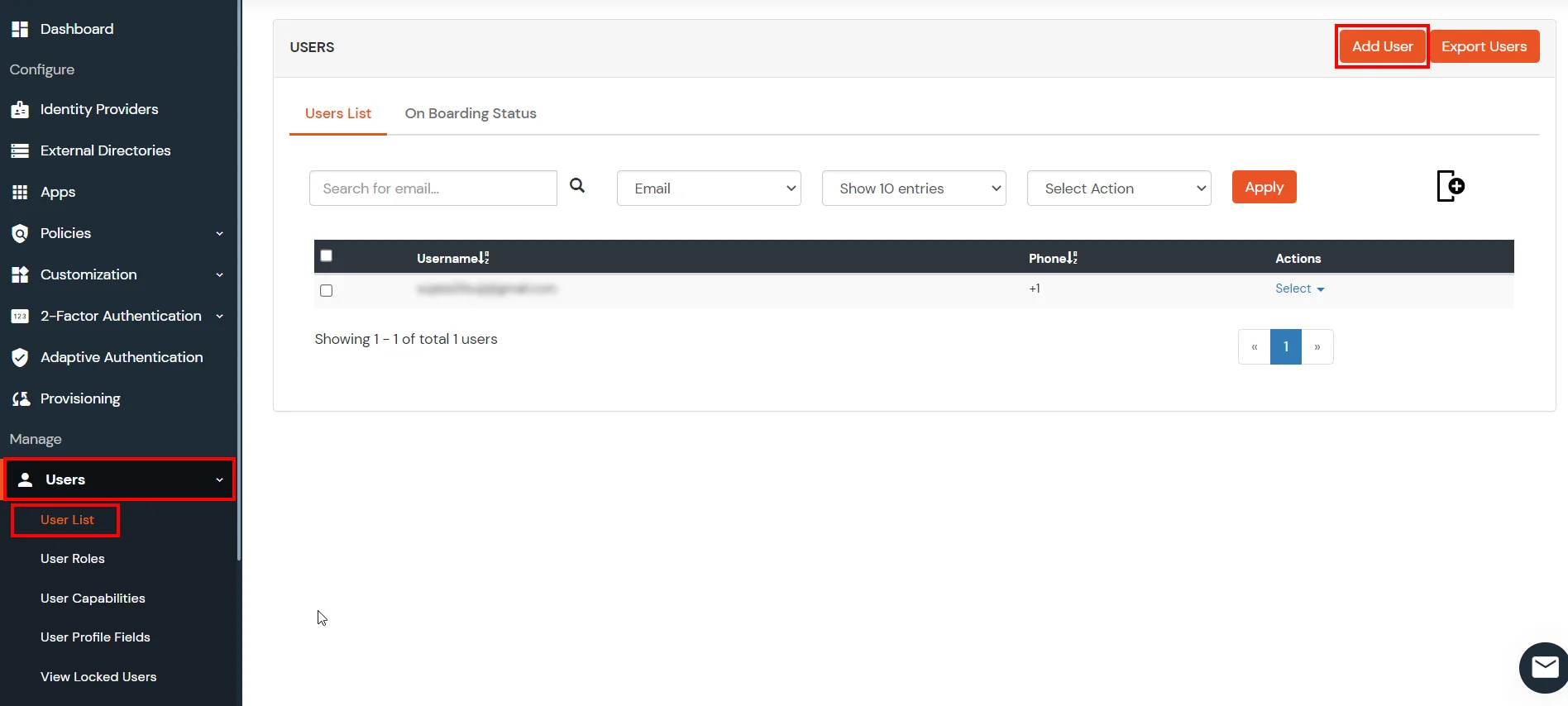
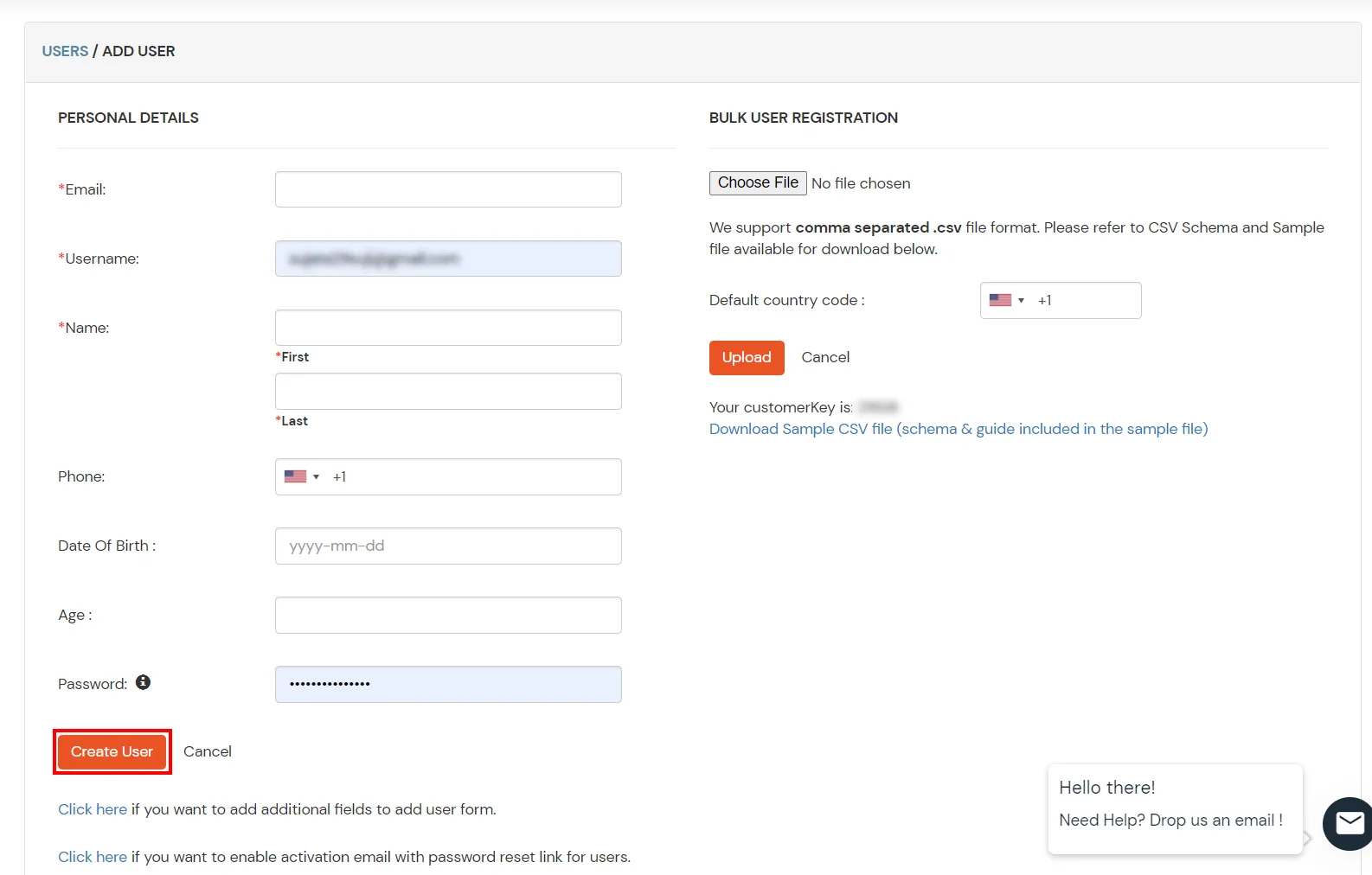
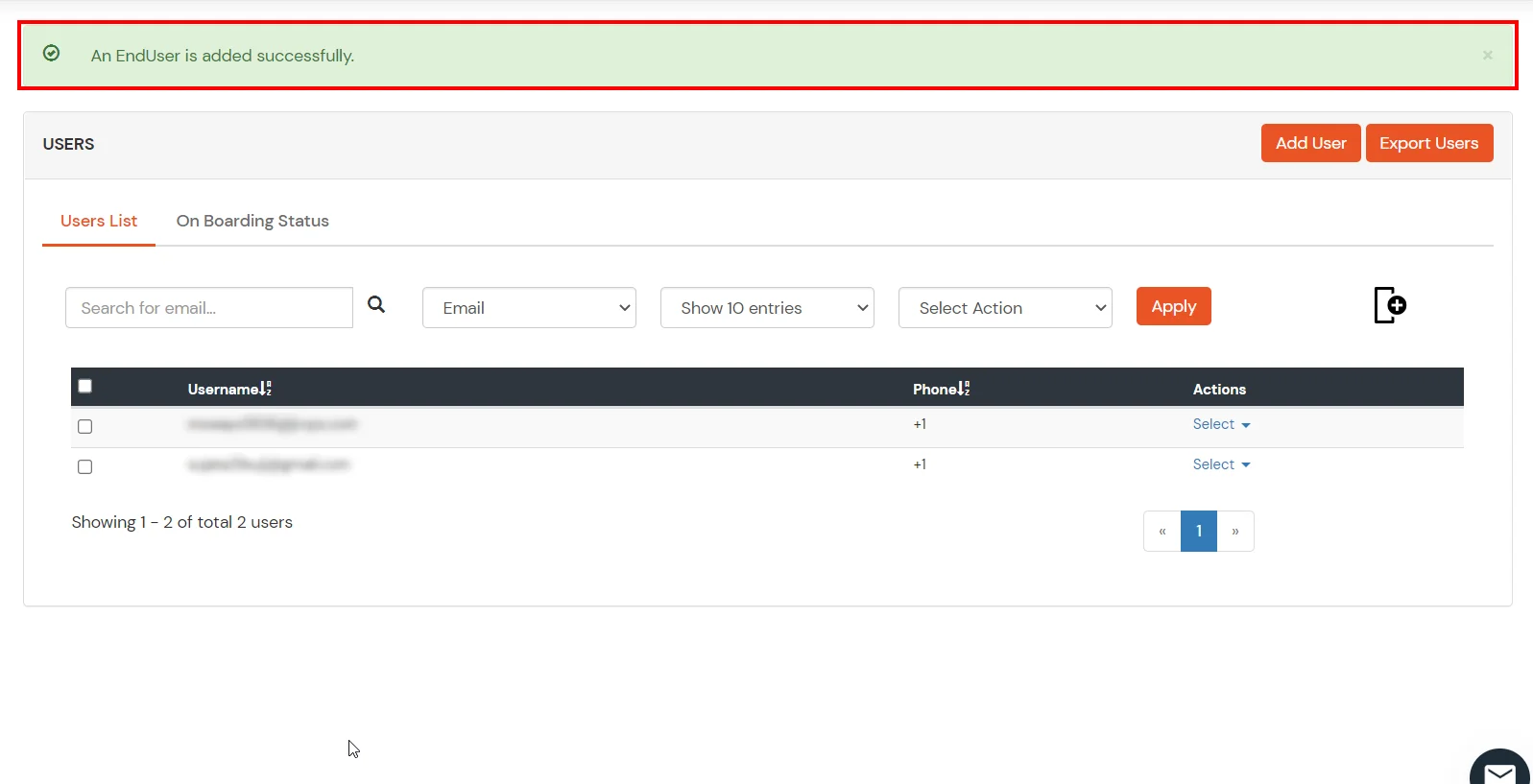
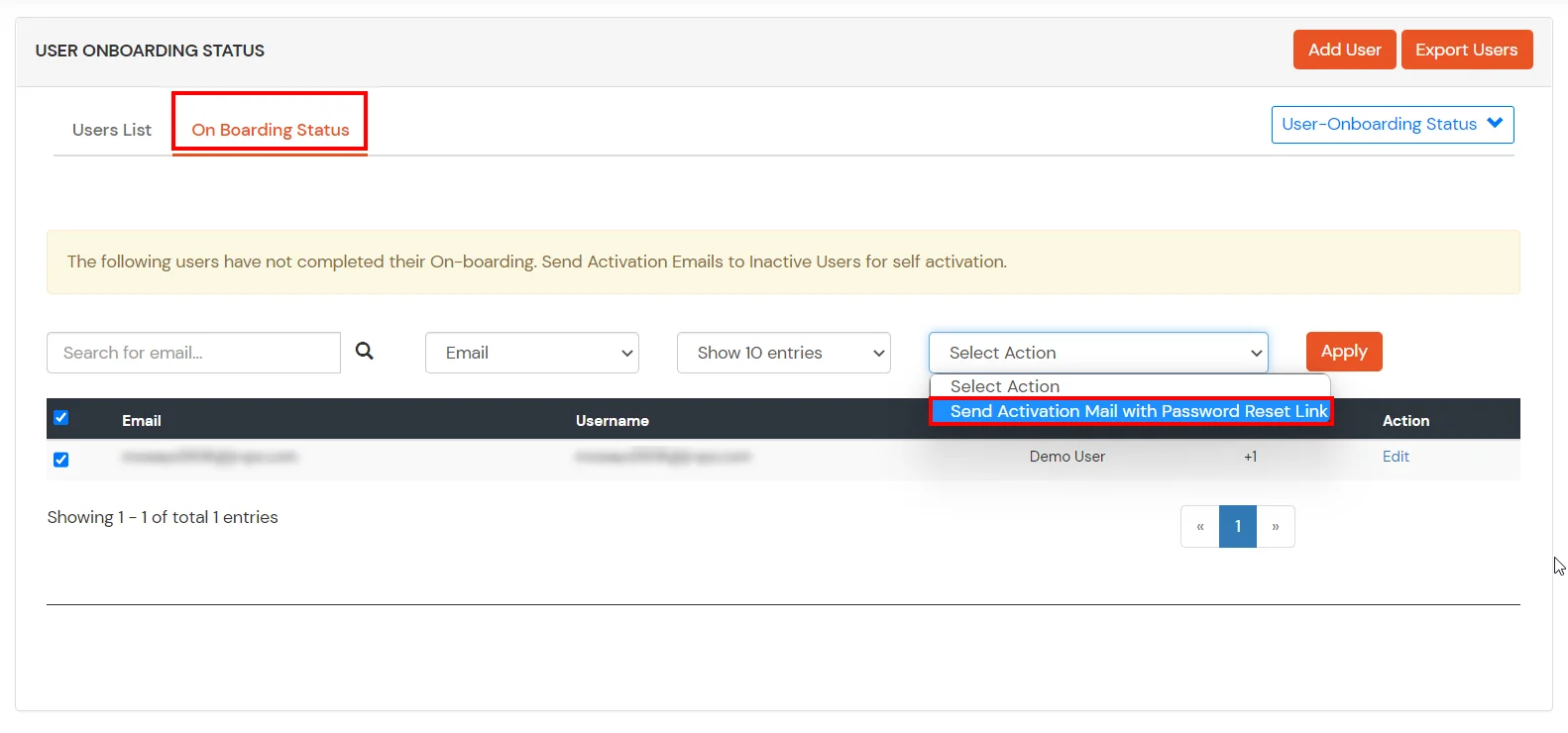
- Login into miniOrange Admin Console.
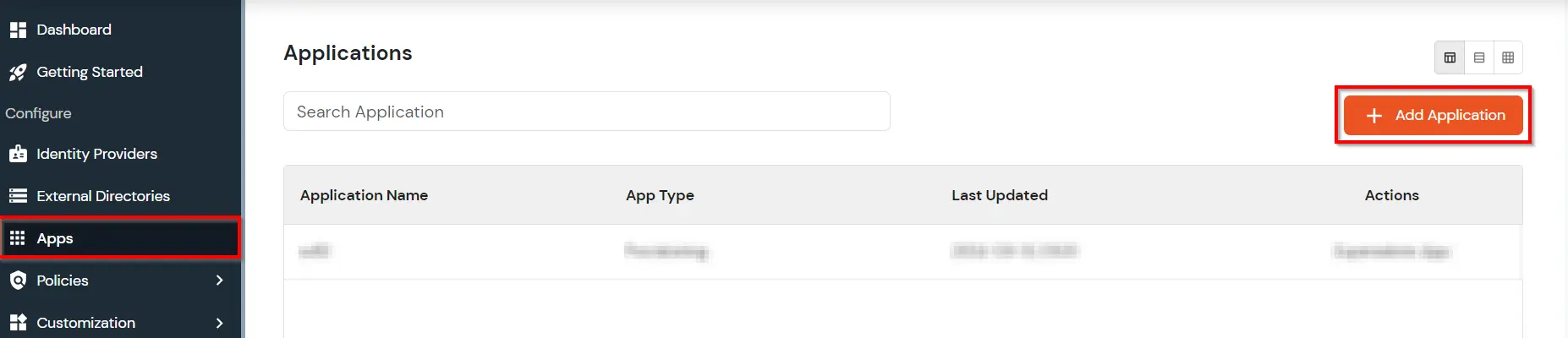
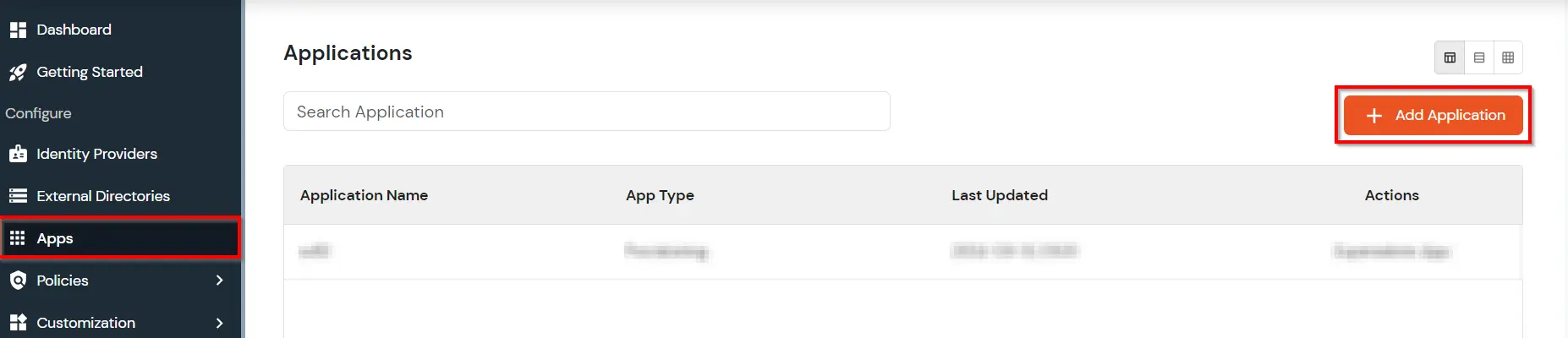
- Go to Apps. Click on Add Application button.
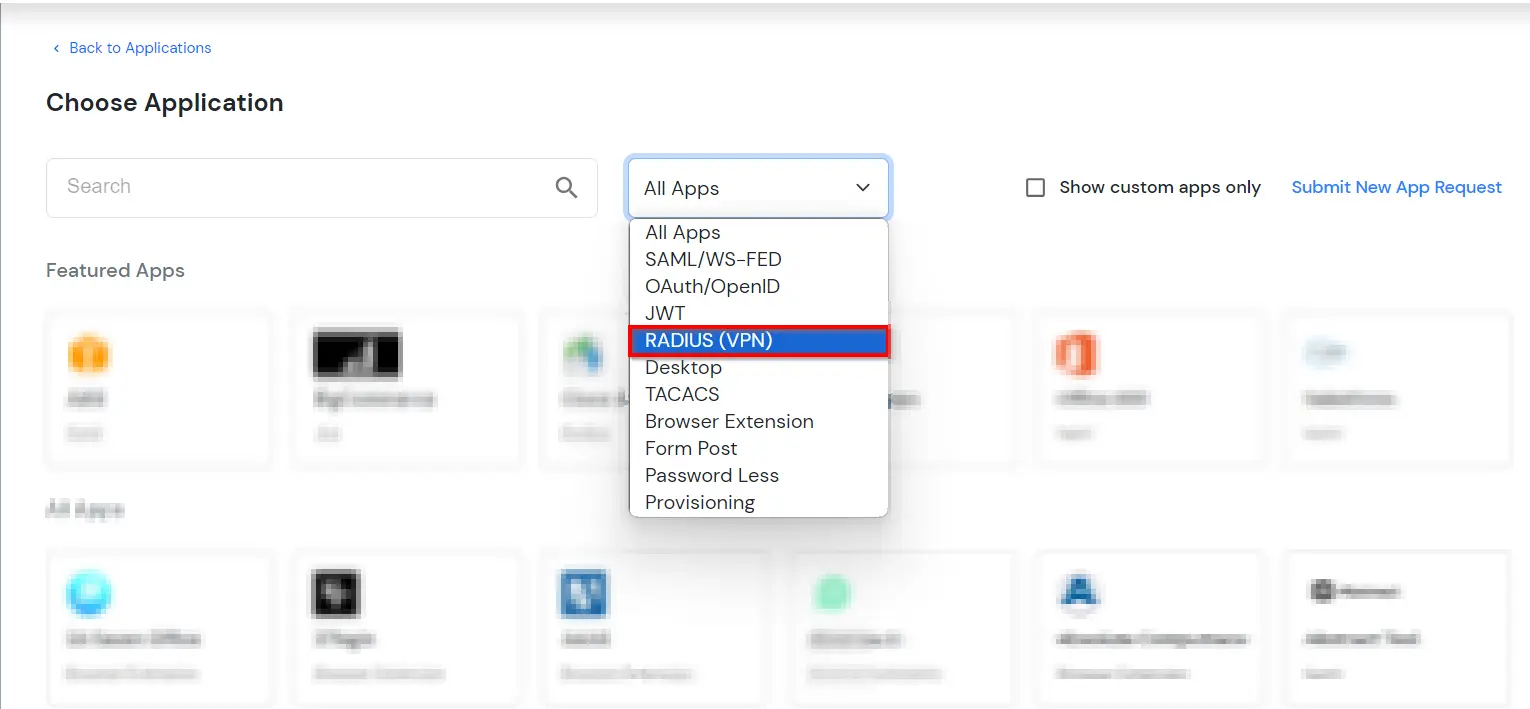
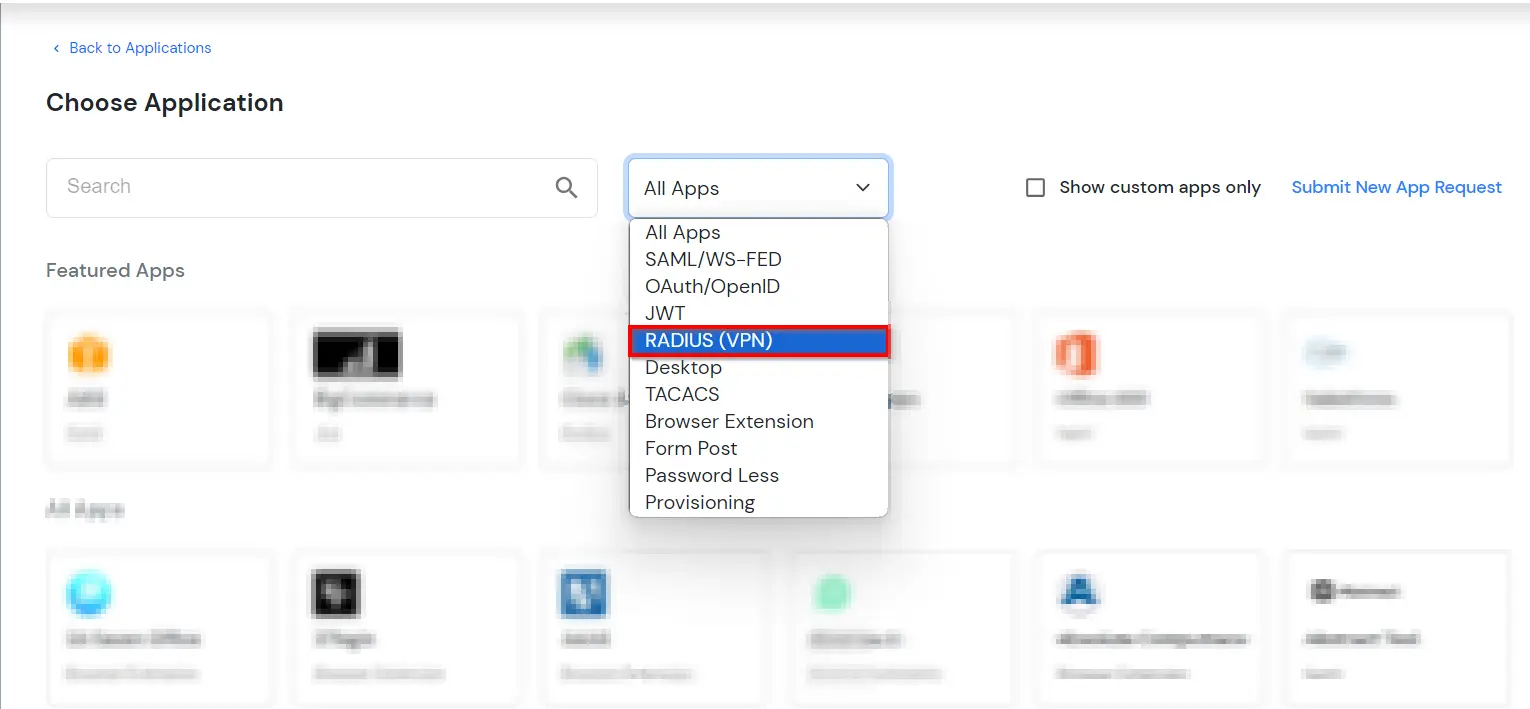
- In Choose Application Type click on Create App button in RADIUS application type.
