Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×miniOrange Identity Broker service solution enables cross protocol authentication. You can configure Azure B2C as an IDP for Single Sign-On (SSO) into your applications/websites. Here, Azure B2C will act as an Identity Provider (IDP) and miniOrange will act as a broker.
We offer a pre-built solution for integrating with Azure B2C, making it easier and quick to implement. Our team can also help you set up Azure B2C as SAML or OIDC IDP to login into your applications.
miniOrange offers free help through a consultation call with our System Engineers to configure Single Sign-On (SSO) for different apps using Azure B2C as an Identity Provider in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
Please make sure your organisation branding is already set under Customization >> Login and Registration Branding in the left menu of the dashboard.
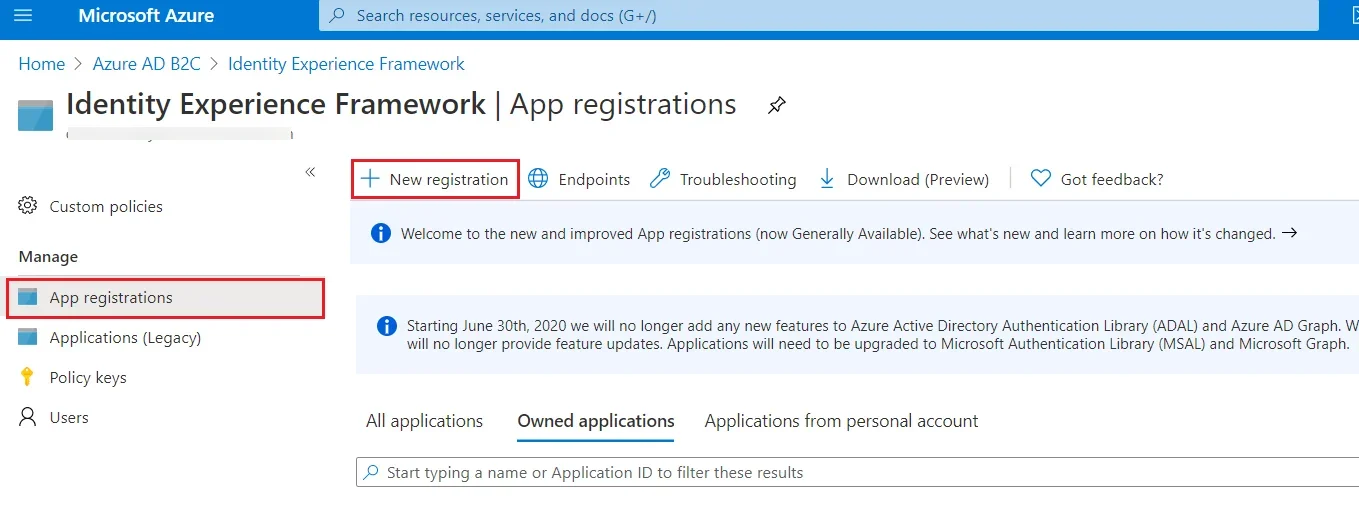
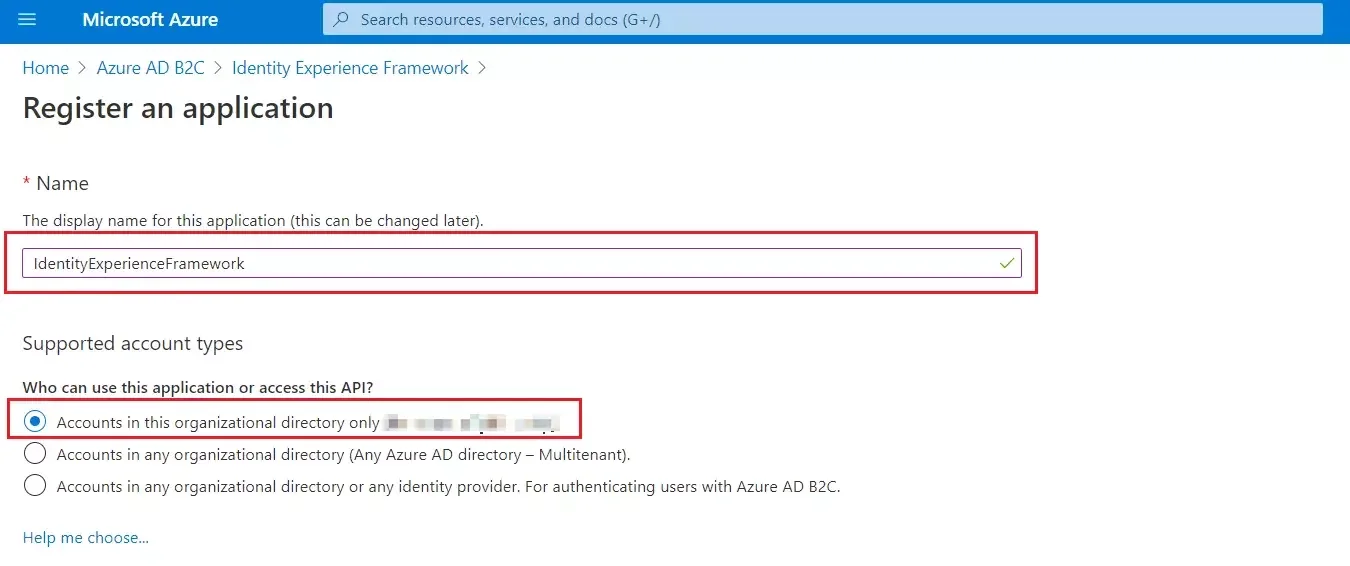
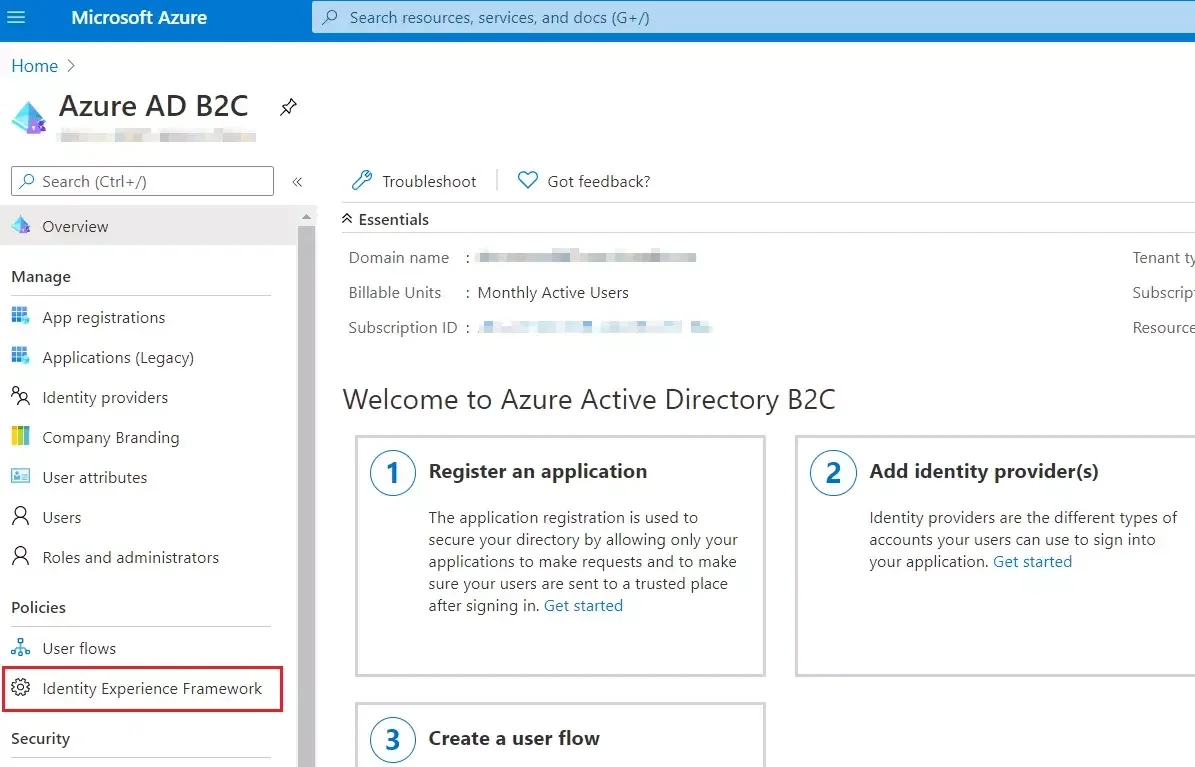
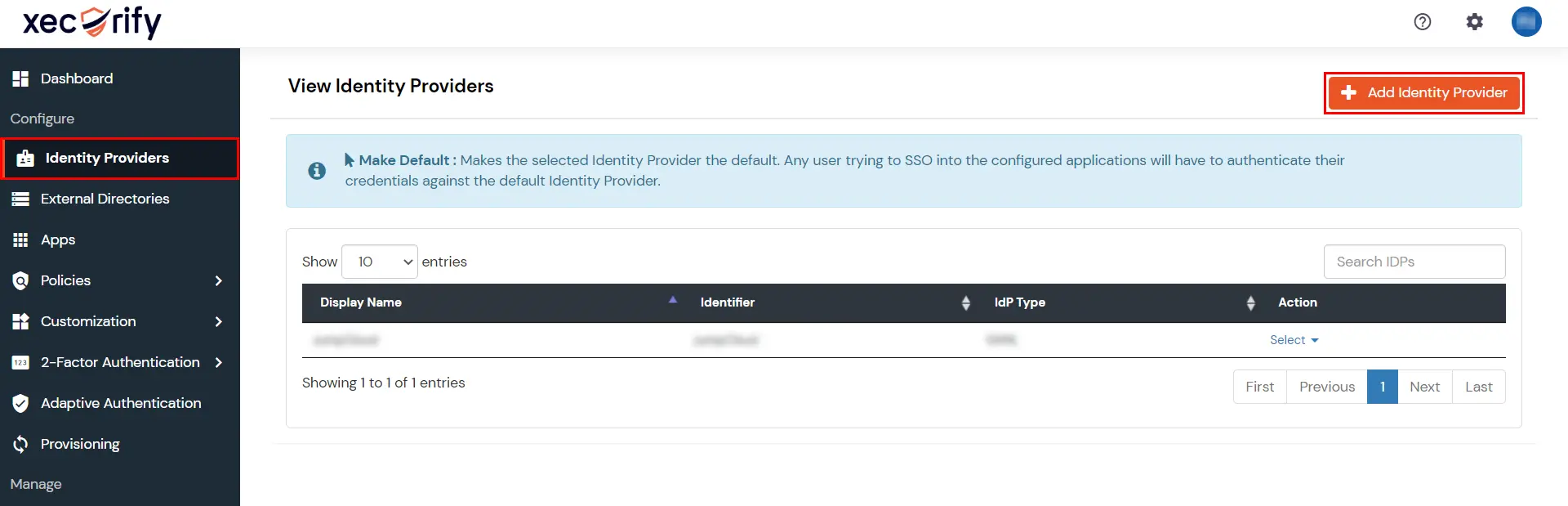
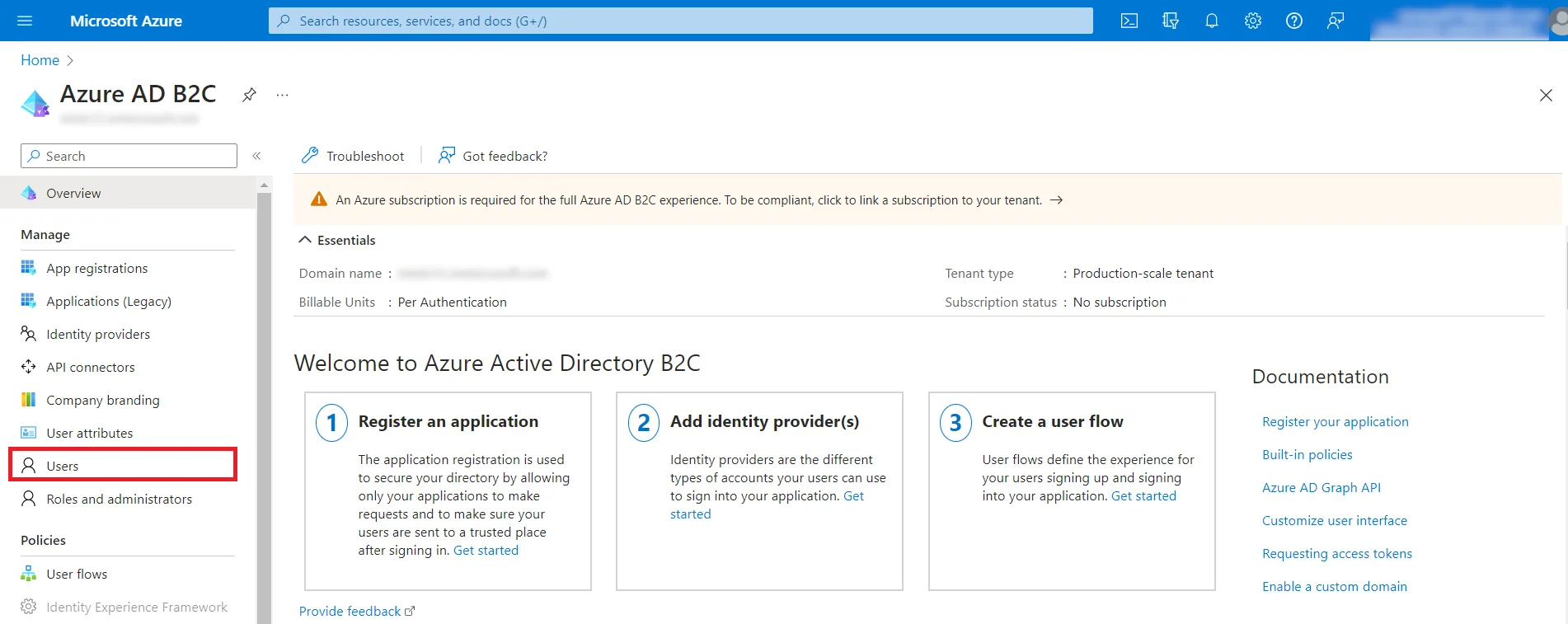
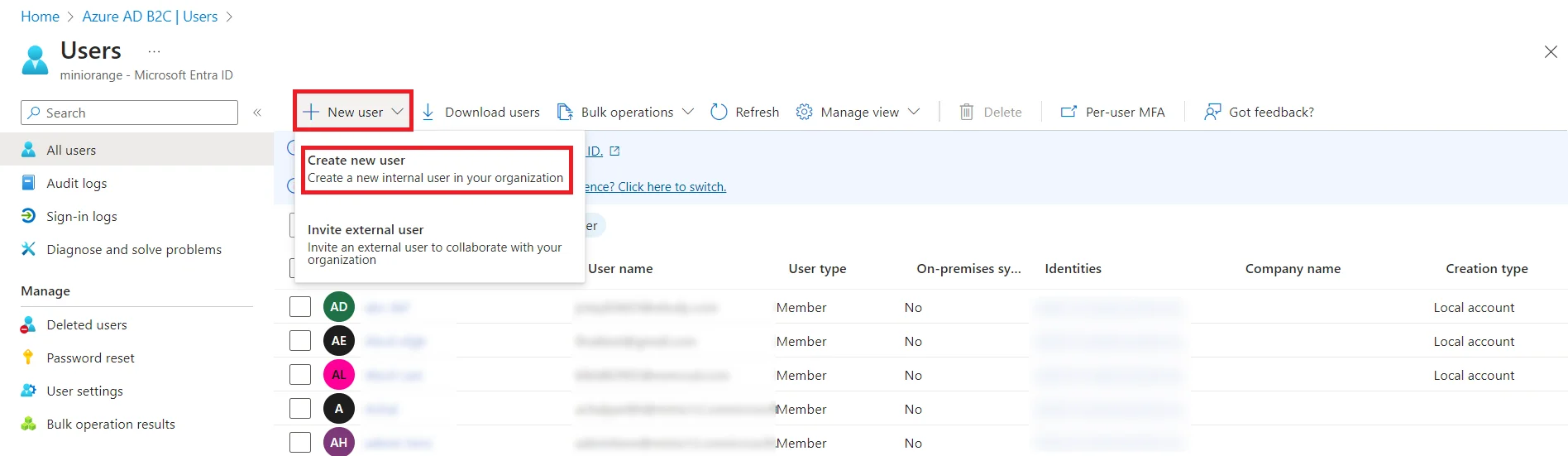
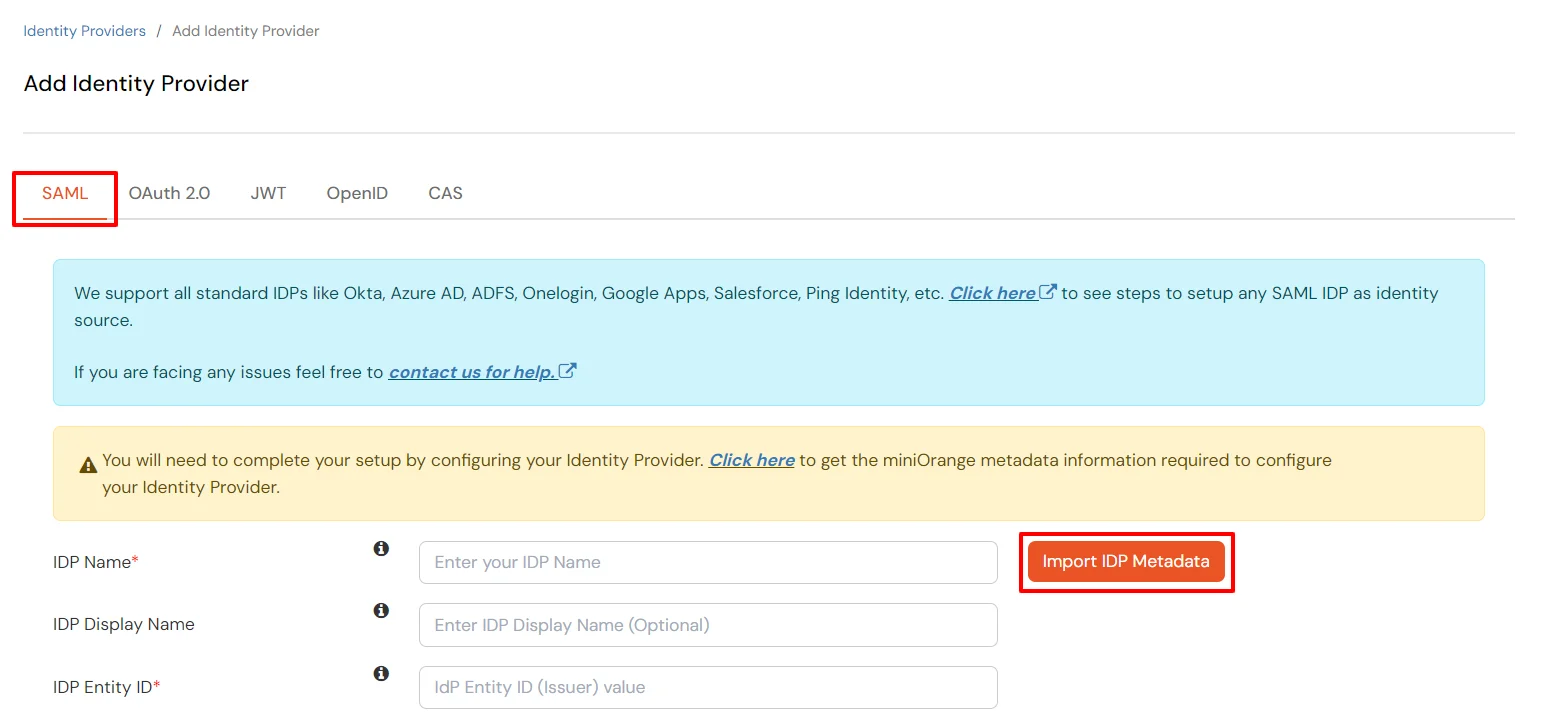
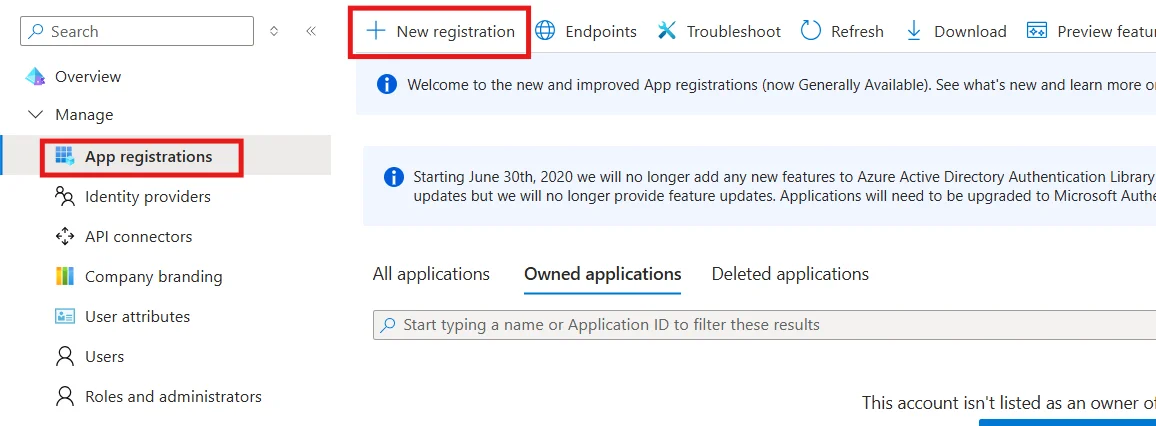
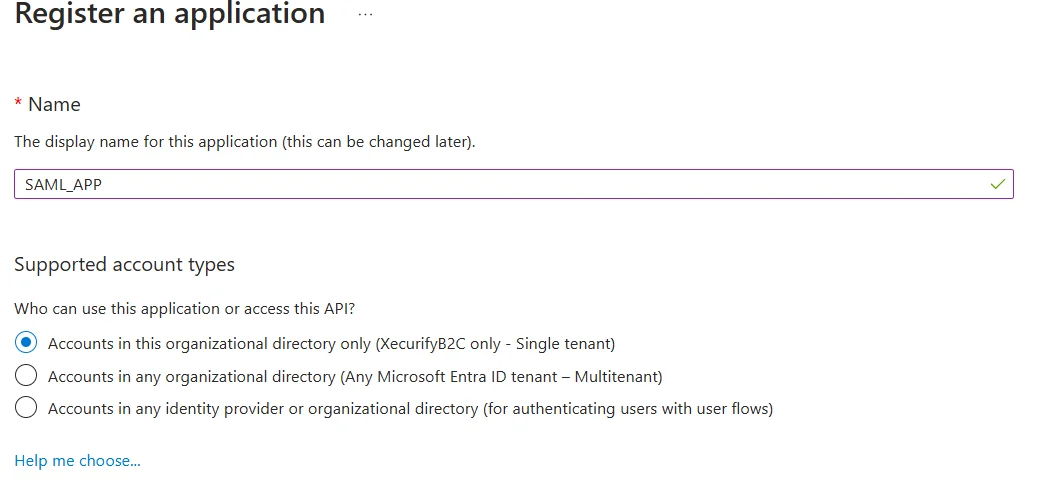
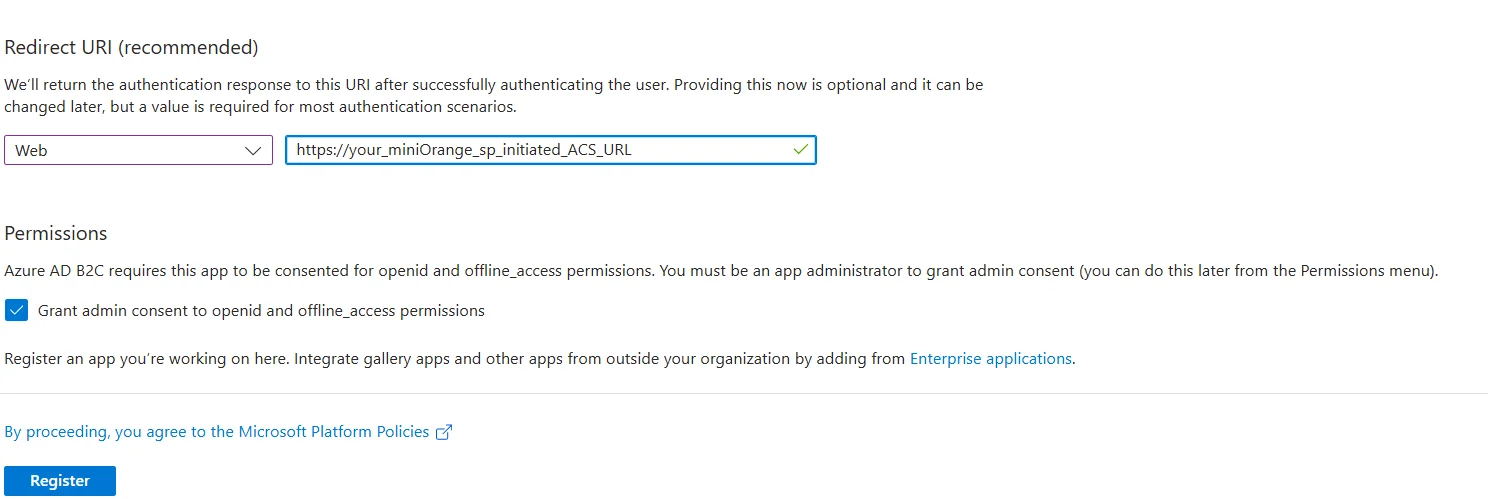
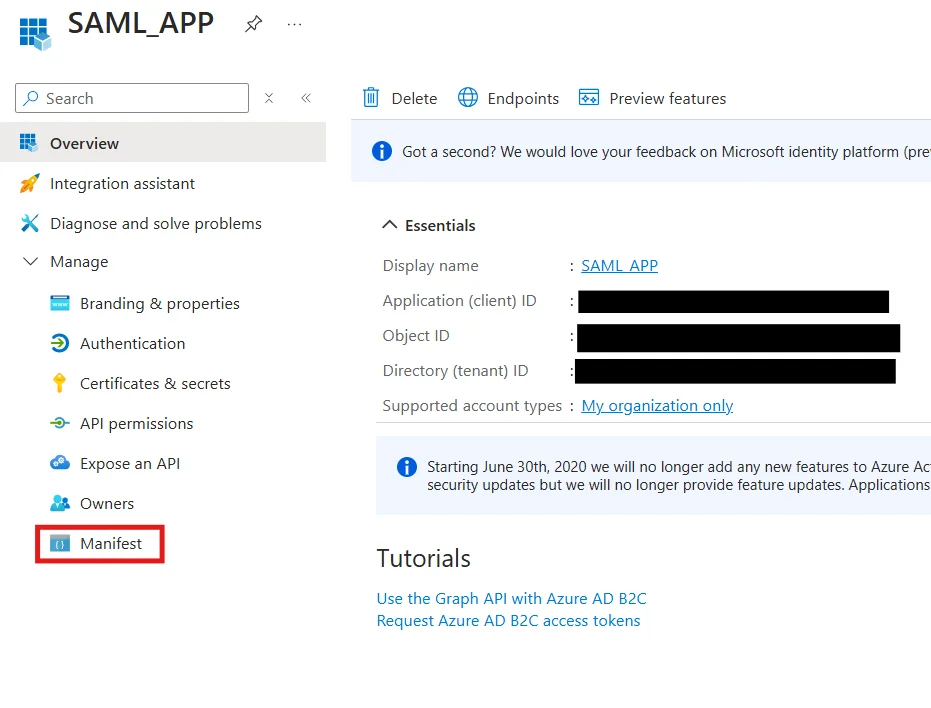
