Ecwid Single Sign-On (SSO)
Ecwid SSO by miniOrange is a cloud-based Single Sign-On solution for Ecwid that allows Organization's or users to use same login credentials that they use cross there services and sites in order to access Ecwid account. Along with Ecwid, miniOrange also provides secure SSO access to other integrated apps configured with Ecwid. miniOrange Ecwid SSO can be easily configured with any of the Directory like Active Directory, LDAP or any of your directory in the cloud. Ecwid SSO solution helps you to integrate with any IDP (Identity Provider) of your choice ADFS, Azure AD, Okta, Onelogin, AWS Cognito, GSuite/Google Apps etc.
Challenge faced by Ecwid Users
Ecwid users want a continuous and seamless access to their portal through their existing accounts. They don't wish for their users to have a separate set of credentials for logging in to Ecwid. Ecwid provides a way for its users to allow their users to log in to the platform seamlessly. But, an interface needs to be created which would allow this.
SSO Solution for Ecwid
miniOrange provides an integrated SSO solution where a logged in user's existing session can be used to log the users into
Ecwid by creating a valid JSON Web Token ( JWT ). Ecwid user is relieved from maintaining separate user credentials
for its users.
As a result, miniOrange Single Sign-On (SSO) solution is implemented. Ecwid users can now login into Ecwid platform using their existing credentials.
Prerequisites
Please make sure your organisation branding is already set under Customization >> Login and Registration Branding in the left menu of the dashboard.
Connect with External Source of Users
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
Follow the Step-by-Step Guide given below for Ecwid Single Sign-On (SSO)
1. Configure Ecwid in miniOrange
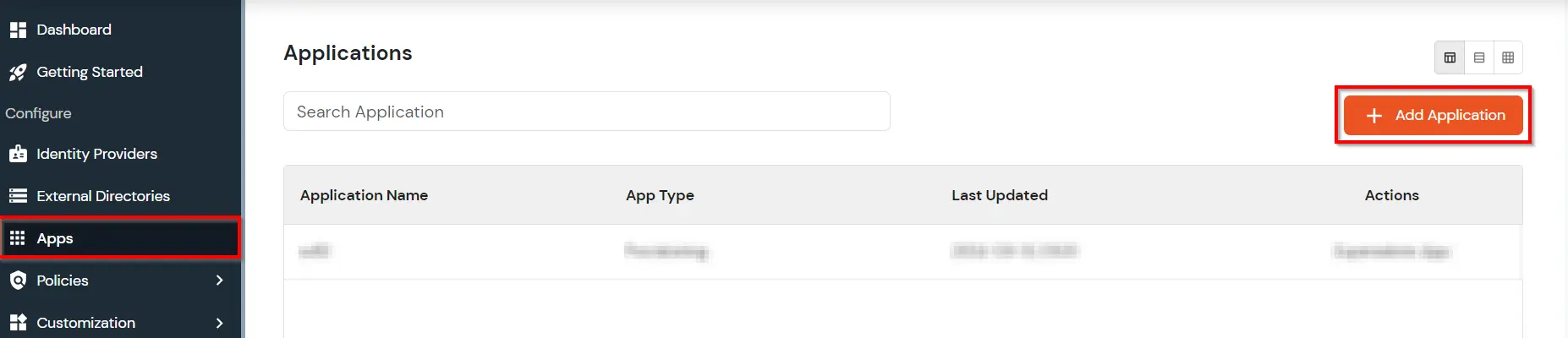
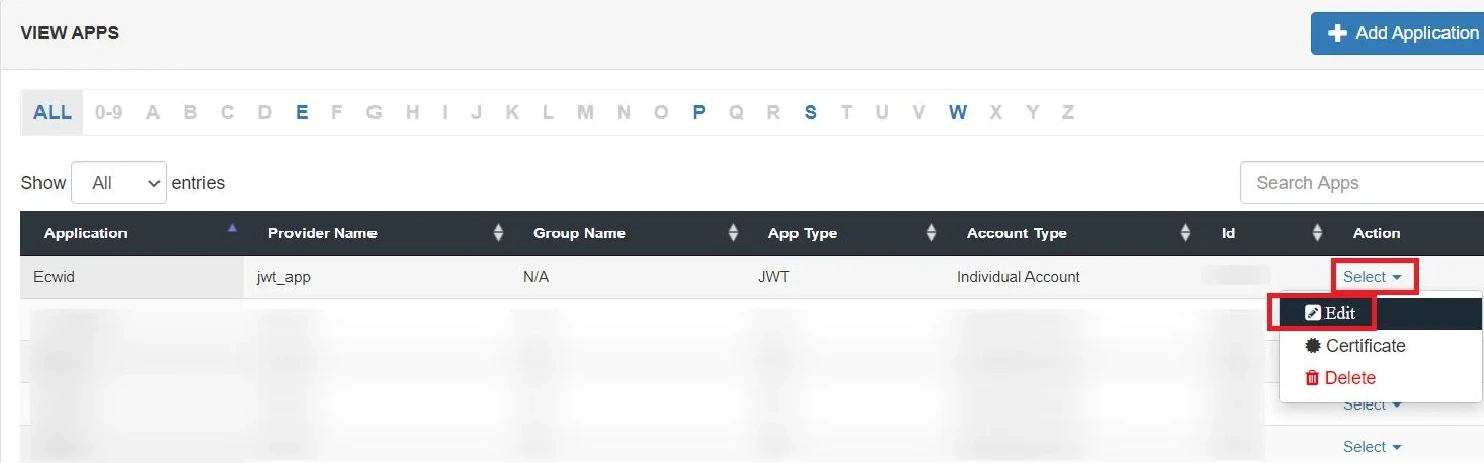
- Go to Apps and click on Add Application button.
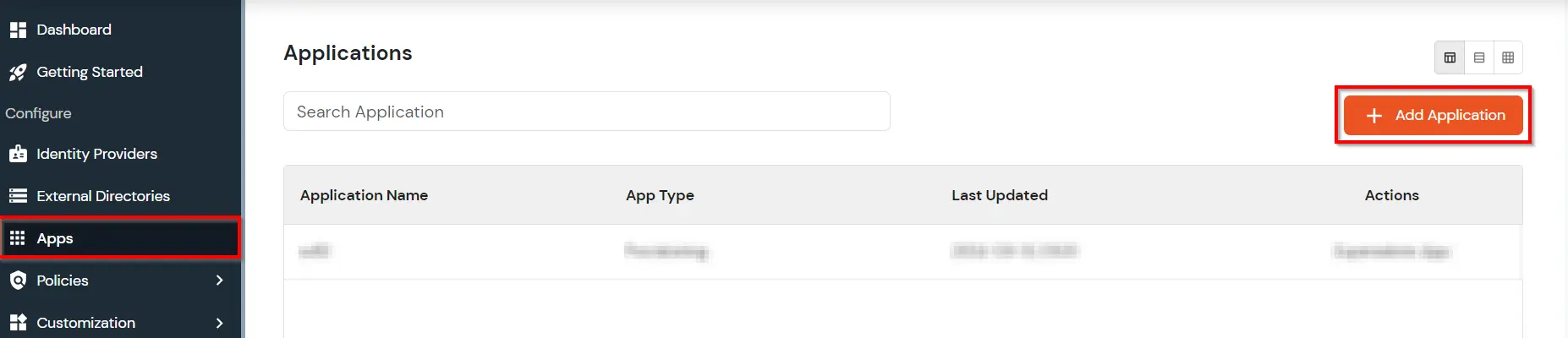
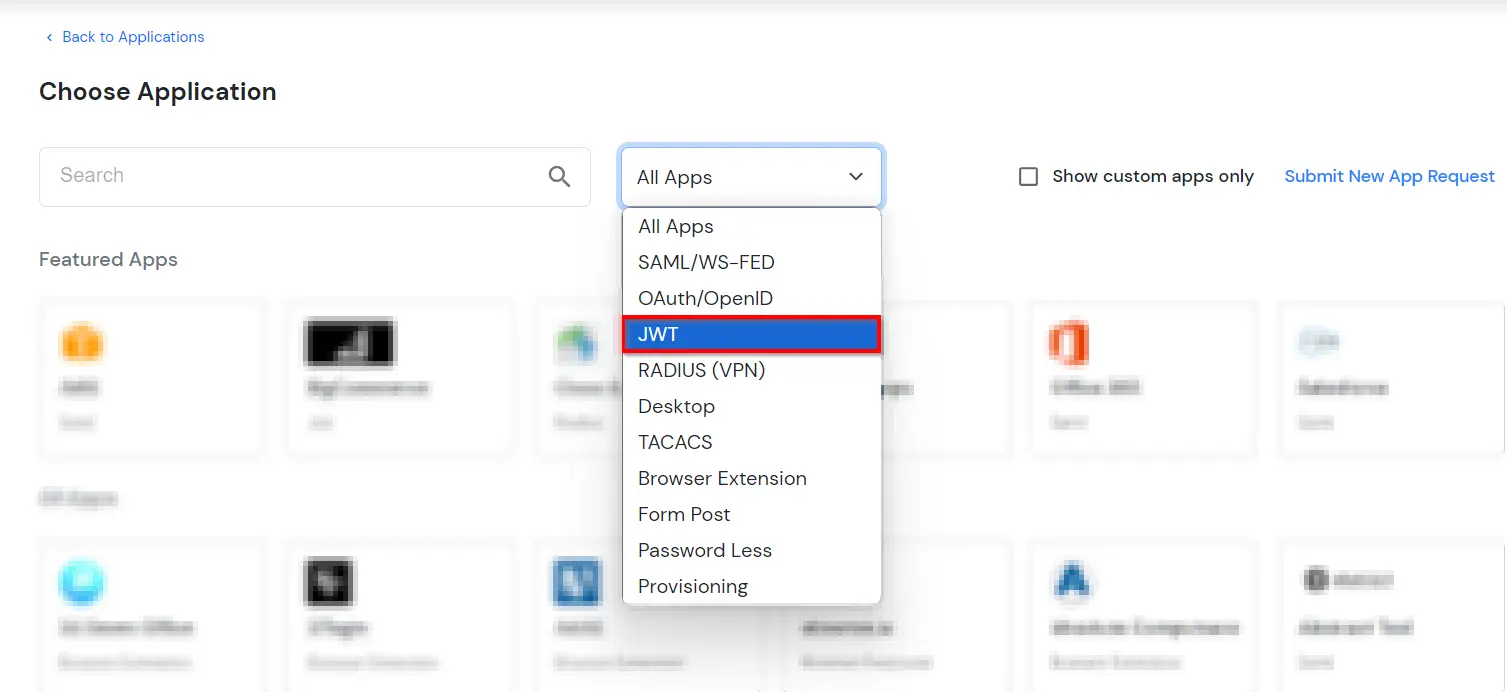
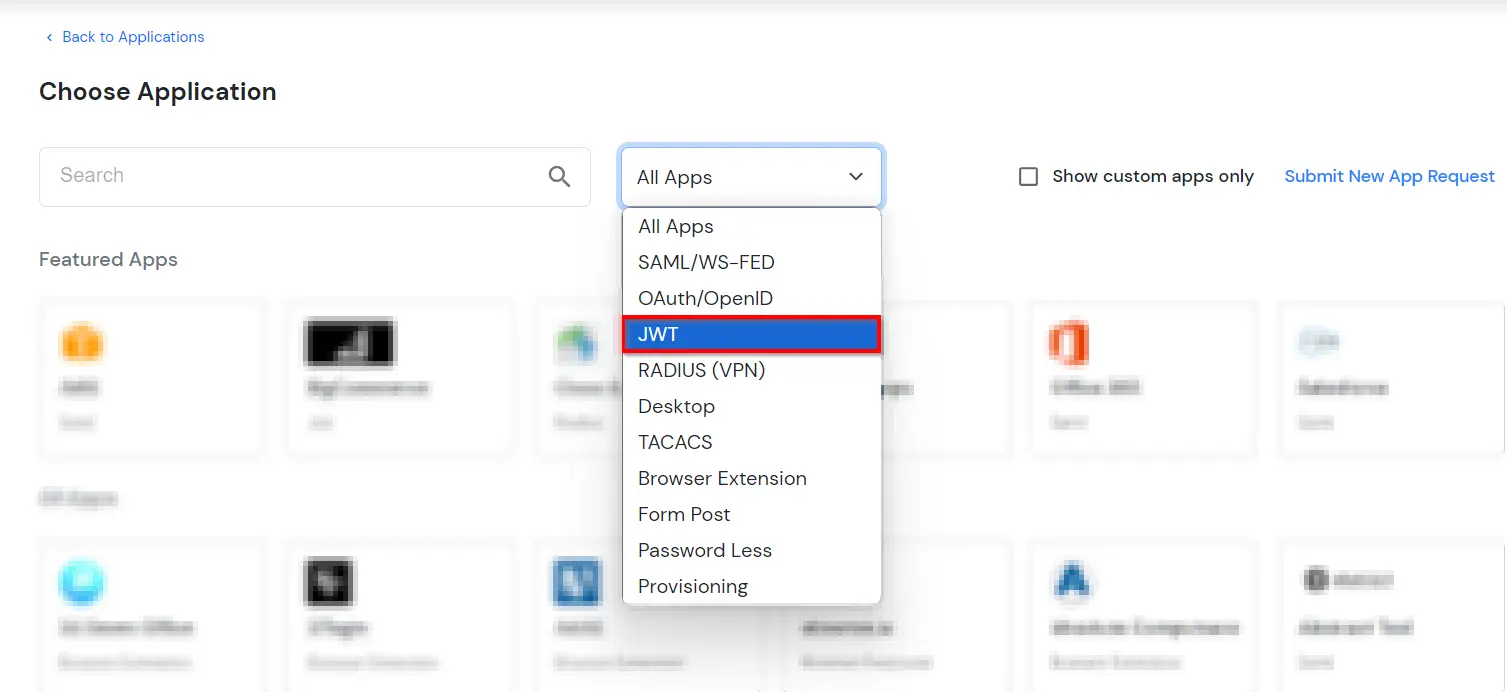
- In Choose Application, select JWT from the application type dropdown.