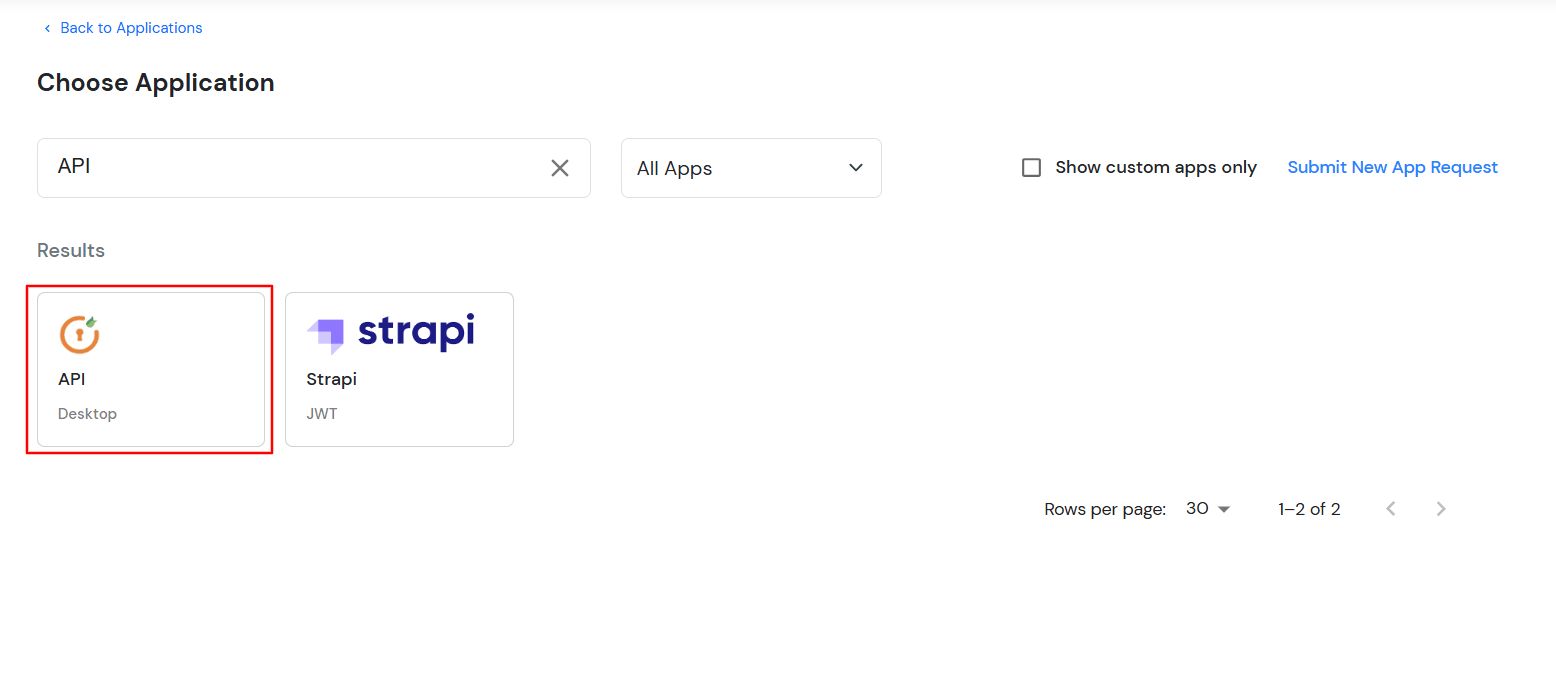
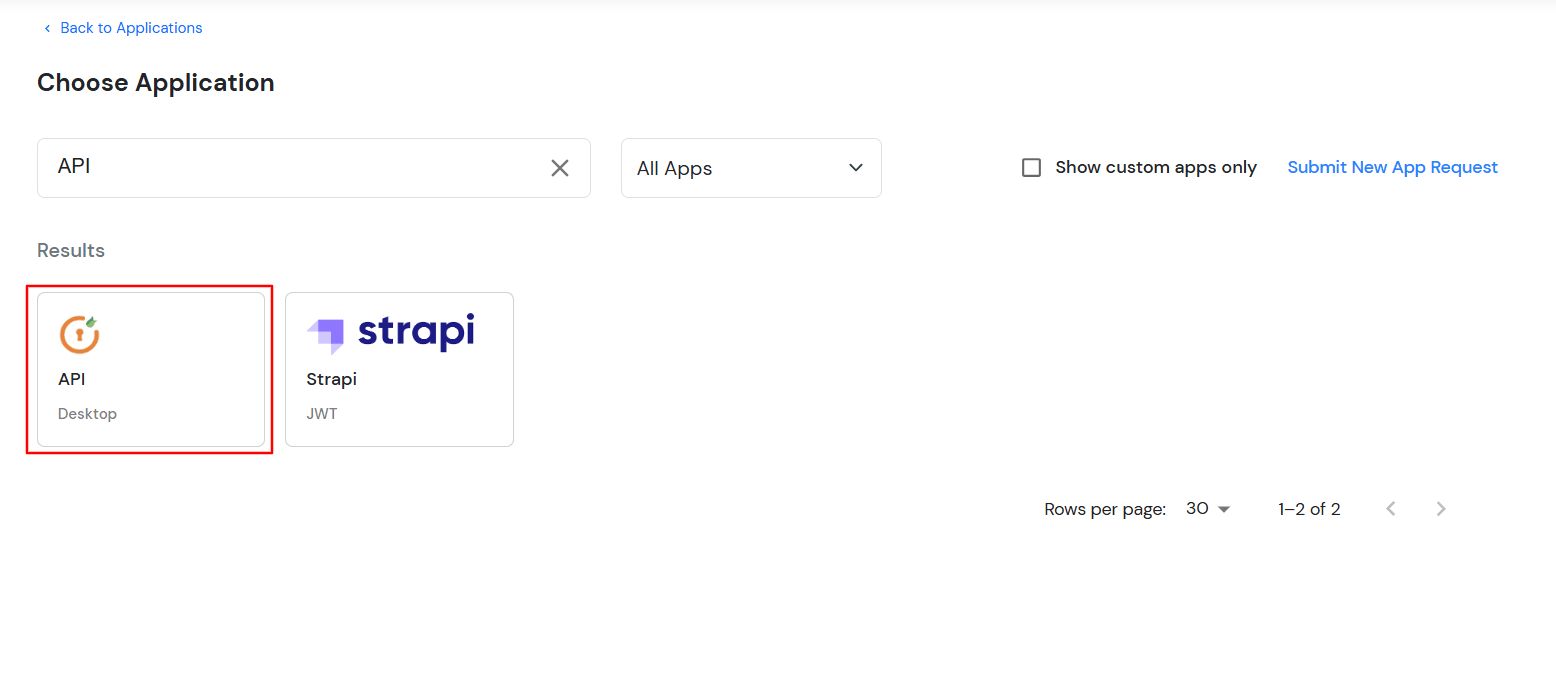
- Click on Microsoft RD Web.
- Click on download the 2FA Module link to download the module.

2. Setup miniOrange Remote Desktop Web Access (RD Web)
- Install the Remote Desktop Web Access (RD Web) module. Unzip the module anywhere on your pc. C:/ for example.
- Take a backup copy of your C:/Windows/Web/RdWeb folder.
- Replace the RDWeb folder extracted from the zip in C:/Windows/Web/RdWeb and refresh RD Web.
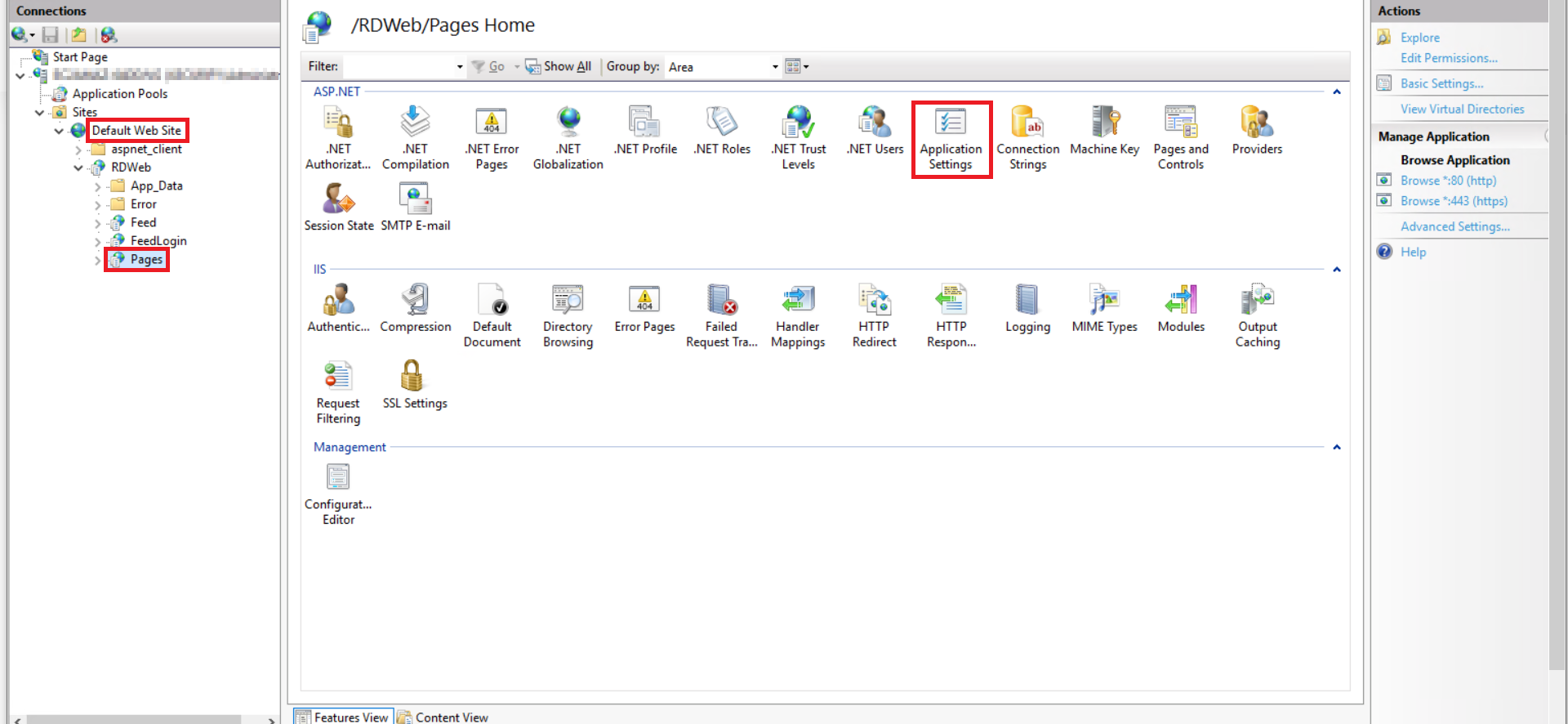
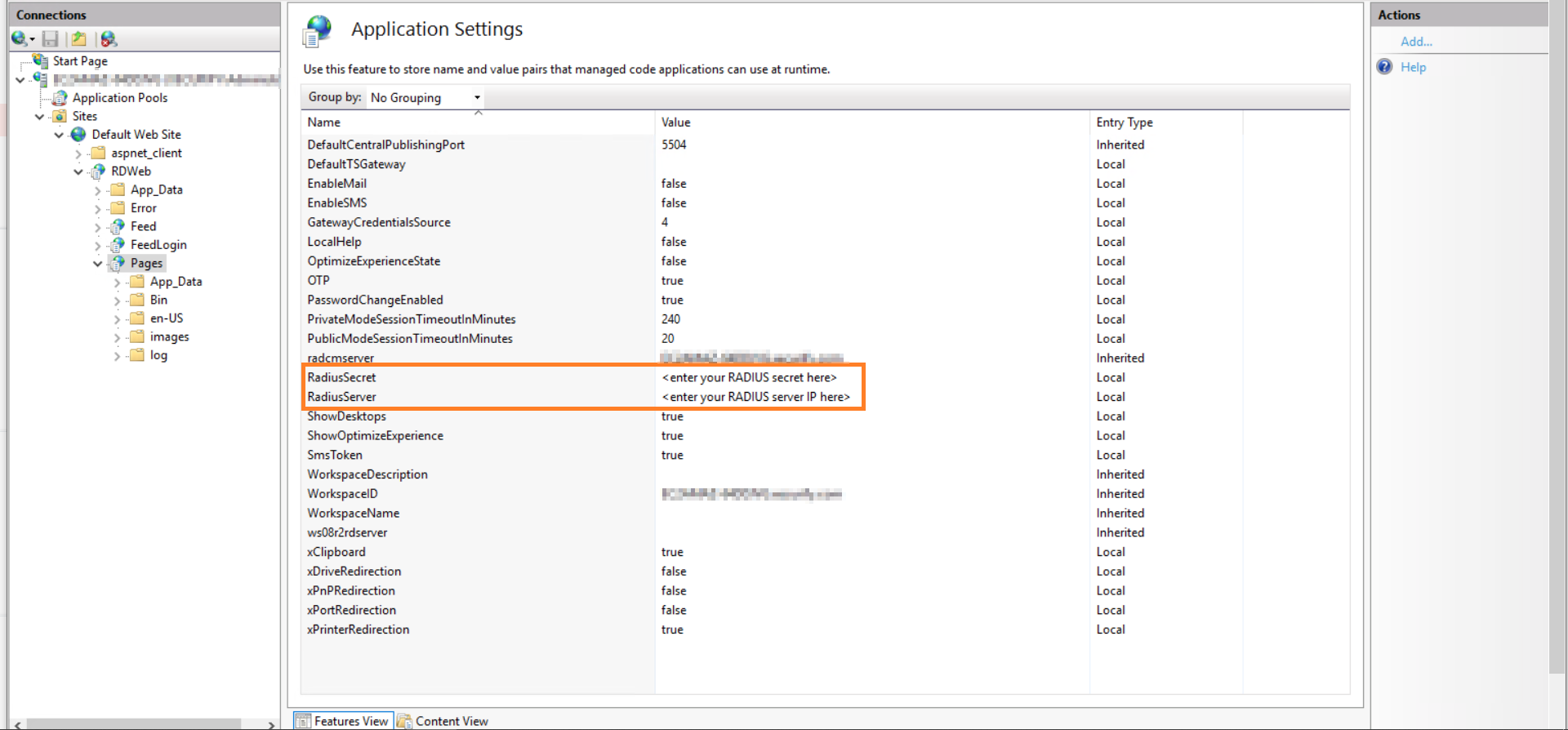
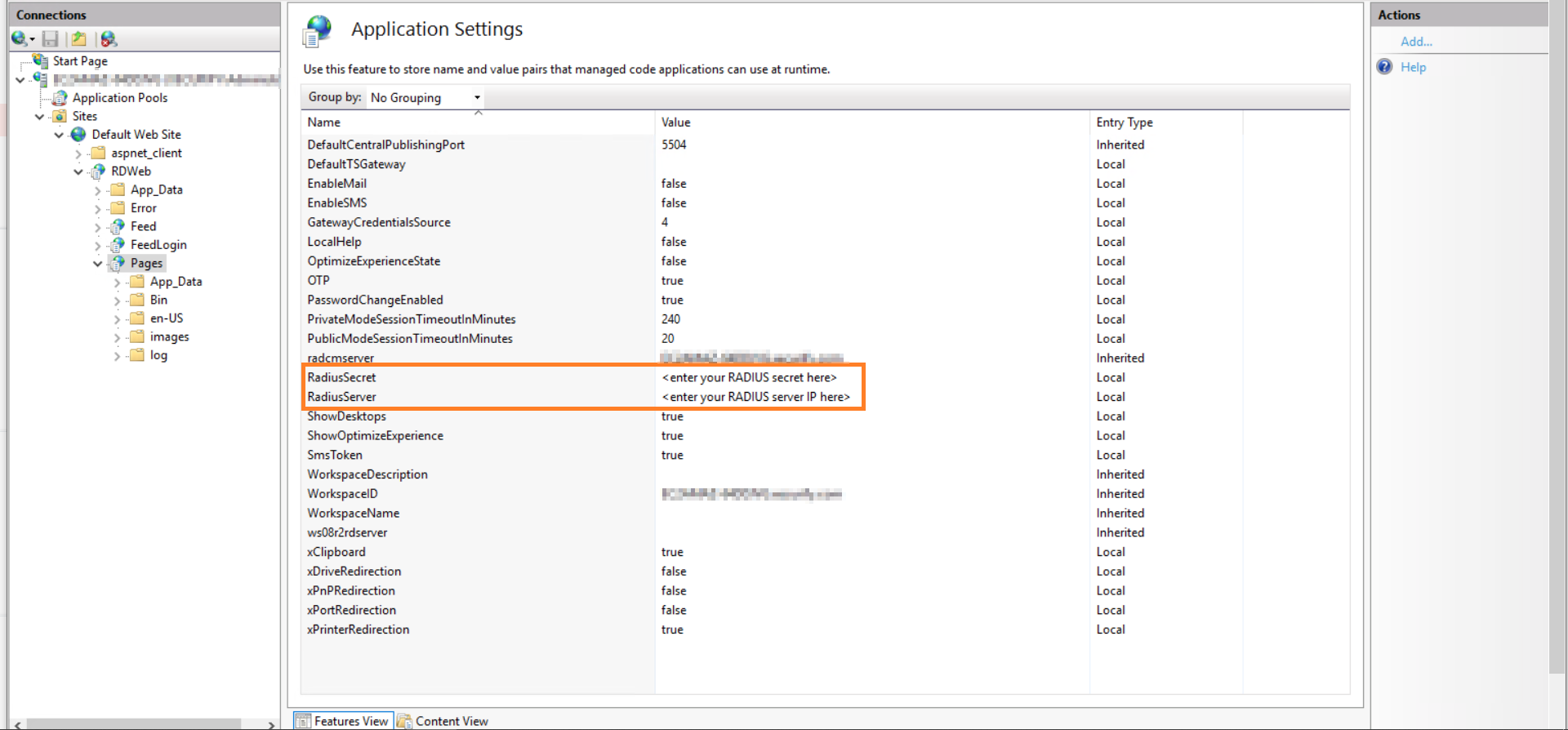
- Go to IIS Manager, Open Default Site -> RD Web -> Pages.
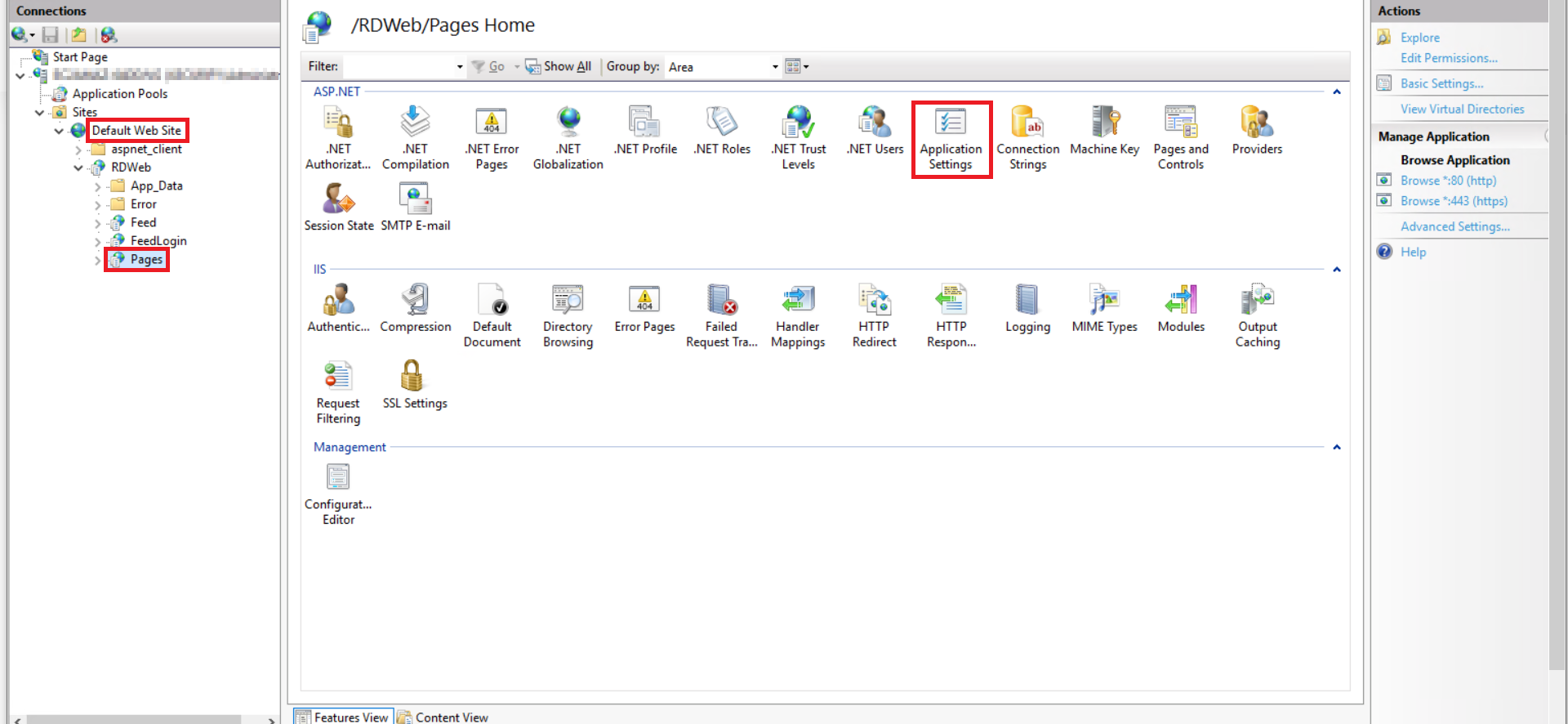
- Open application settings, Change Radius Server IP and secret of IDP. Once that is configured.
3. Configure Two-Factor Authentication(2FA) for RD Web
4. Test Your Setup
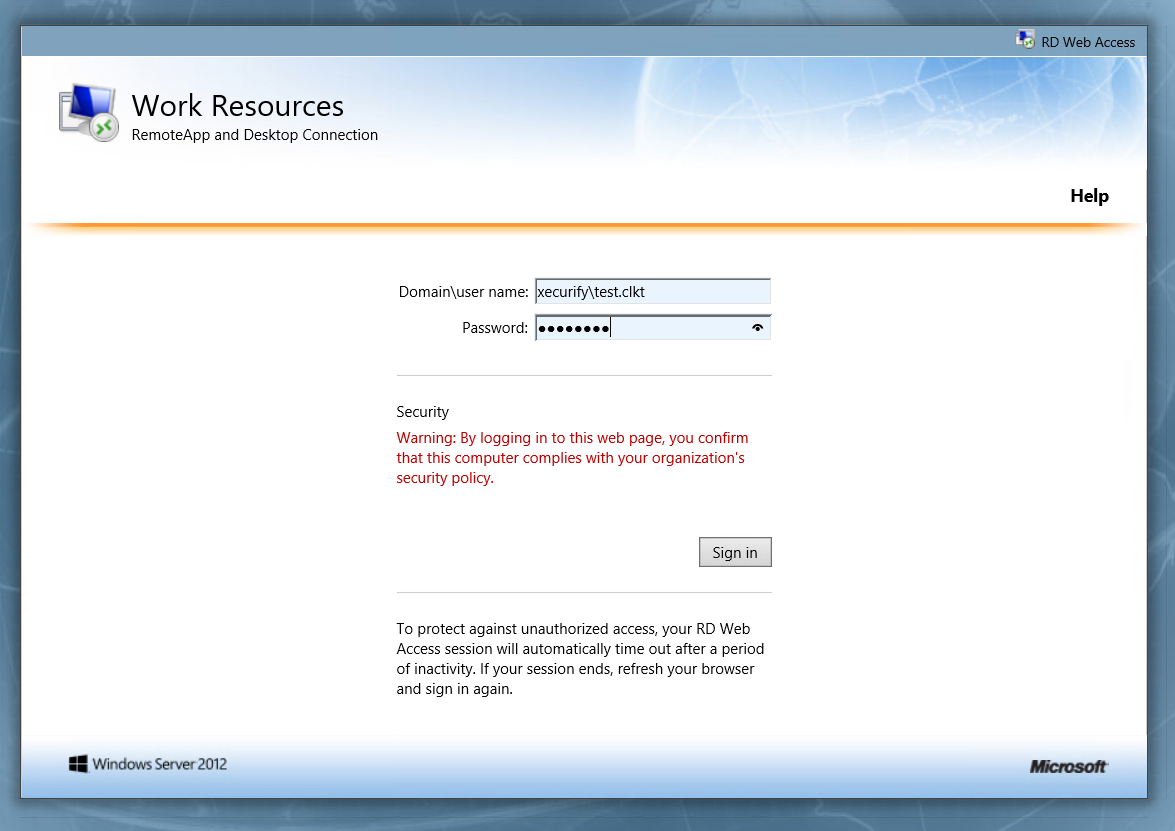
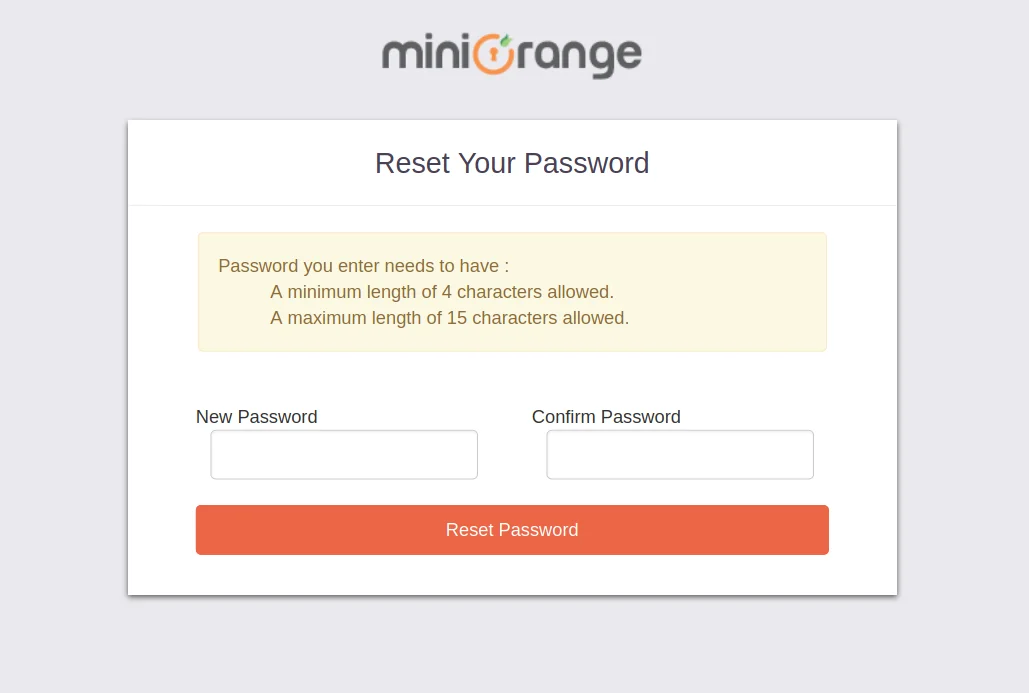
- To test your setup, log into Remote Desktop Web Access with your username and password.