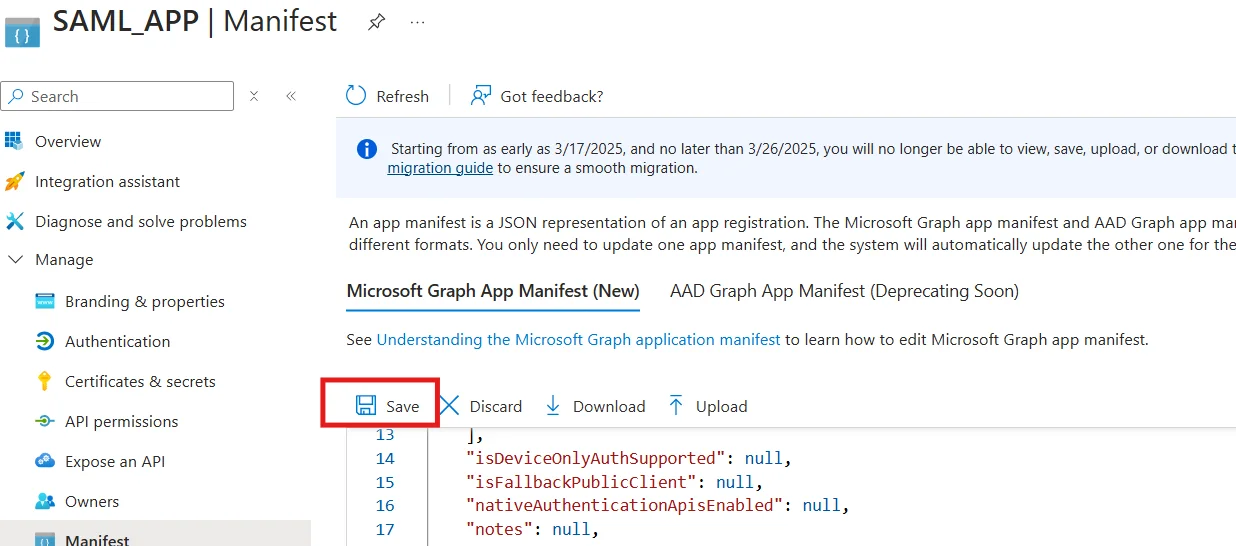
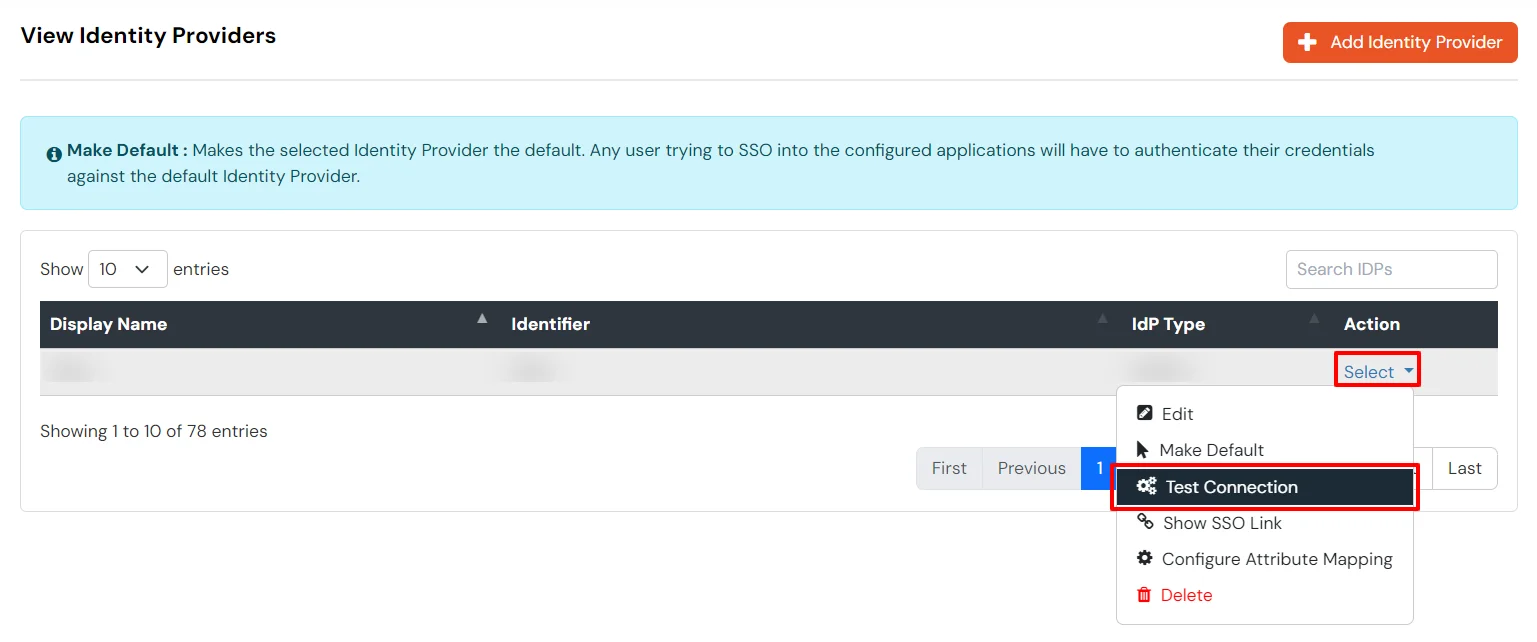
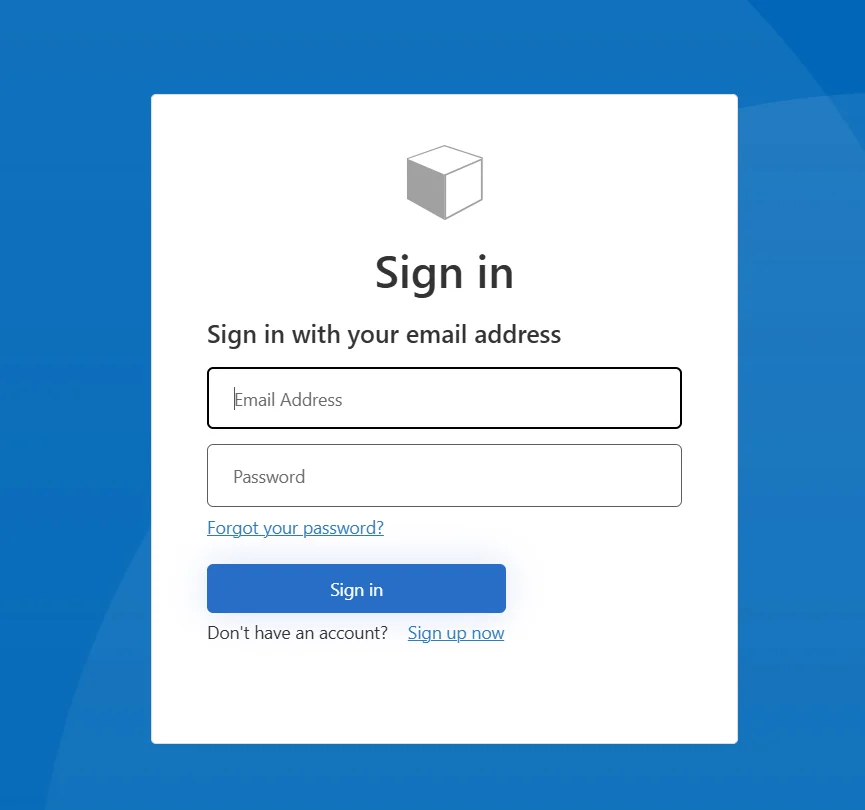
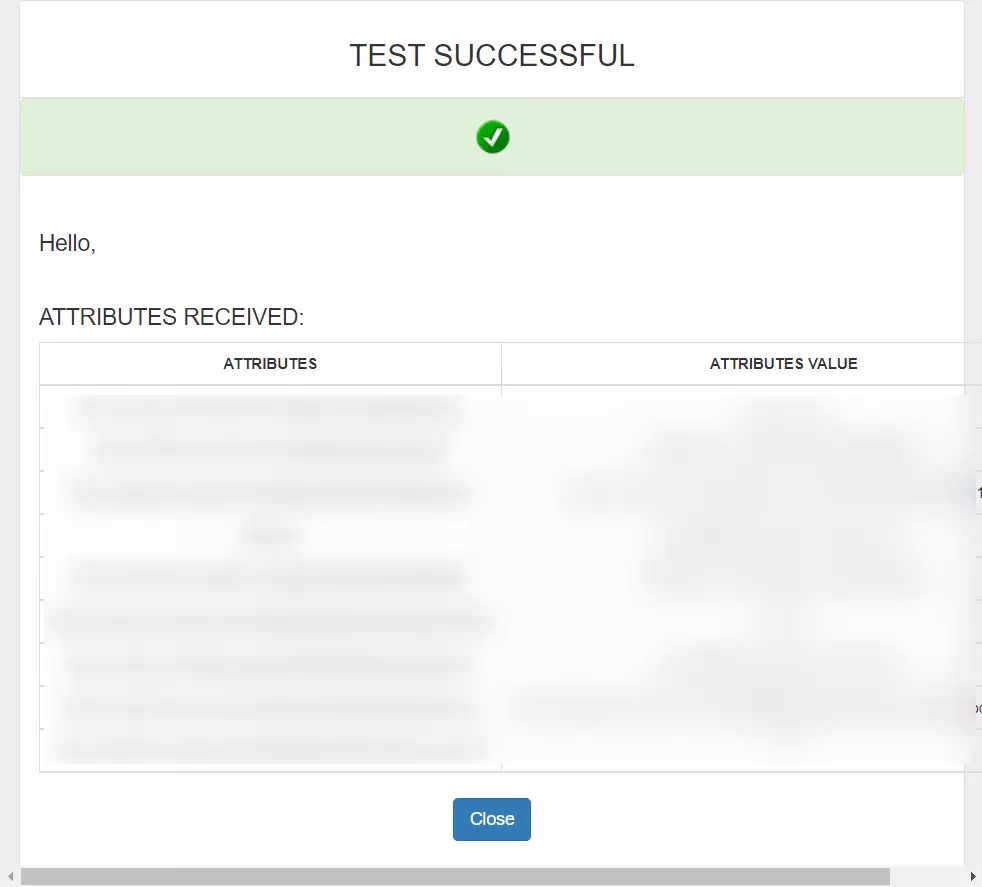
Follow the steps below to configure Azure AD B2C as an Identity Provider:
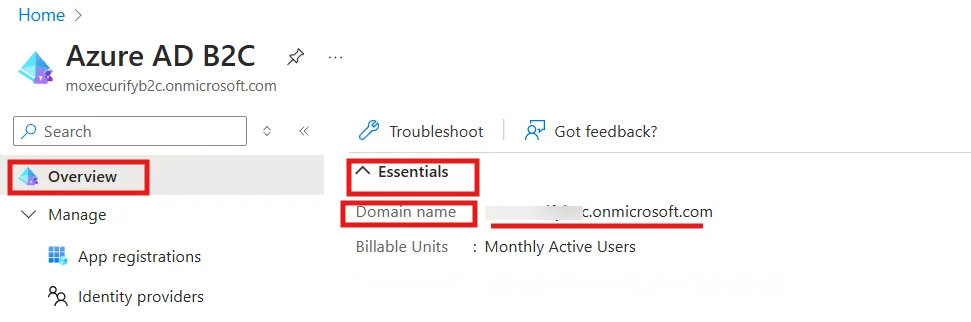
To find your Tenant name, go to the Azure B2C home page. In the Overview section, under Essentials, you'll see a Domain name field. The part before .onmicrosoft.com is your tenant name.