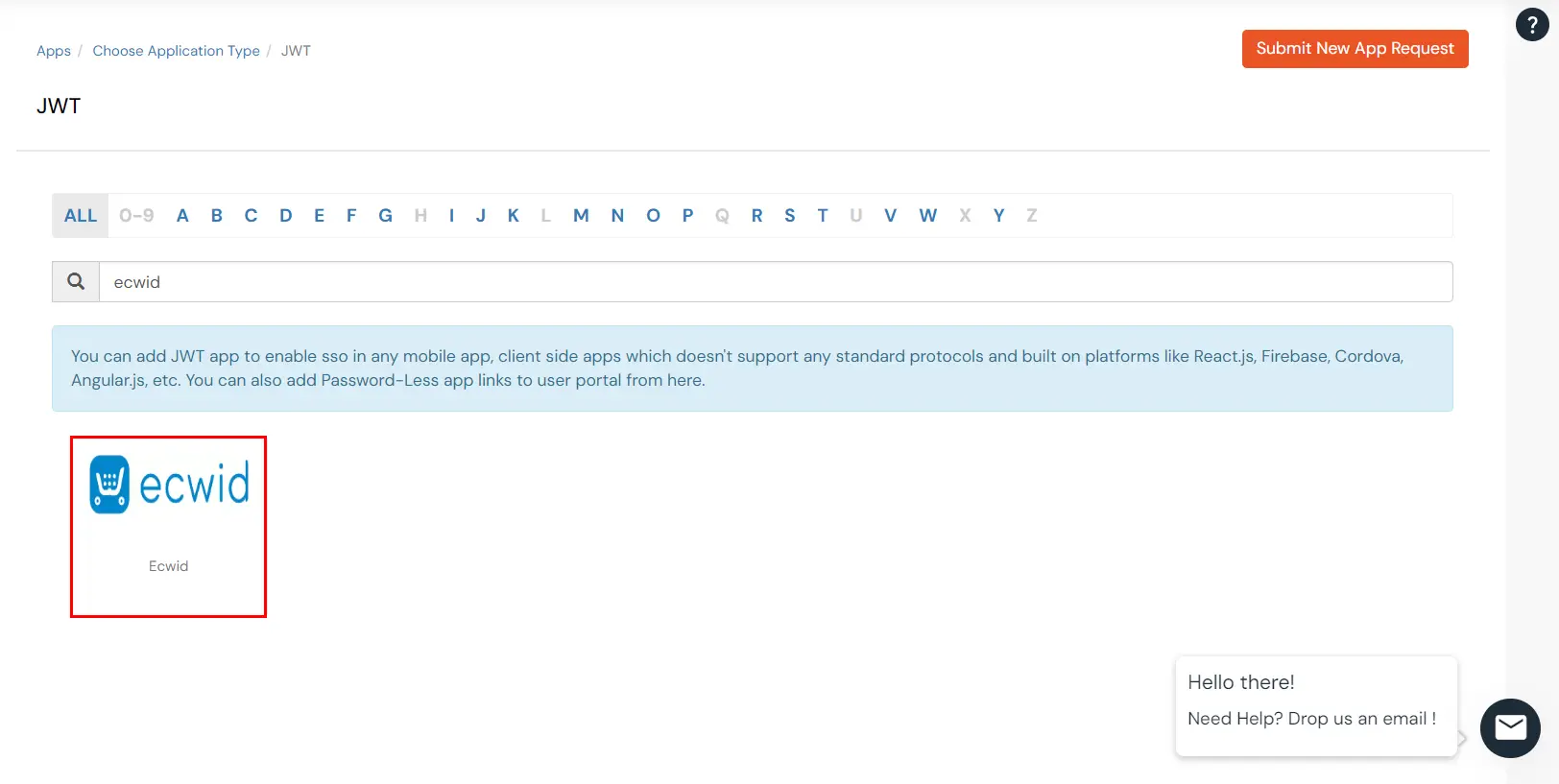
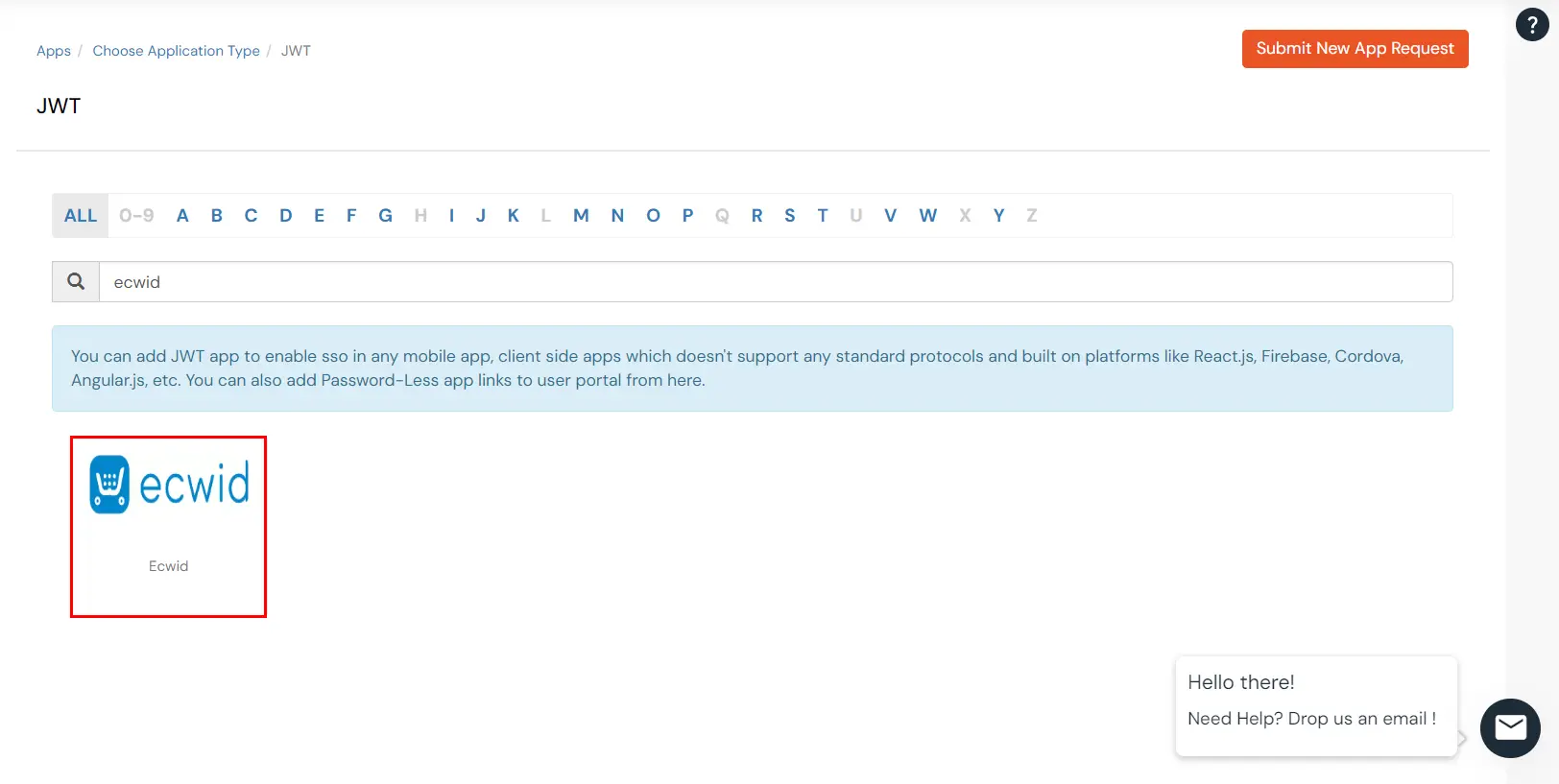
- In the next step, search for Ecwid application from the list. If your application is not found, search for JWT App and you can set up your Application.
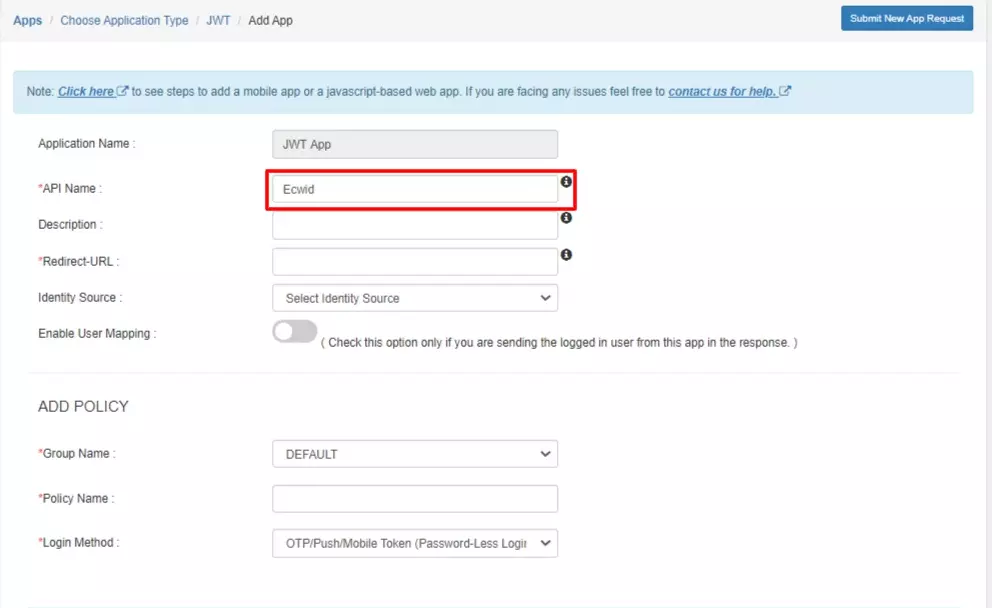
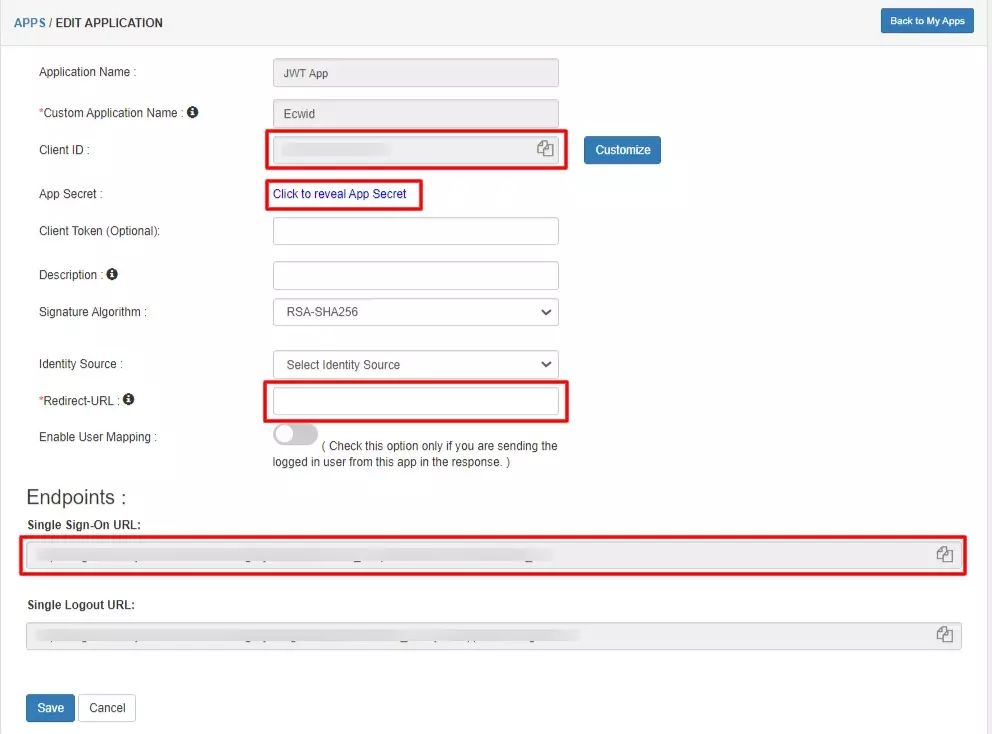
- You can configure the following details in the application:
| Custom App Name |
Enter the Application Name of your choice, and add a description if required. |
| Redirect-URL |
Enter the Redirect-URL (i.e. the endpoint where you want to send/post your JWT).
You can add multiple redirect URLs by separating them with a ‘;’. E.g. abc.com;xyz.com |
| Primary Identity Provider (optional) |
Select your Identity Source from the dropdown. You can select miniOrange here as default IDP. |
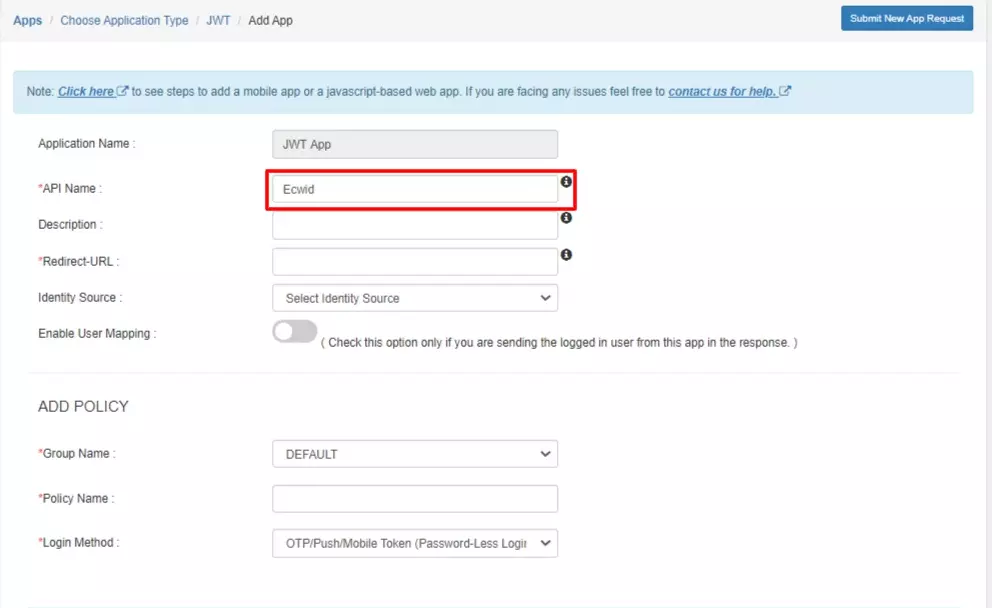
- Click on Save to complete the configuration.
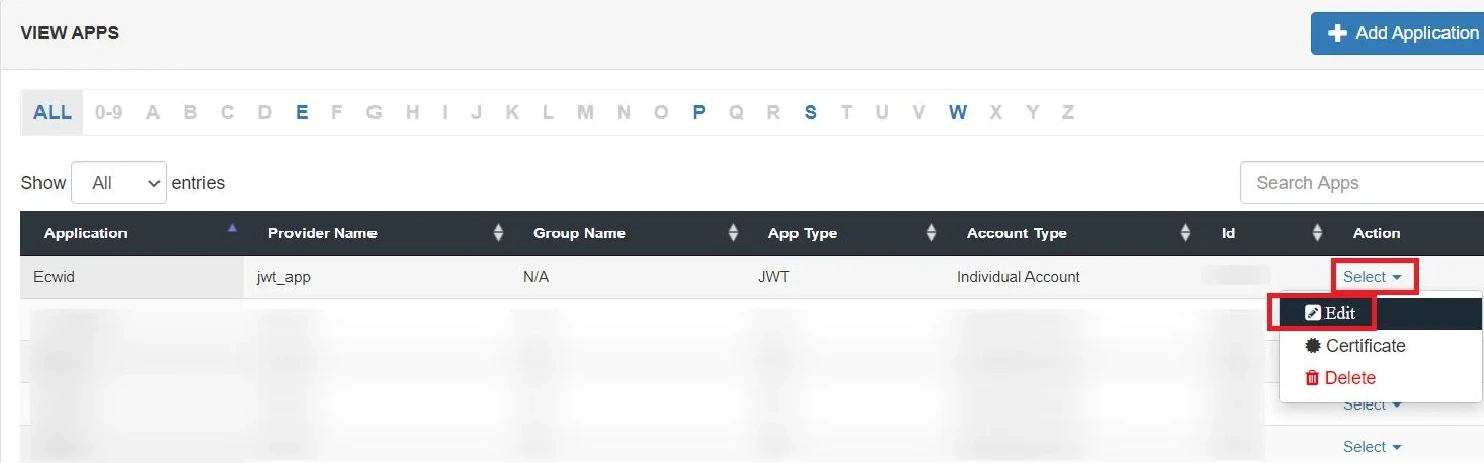
- Click on Edit in the ' ' icon against your app.
- You can get further details about your recently added JWT application:
| Client ID |
If your application provides its own client ID, you can configure it by clicking on the Customize button. |
| App Secret |
You can find App Secret by clicking on the copy icon. This is used in the HS265 Signature algorithm for generating the signature. |
| Signature Algorithm |
Select RSA-SHA256 as your signature algorithm from the dropdown. |
| Primary Identity Provider |
Select the default Identity Provider from the dropdown for the application. If not selected, users will see the screen of default IdP (miniOrange) |
| Redirect URL |
Enter your app’s URL here (This is the URL where you will receive your JWT.)
<app-login-url>/?id_token=<token>
eg: https://localhost:3000/home/?id_token=eyefb43bf.whfeeg.hfwf
In this example, https://localhost:3000/home is my app’s URL where id_token will be posted after authentication.
|
- Scroll down to Endpoints.
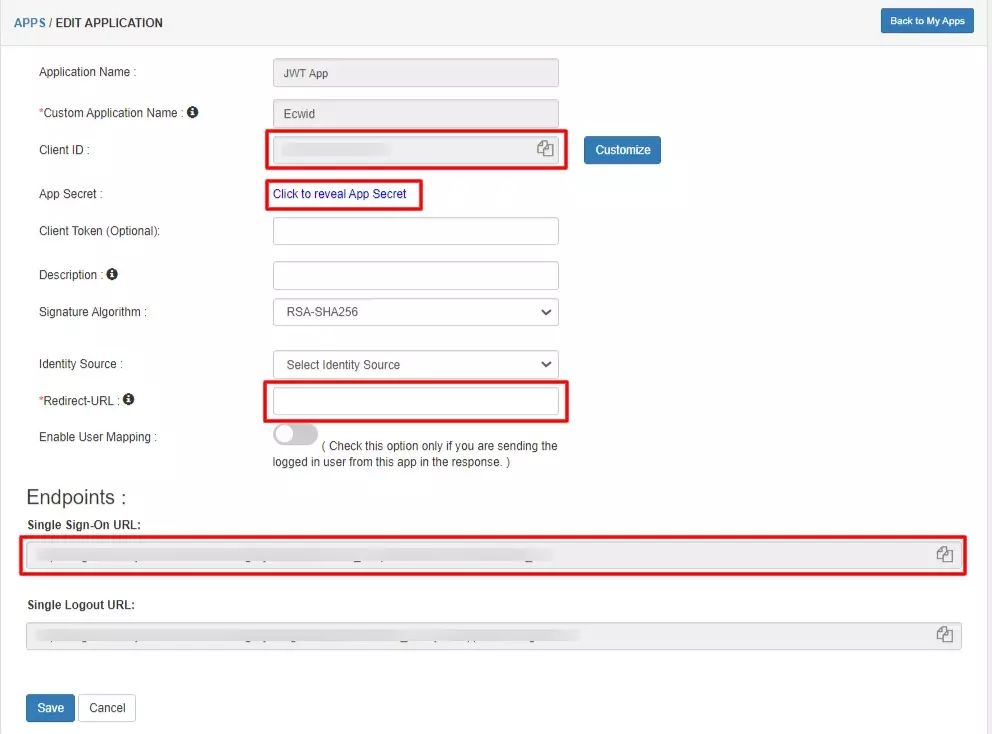
- SSO URL for using miniOrange as Authentication Source: If you are going to store users in miniOrange and use miniOrange as your authentication source,then, copy and save this URL somewhere as it will be used in further steps.