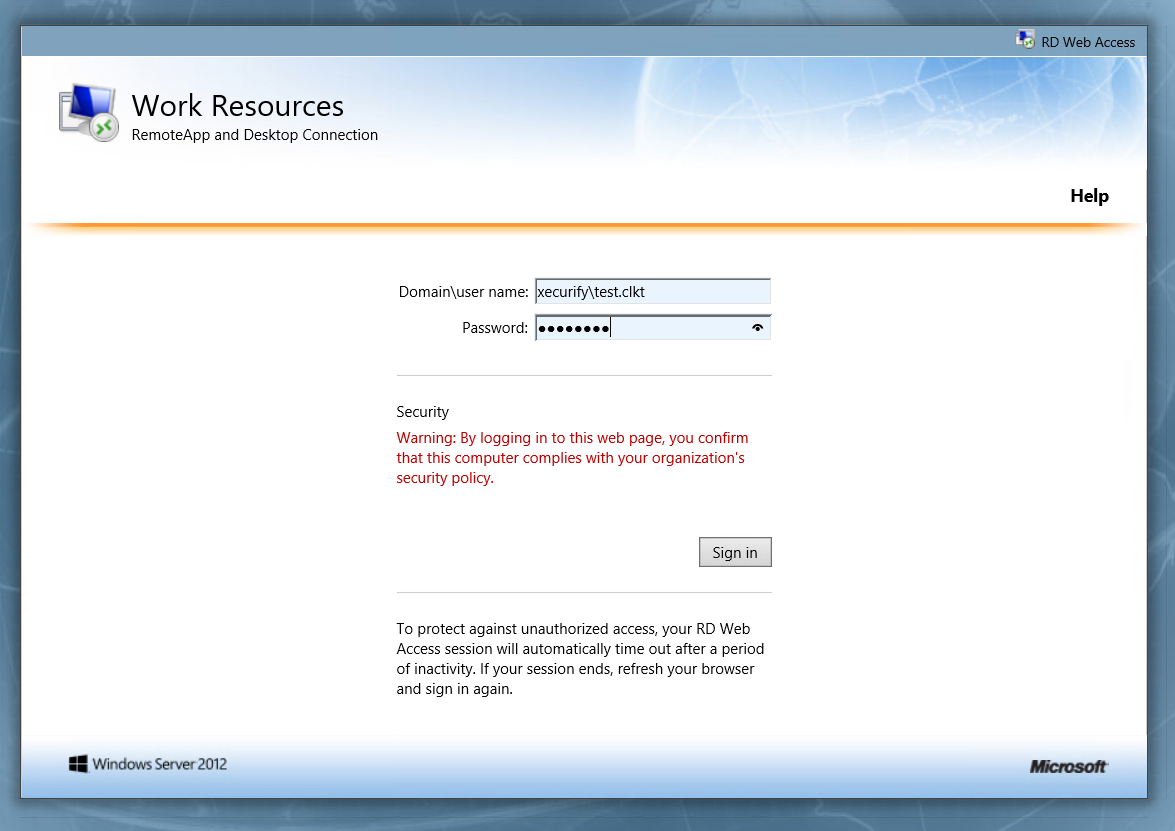
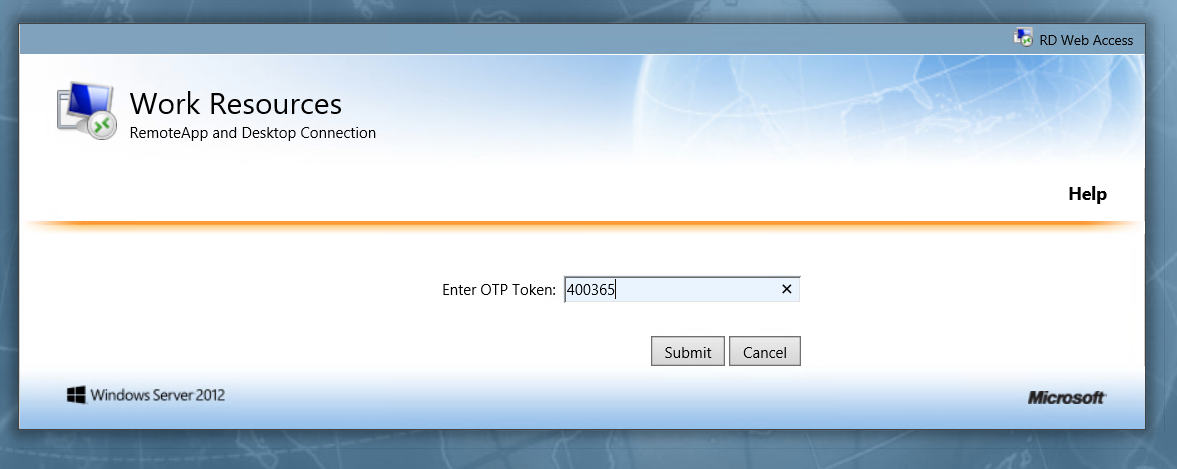
- Enter the second factor (in this case OTP token). Then click on Submit.
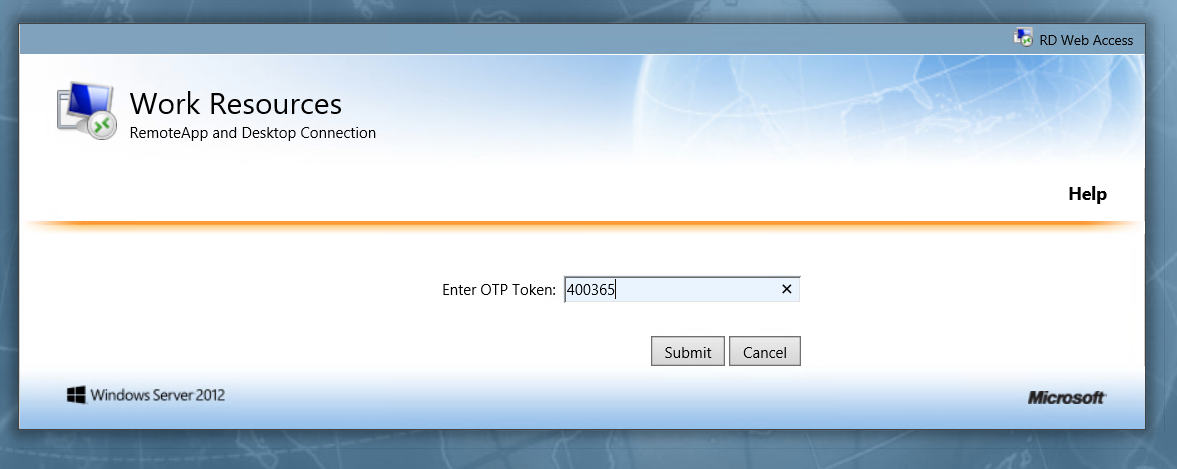
- You will be successfully logged-in to your Remote Desktop Web Access.
5. Configure Your User Directory (Optional)
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
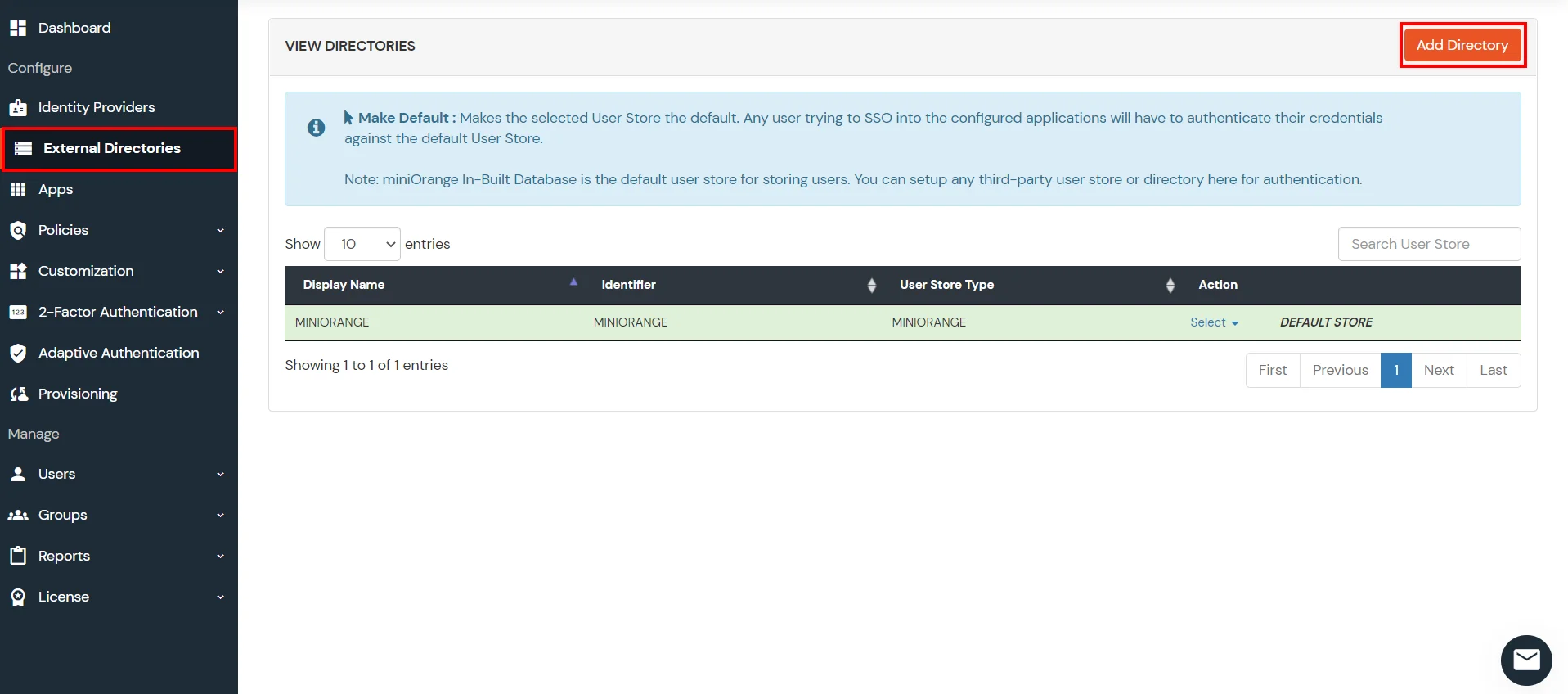
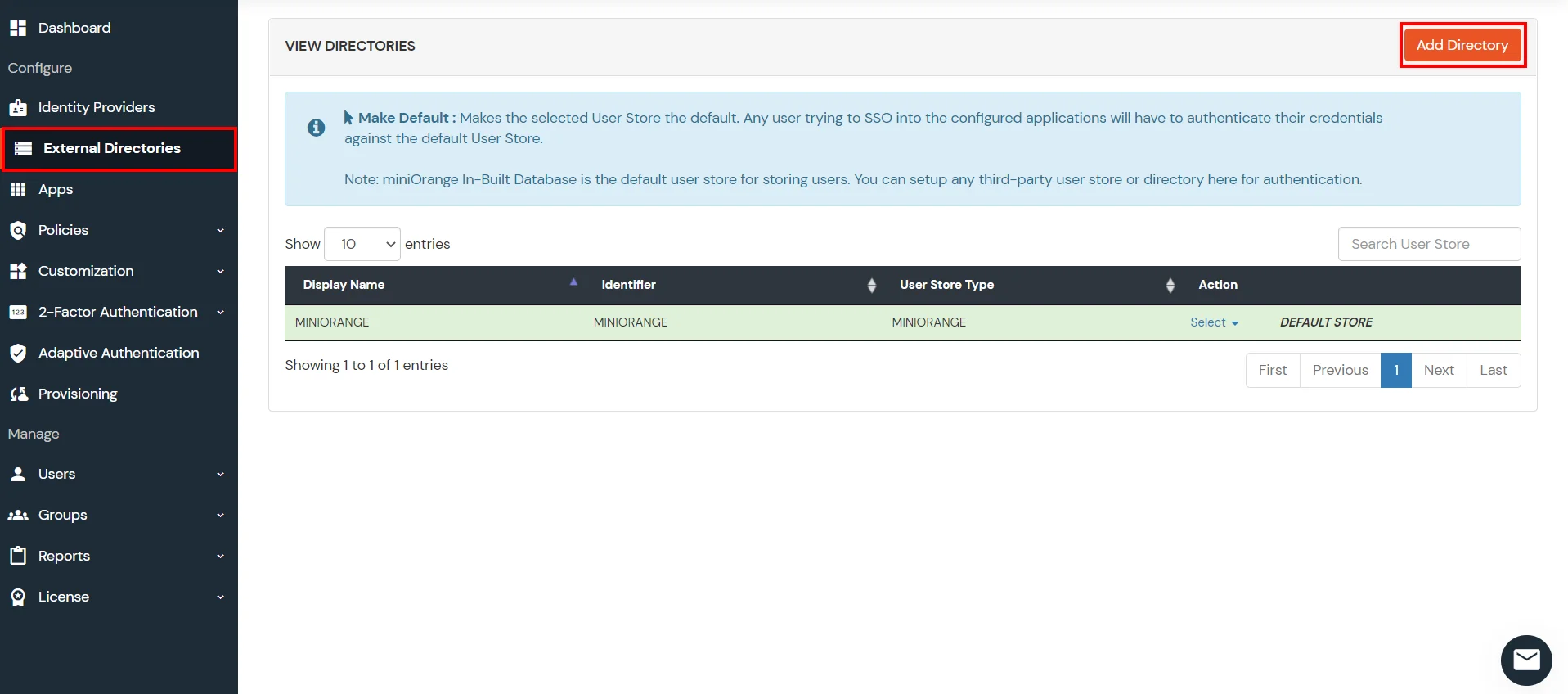
- Click on External Directories >> Add Directory in the left menu of the dashboard.
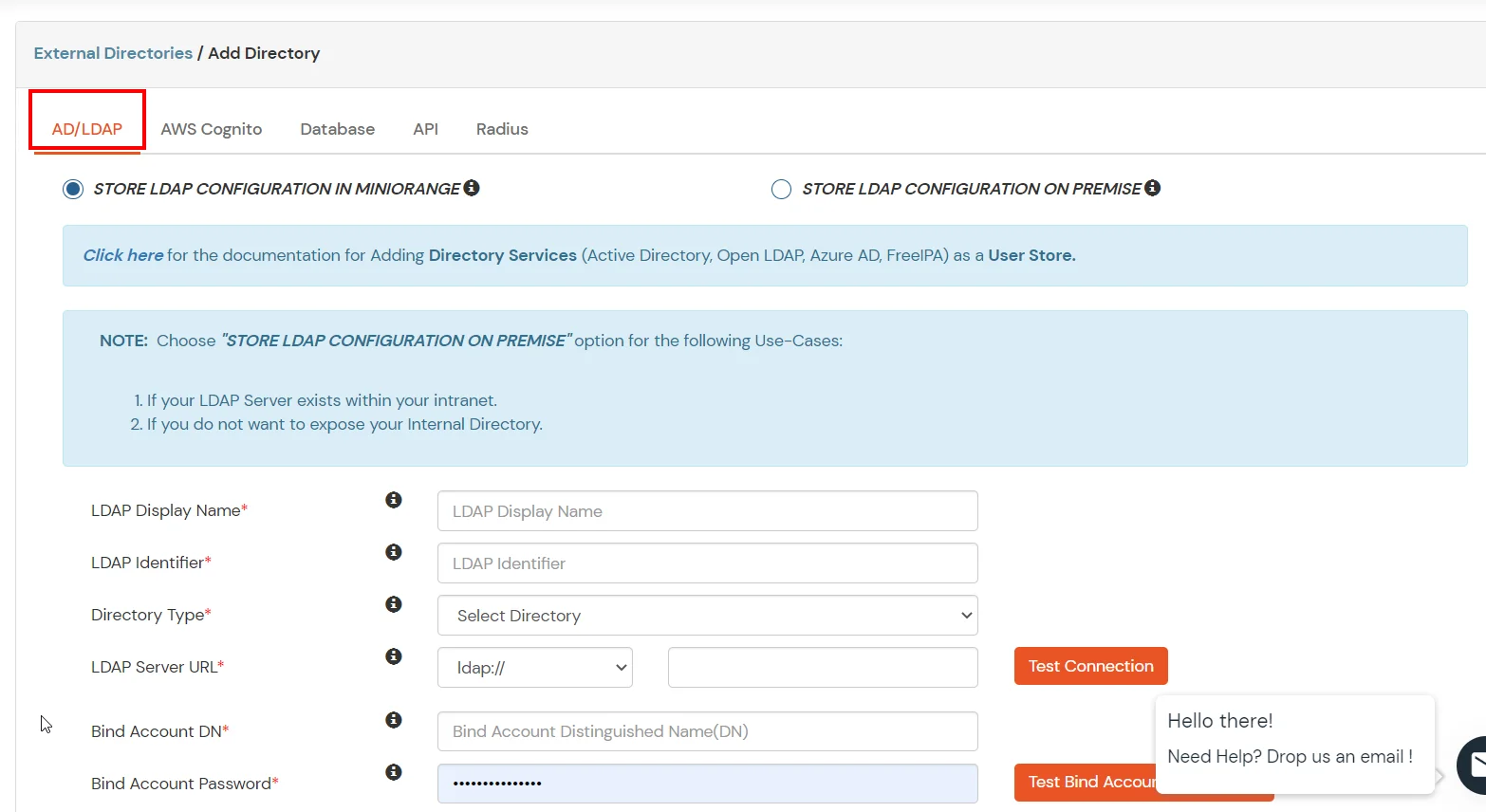
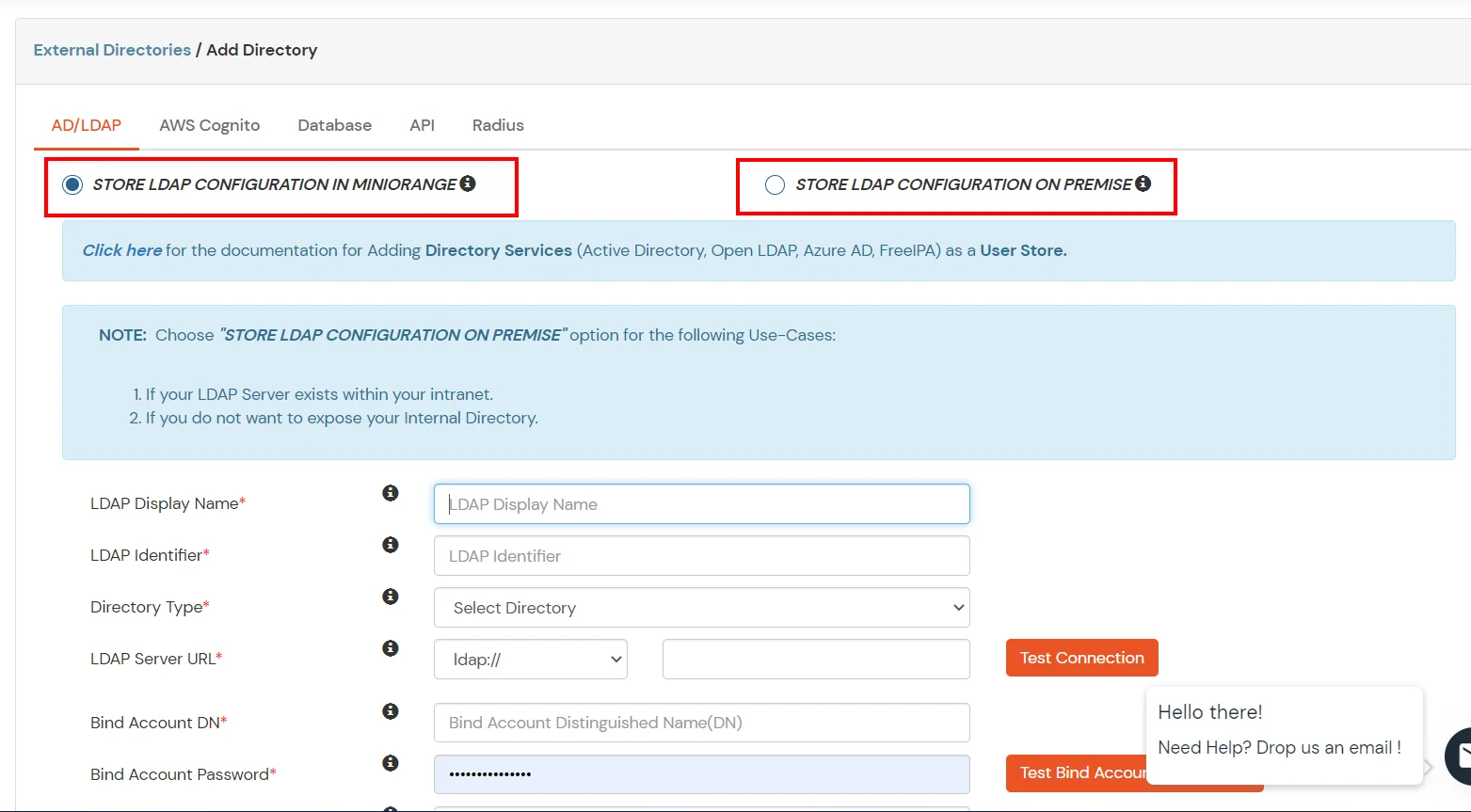
- Select Directory type as AD/LDAP.
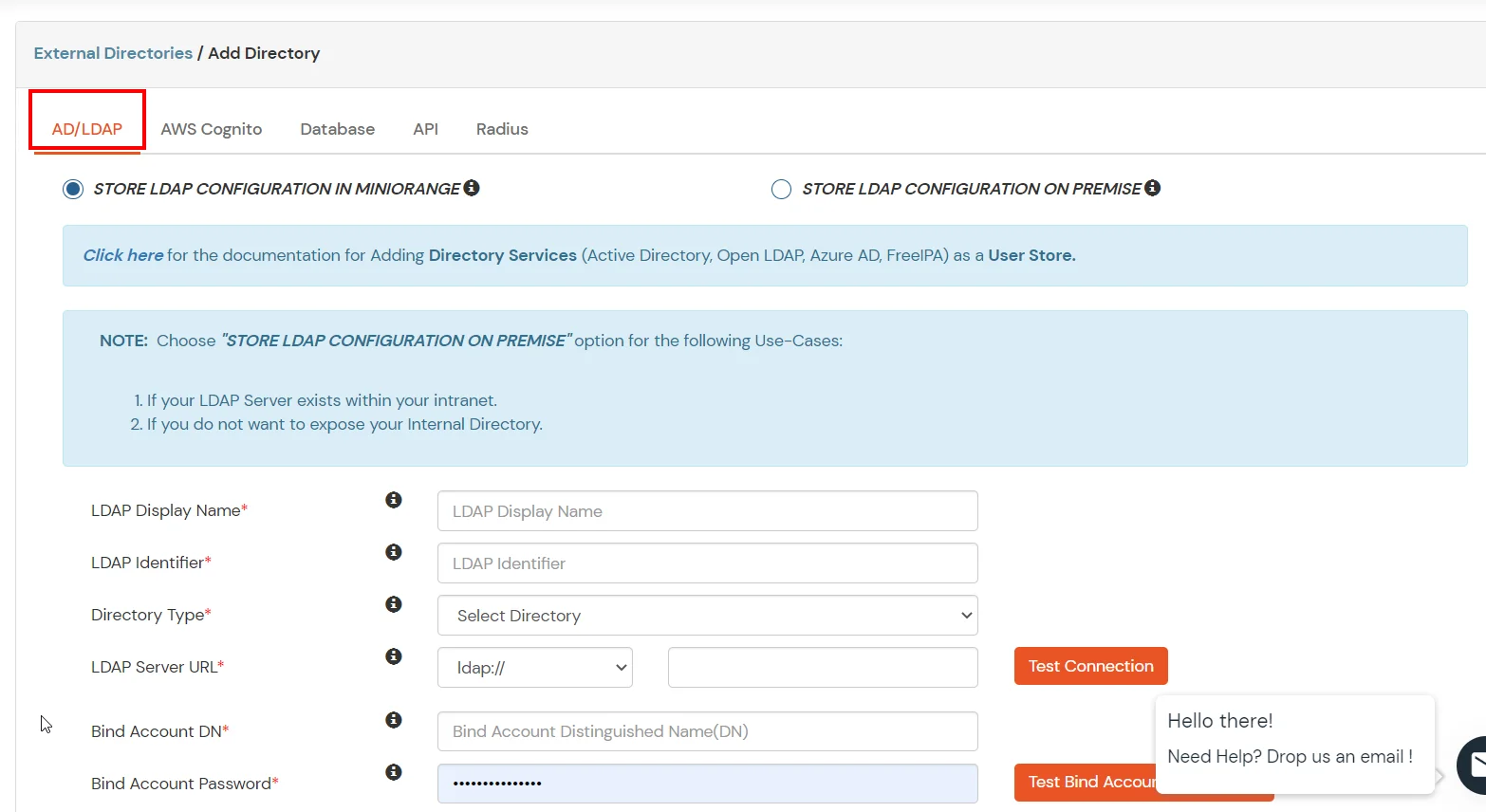
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway in your premise.
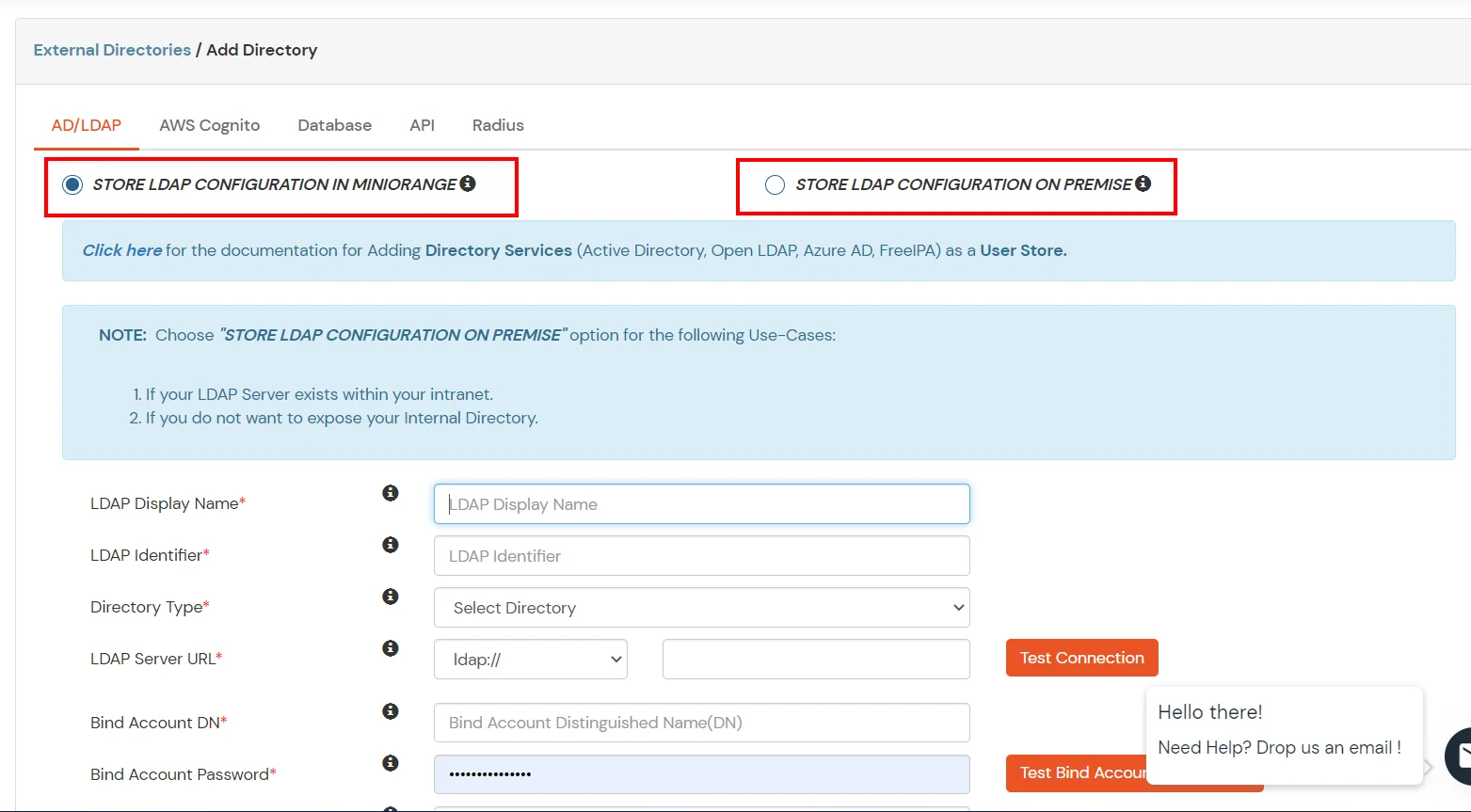
- Enter LDAP Display Name and LDAP Identifier name.