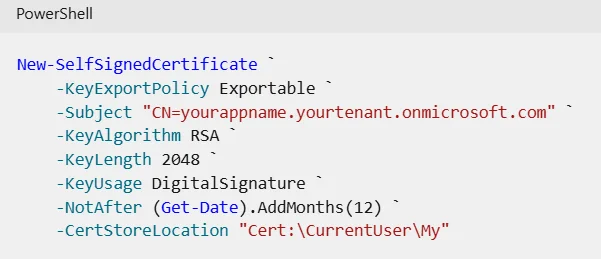
Obtain a certificate:- If you don't already have a certificate, you can use a self-signed certificate. A self-signed certificate is a security certificate that is not signed by a certificate authority (CA) and doesn't provide the security guarantees of a certificate signed by a CA.
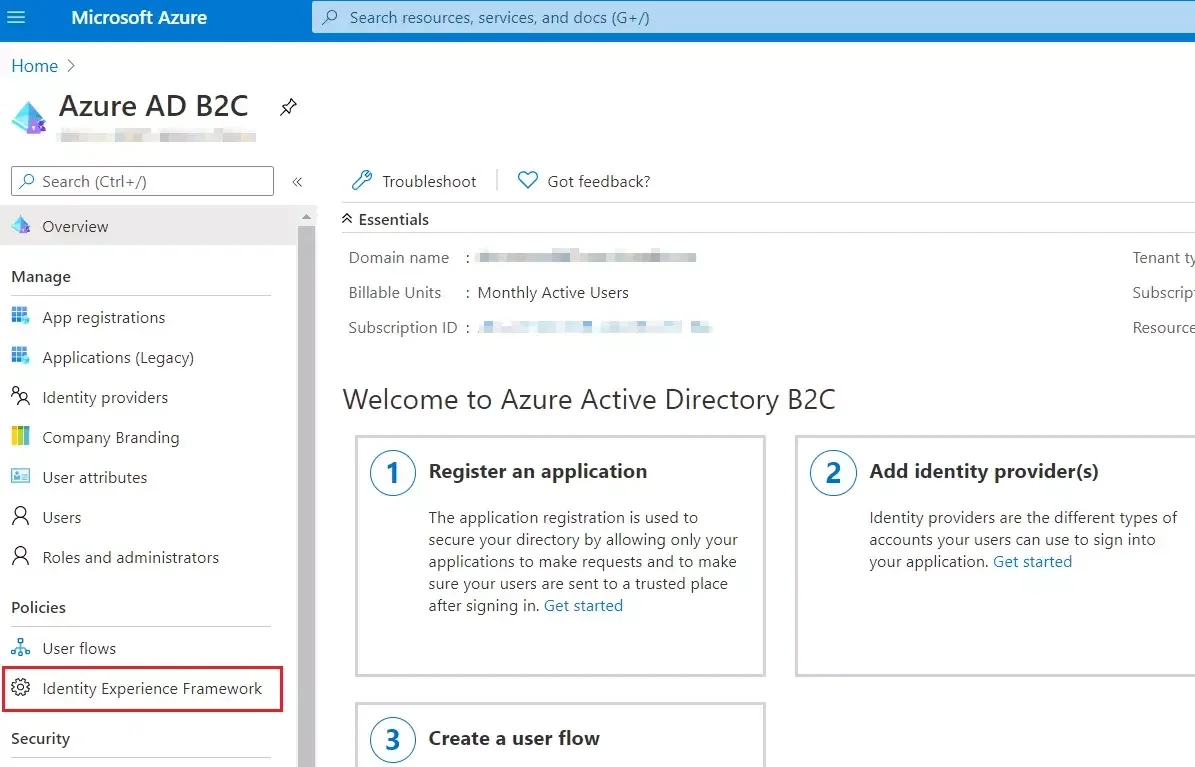
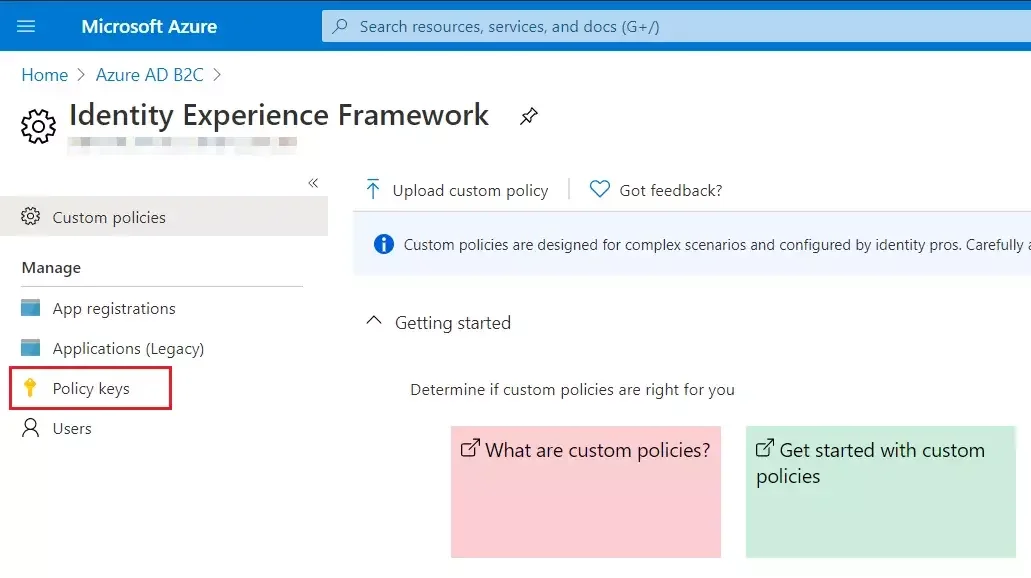
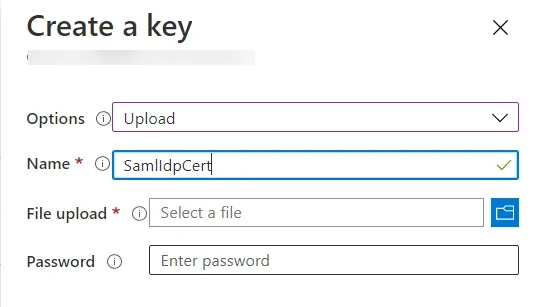
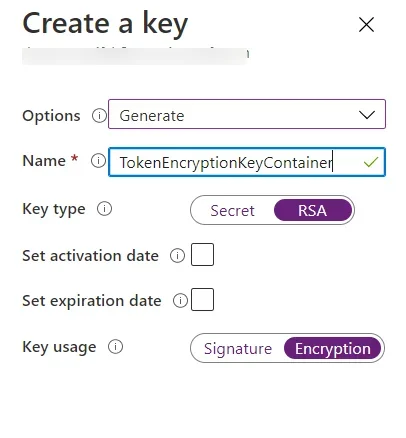
Create the encryption key:
Upload the Policies:









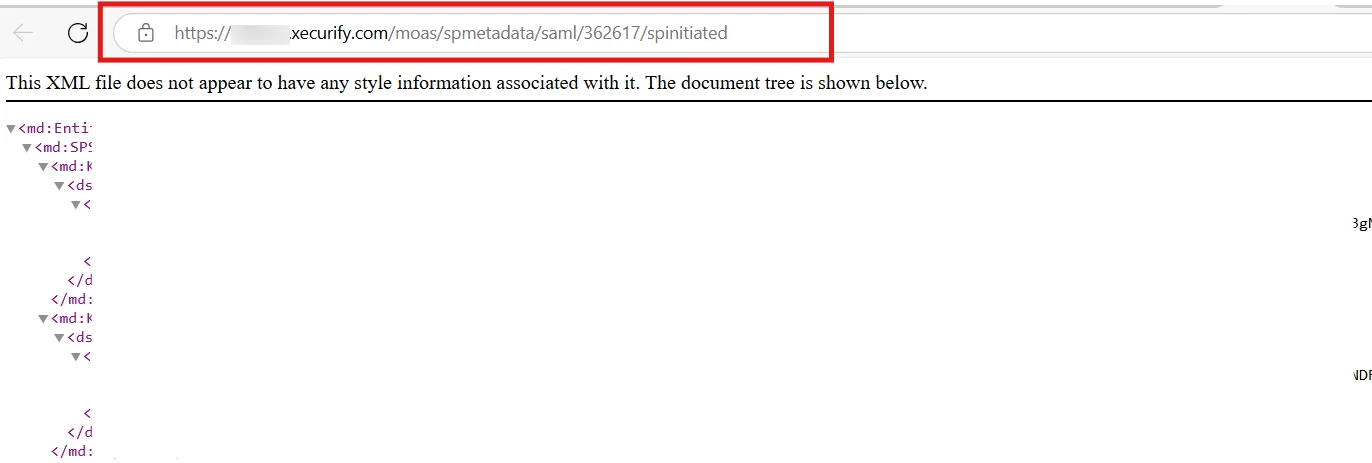
In this url section you have to replace the tenant-name with your tenant name and policy_Name with your actual policy name.