- SSO URL for using External Providers as Authentication Source: If you are going to use any External Provider as your authentication source, then, Copy this one and save somewhere as it will be used in further step.
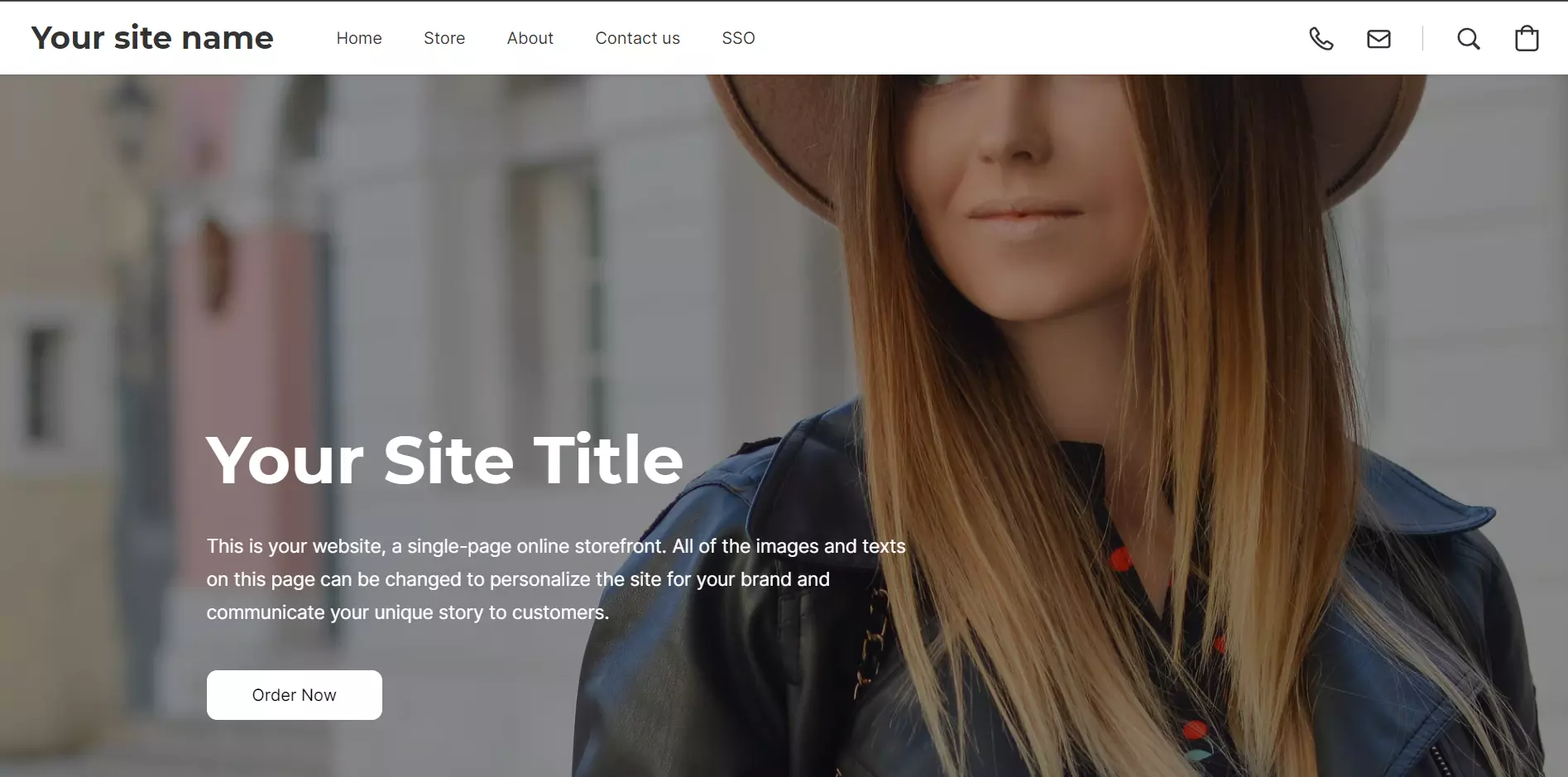
2. Adding Script on Ecwid's End
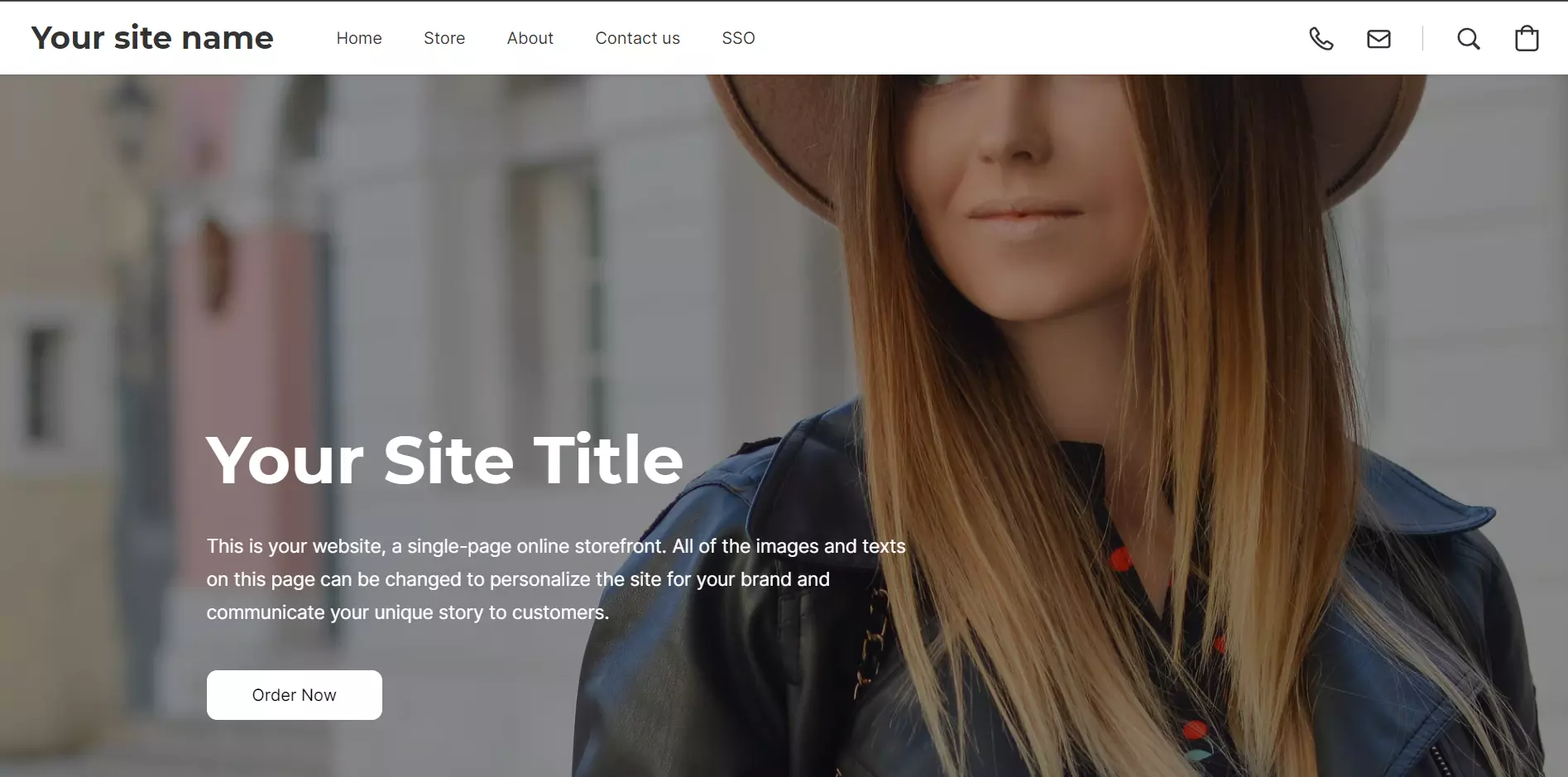
- To enable SSO on Ecwid's end, all you need to do is click on Install App to install miniOrange SSO app.

- Please click here to contact us for the script which is to be added.