- Select Directory Type as Active Directory.
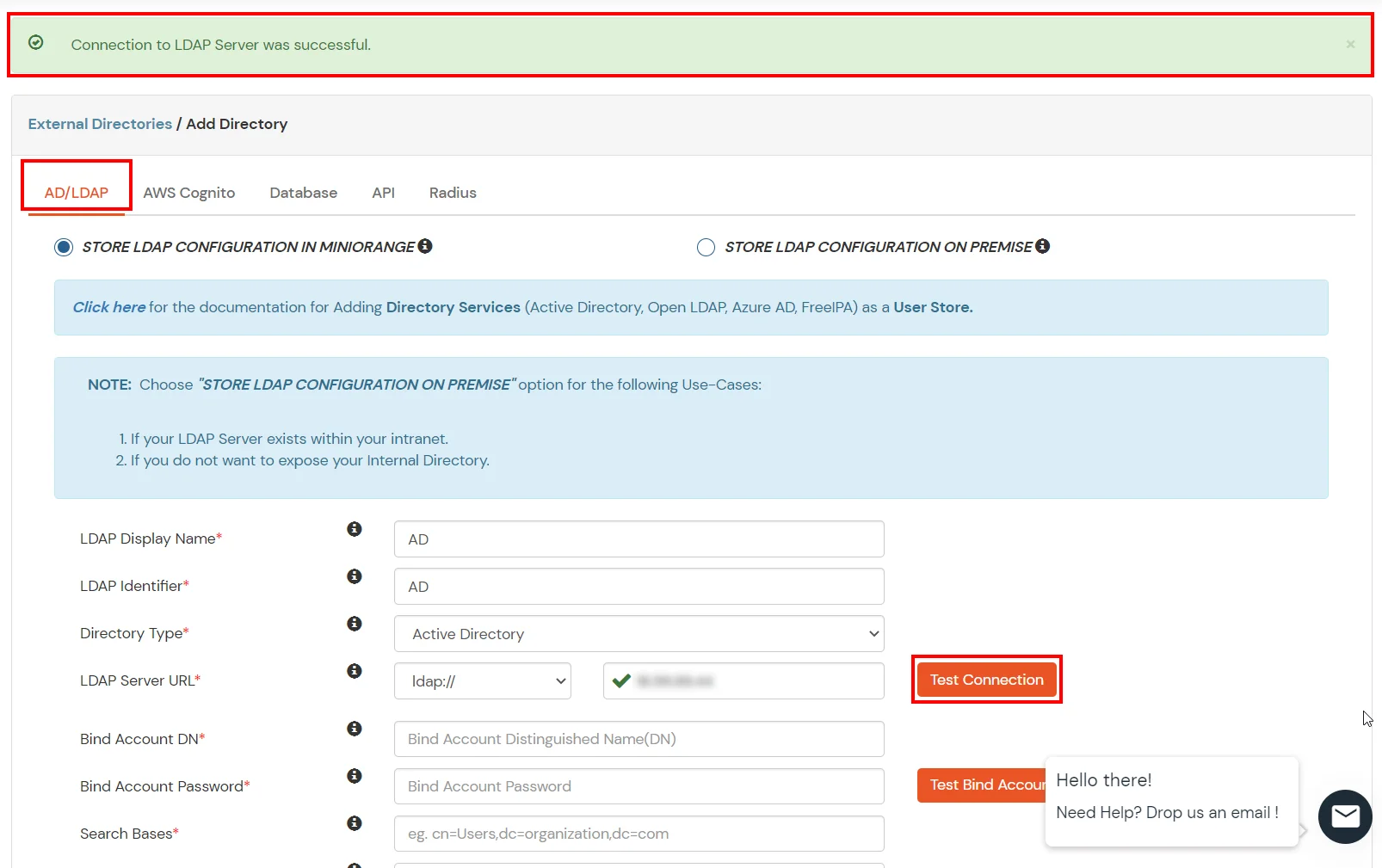
- Enter the LDAP Server URL or IP Address against LDAP Server URL field.
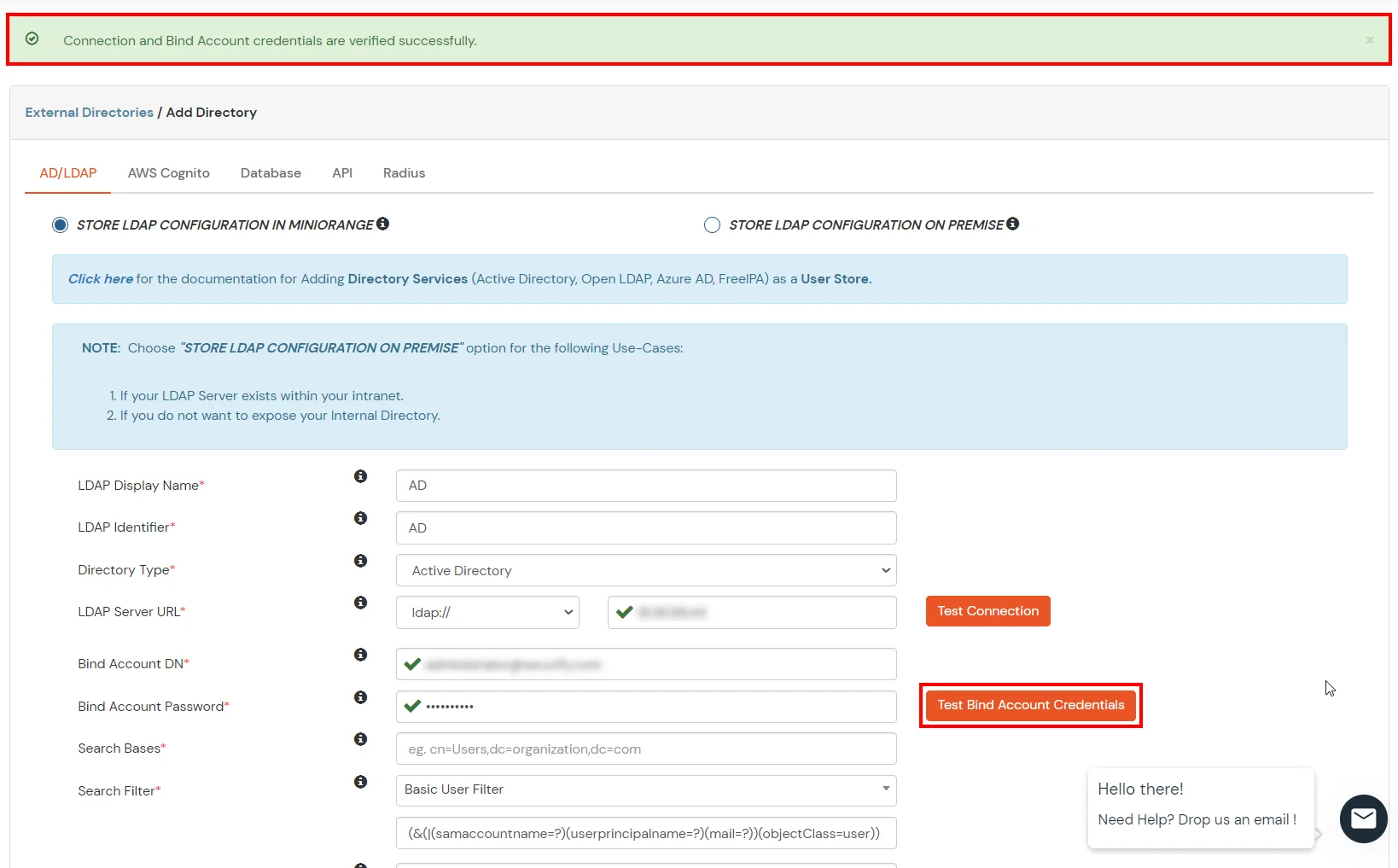
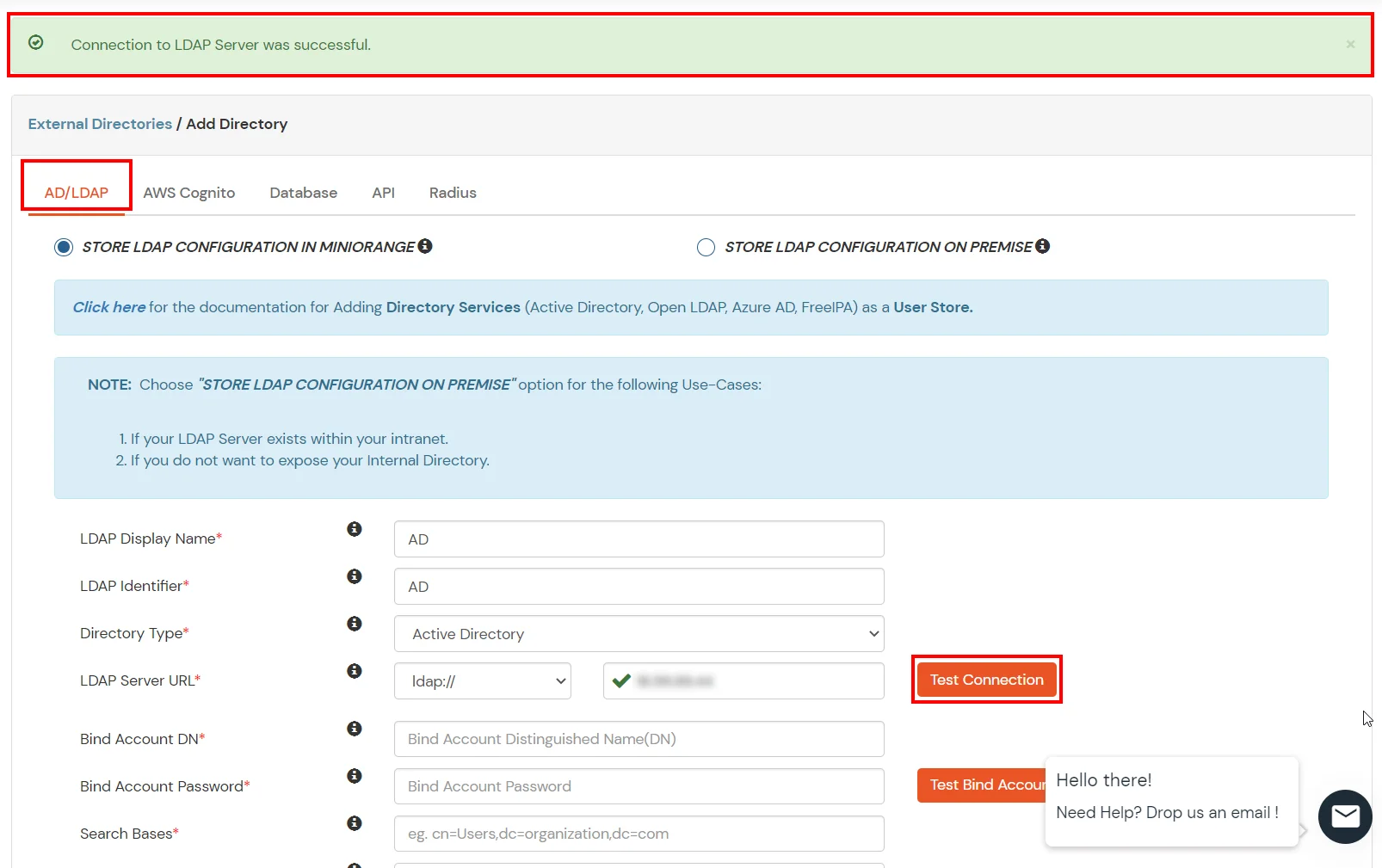
- Click on Test Connection button to verify if you have made a successful connection with your LDAP server.
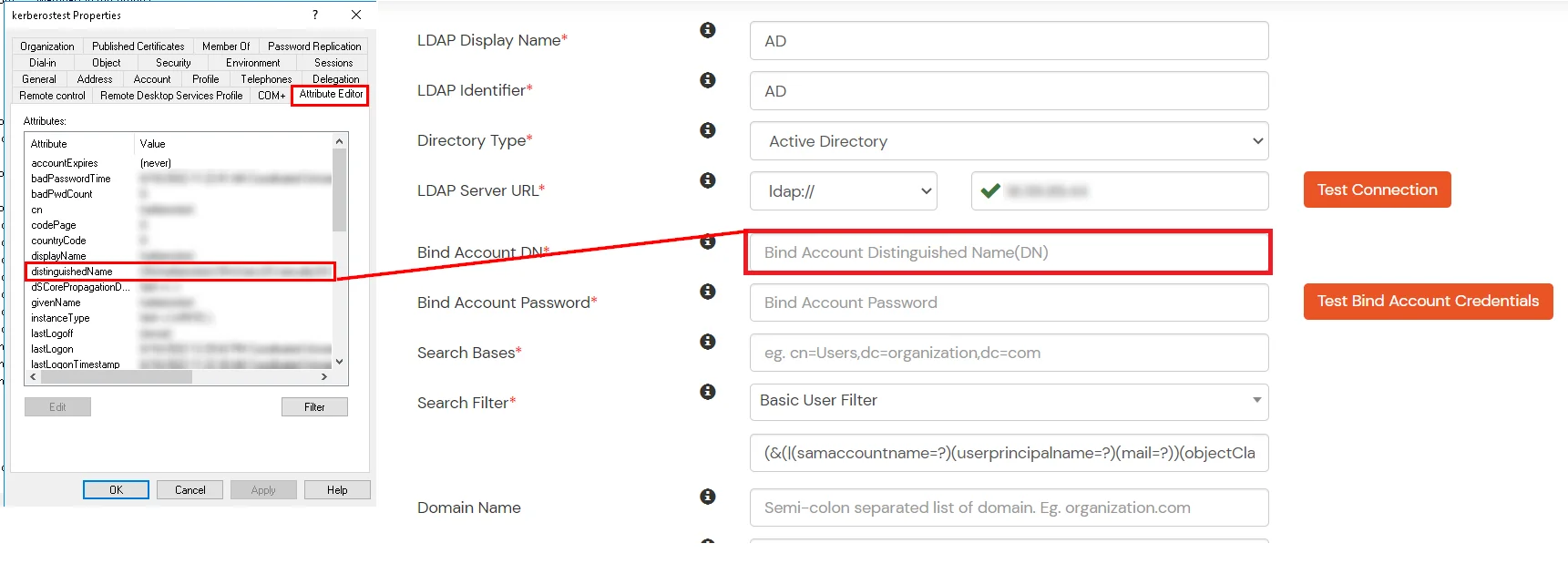
- In Active Directory, go to the properties of user containers/OU's and search for Distinguished Name attribute.
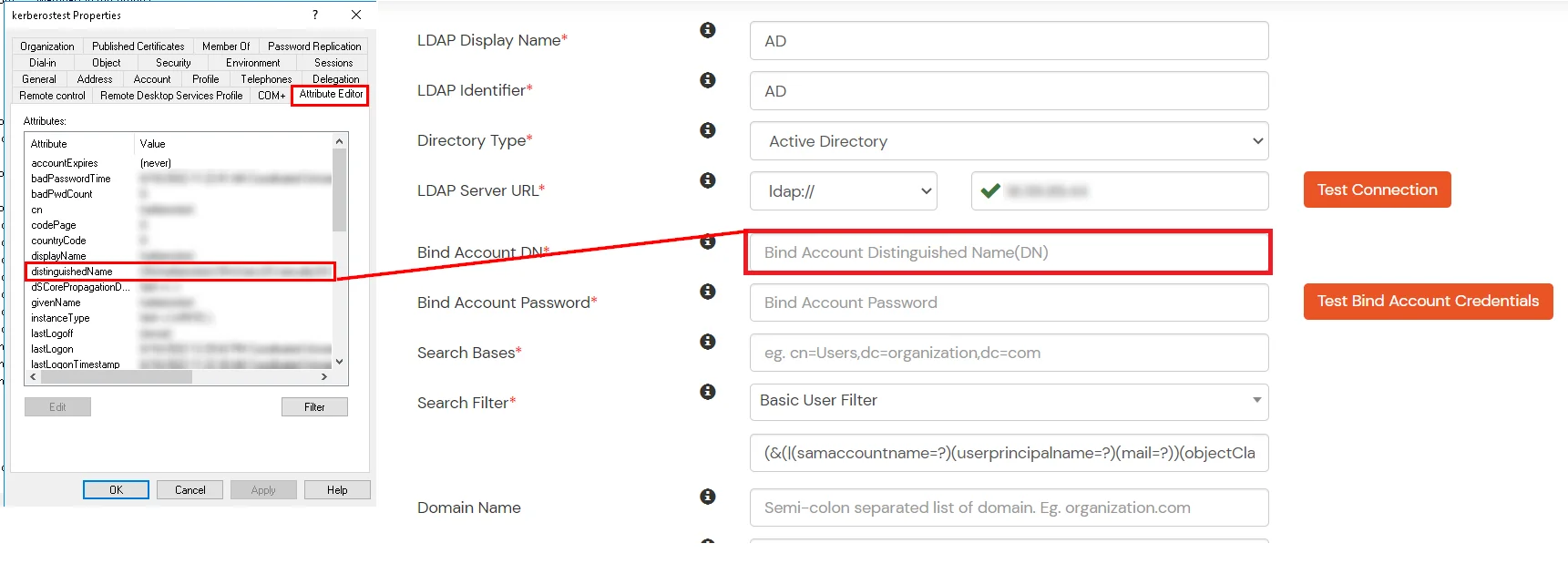
- Enter the valid Bind account Password.