For example your tenant name is MiniOrange and policy name is signup_signin_saml then your URL will be https://MiniOrange.b2clogin.com/MiniOrange.onmicrosoft.com/B2C_1A_signup_signin_saml/Samlp/metadata

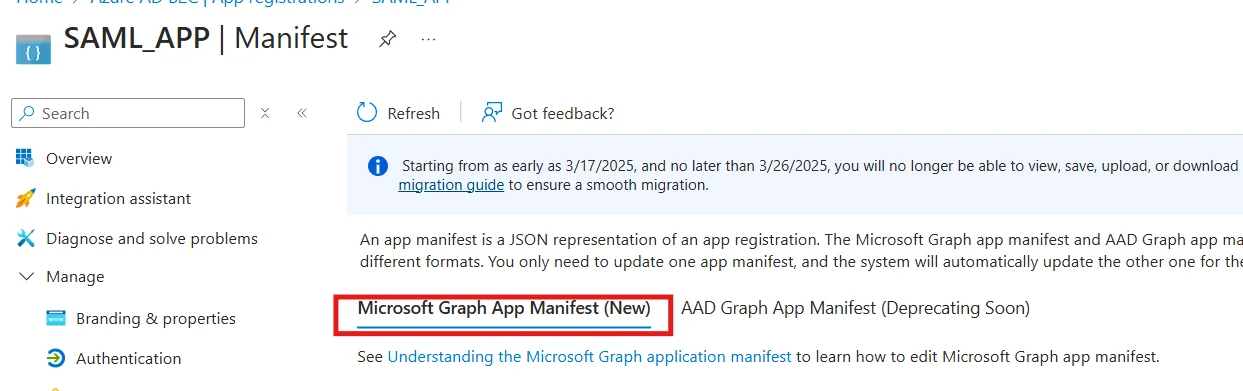
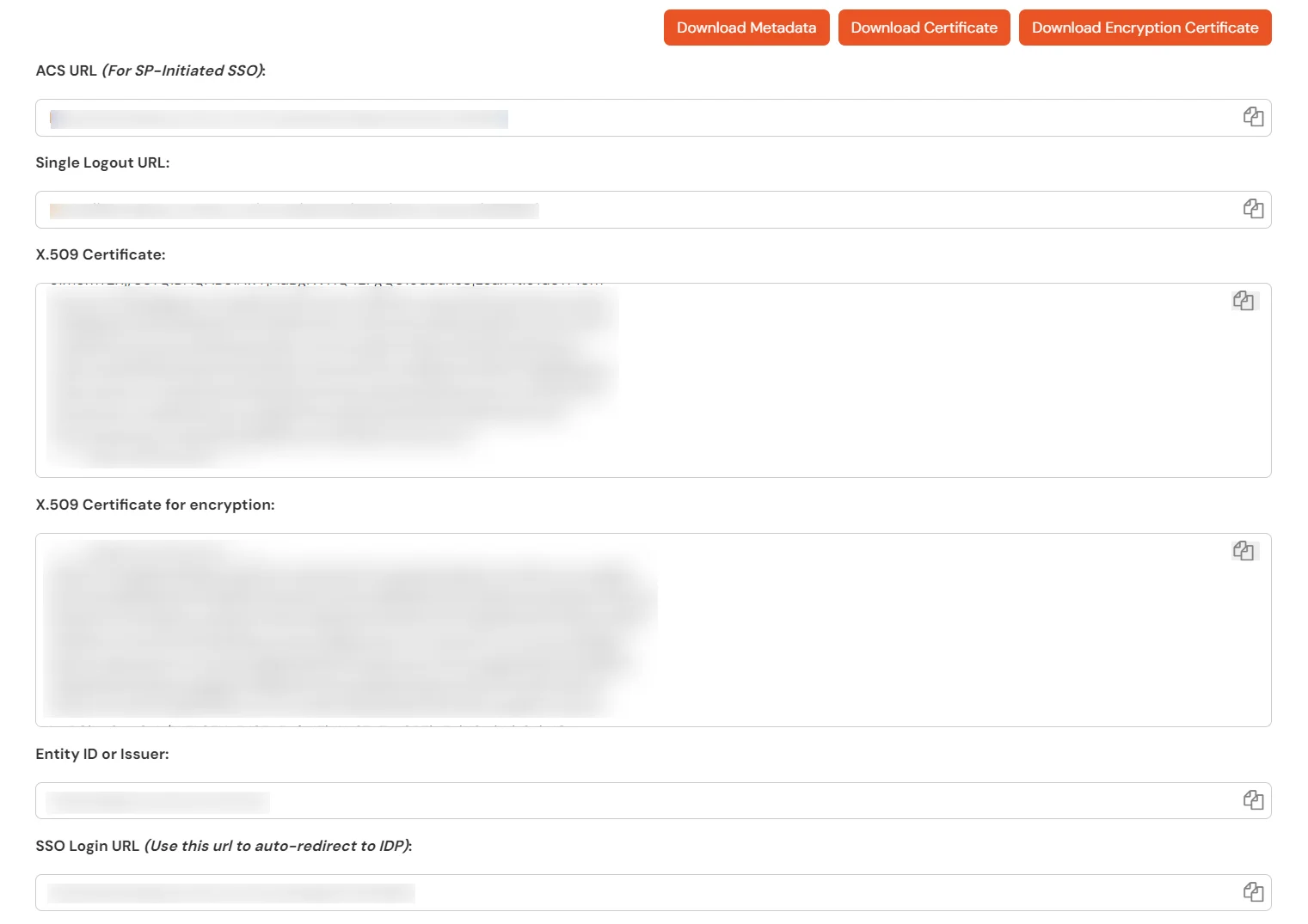
| identifierUris | Place Your Entity ID or Issuer url |
| requestedAccessTokenVersion | 2 |
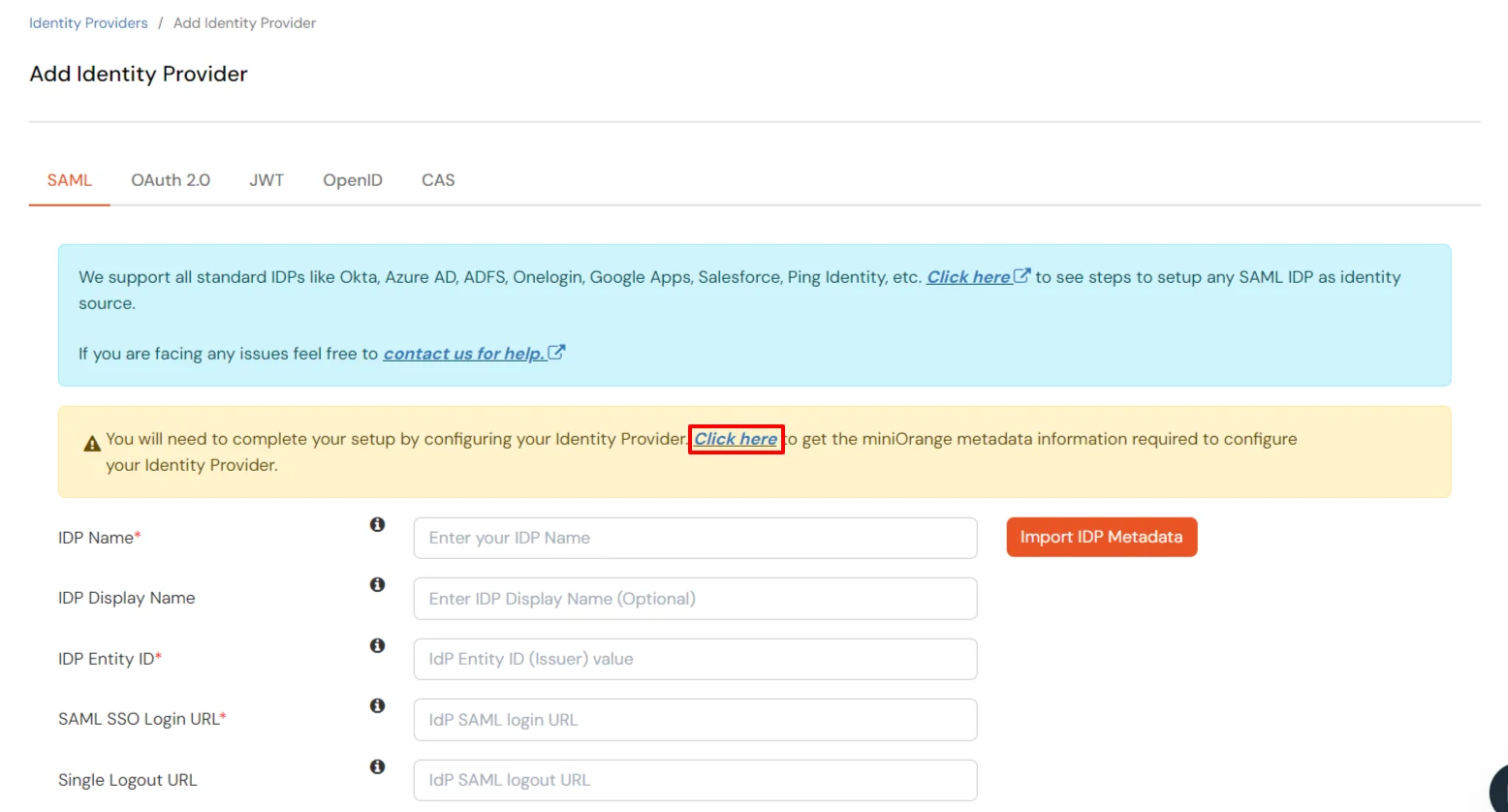
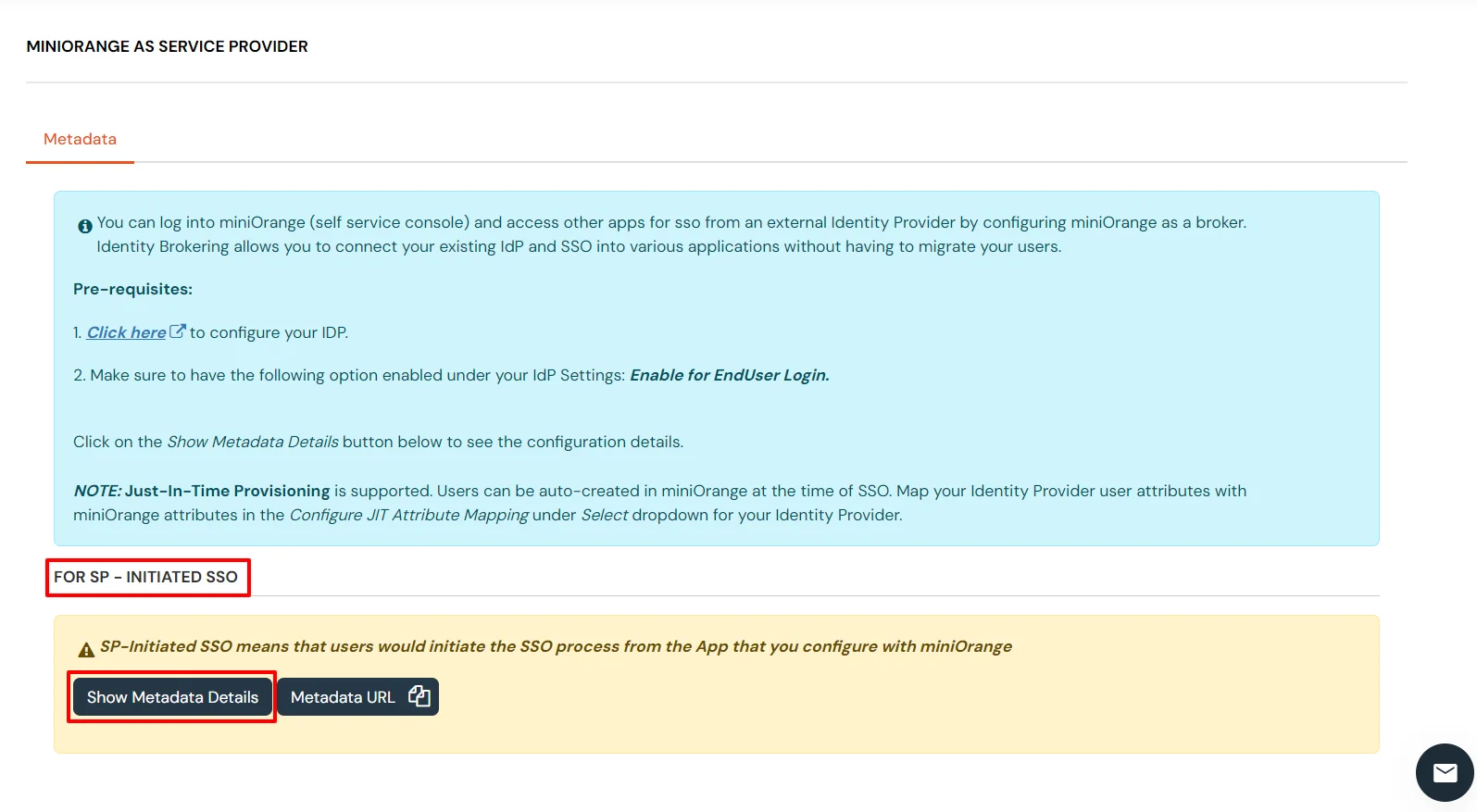
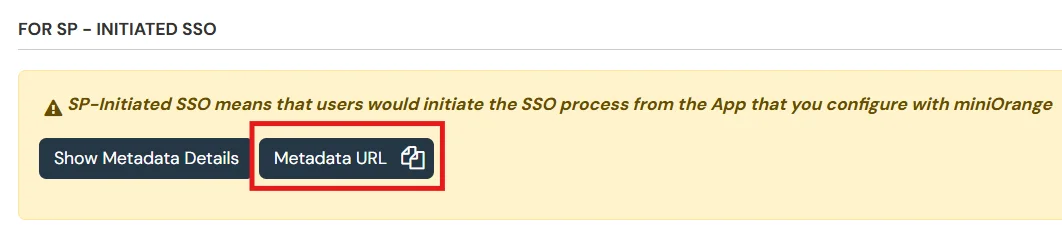