3. Configure Your User Directory
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
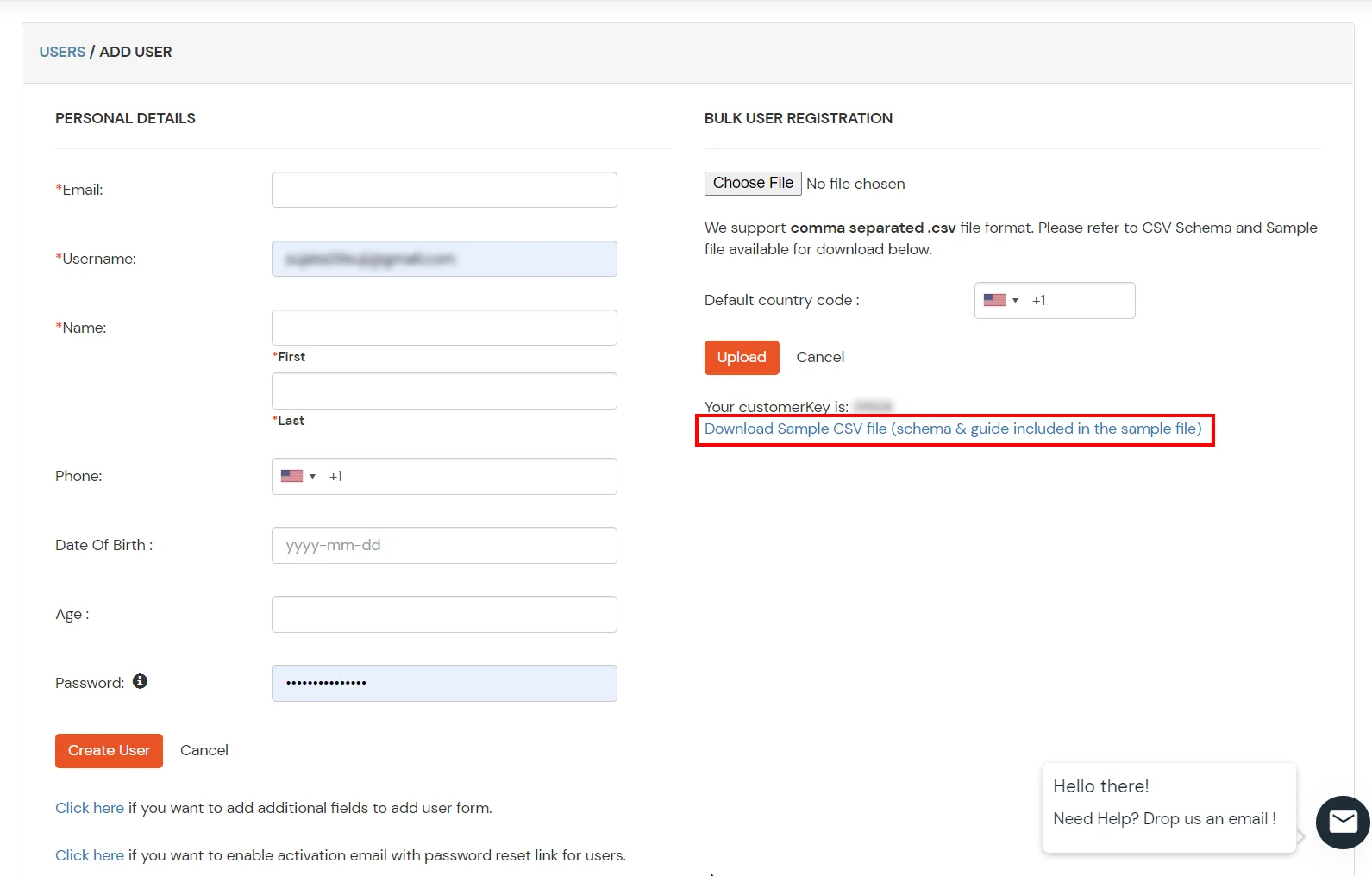
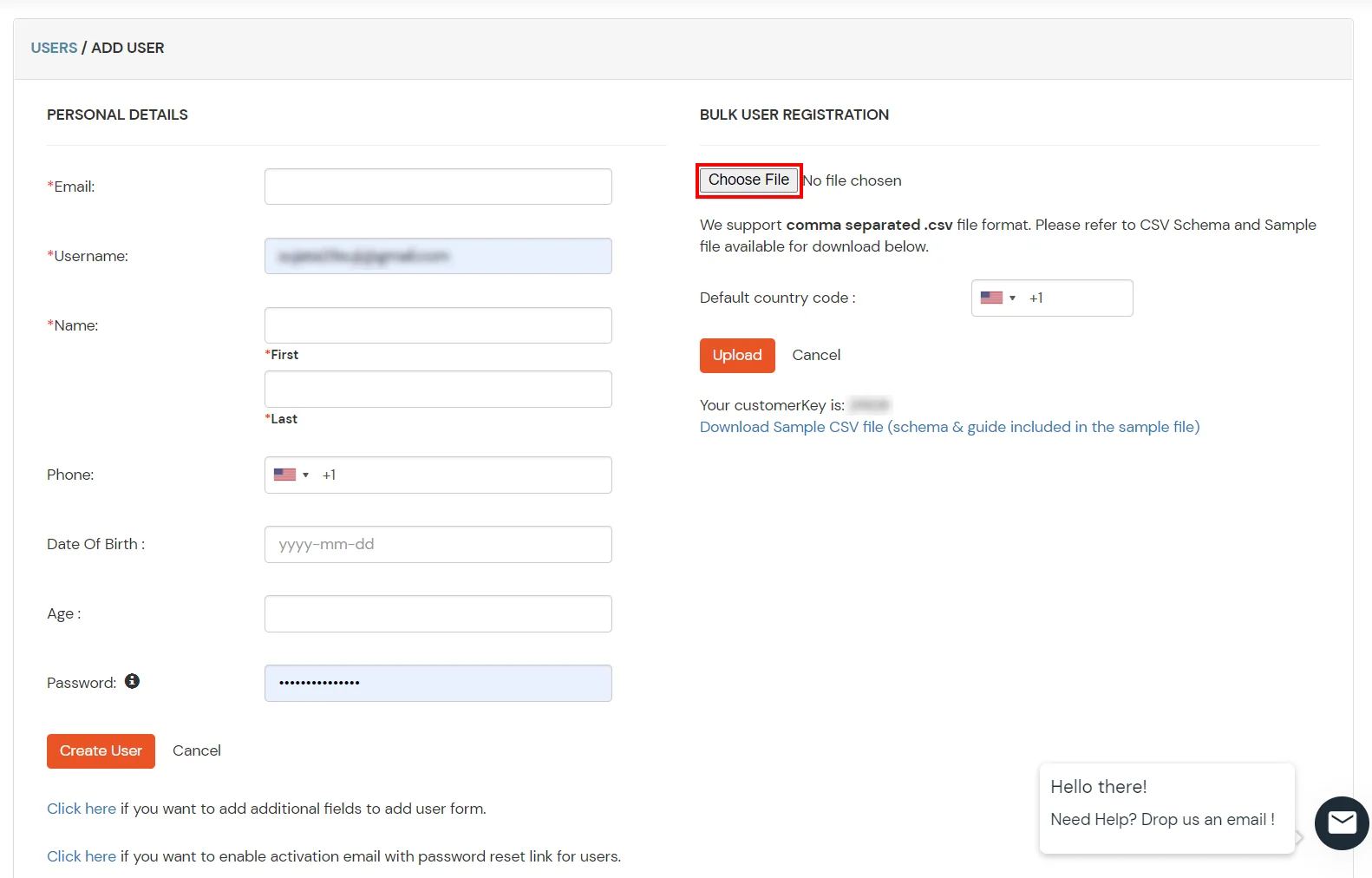
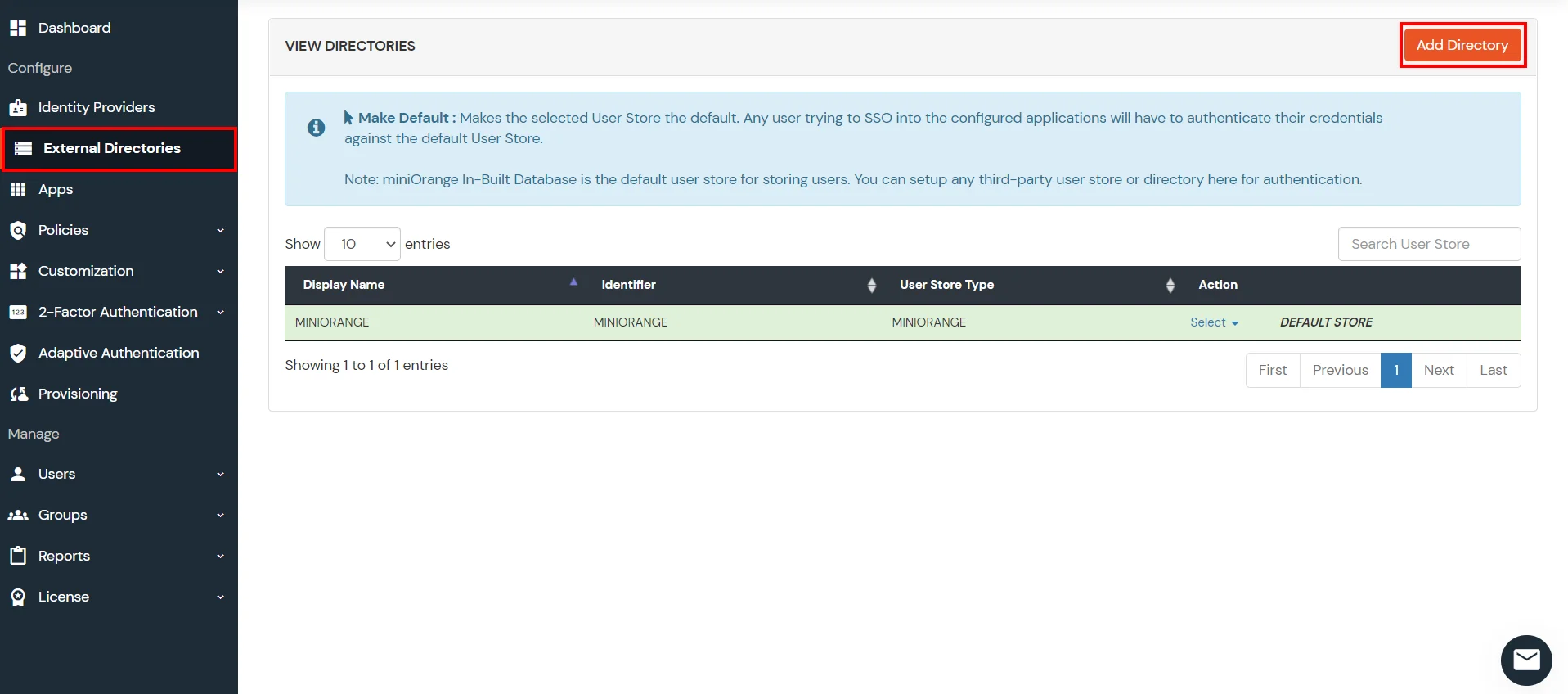
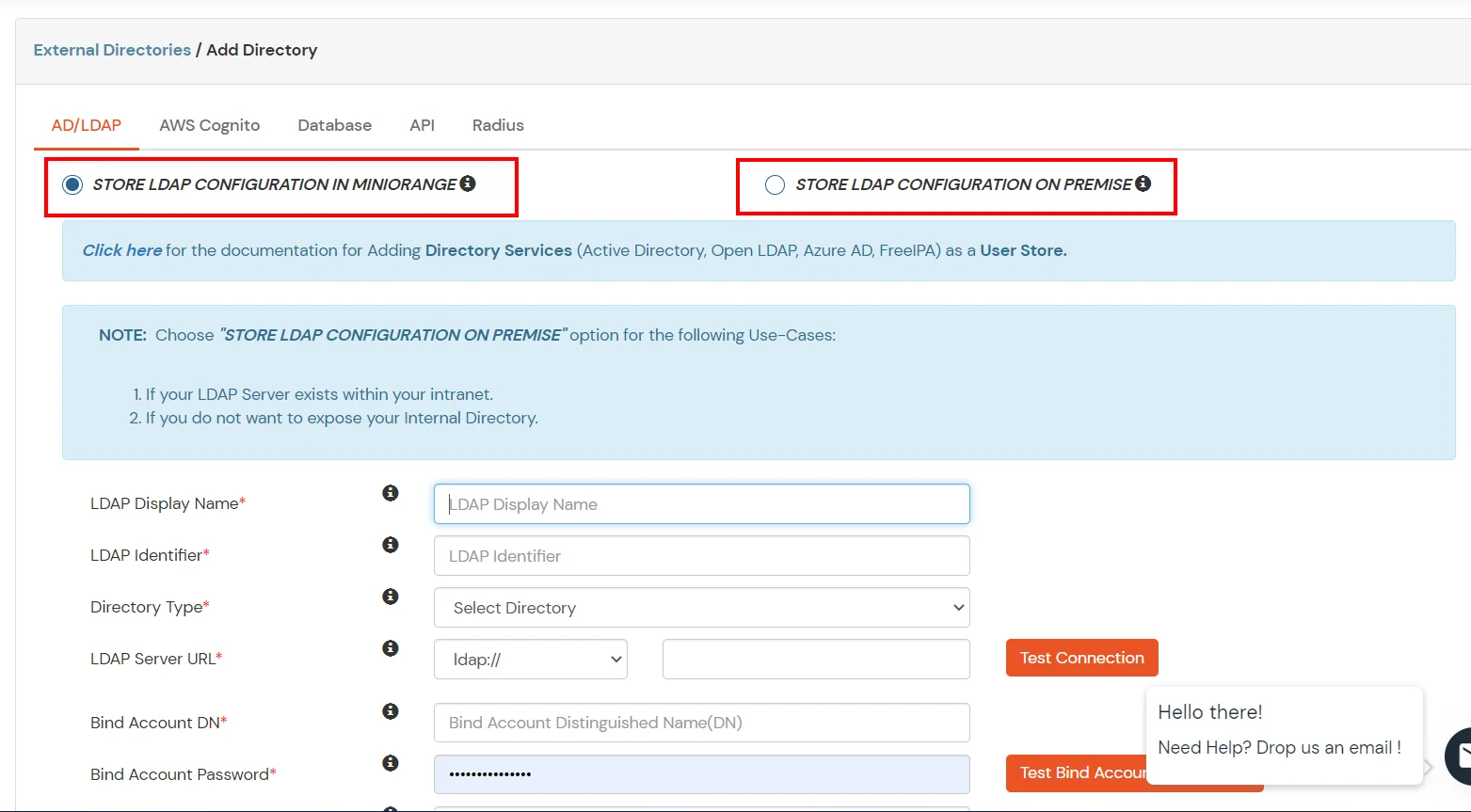
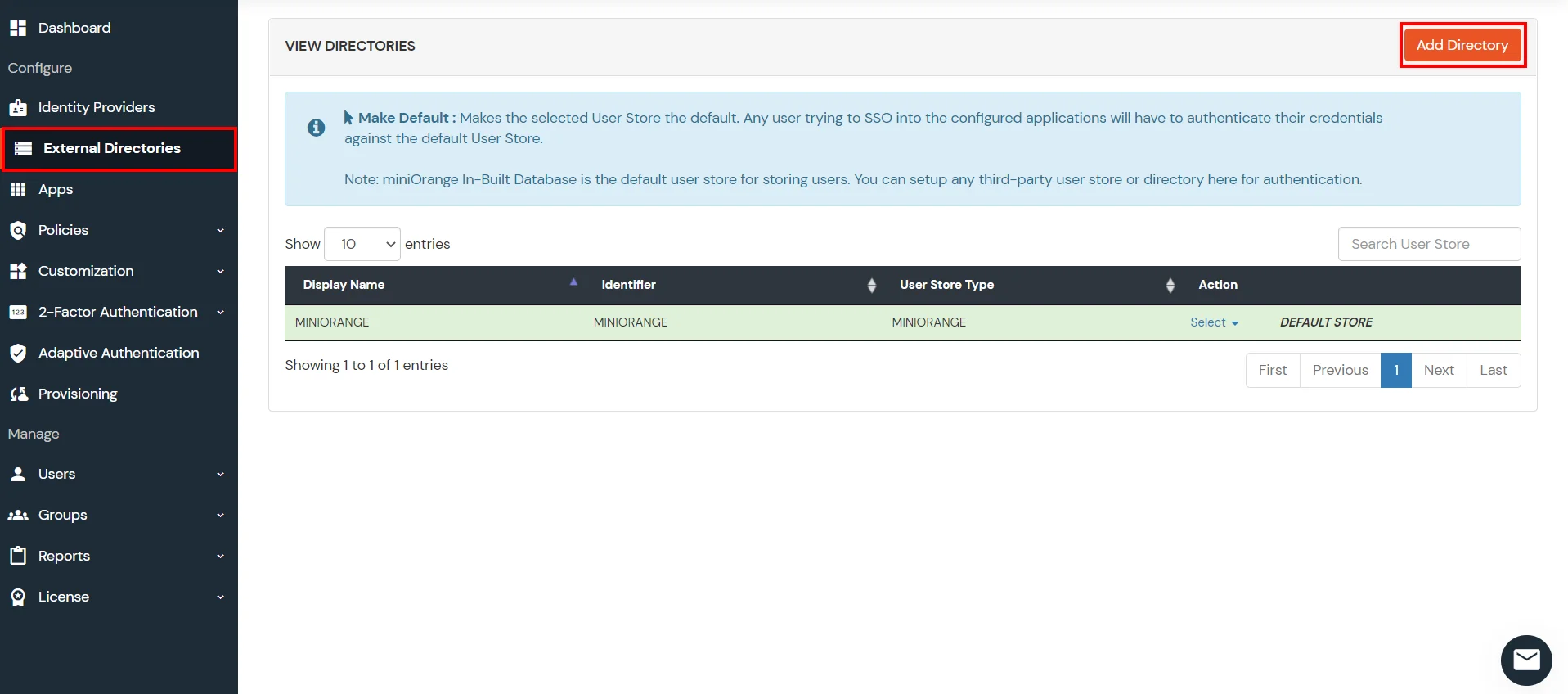
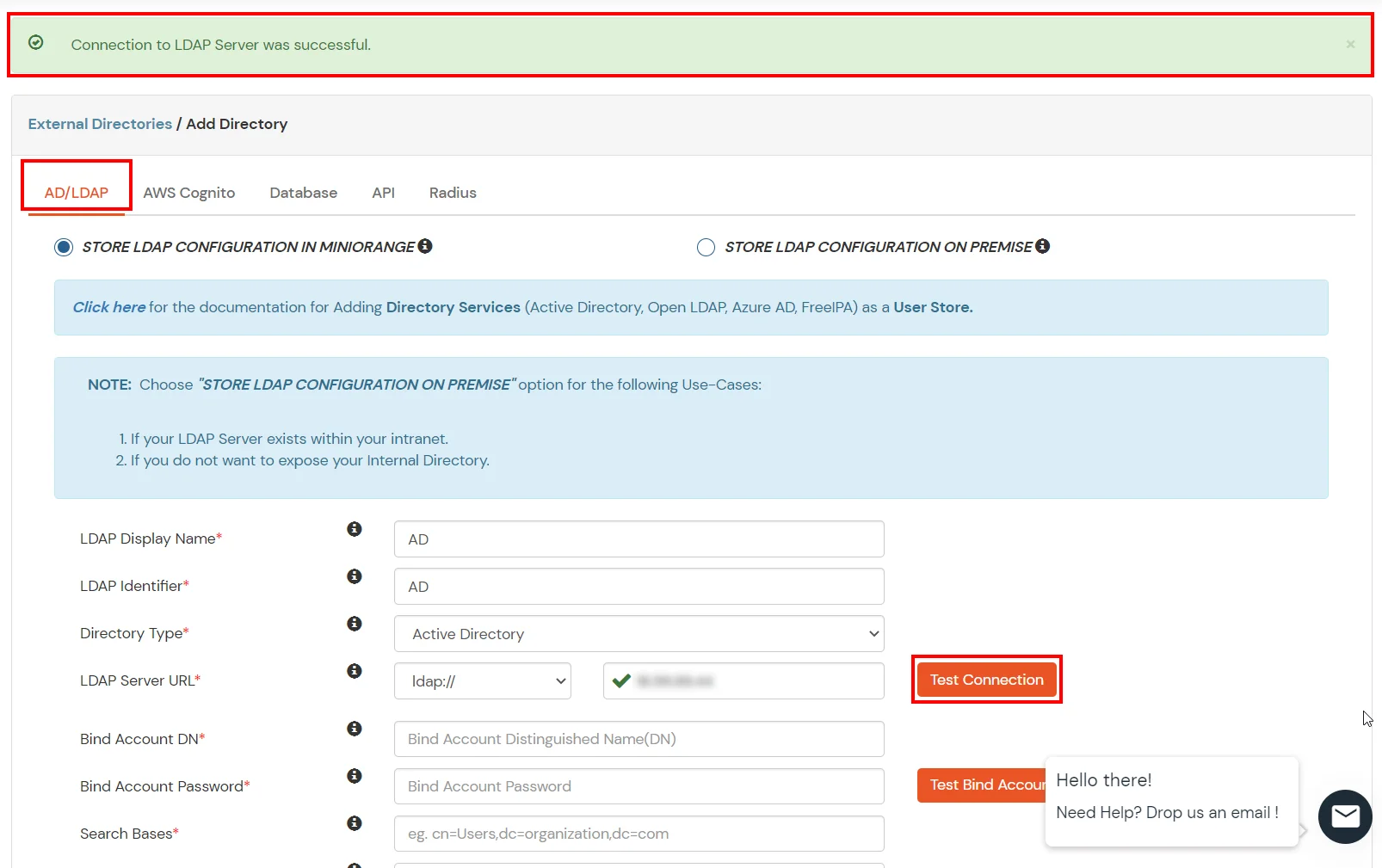
- Click on External Directories >> Add Directory in the left menu of the dashboard.
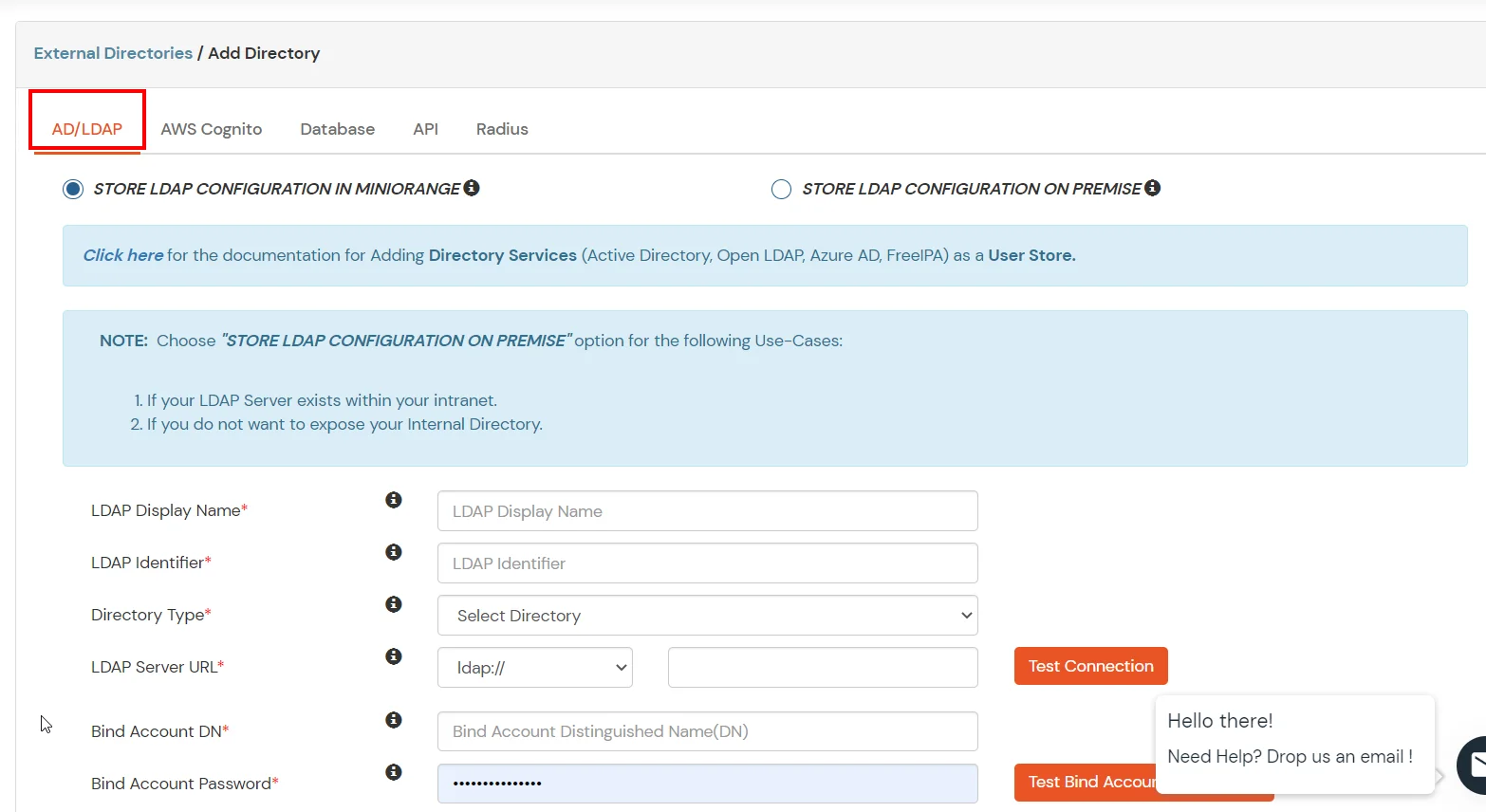
- Select Directory type as AD/LDAP.