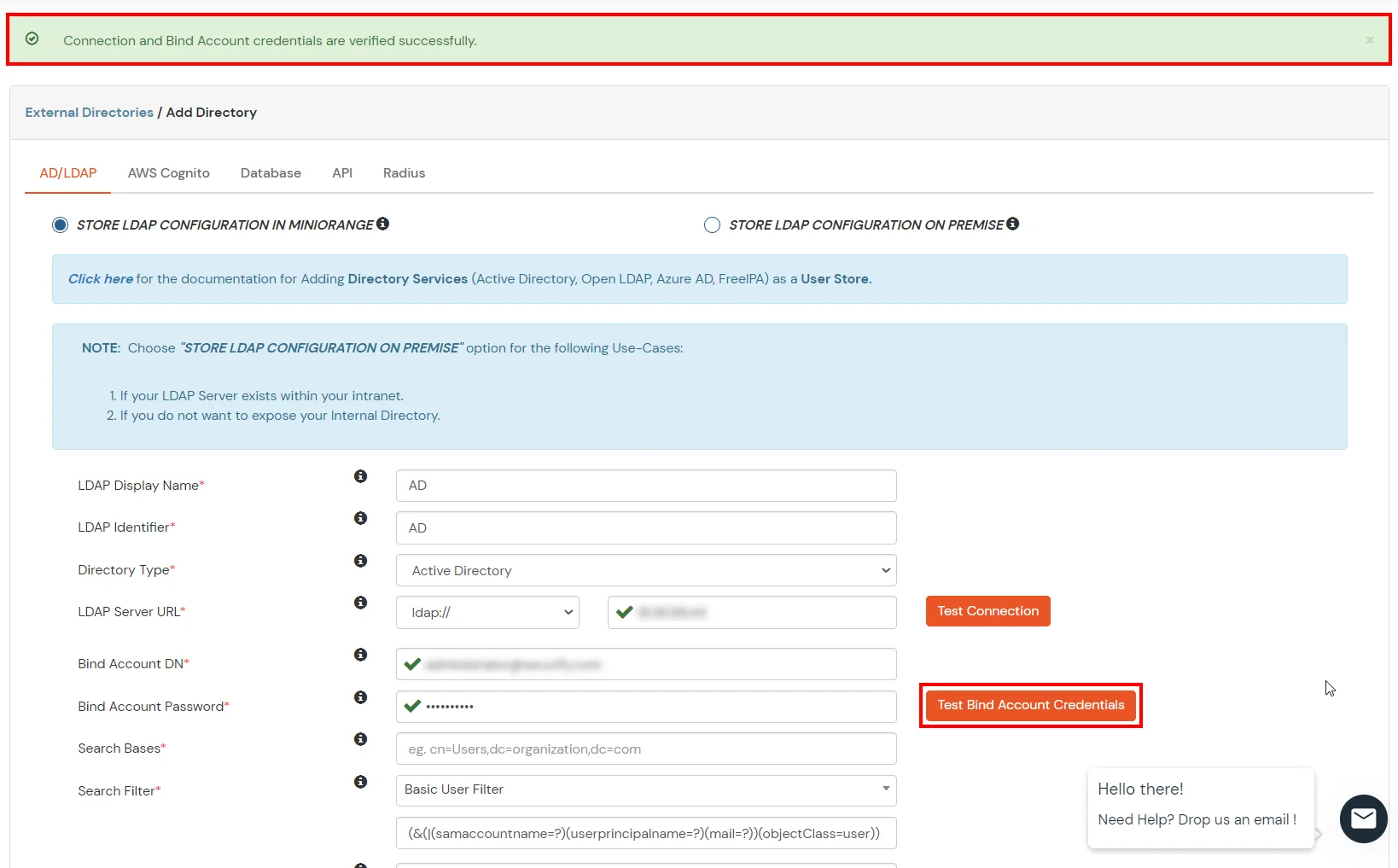
- Click on Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
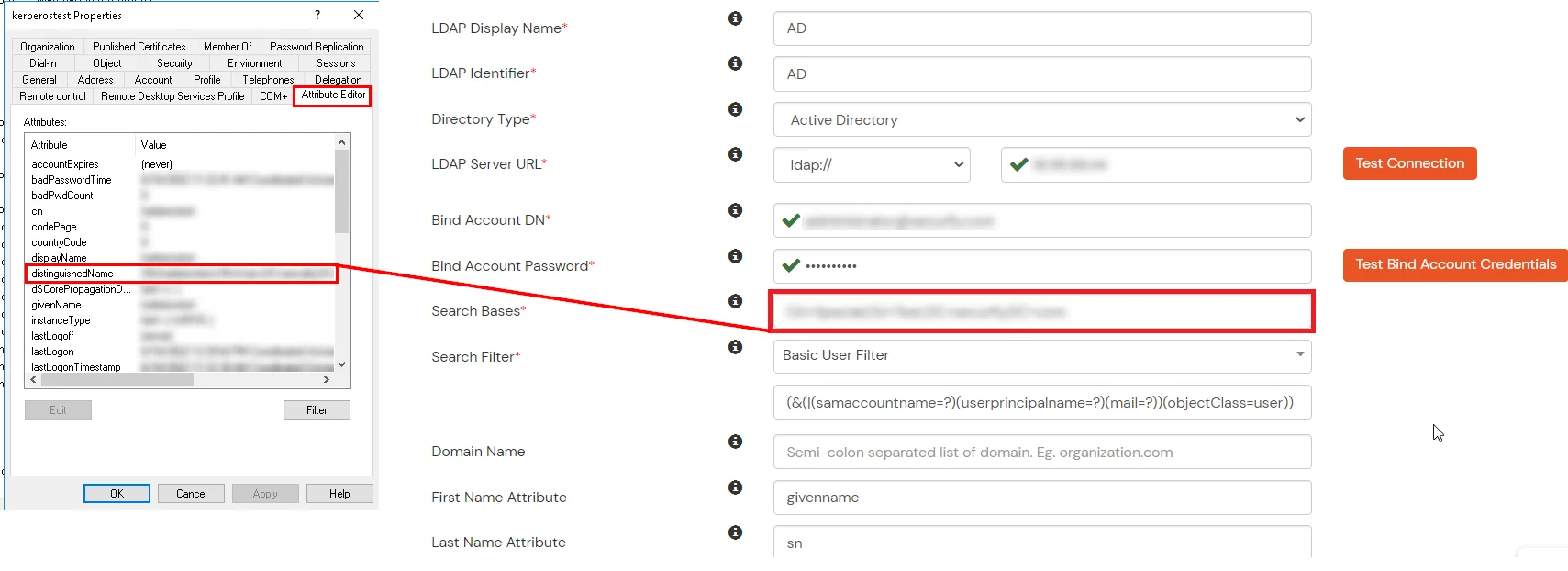
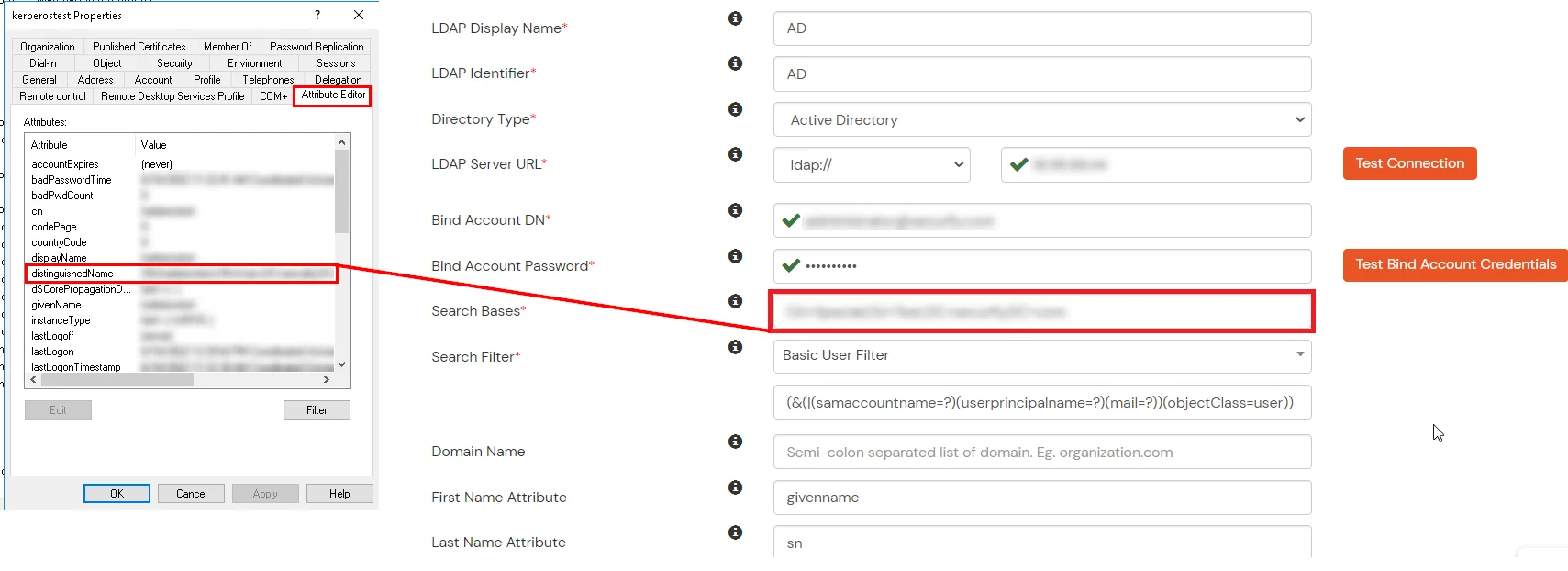
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
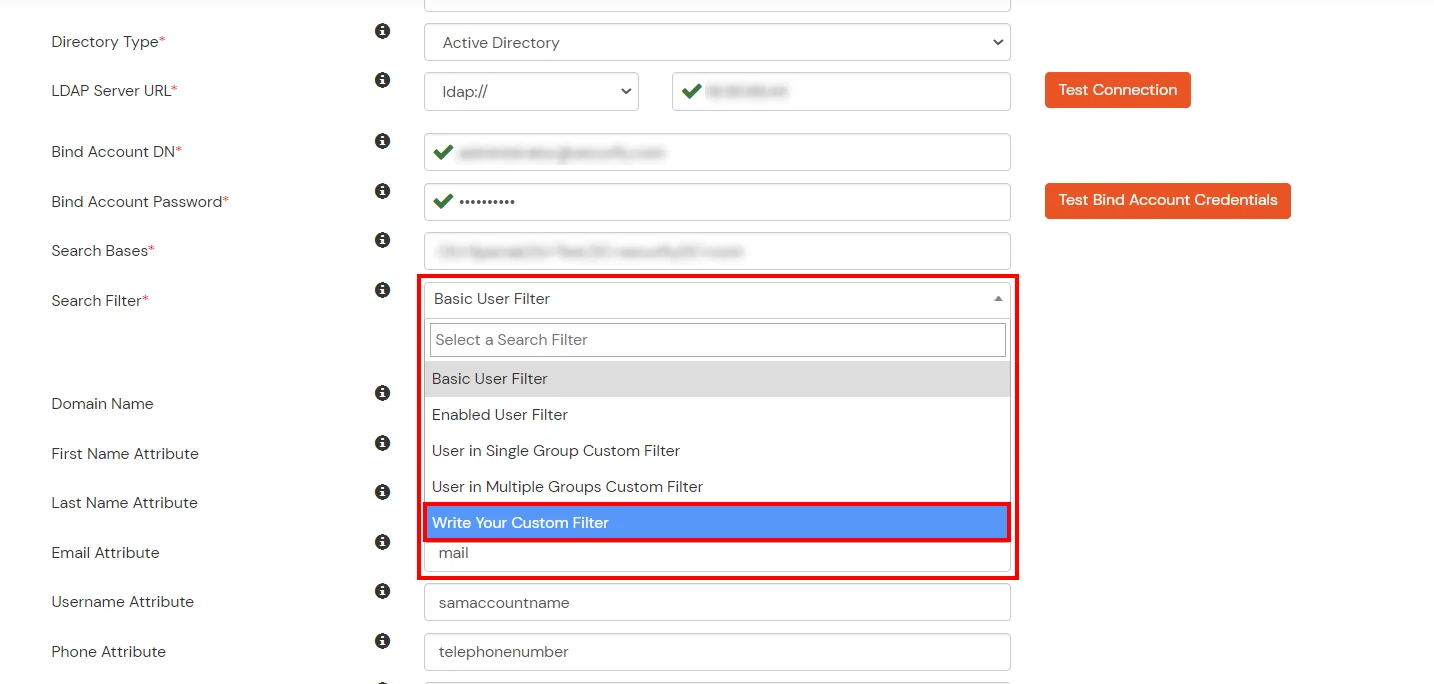
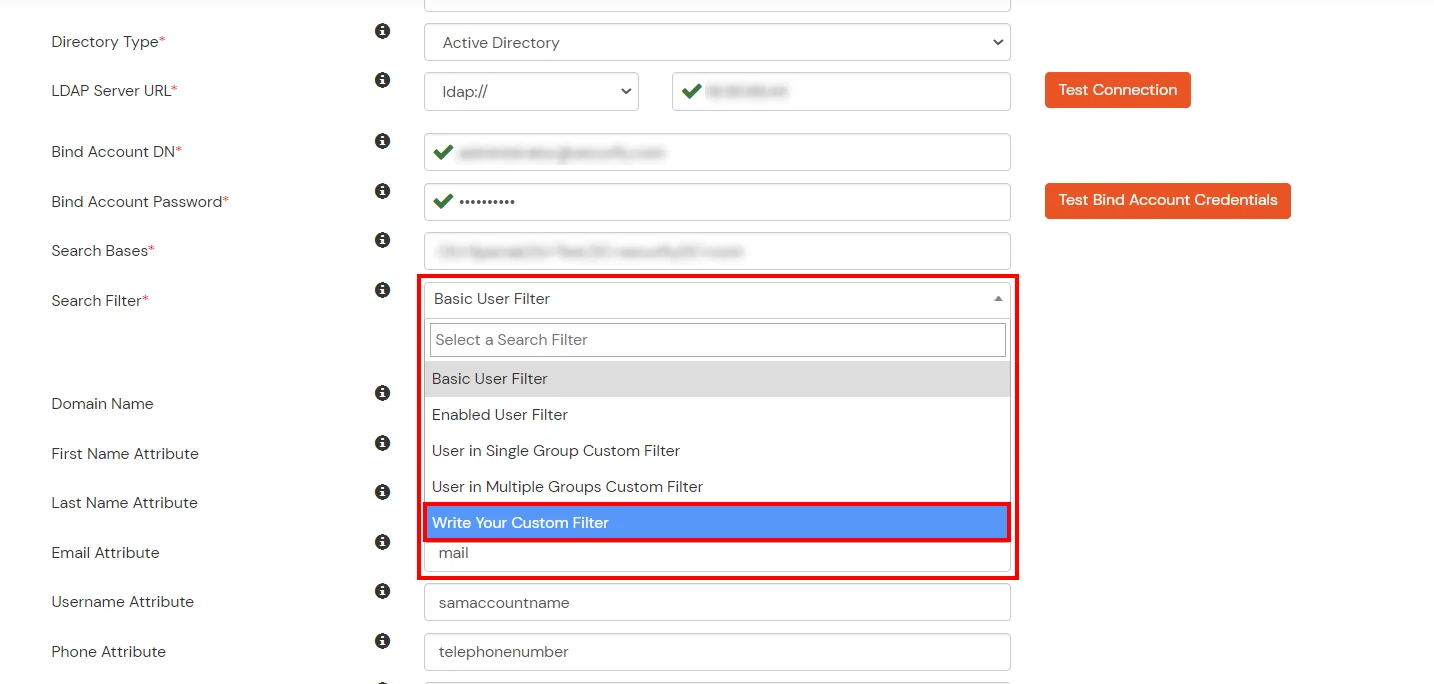
- Select a suitable Search filter from the drop-down menu. If you use User in Single Group Filter or User in Multiple Group Filter, replace the <group-dn> in the search filter with the distinguished name of the group in which your users are present. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
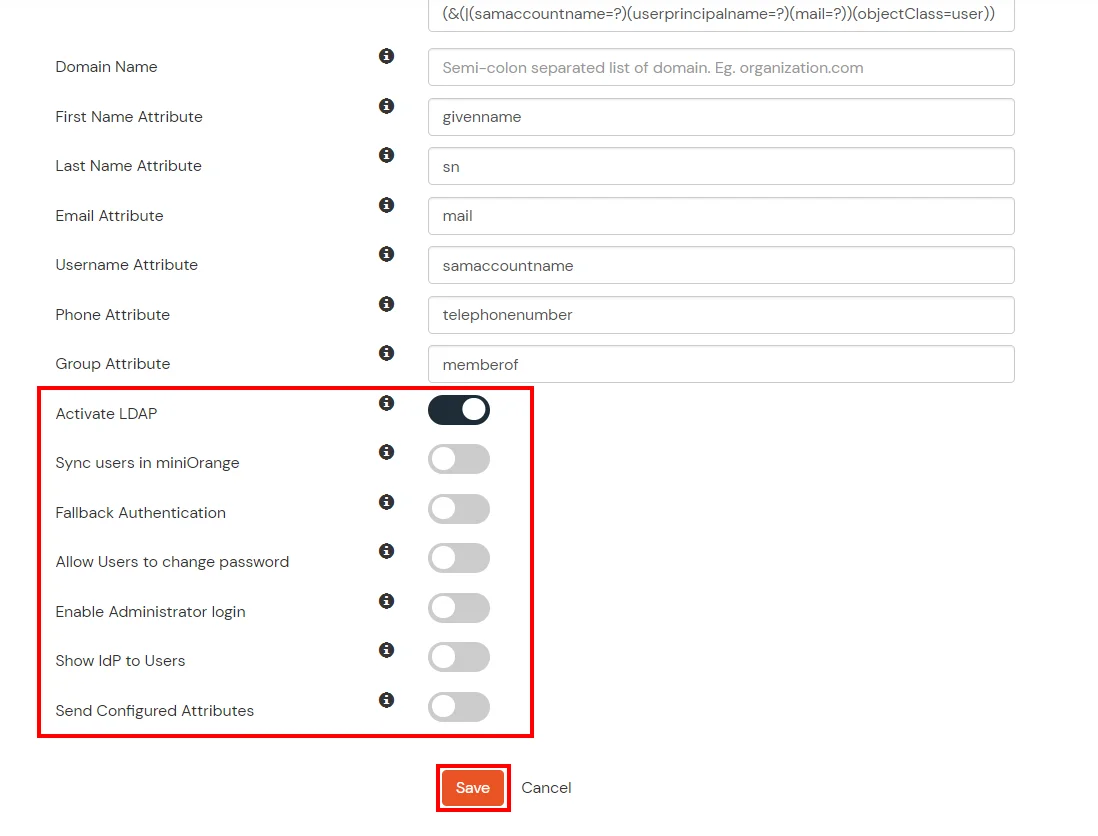
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Save button to add user store.
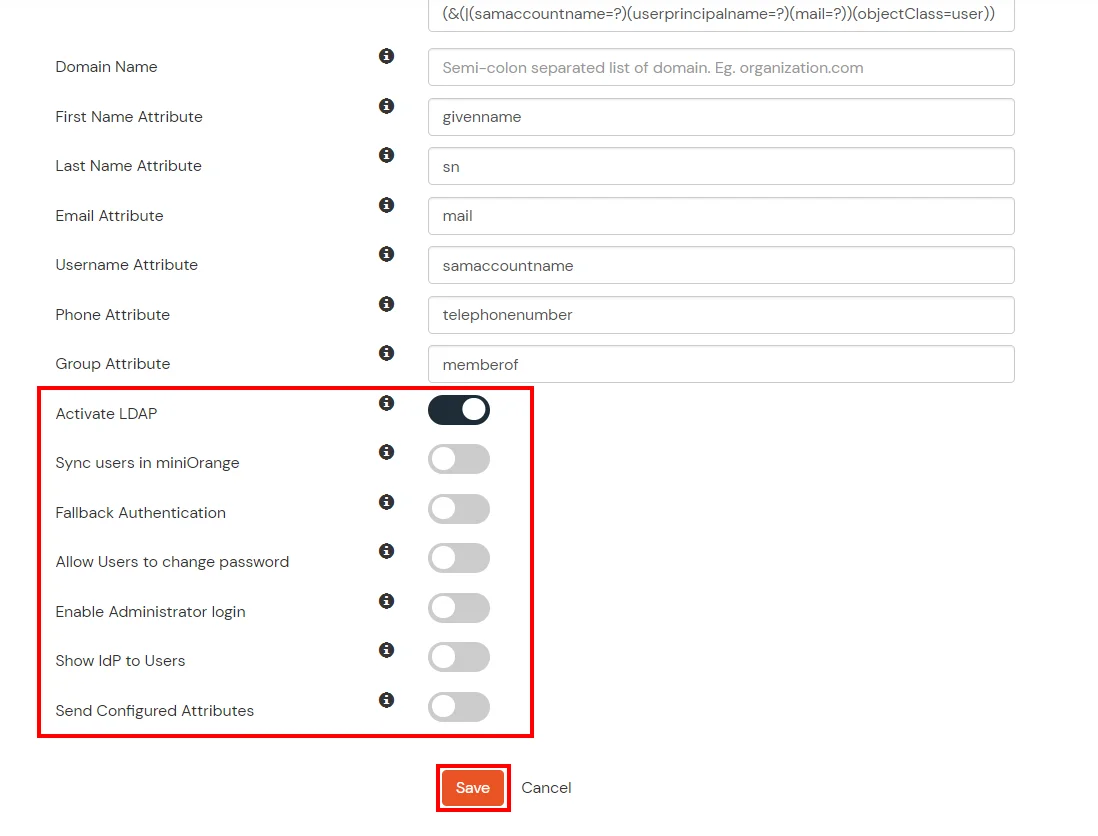
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Allow users to change password |
This allows your users to change their password. It updates the new credentials in your LDAP server |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Send Configured Attributes |
If you enable this option, then only the attributes configured below will be sent in attributes at the time of login |
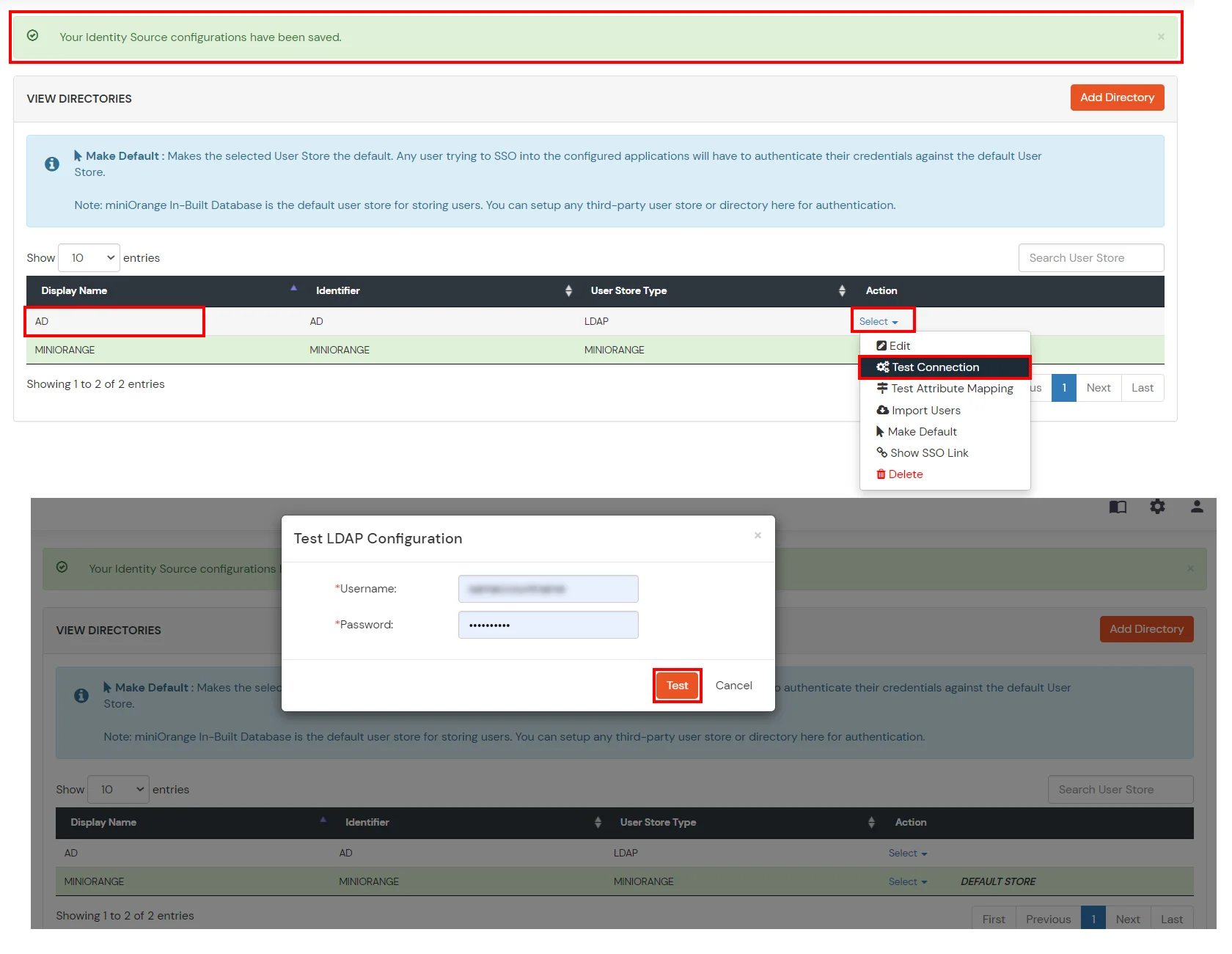
- Click on Save. After this, it will show you the list of User stores. Click on Test Connection to check whether you have enter valid details. For that, it will ask for username and password.
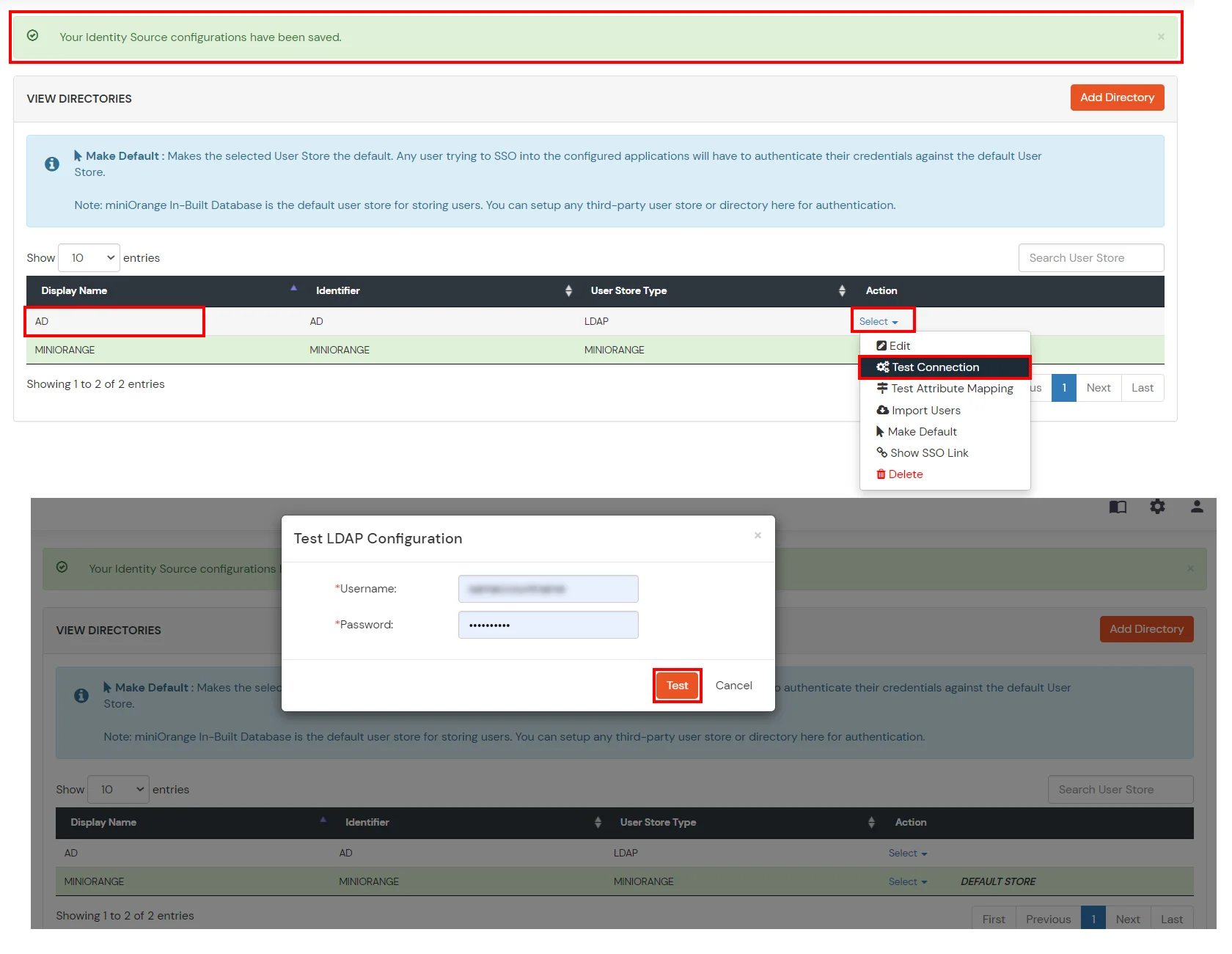
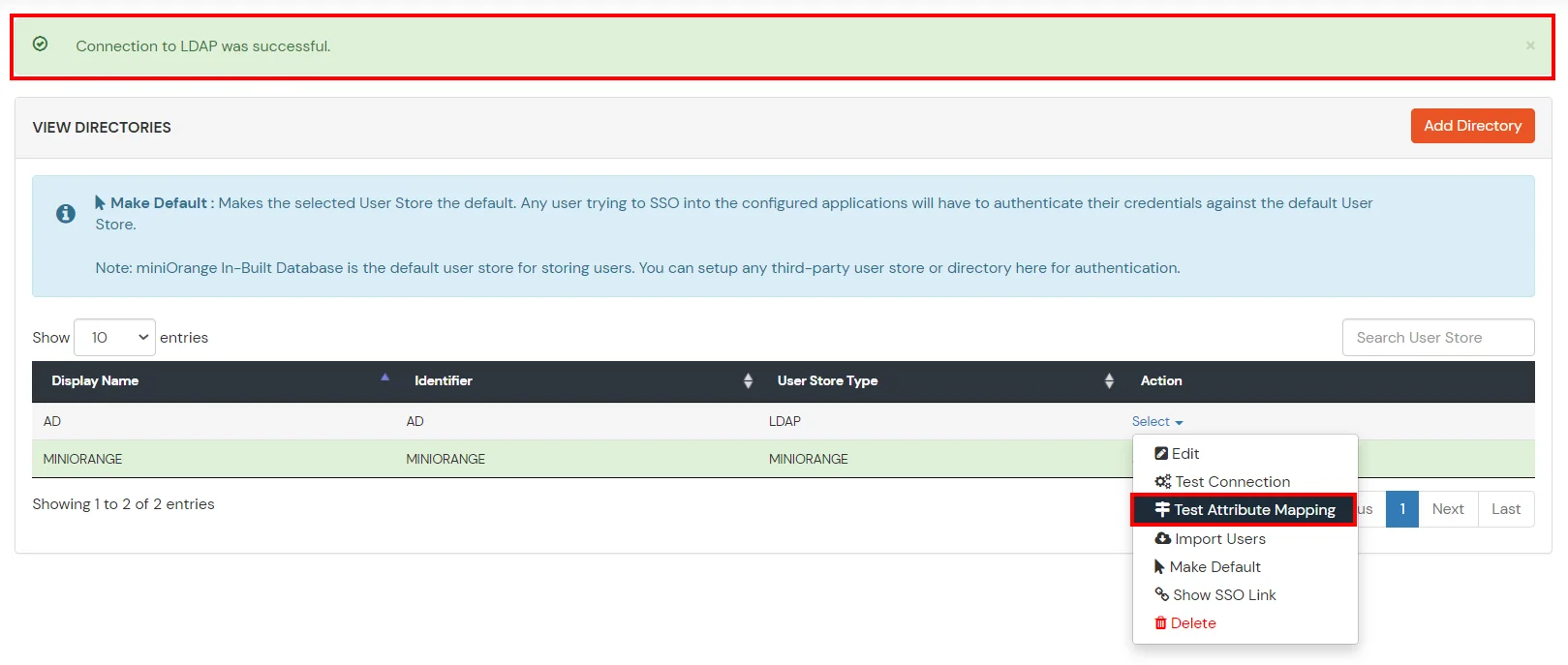
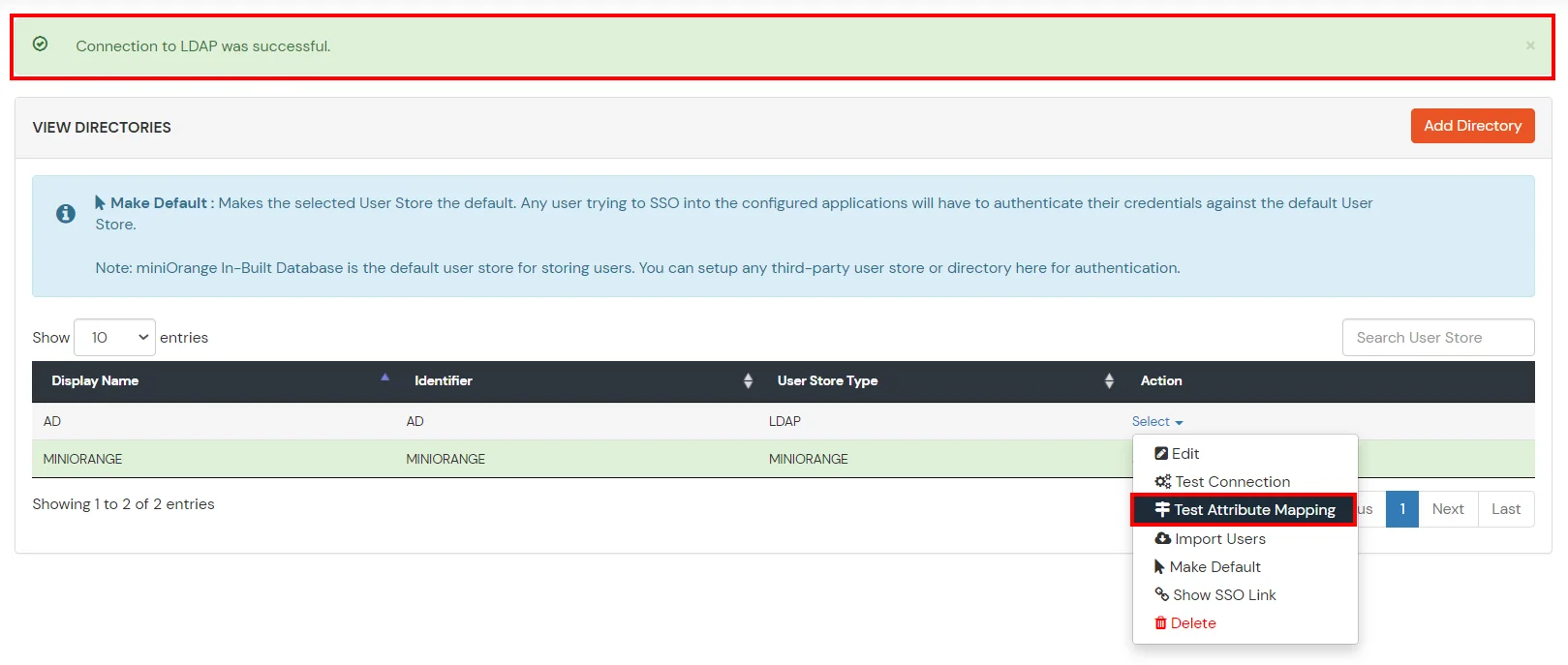
- On Successful connection with LDAP Server, a success message is shown.