| samlMetadataUrl | Place your For SP - Initiated SSO metadata URL here |

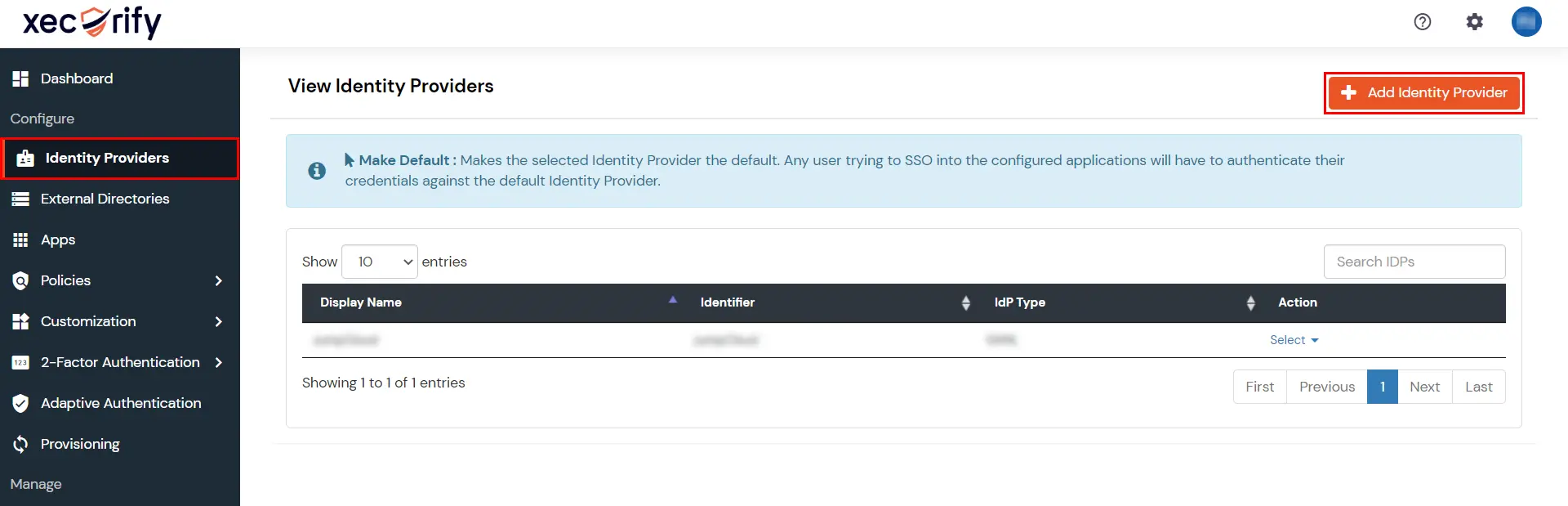

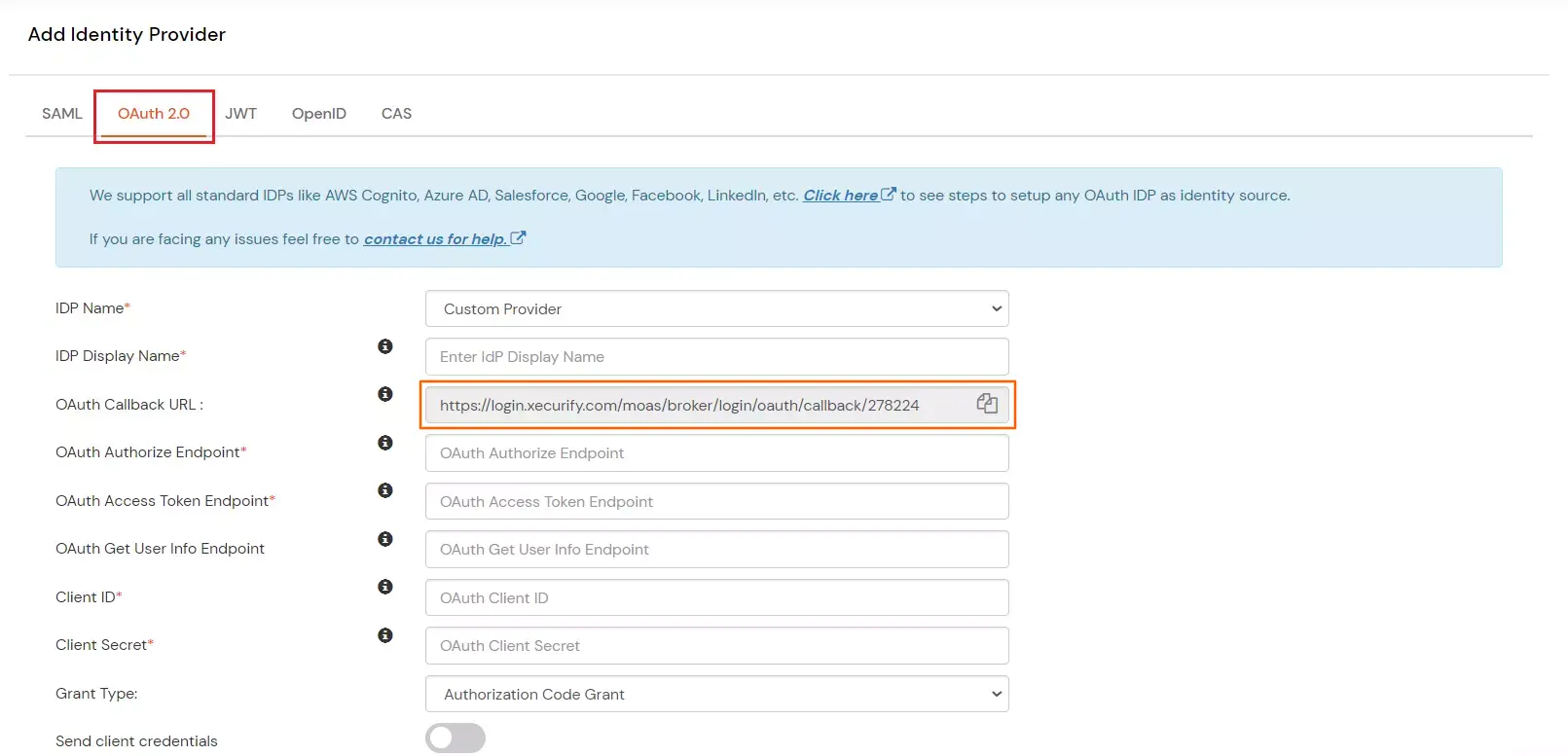
| IdP Display Name | Choose appropriate Name |
| OAuth Authorize Endpoint | From step 2 | OAuth Access Token Endpoint | From step 2 |
| Client ID | From step 1 |
| Client secret | From step 1 |
| Scope | openid email profile |
You can follow this guide, if you want to configure SAML/WS-FED, OAuth/OIDC, JWT, Radius etc
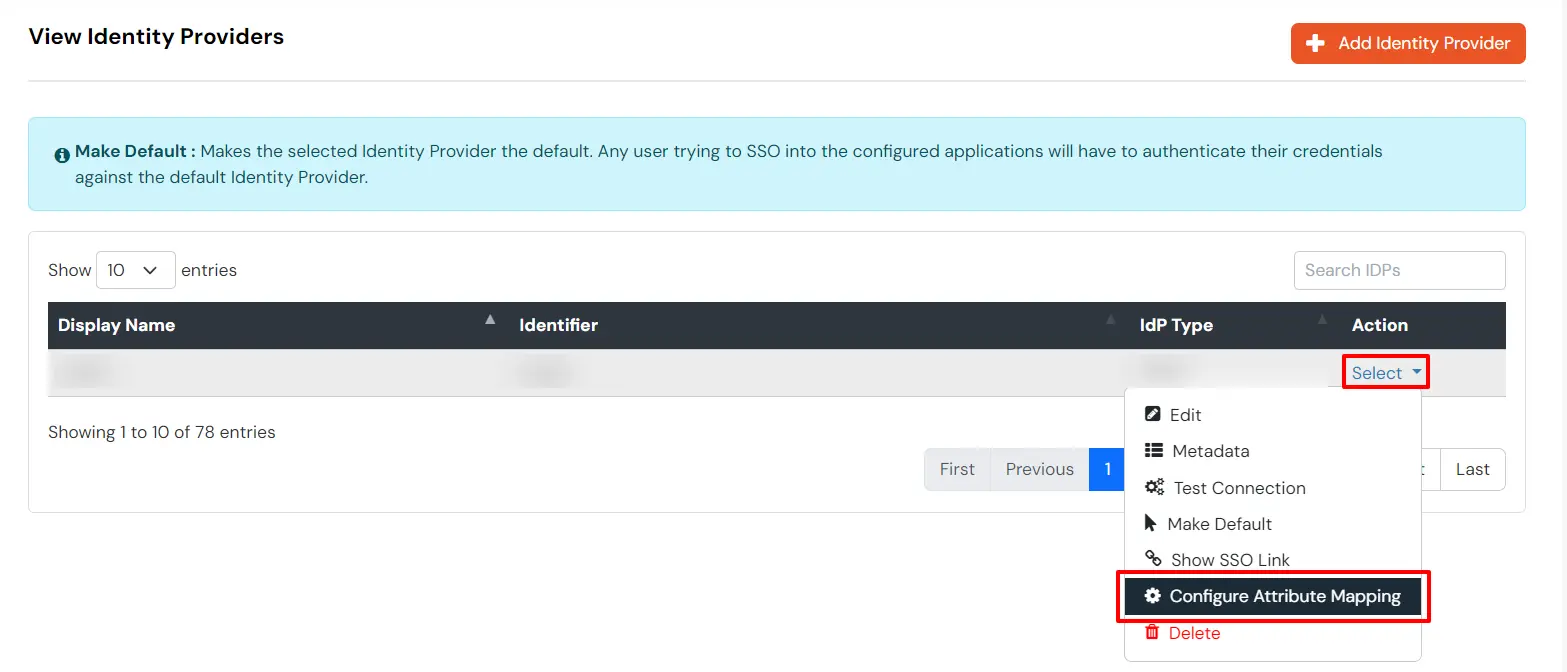
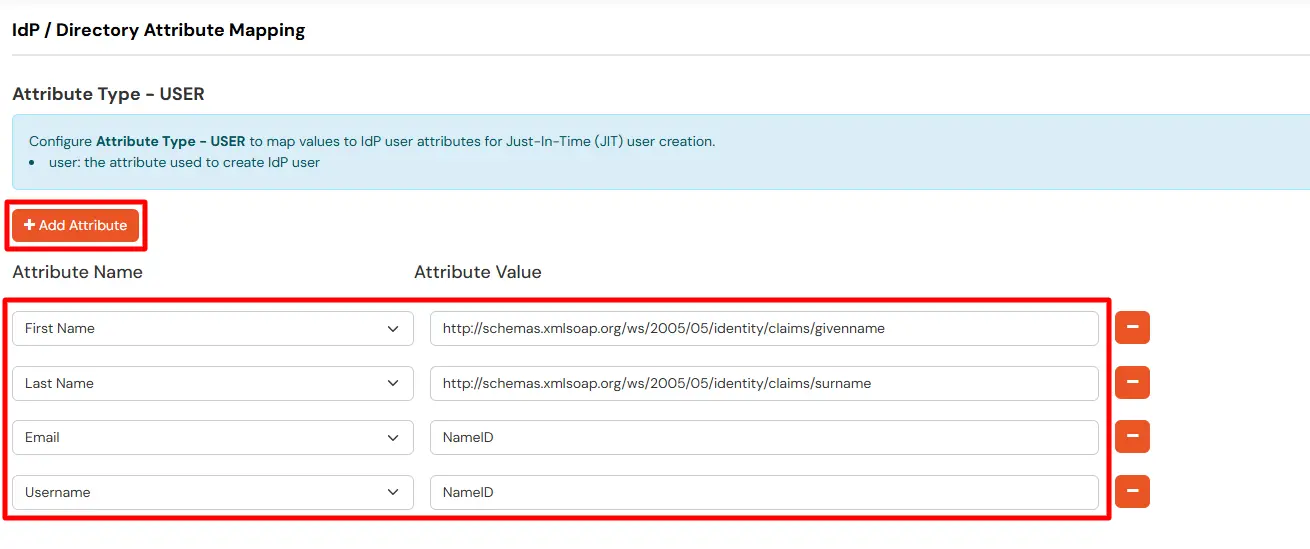