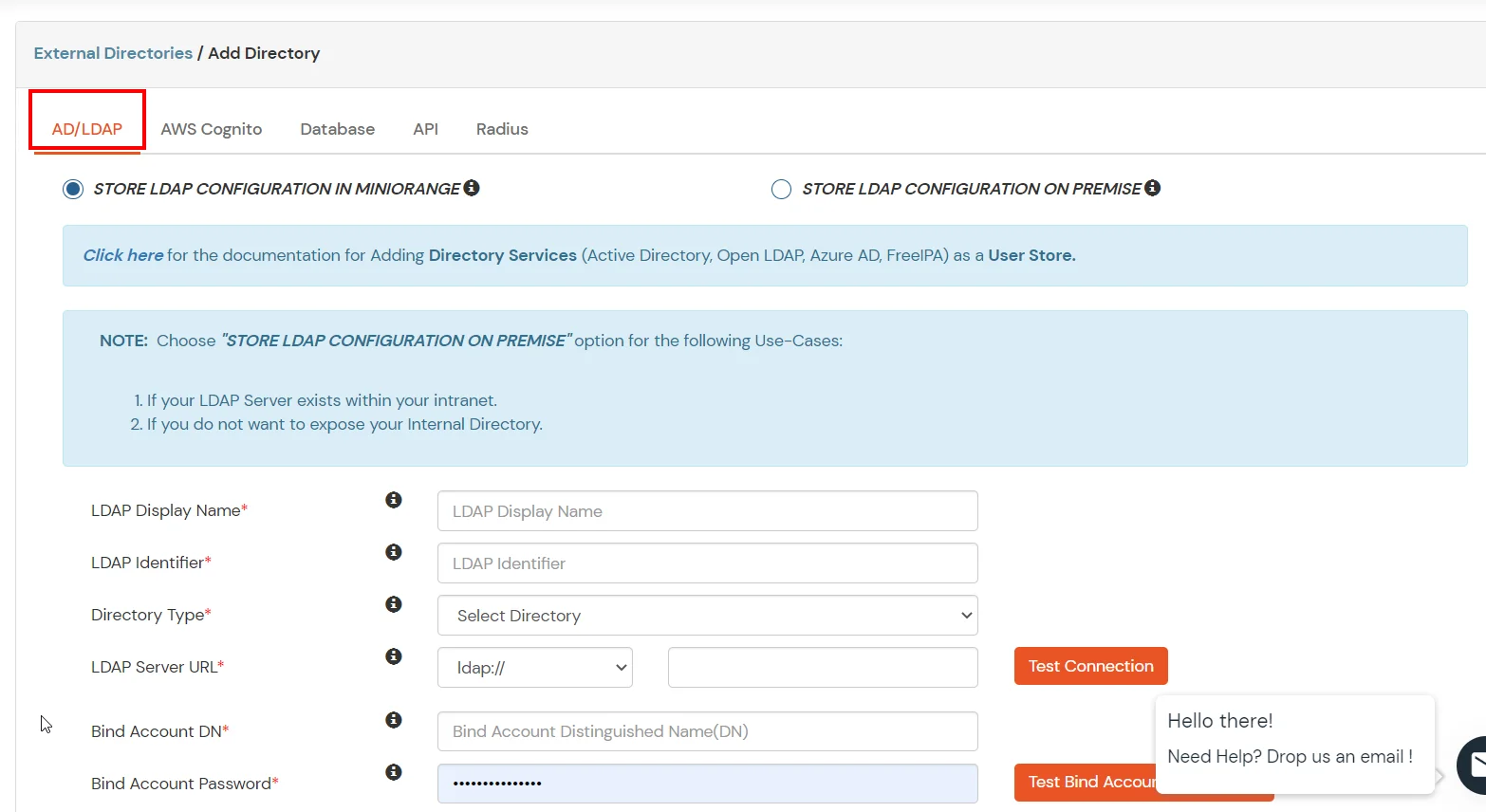
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway in your premise.
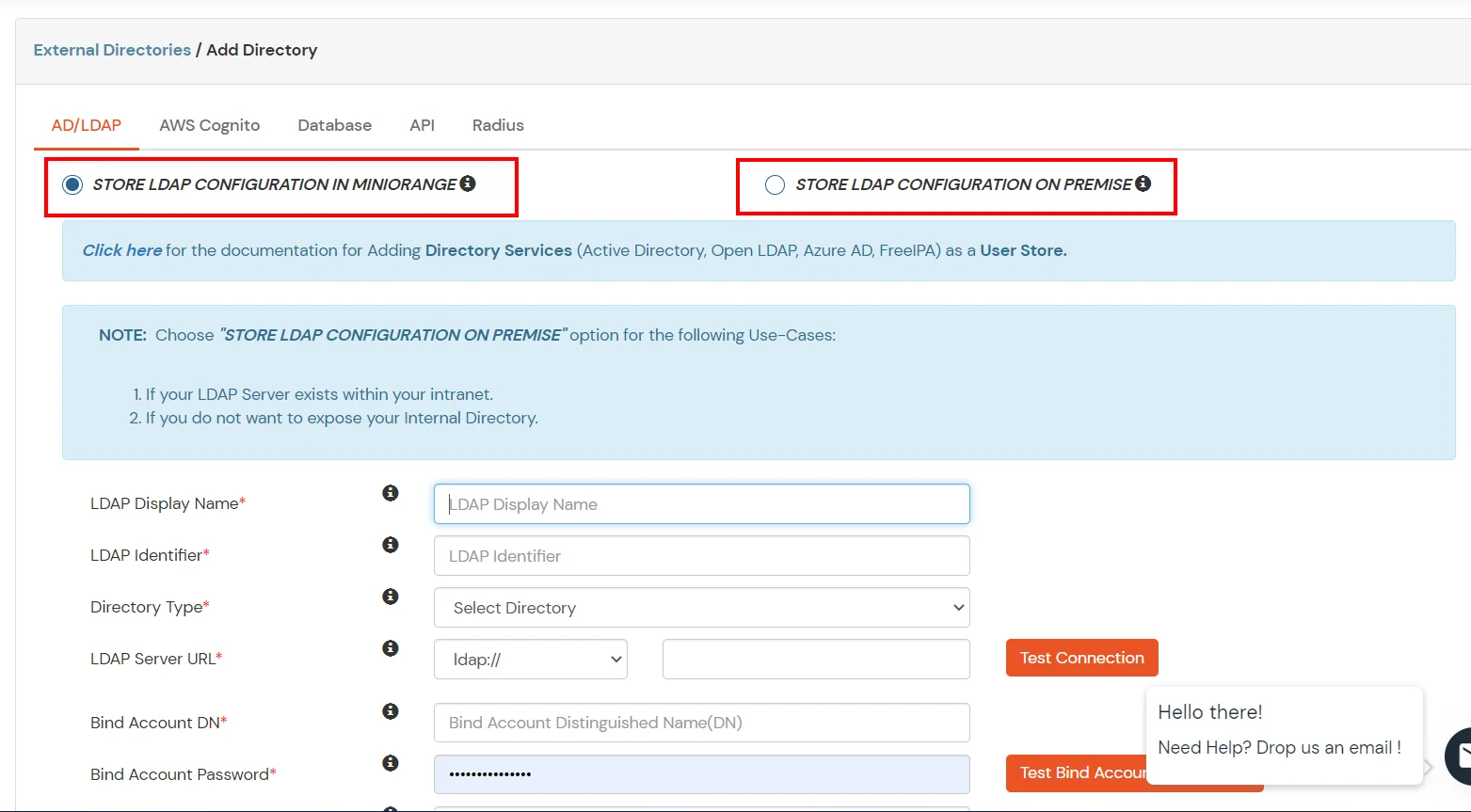
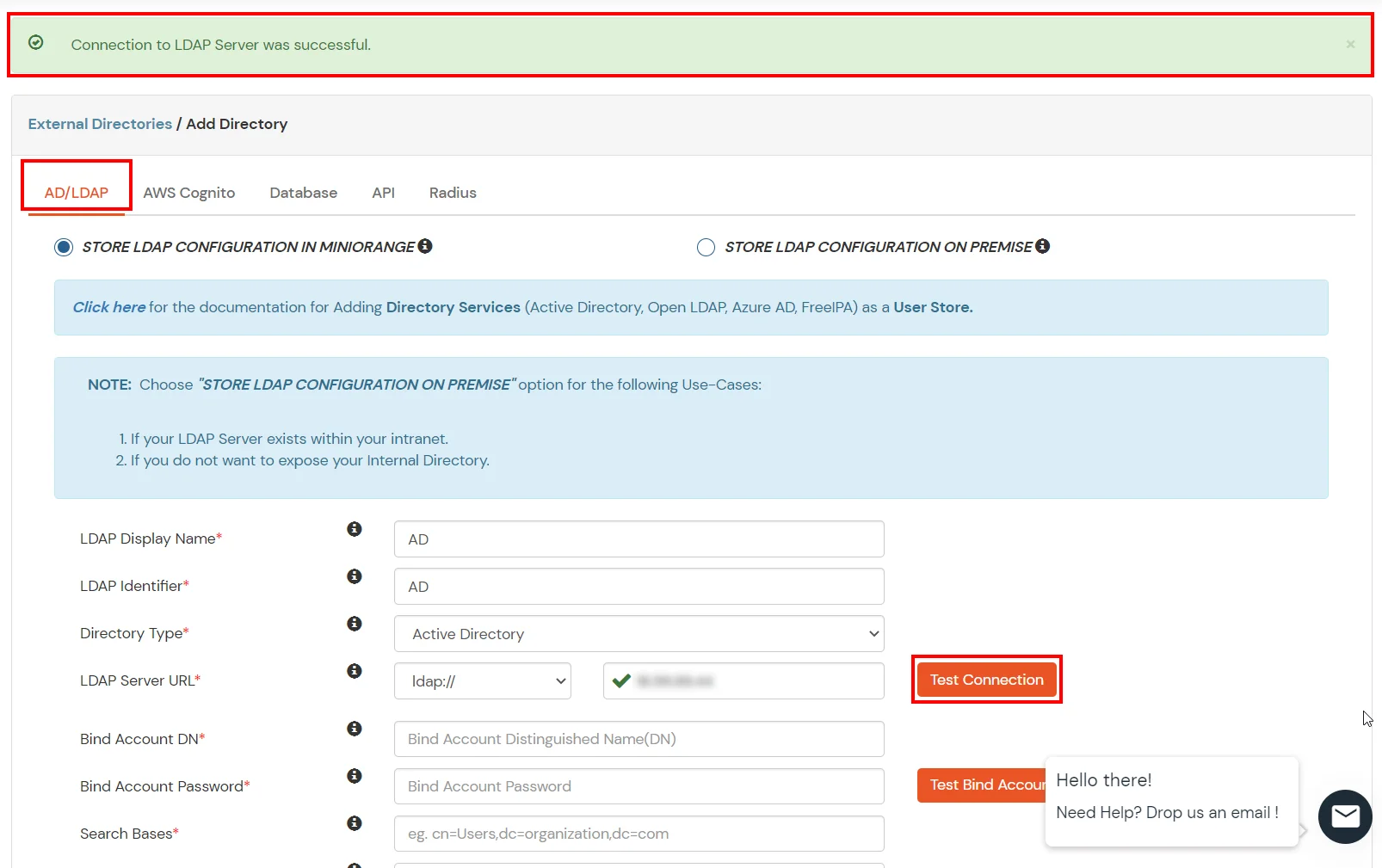
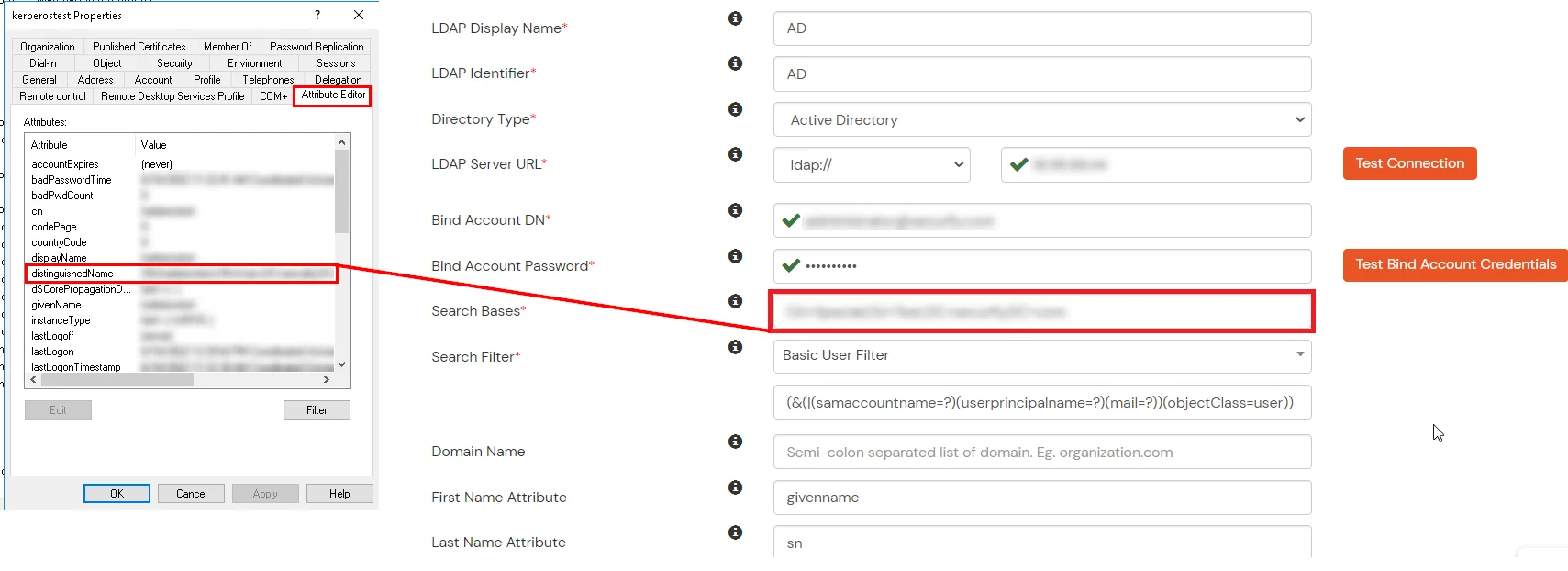
- Enter LDAP Display Name and LDAP Identifier name.
- Select Directory Type as Active Directory.
- Enter the LDAP Server URL or IP Address against LDAP Server URL field.
- Click on Test Connection button to verify if you have made a successful connection with your LDAP server.
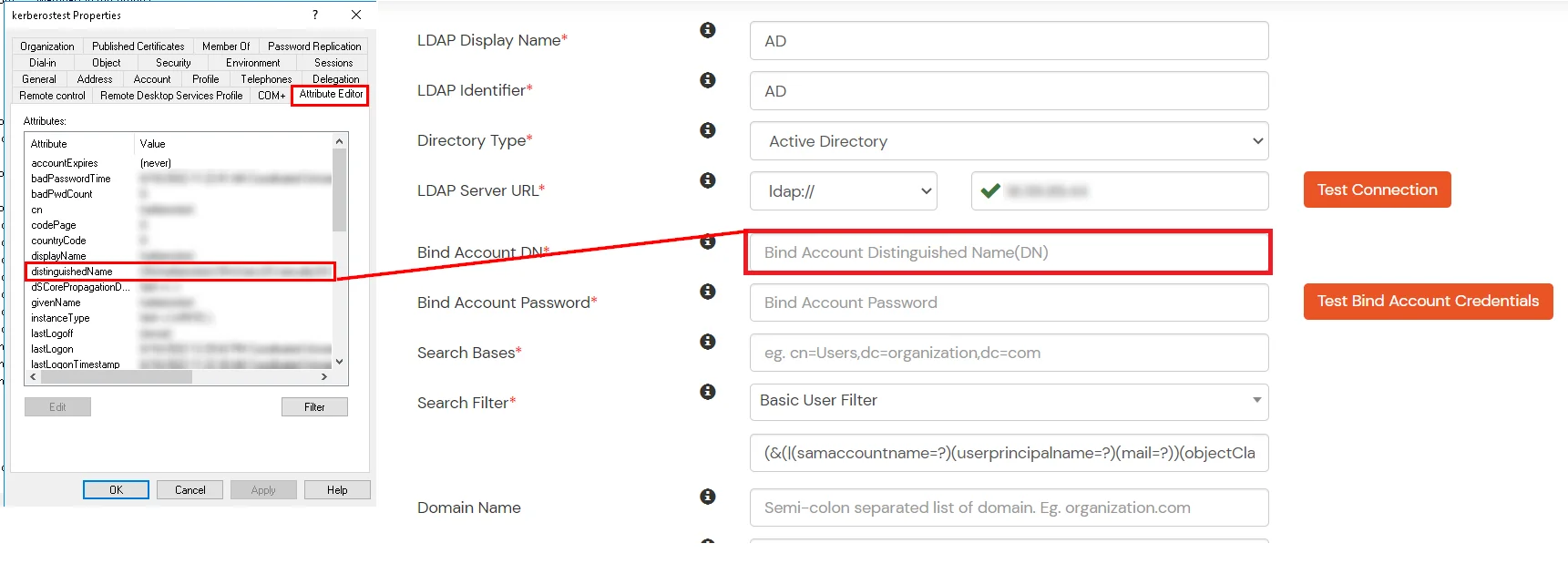
- In Active Directory, go to the properties of user containers/OU's and search for Distinguished Name attribute.