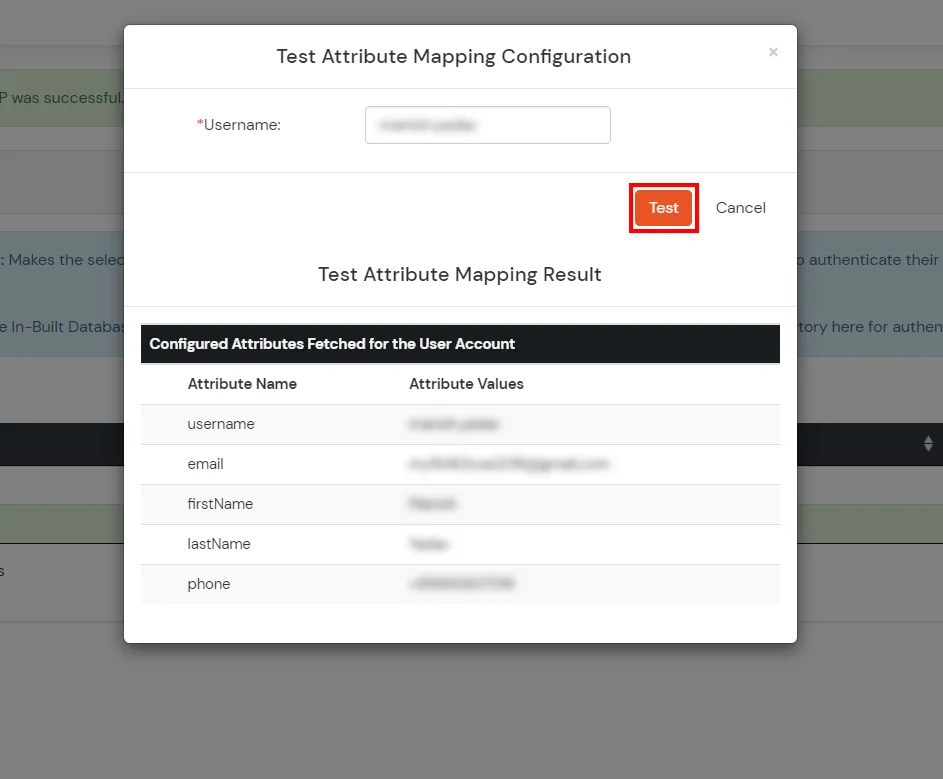
- Click on Test Attribute Mapping.
- Enter a valid Username. Then, click on Test. Mapped Attributes corresponding to the user are fetched.
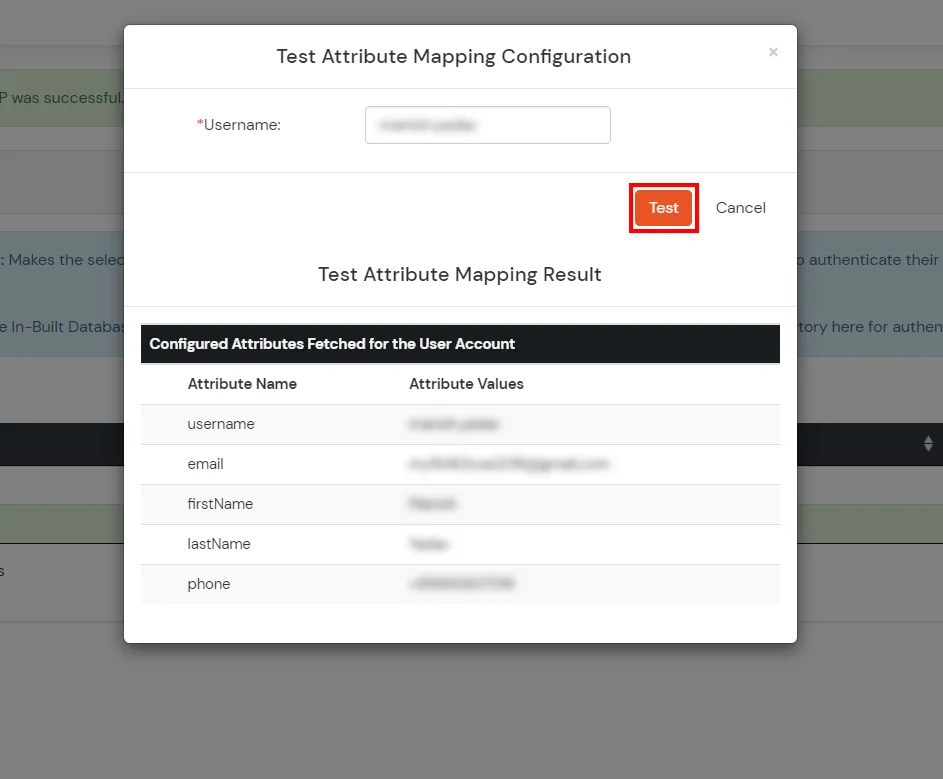
- After successful Attribute Mapping Configuration, go back to the ldap configuration and enable Activate LDAP in order to authenticate users from AD/LDAP.
Refer our guide to setup LDAPS on windows server.
User Import and Provisioning from AD
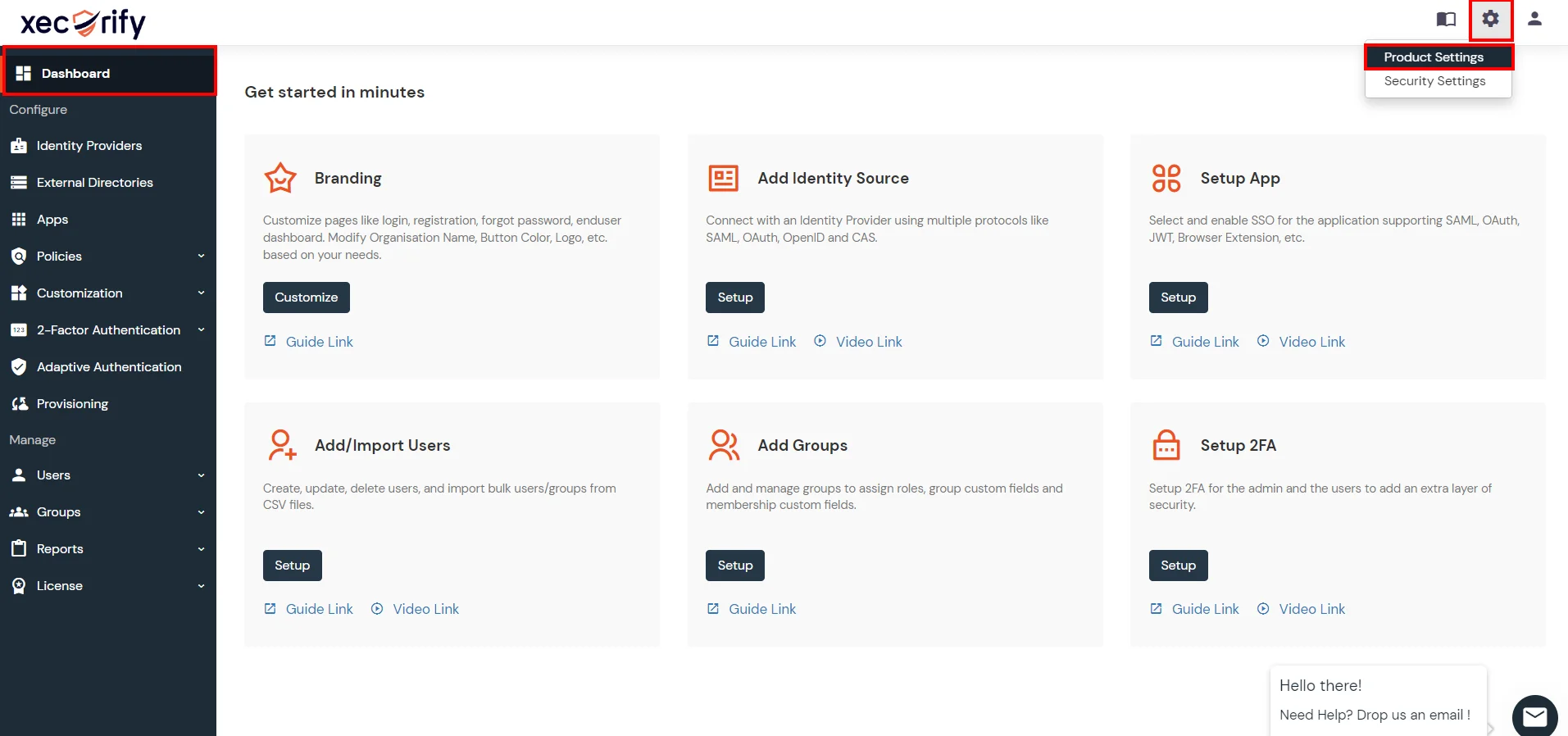
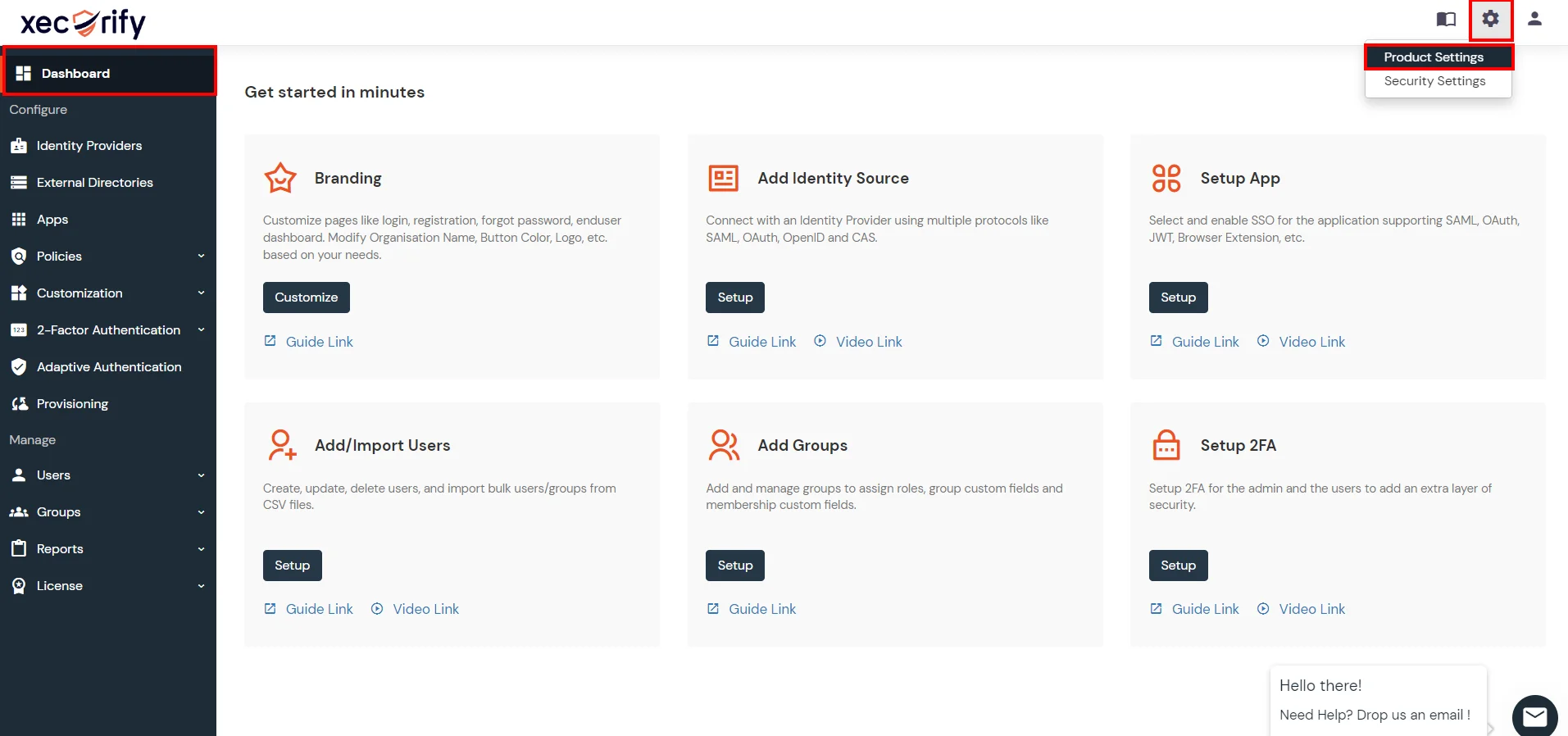
- Go to Settings >> Product Settings in the Customer Admin Account.
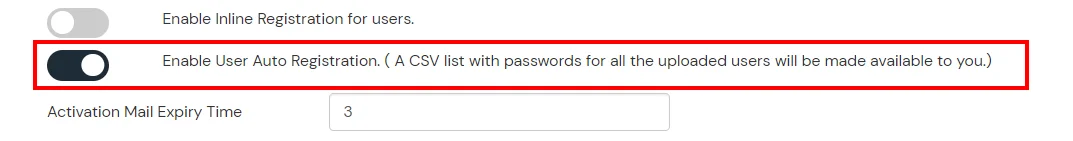
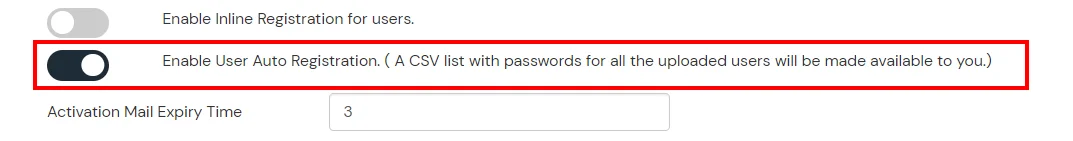
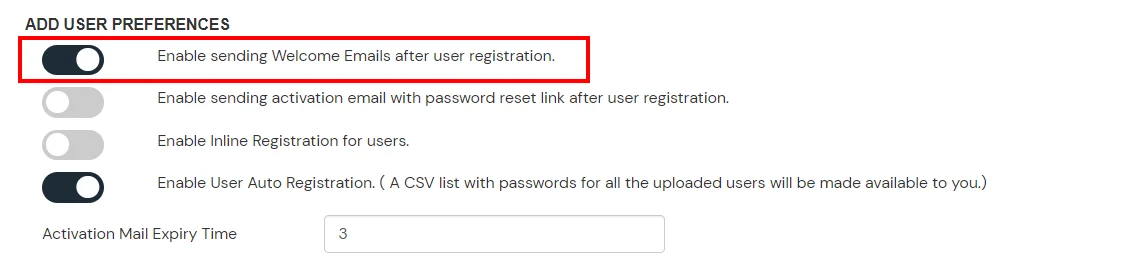
- Enable the "Enable User Auto Registration" option and click Save.
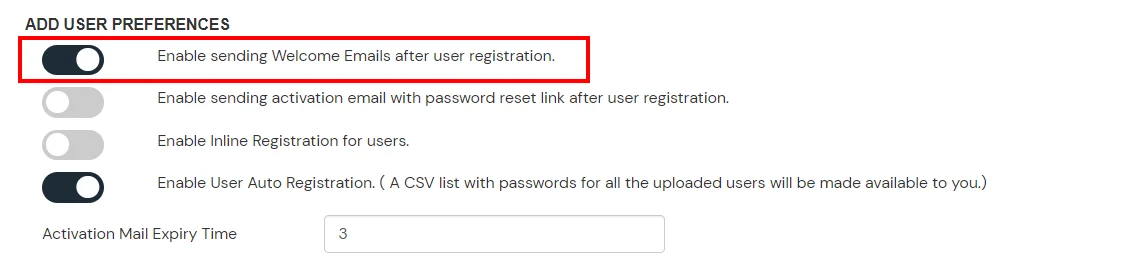
- (Optional) To send a welcome email to all the end users that will be imported, enable the "Enable sending Welcome Emails after user registration" option and click Save.
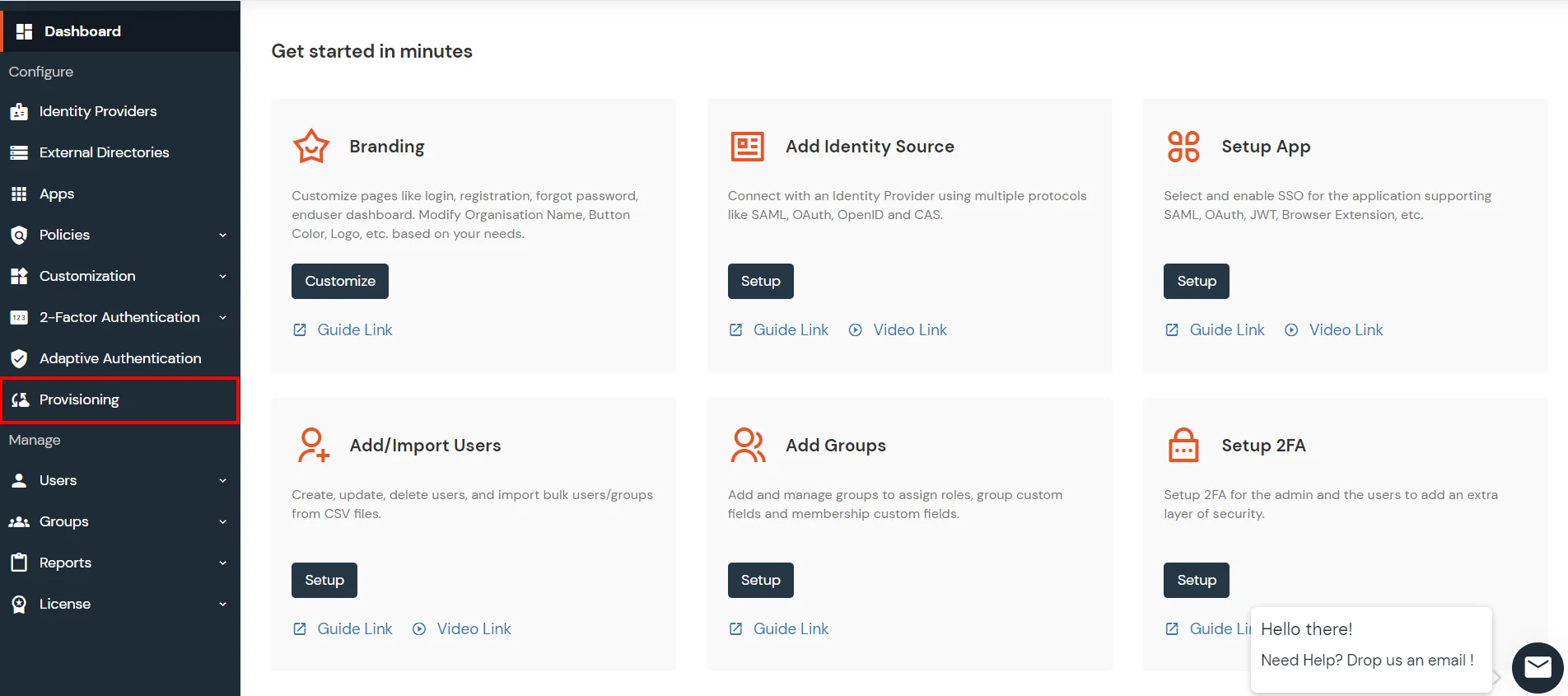
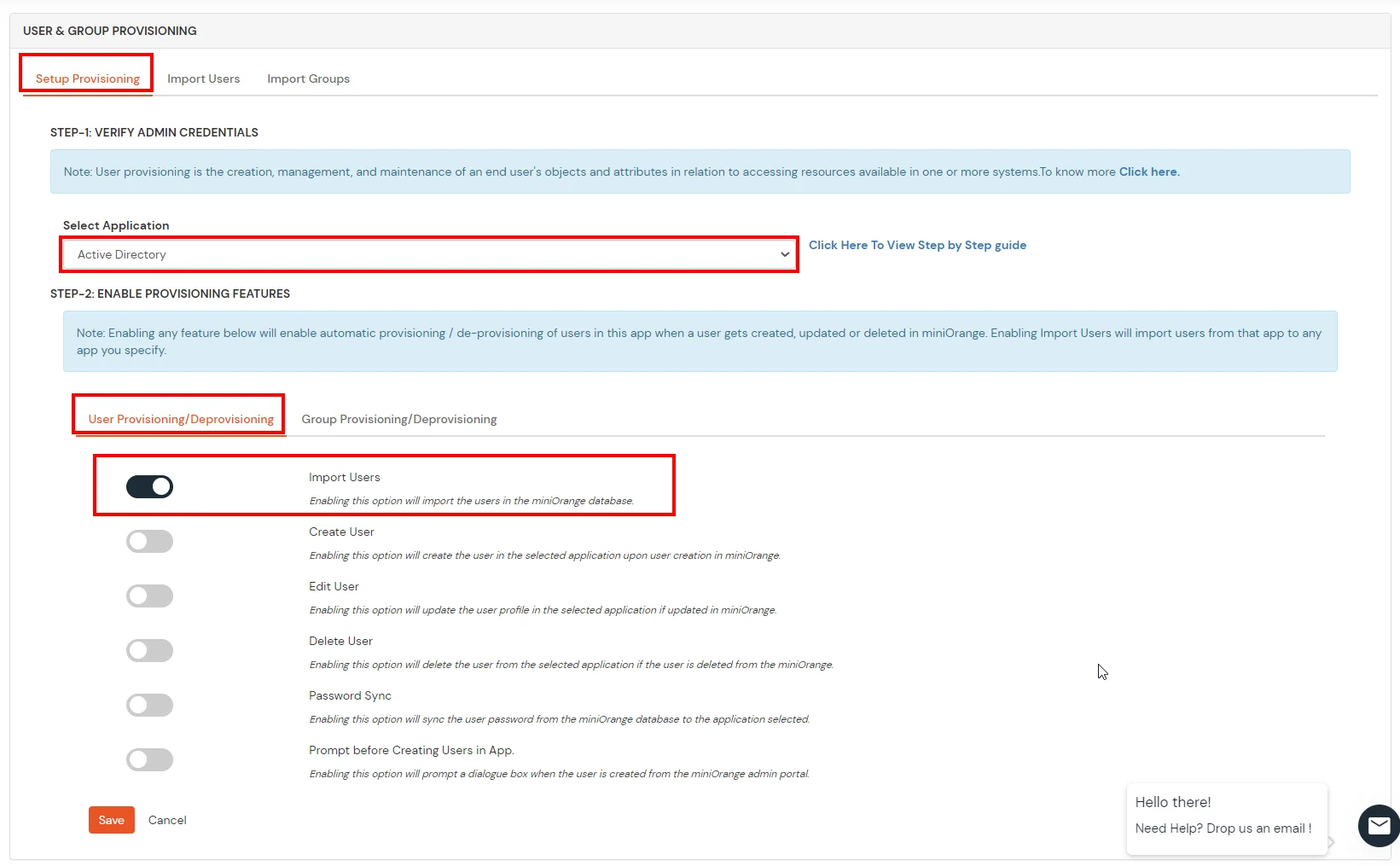
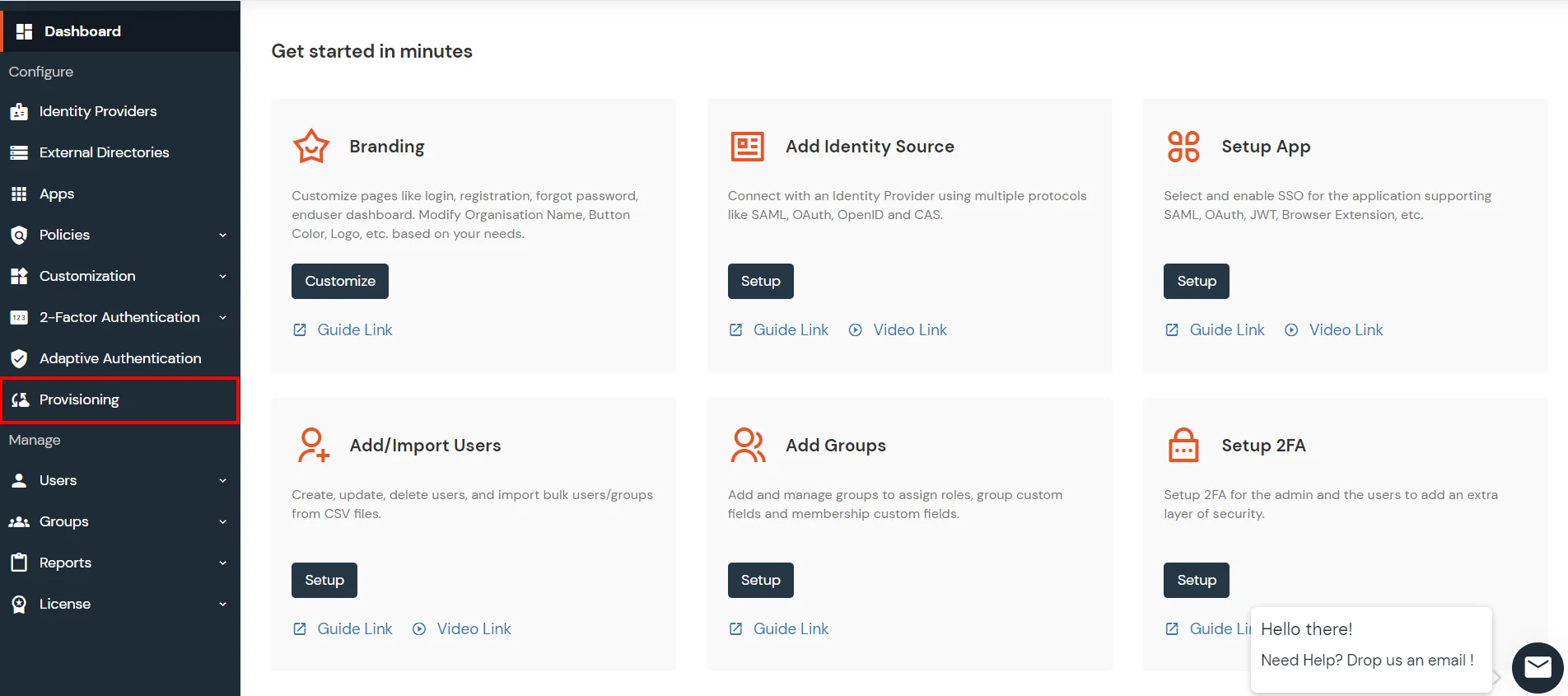
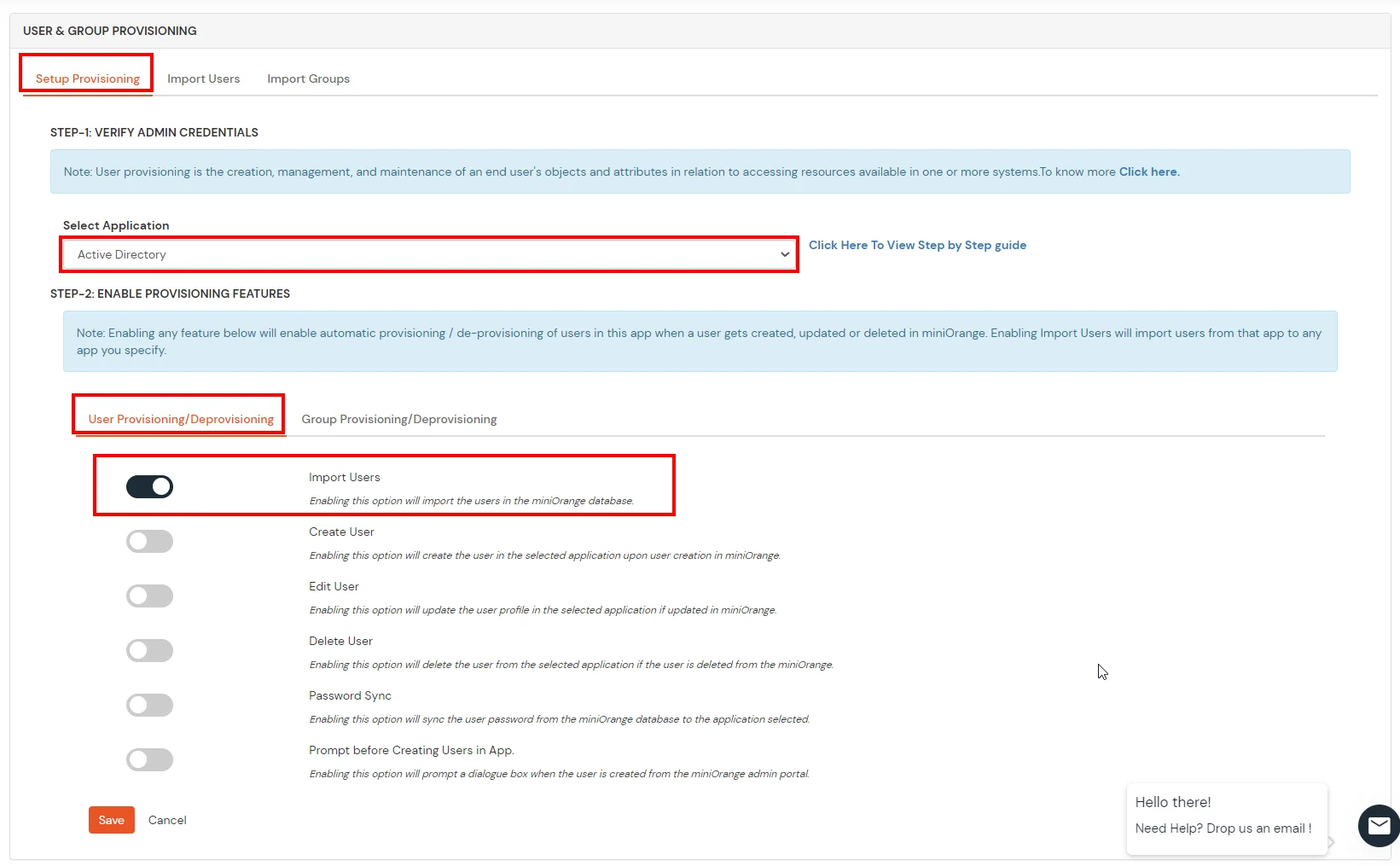
- From the Left-Side menu of the dashboard select Provisioning.