Maps information, such as email and username, during Just-In-Time (JIT) user creation. Email and Username attributes are necessary to create the user profile.
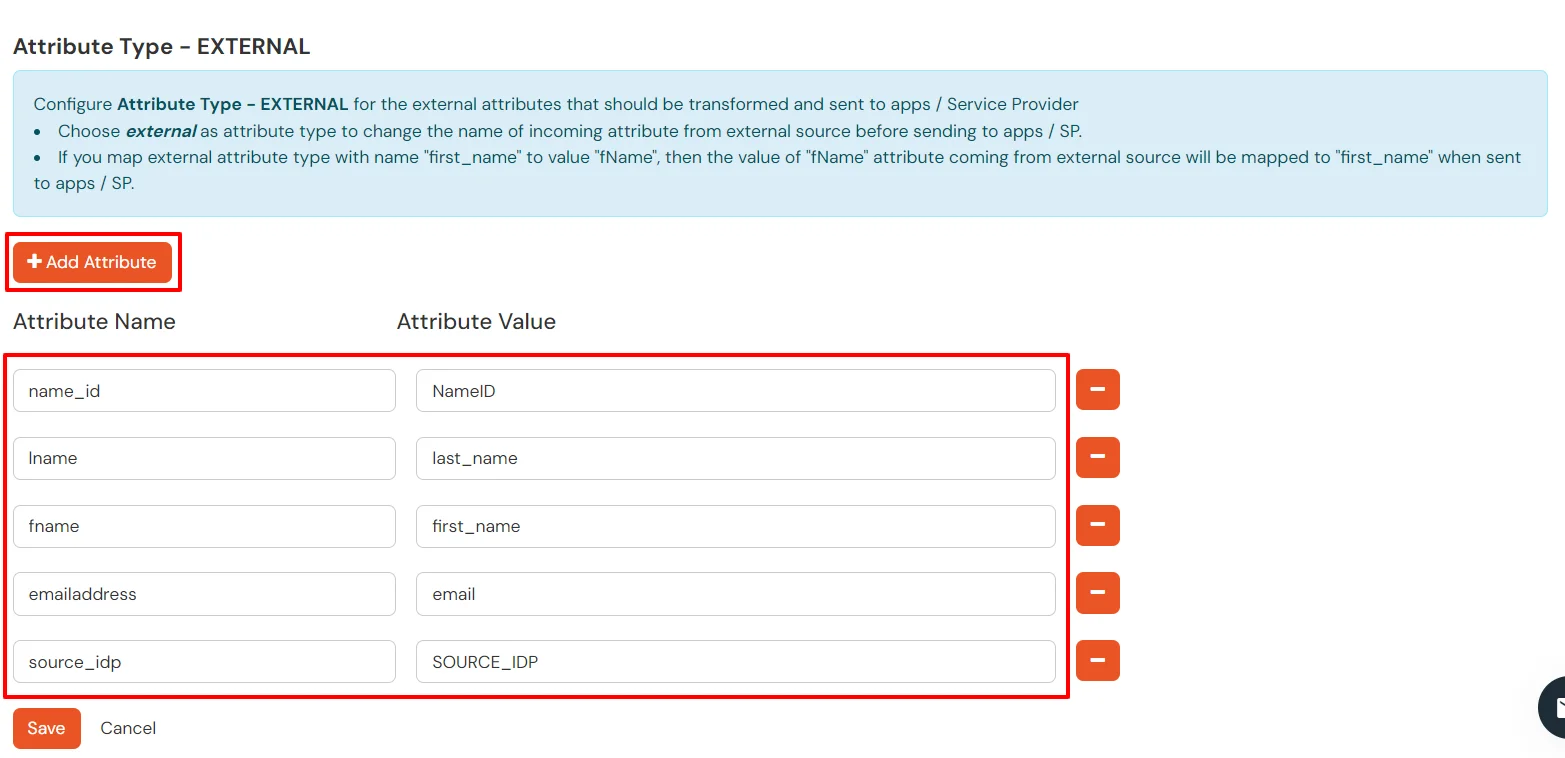
EXTERNAL mappings help alter incoming attribute names before sending them to apps, ensuring that the data is in the correct format.
You can follow this guide, if you want to configure multiple IDPs (Identity Providers) and give users the option to select the IDP of their choice to authenticate with.