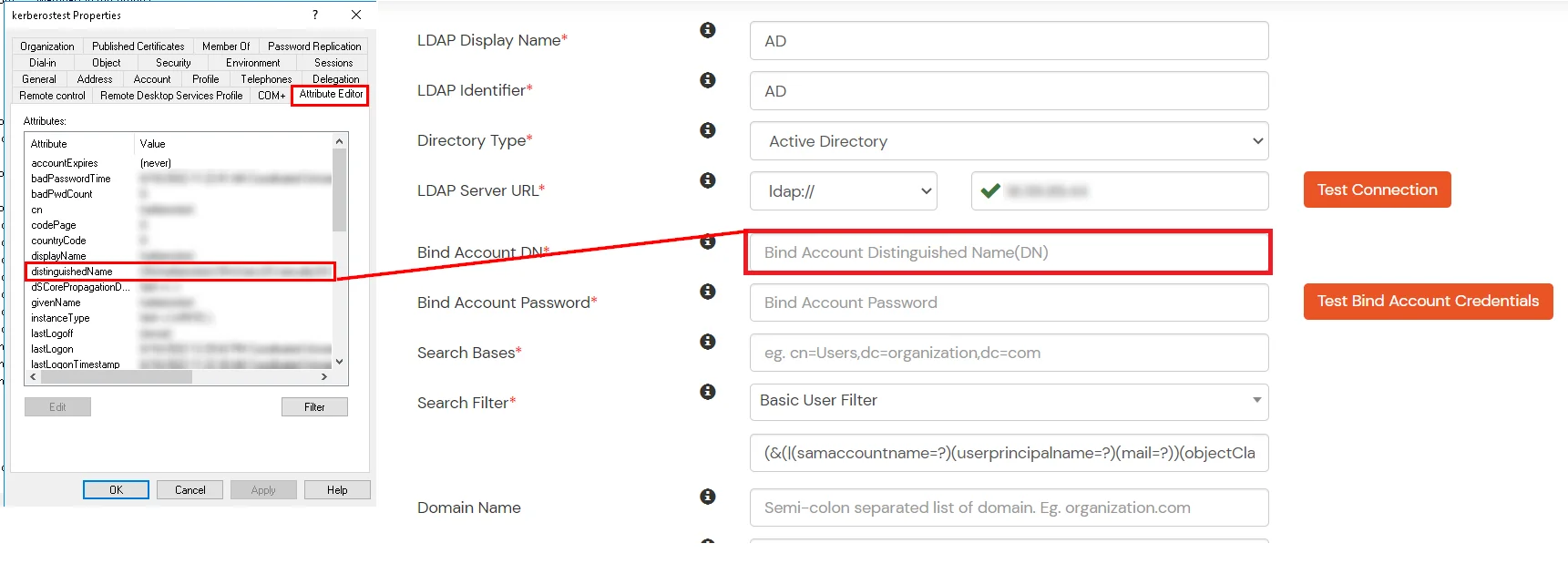
- Enter the valid Bind account Password.
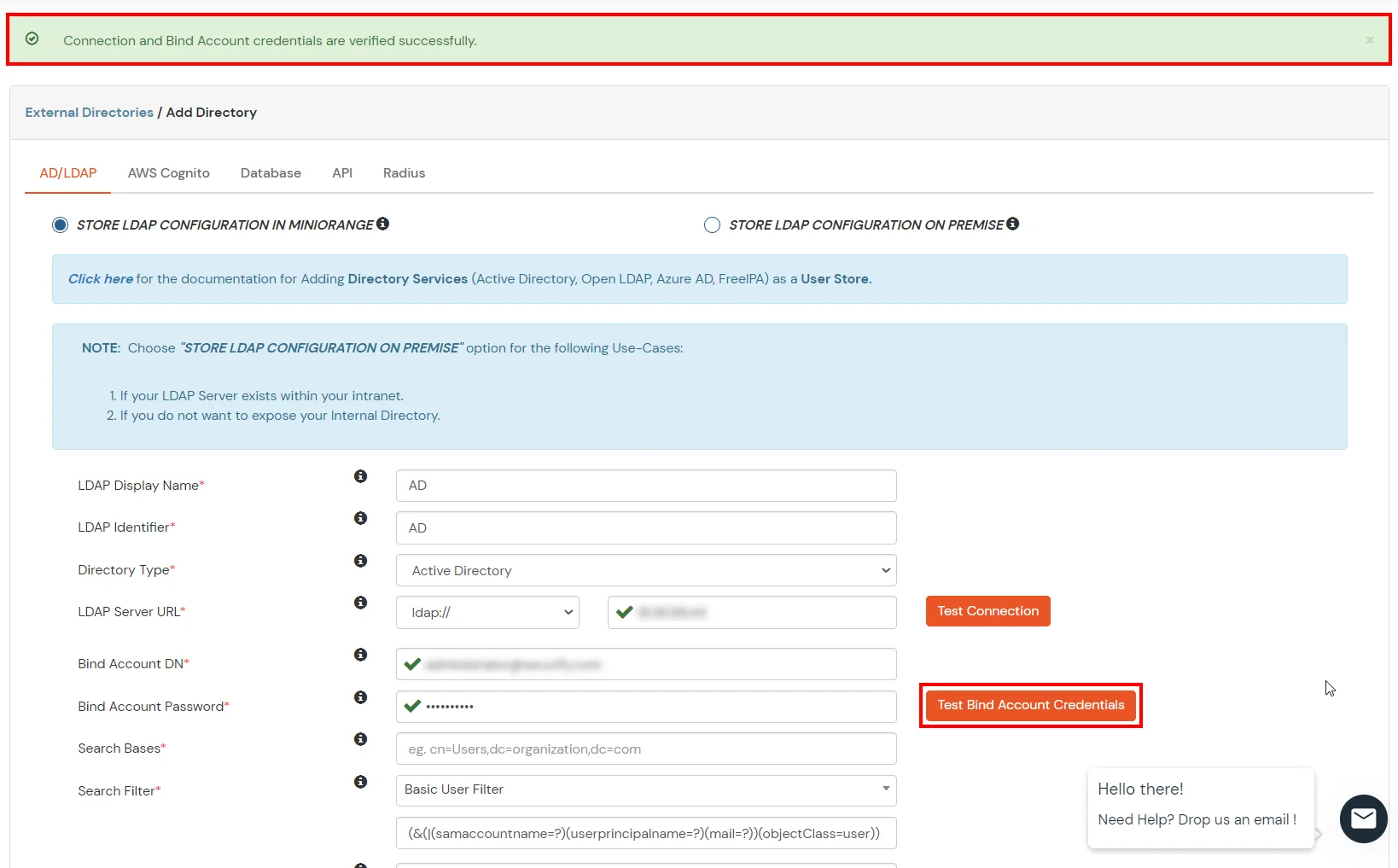
- Click on Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
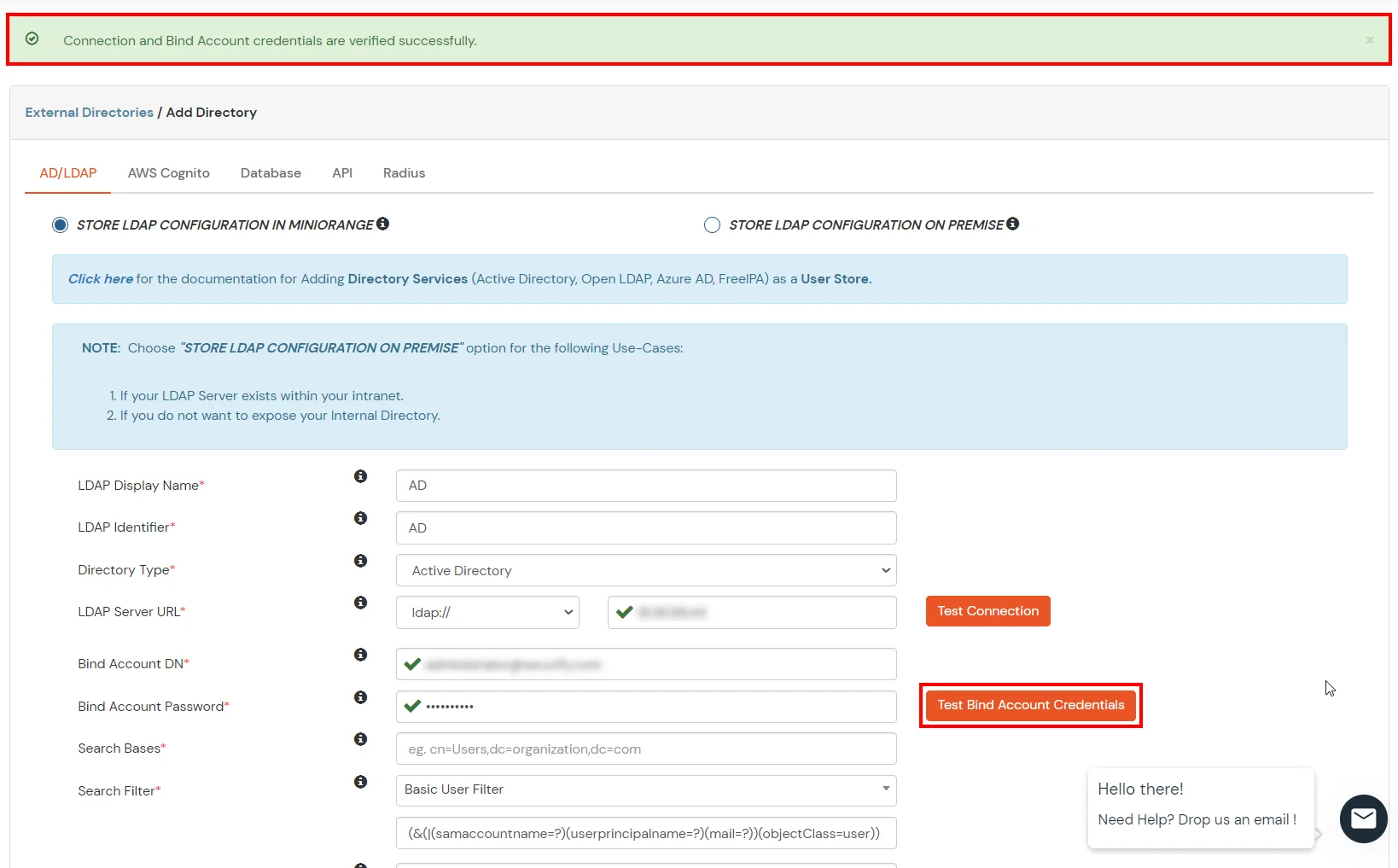
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
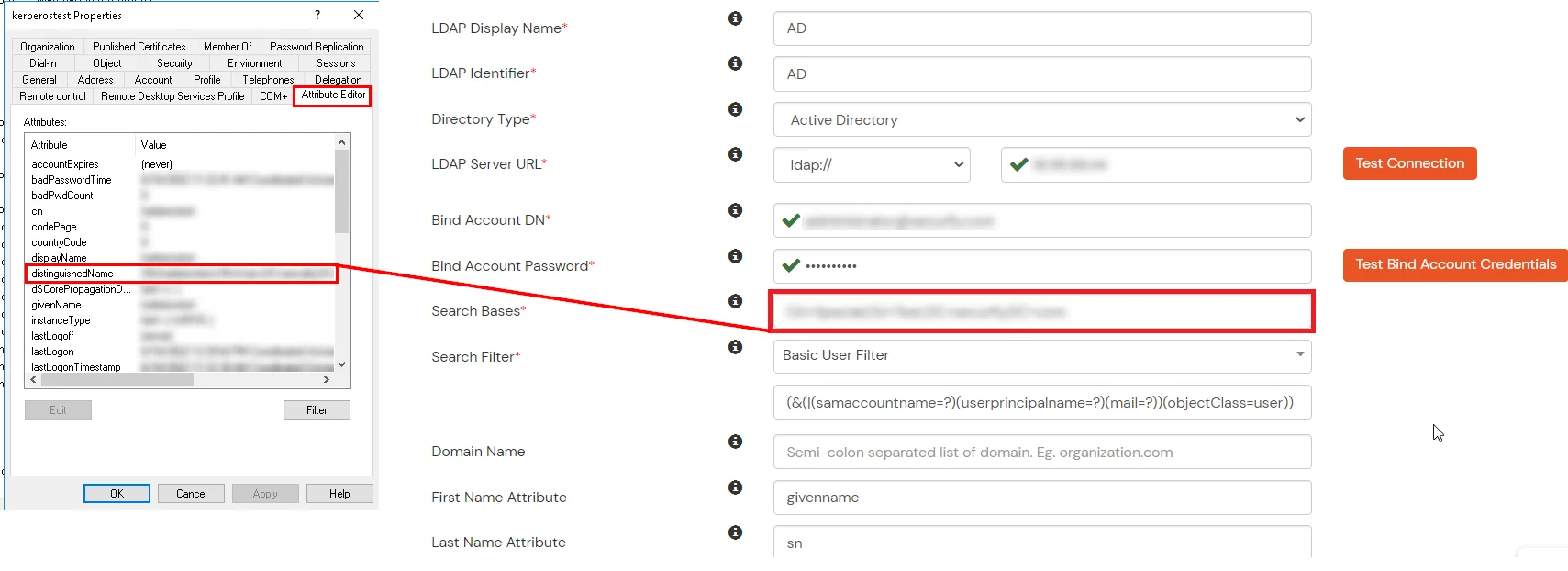
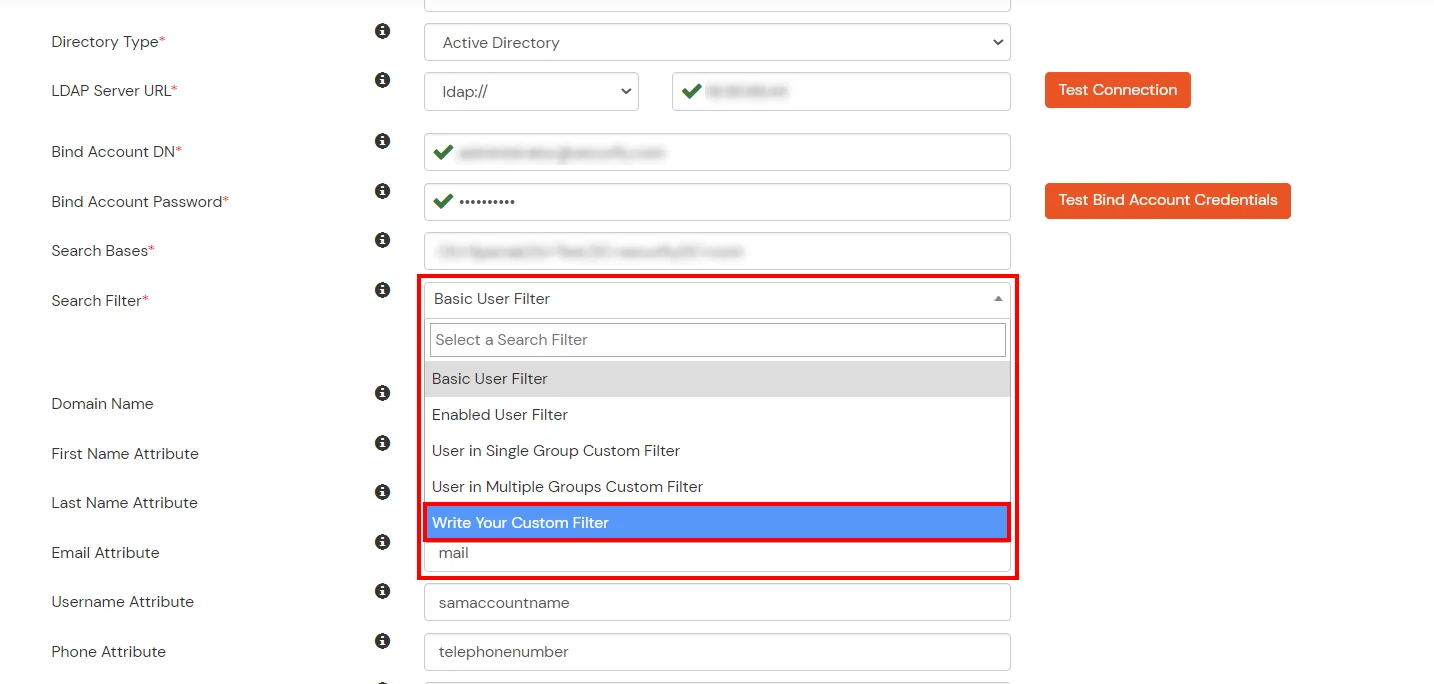
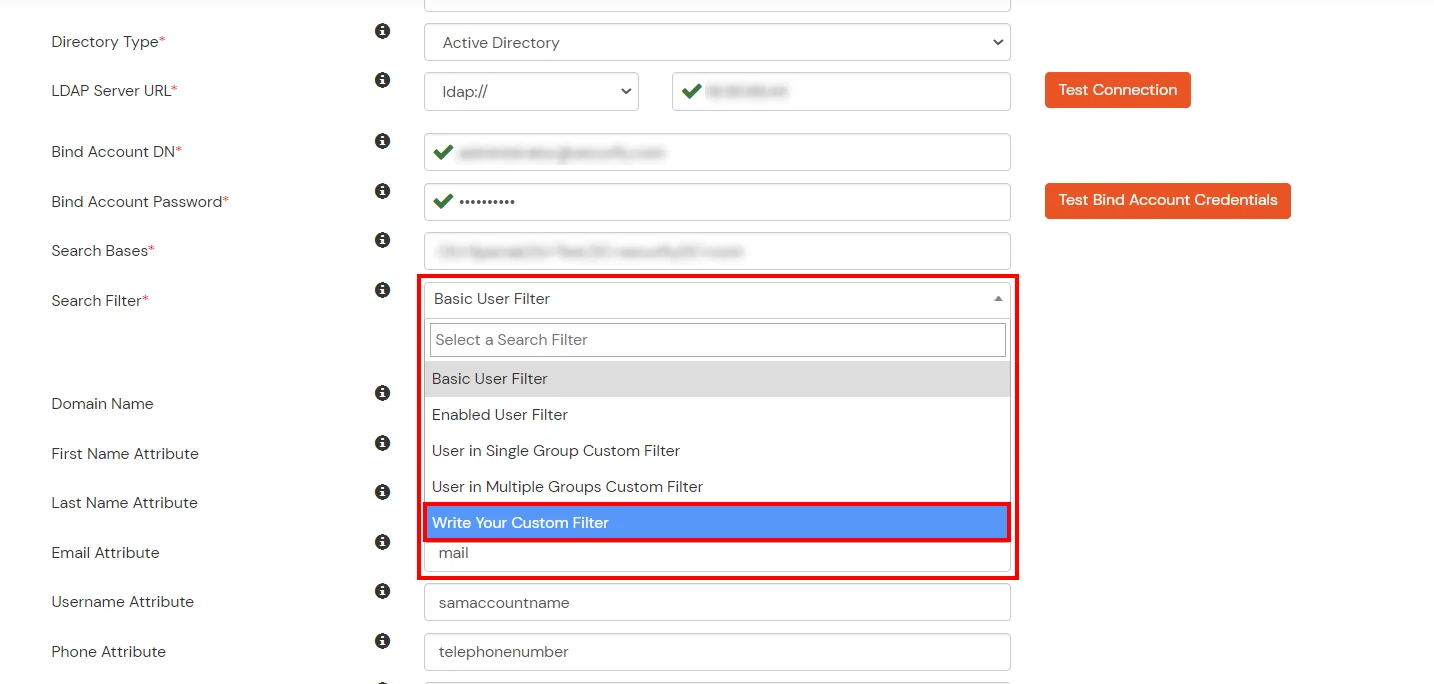
- Select a suitable Search filter from the drop-down menu. If you use User in Single Group Filter or User in Multiple Group Filter, replace the <group-dn> in the search filter with the distinguished name of the group in which your users are present. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
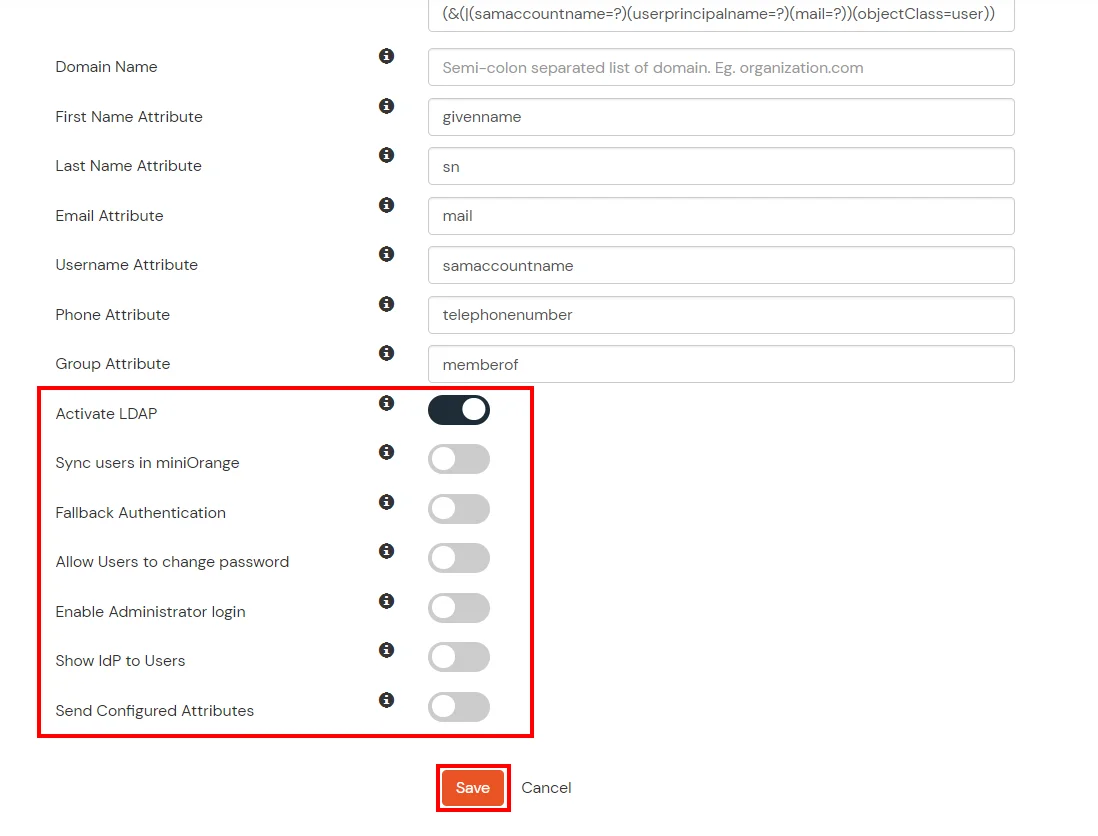