- In Setup Provisioning tab select Active Directory in the Select Application drop-down.
- Toggle the Import Users tab, click on Save button.
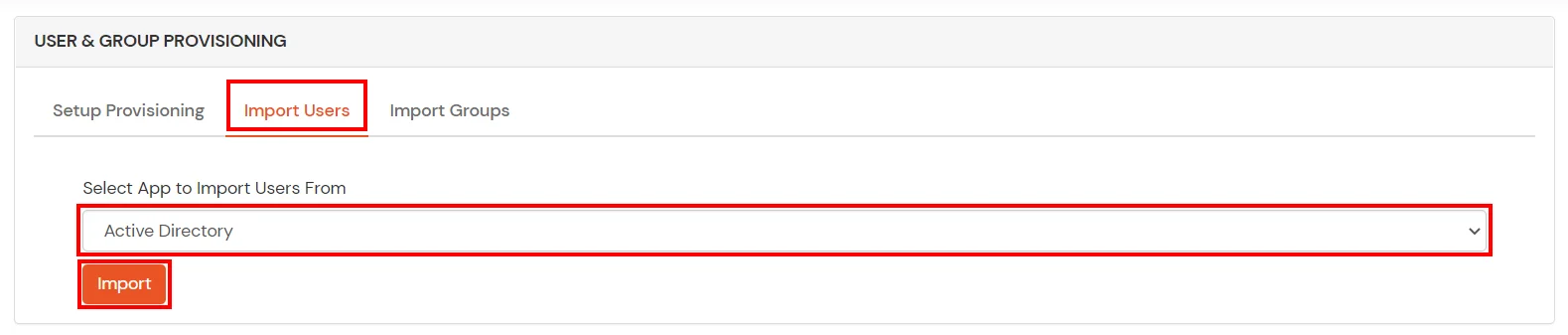
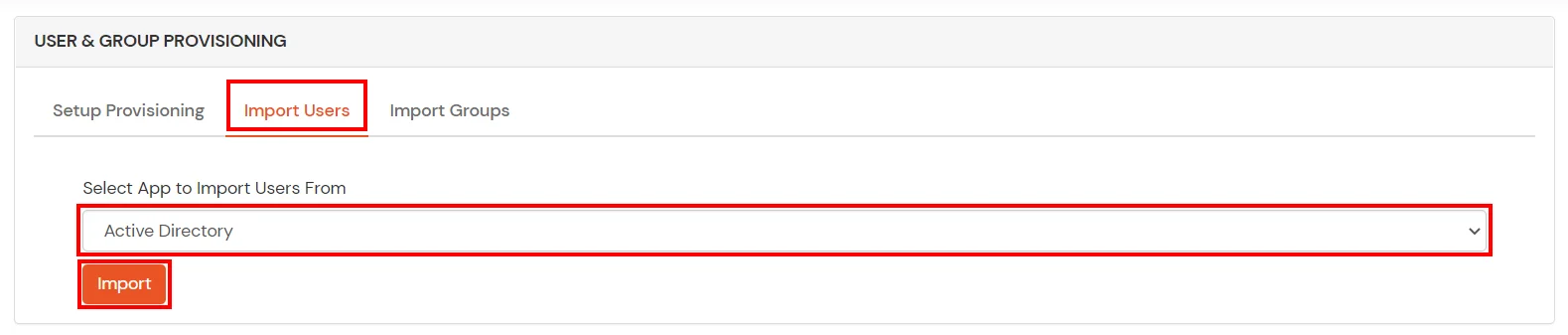
- On the same section, switch to Import Users section.
- Select Active Directory from the dropdown and click on the Import Users tab, to import all the users from Active Directory to miniOrange.
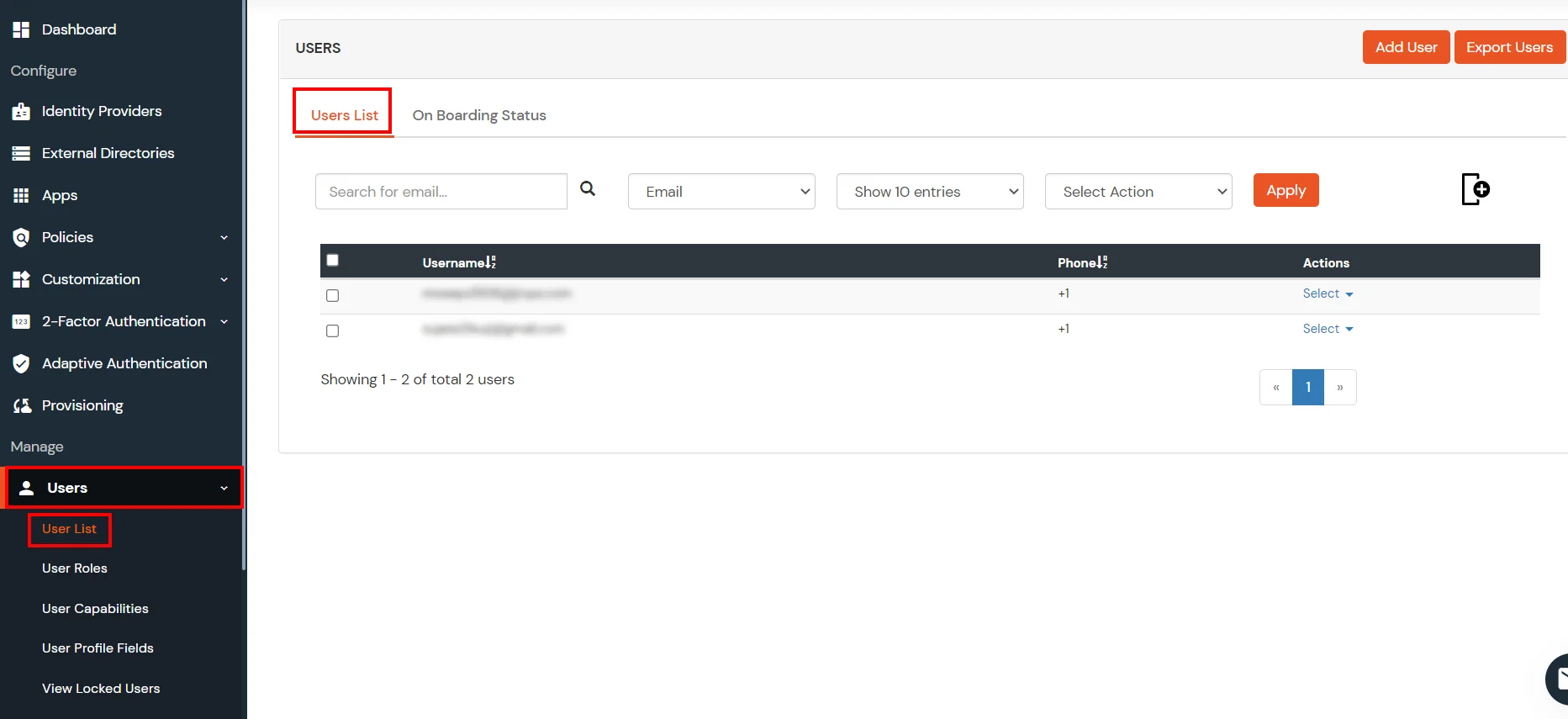
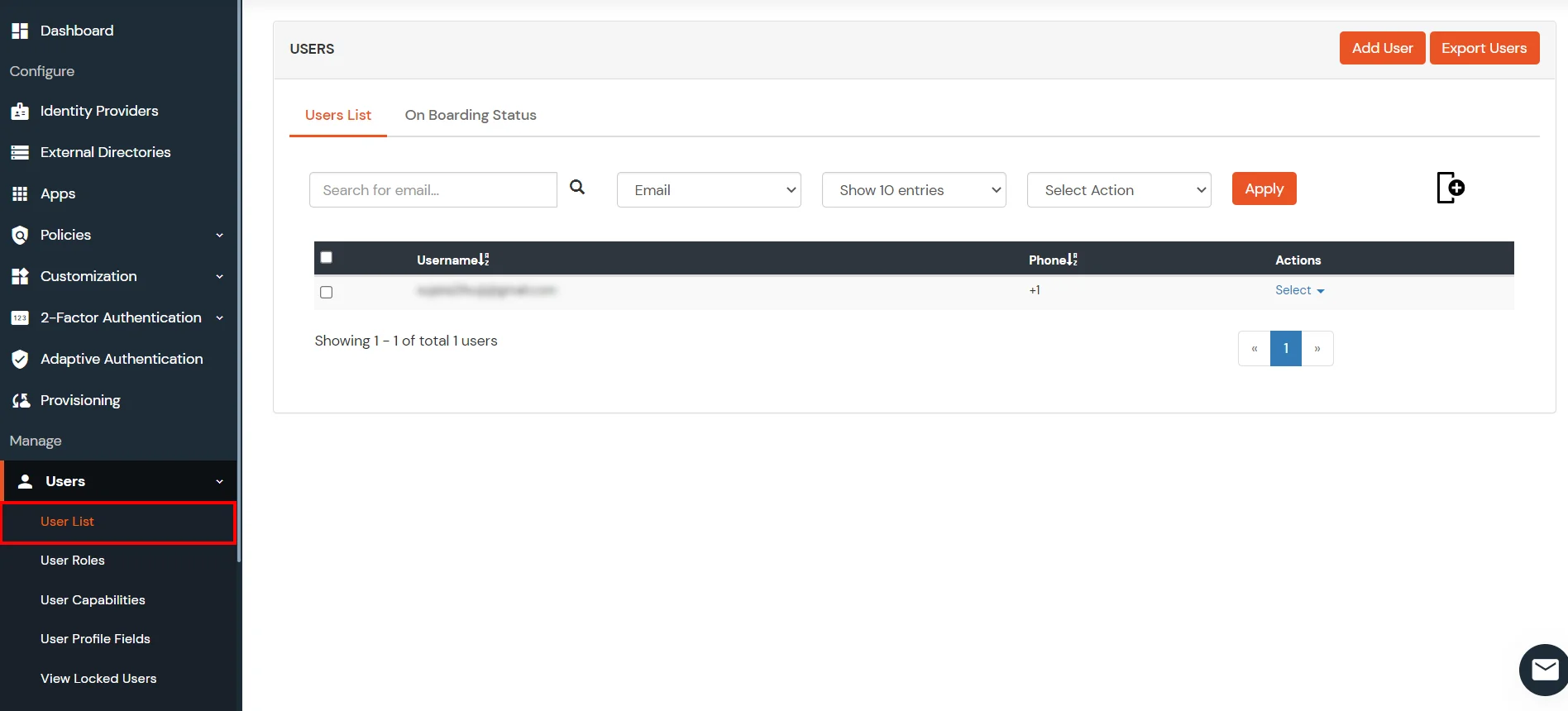
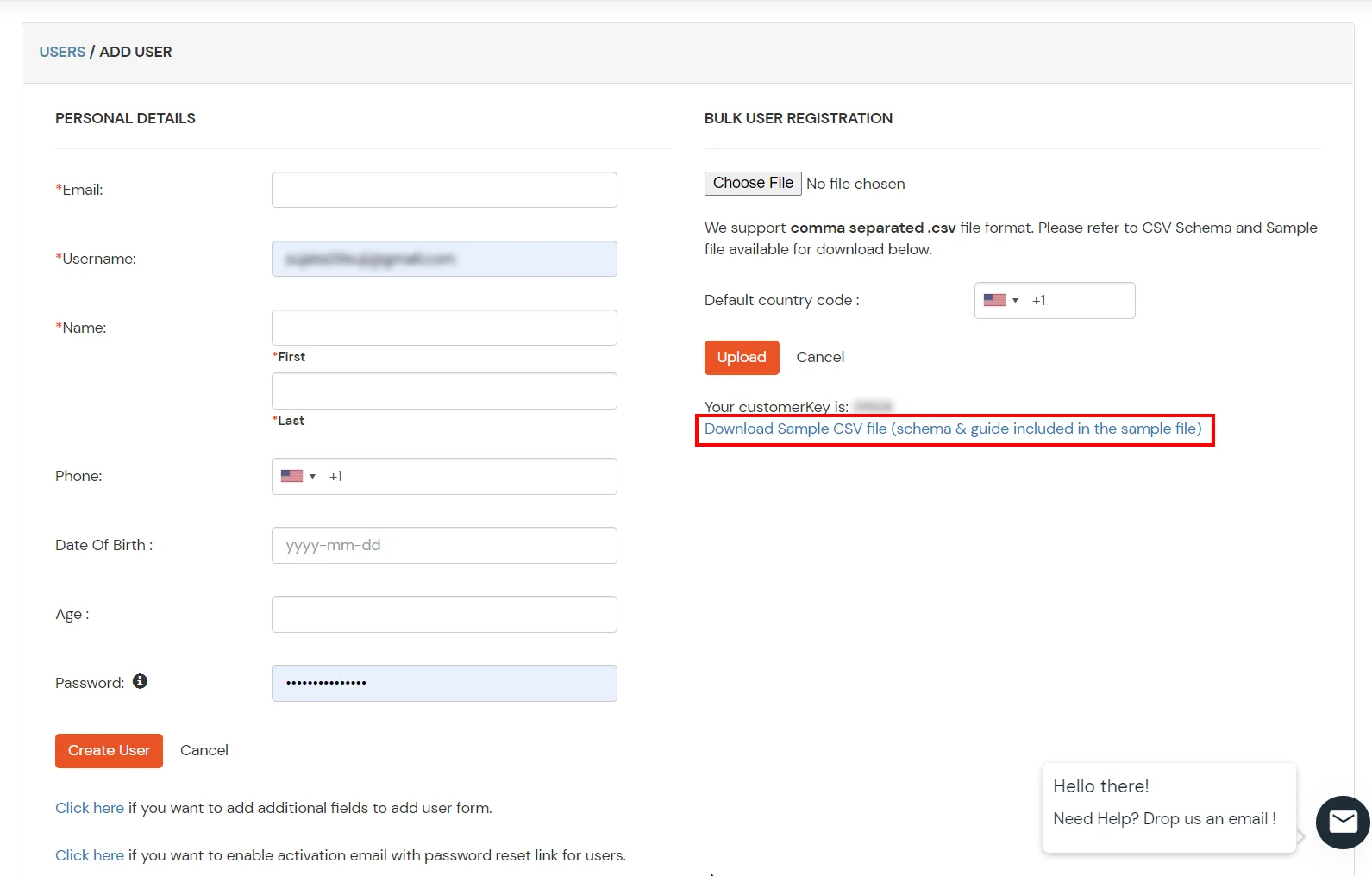
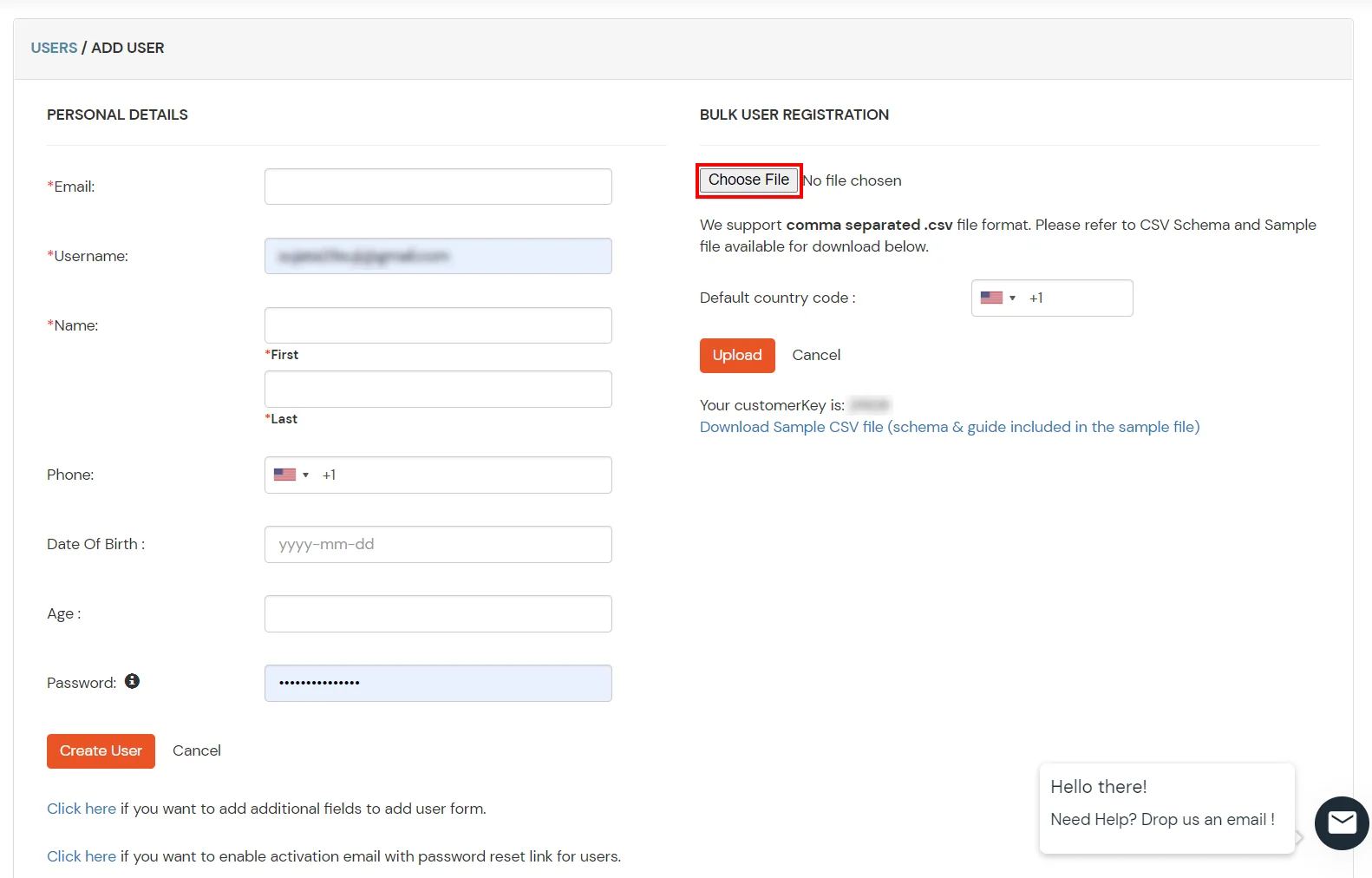
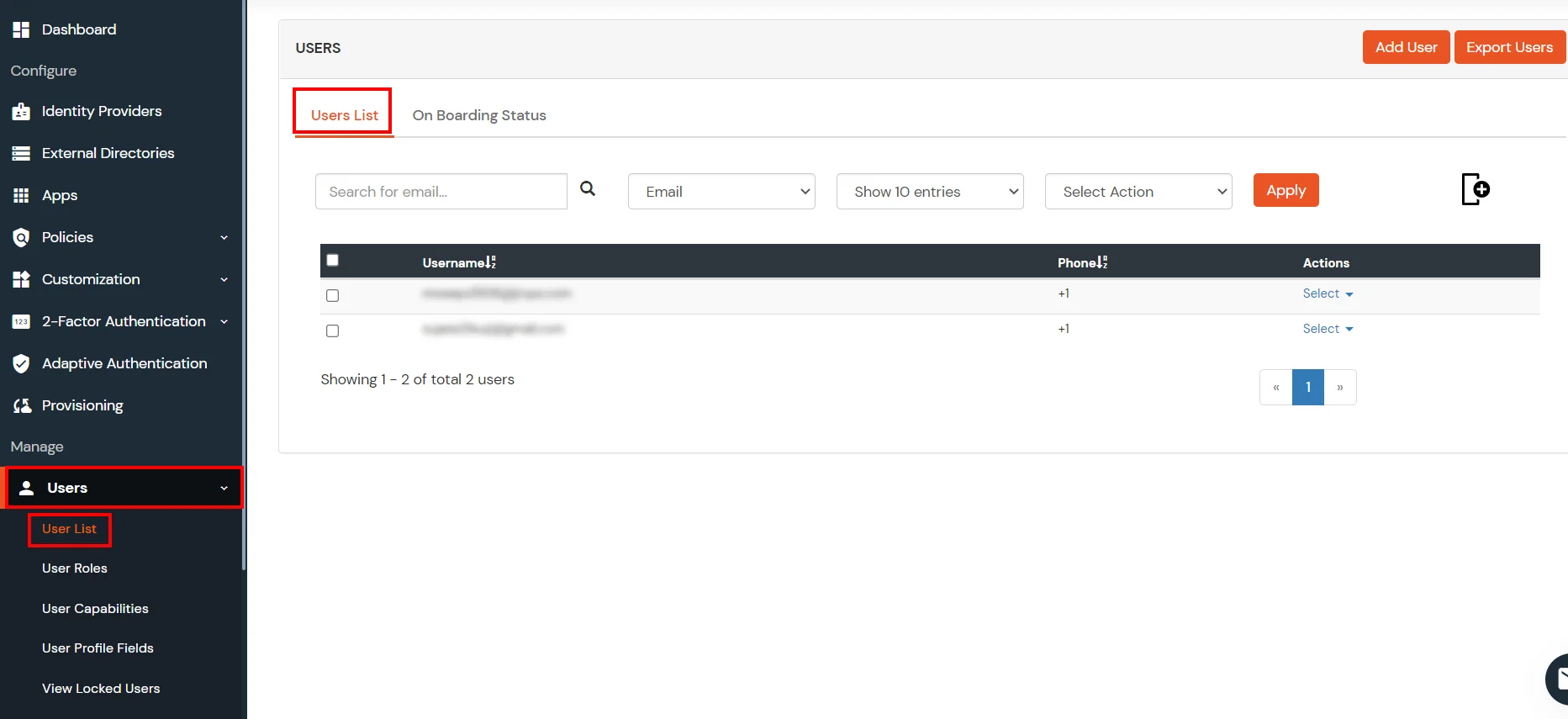
- You can view all the Users you have imports by selecting Users >> User List from Left Panel.