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Save button to add user store.
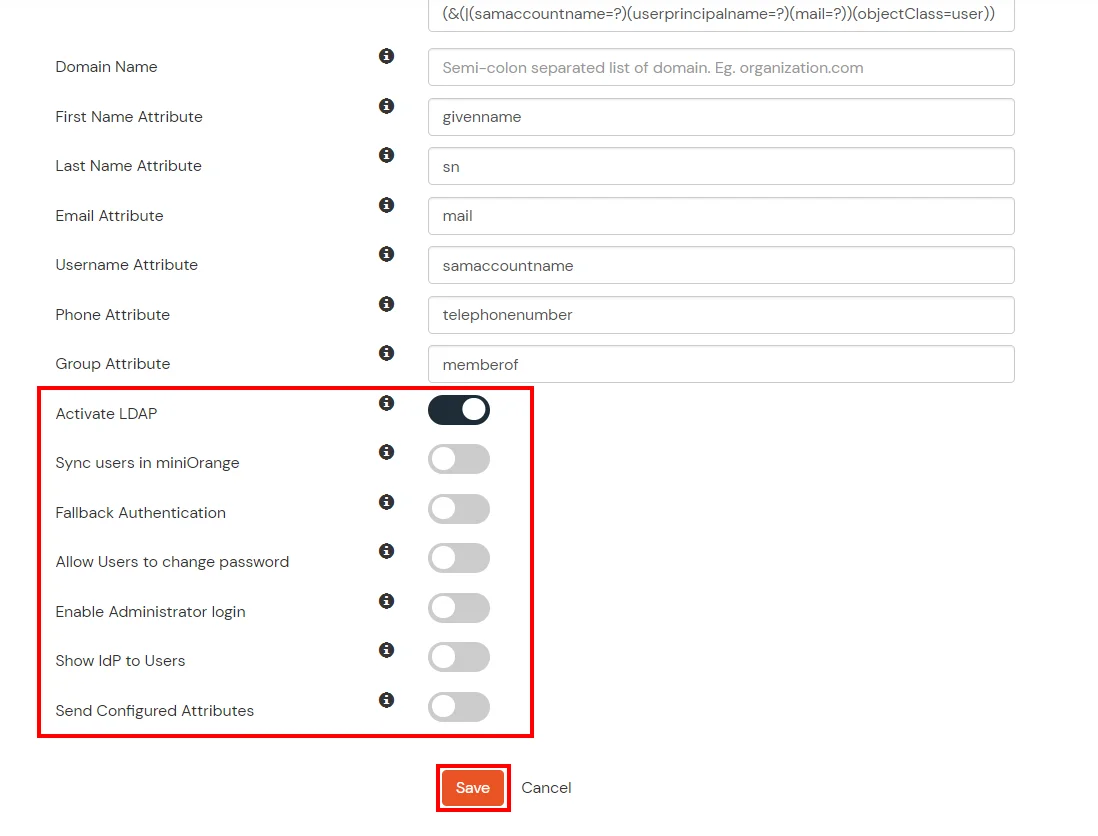
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Allow users to change password |
This allows your users to change their password. It updates the new credentials in your LDAP server |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Send Configured Attributes |
If you enable this option, then only the attributes configured below will be sent in attributes at the time of login |
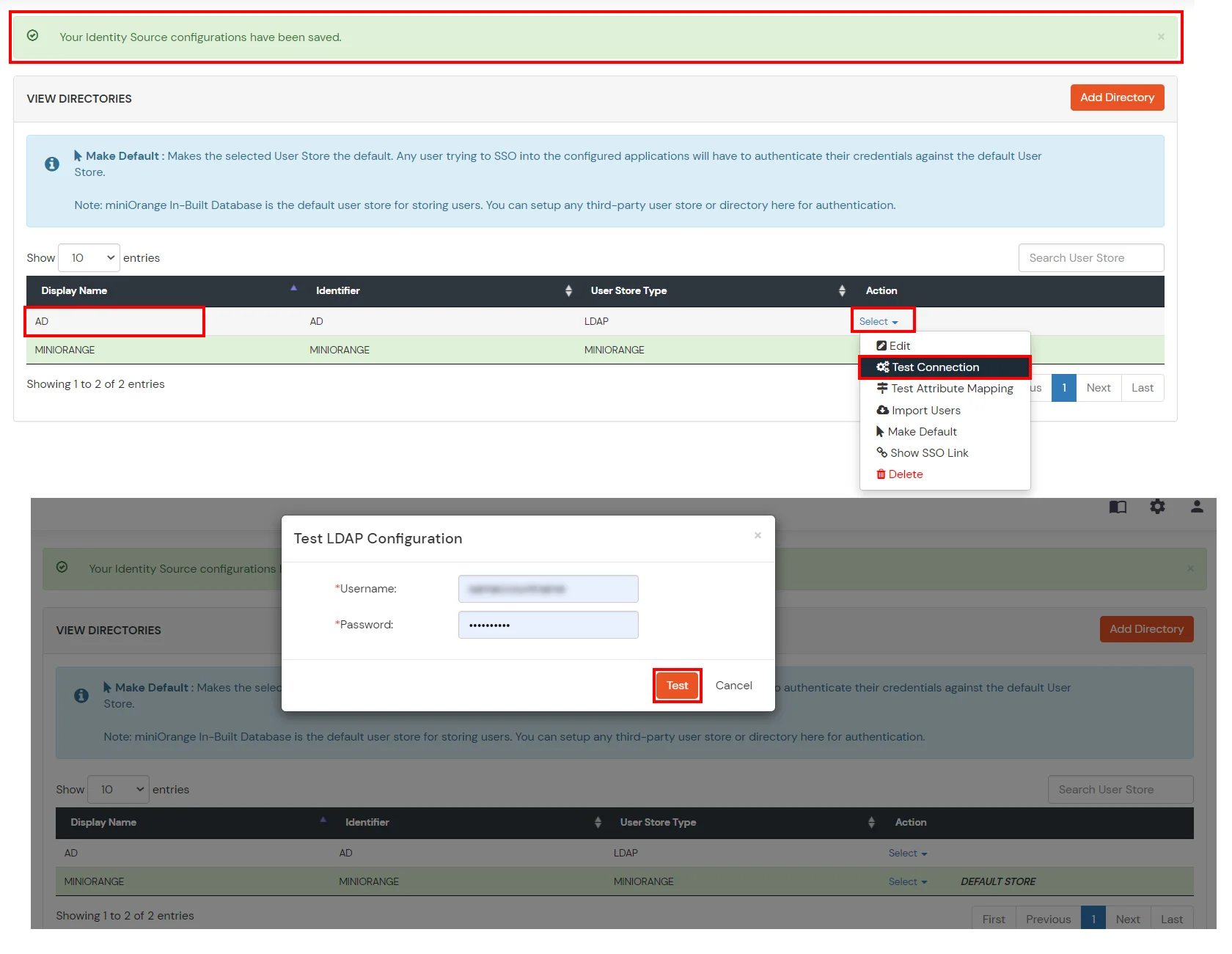
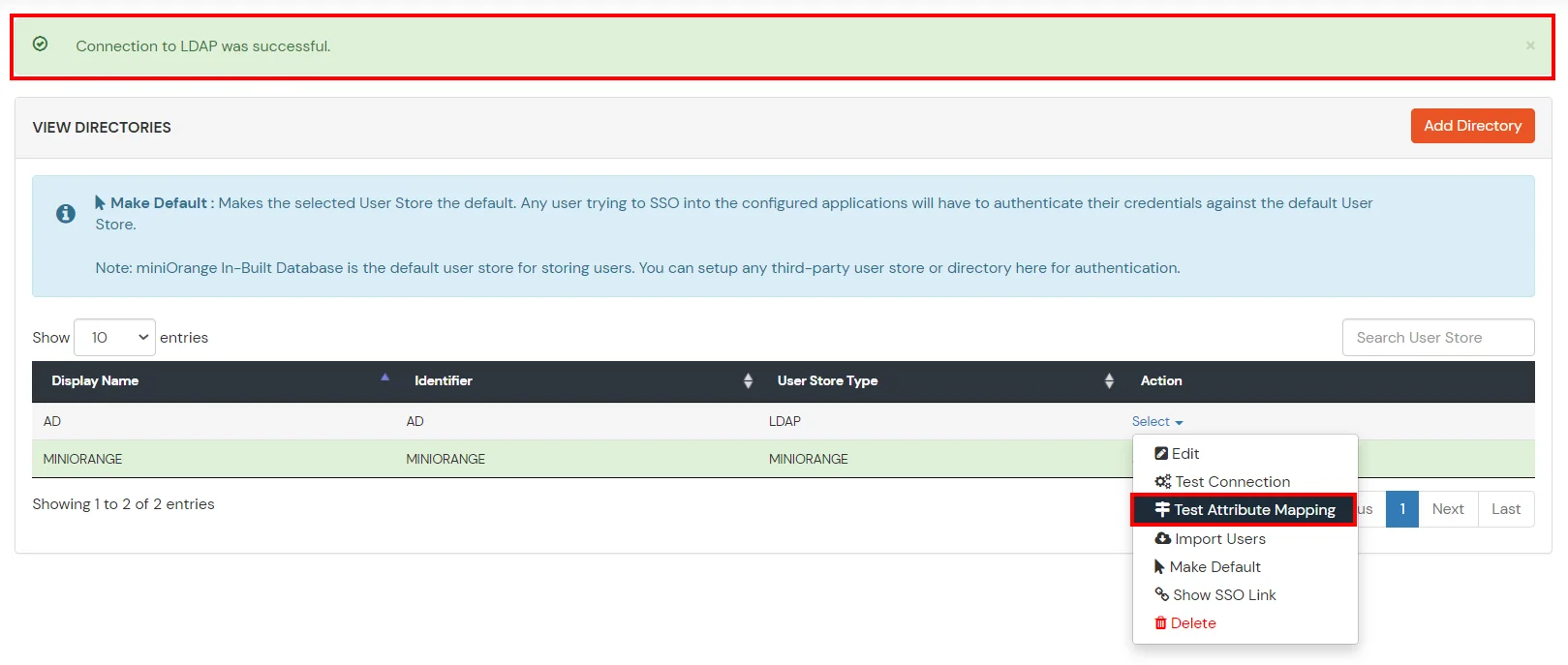
- Click on Save. After this, it will show you the list of User stores. Click on Test Connection to check whether you have enter valid details. For that, it will ask for username and password.