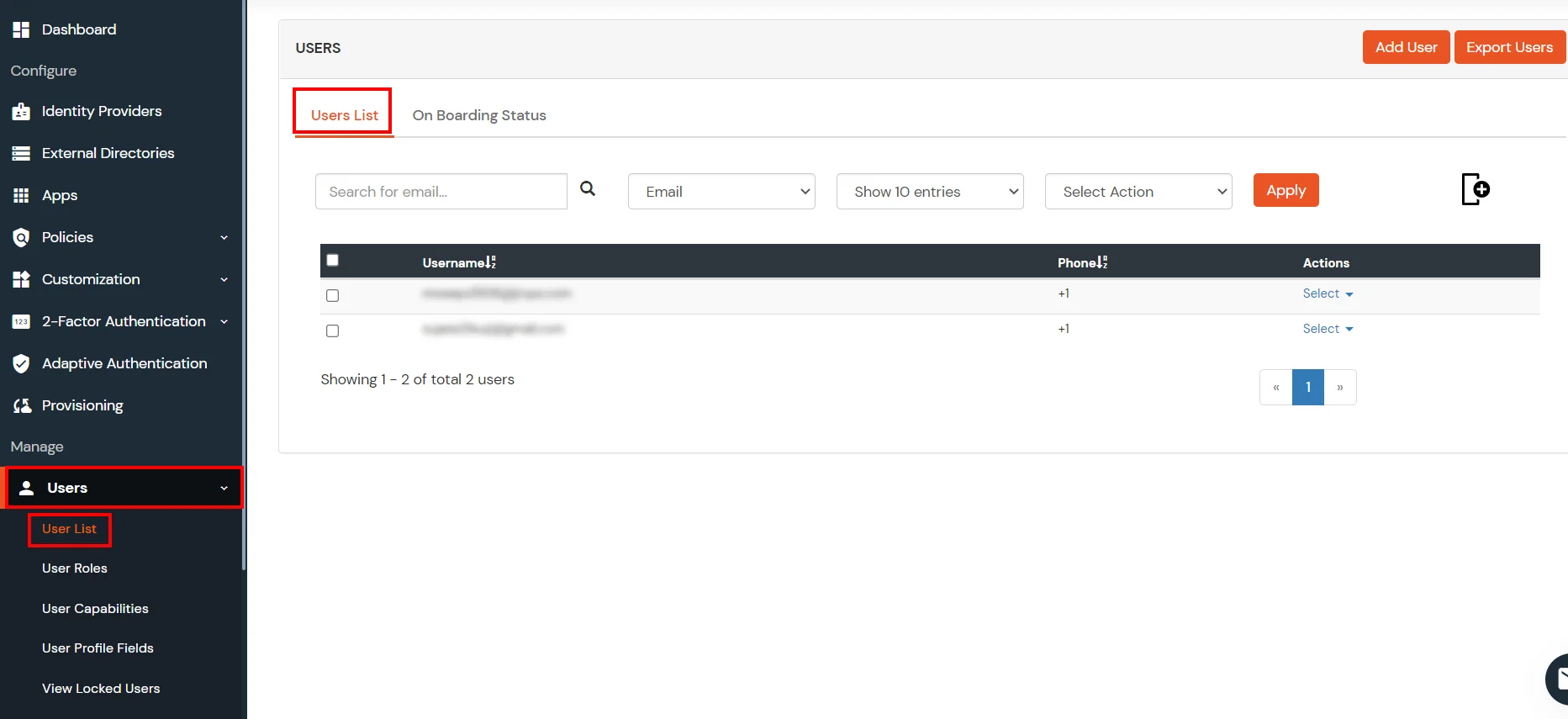
- All the imported users will be auto registered.
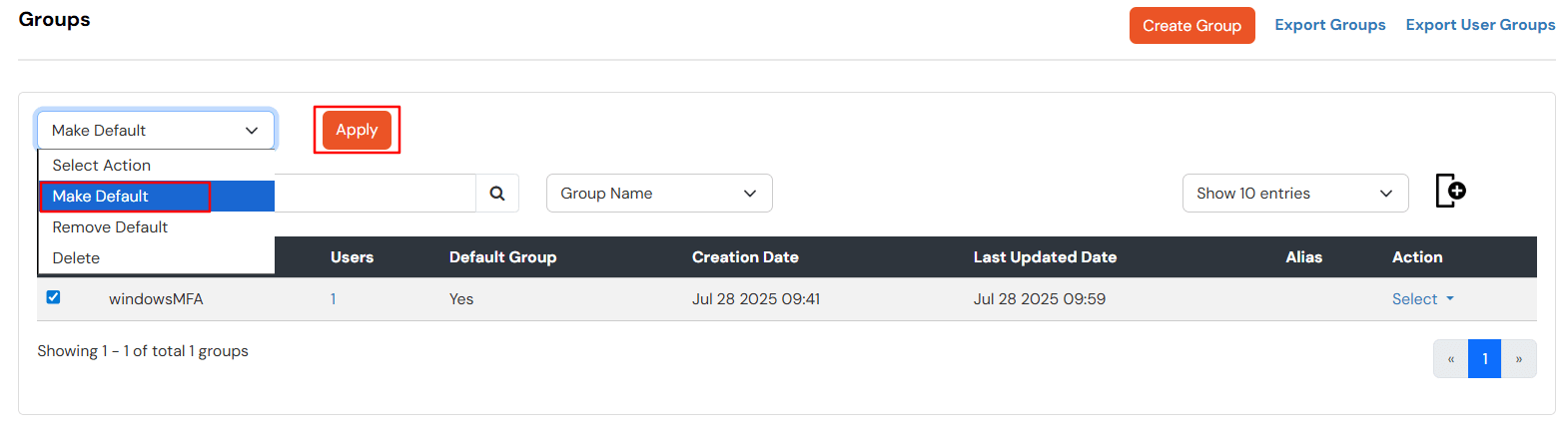
- These groups will be helpful in adding multiple 2FA policies on the applications.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
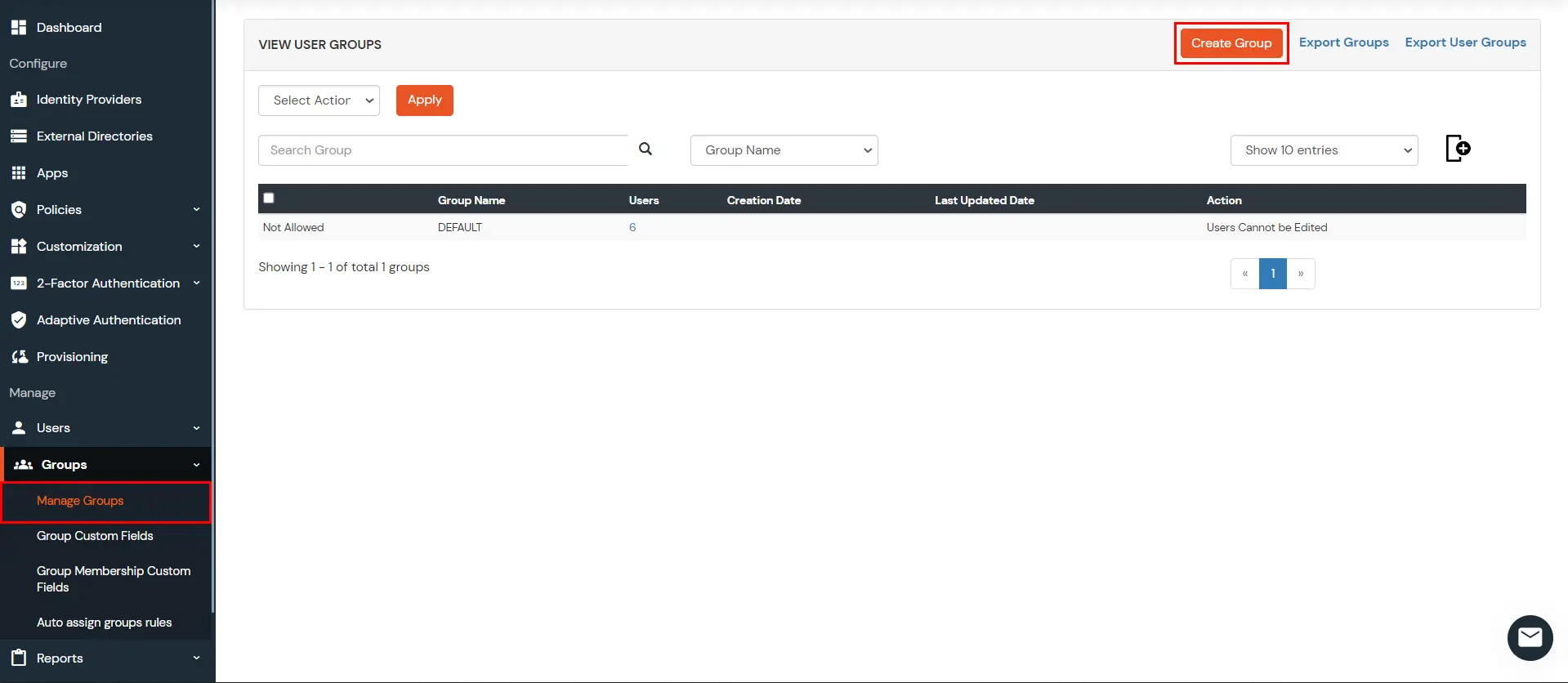
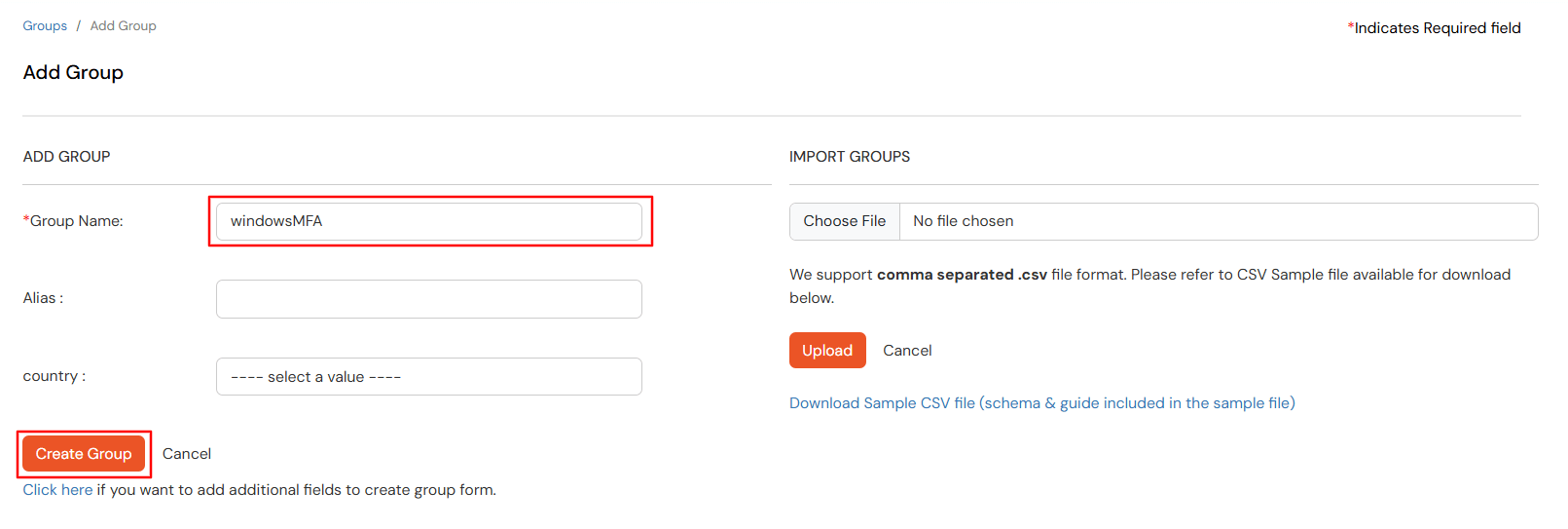
6. Creating User Groups(Recommended)
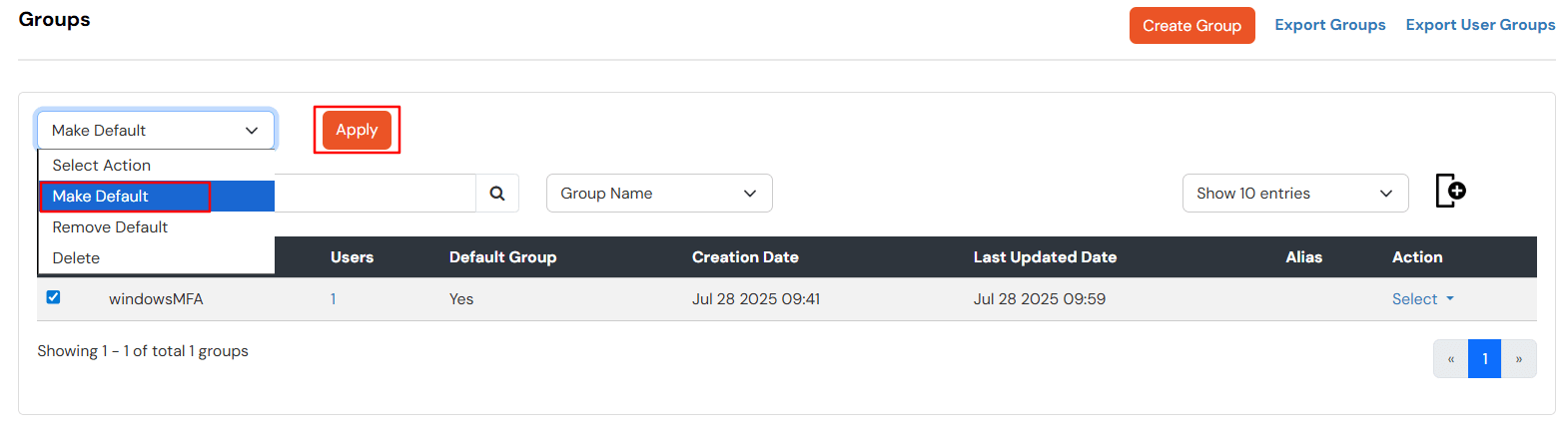
- Select Groups >> Manage Groups from left panel.
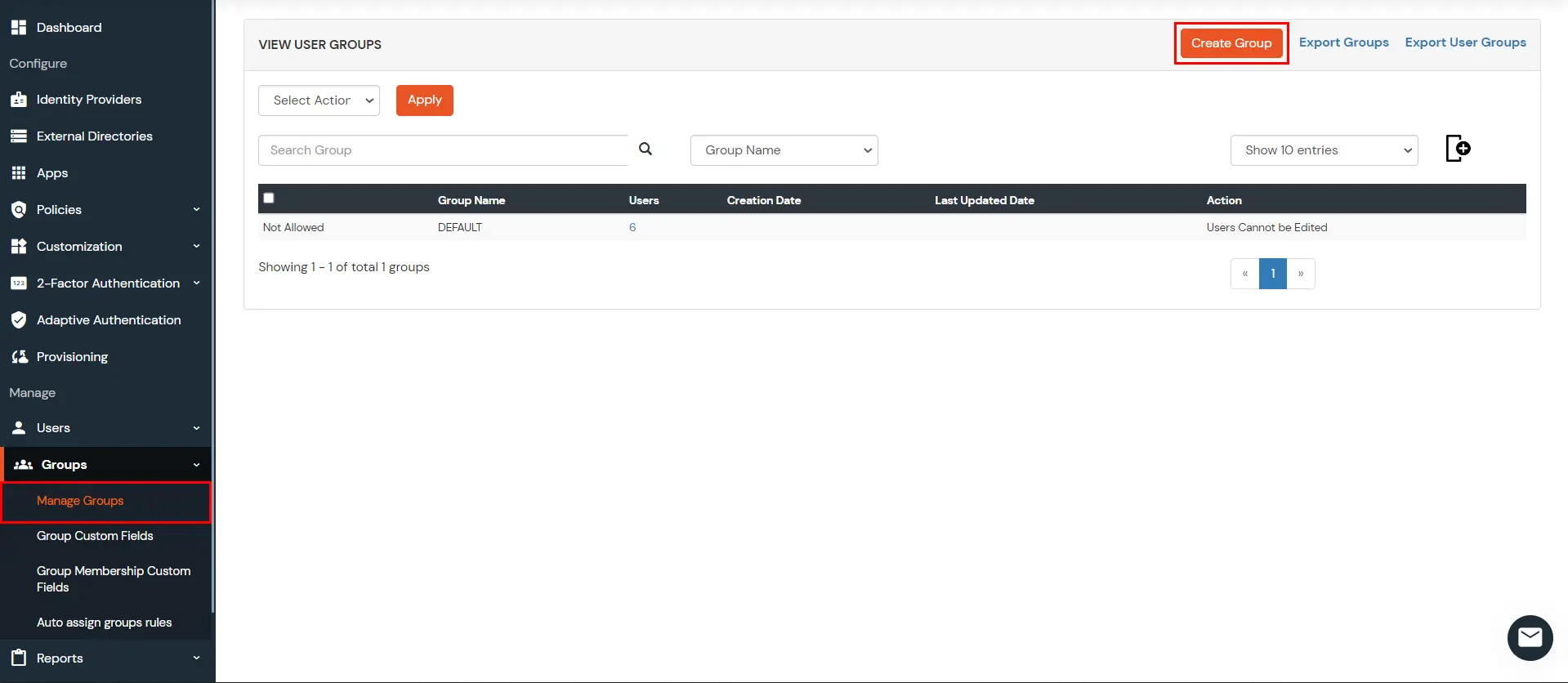
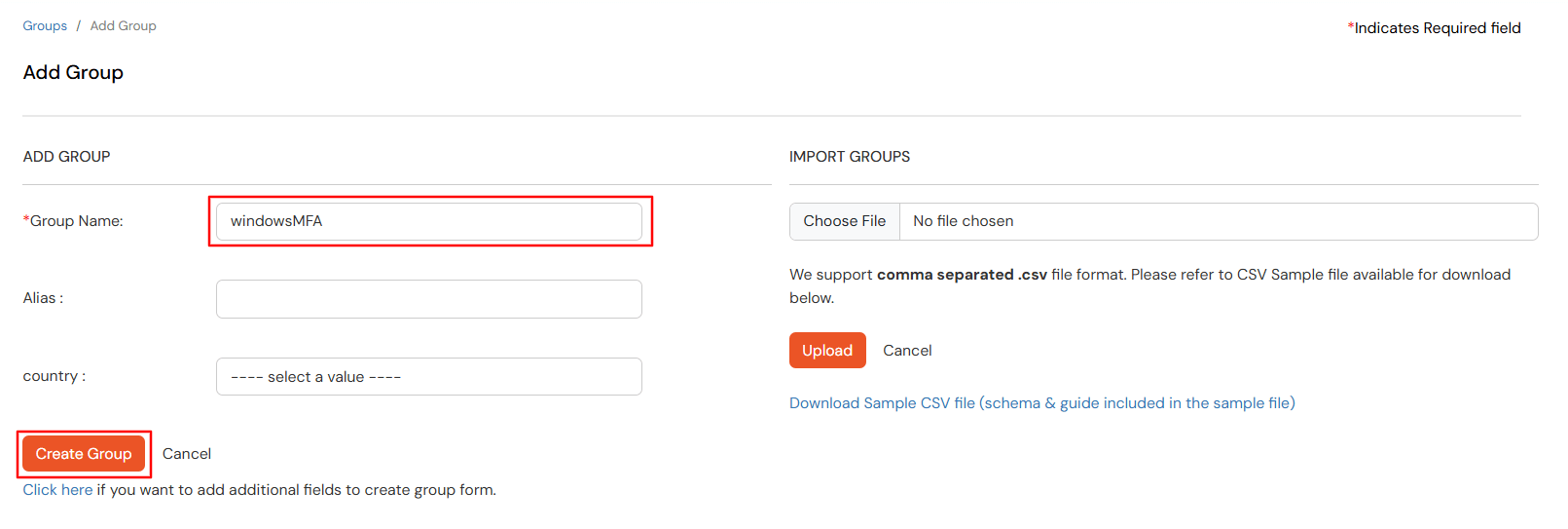
- Click on the Create Group button on the top.
- Enter windowsMFA as Group Name and click on Create Group.
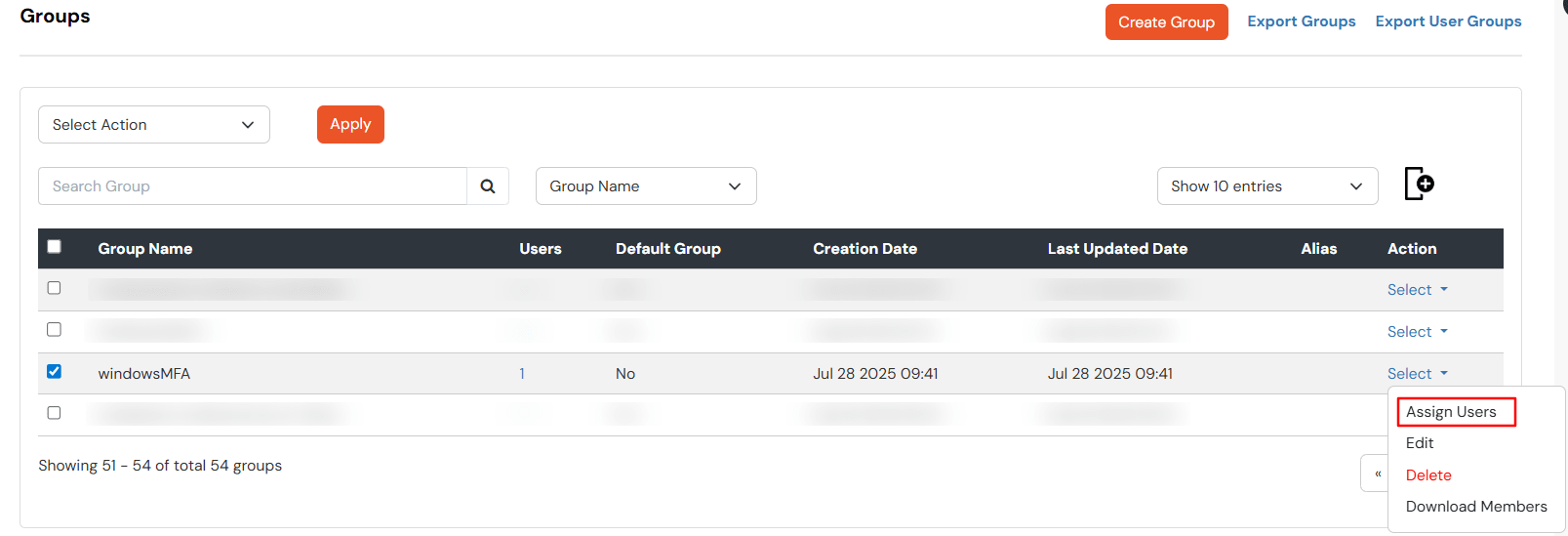
- Assign various members to the group using the Assign User option associated with the group in the groups list.
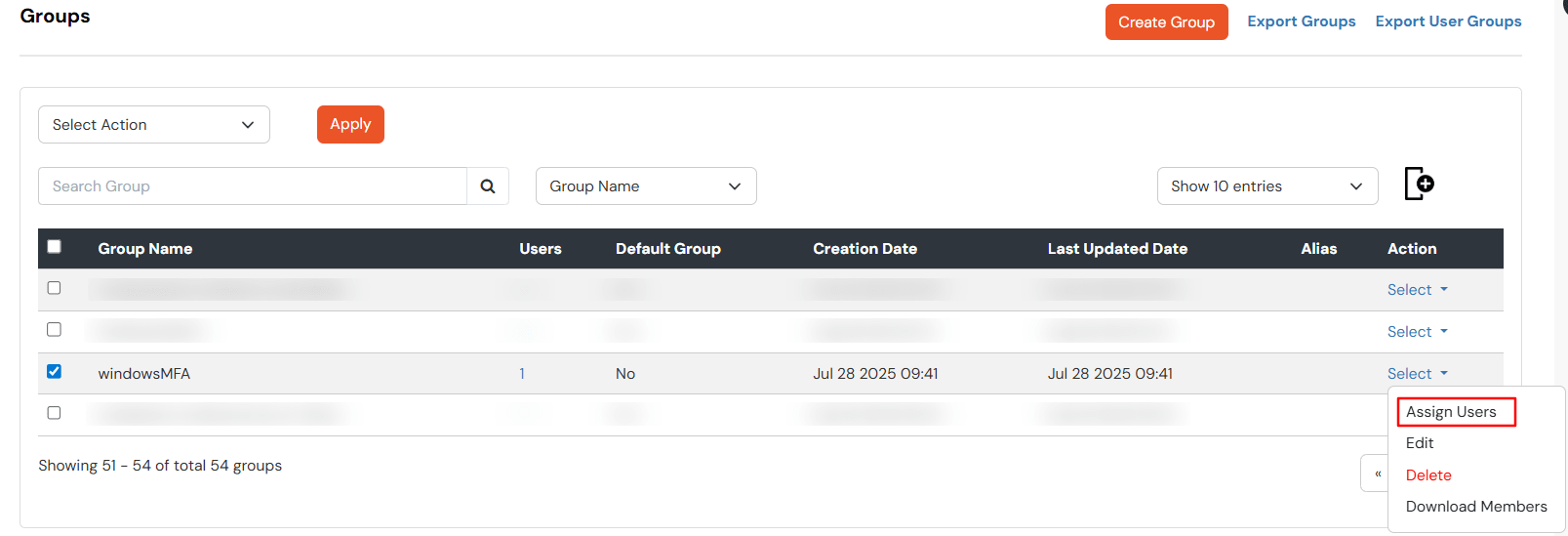
- Select the Users that are required to be assigned to this group. Then Select Assign to Group in Select Action Dropdown. Then click Apply.
External References