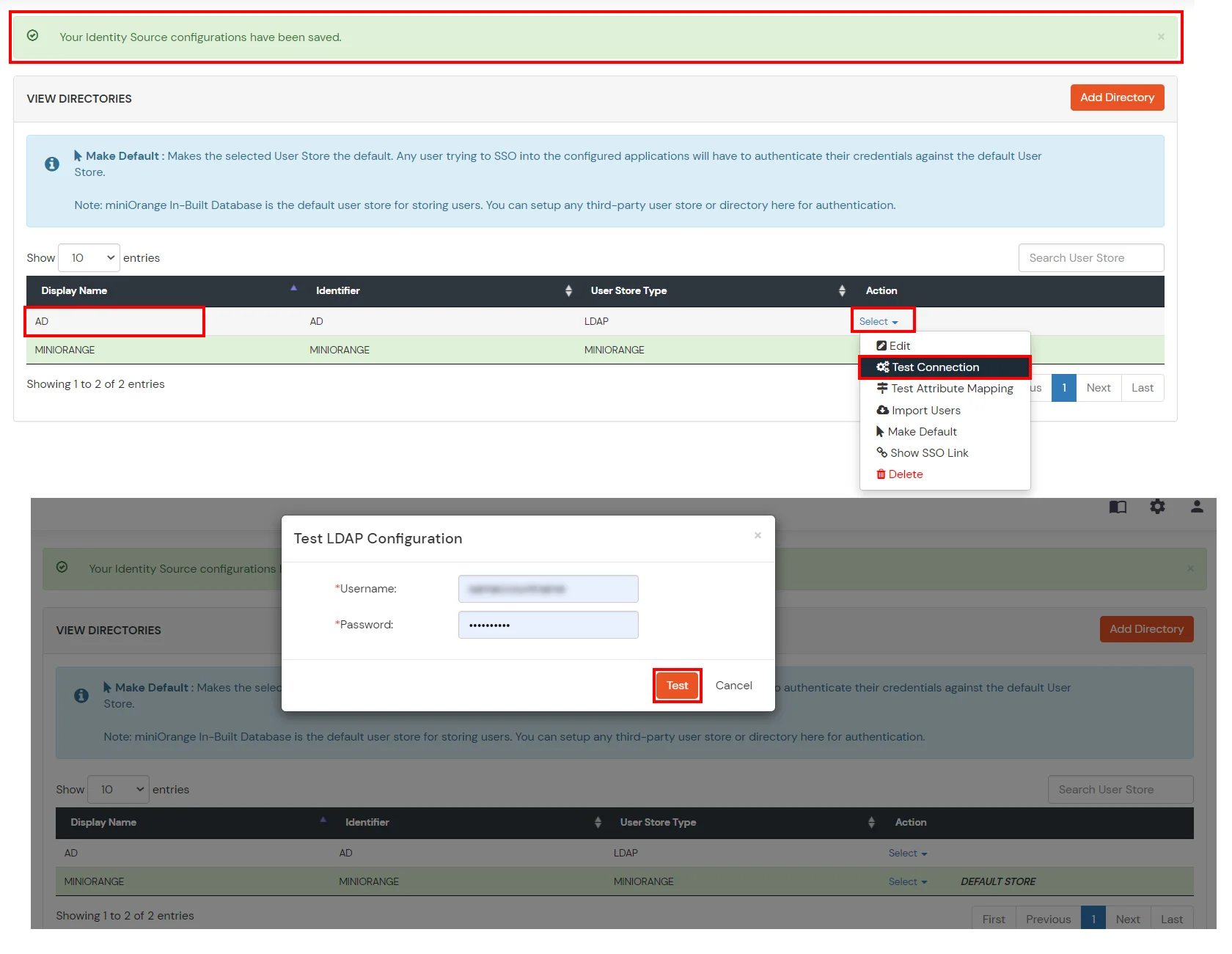
- On Successful connection with LDAP Server, a success message is shown.
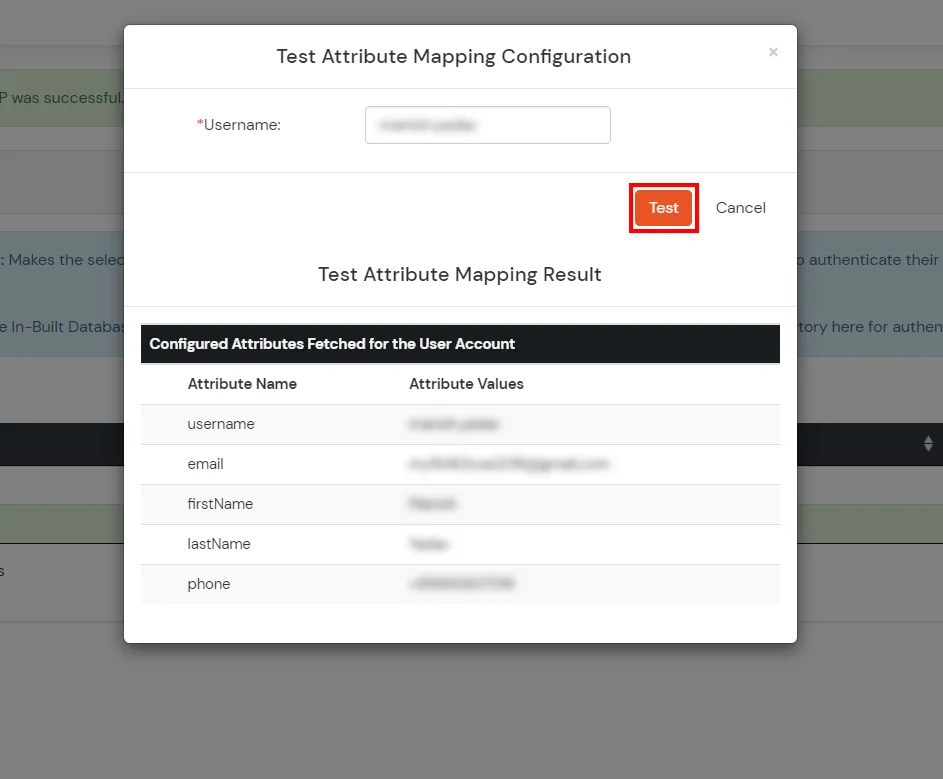
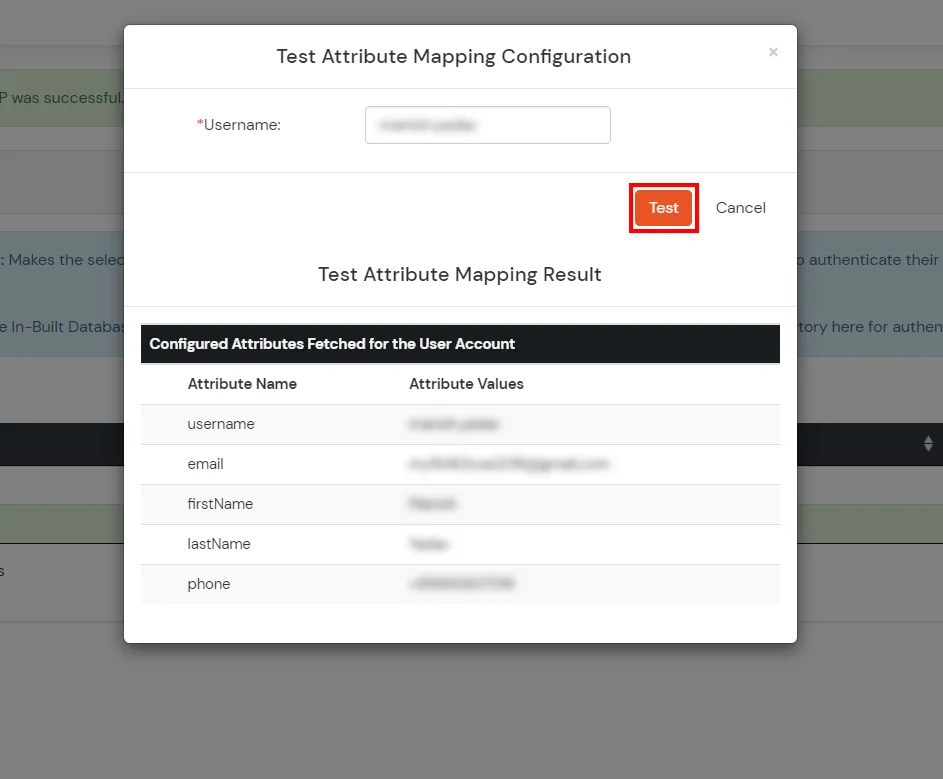
- Click on Test Attribute Mapping.
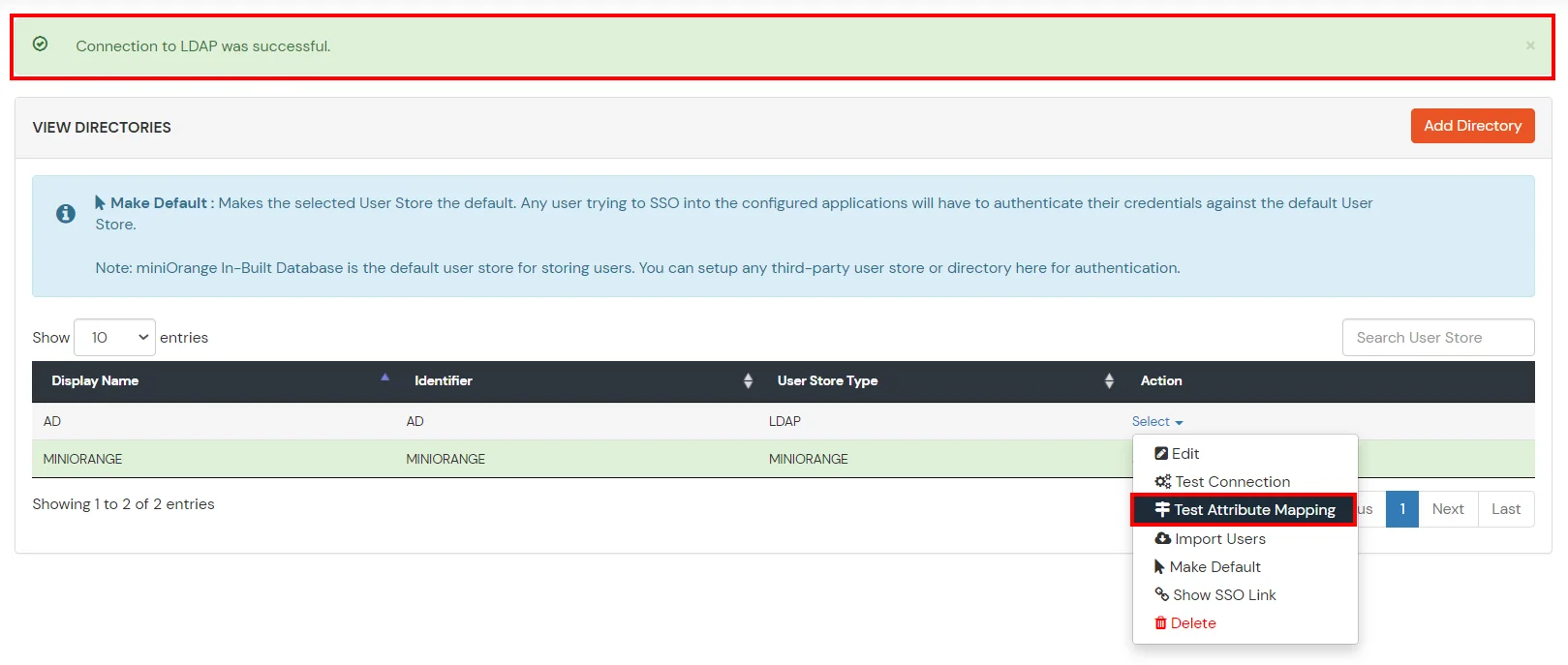
- Enter a valid Username. Then, click on Test. Mapped Attributes corresponding to the user are fetched.
- After successful Attribute Mapping Configuration, go back to the ldap configuration and enable Activate LDAP in order to authenticate users from AD/LDAP.
Refer our guide to setup LDAPS on windows server.
User Import and Provisioning from AD
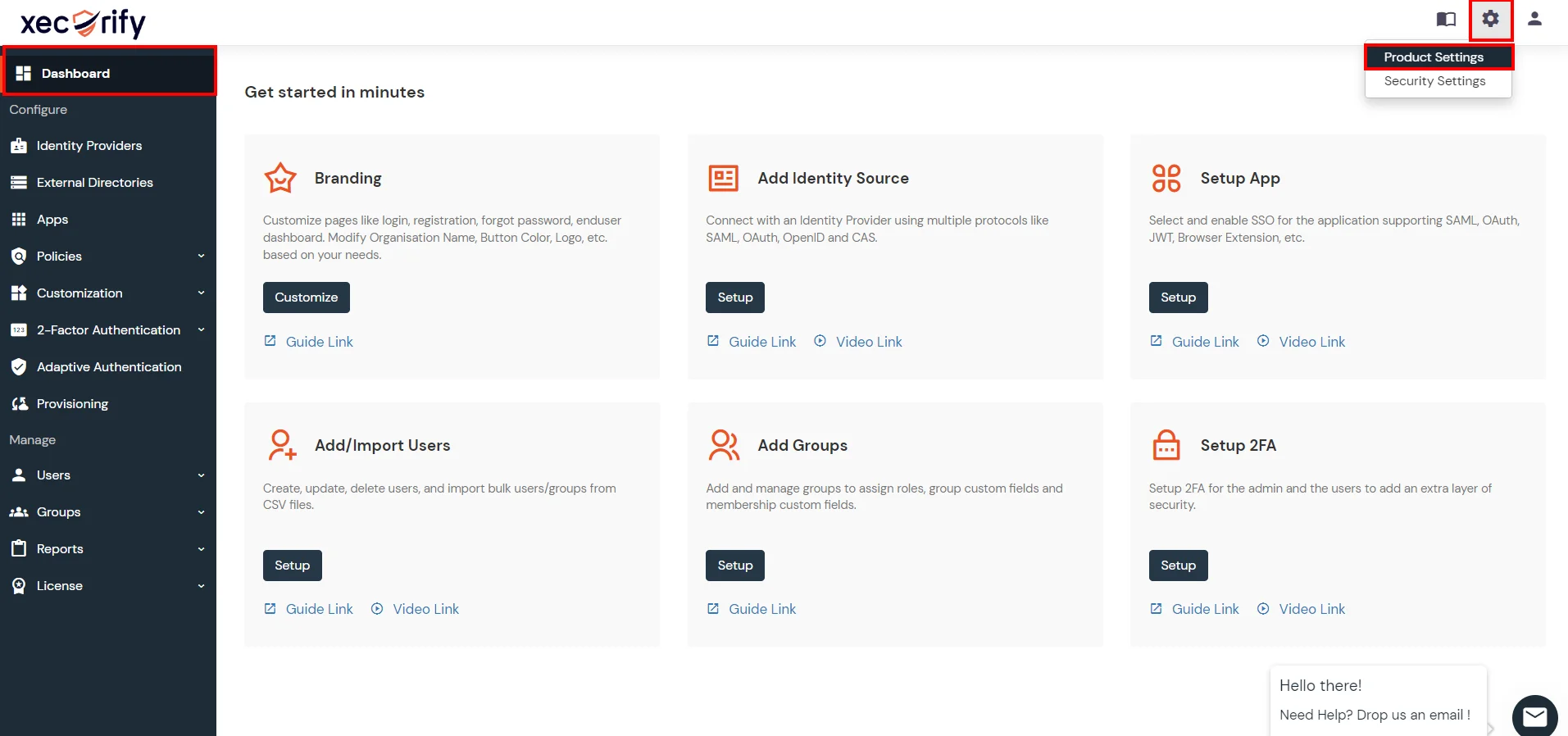
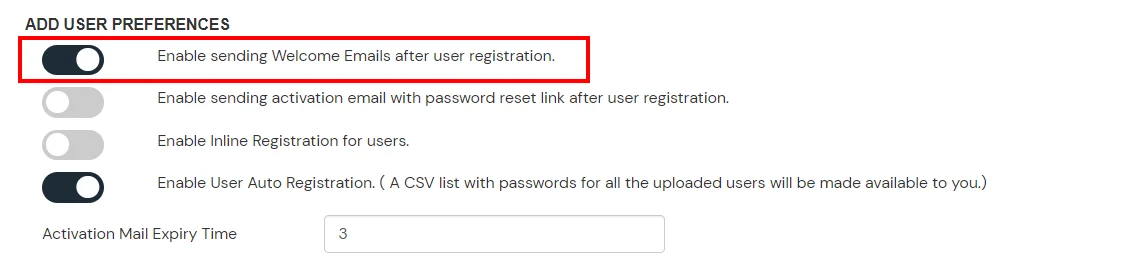
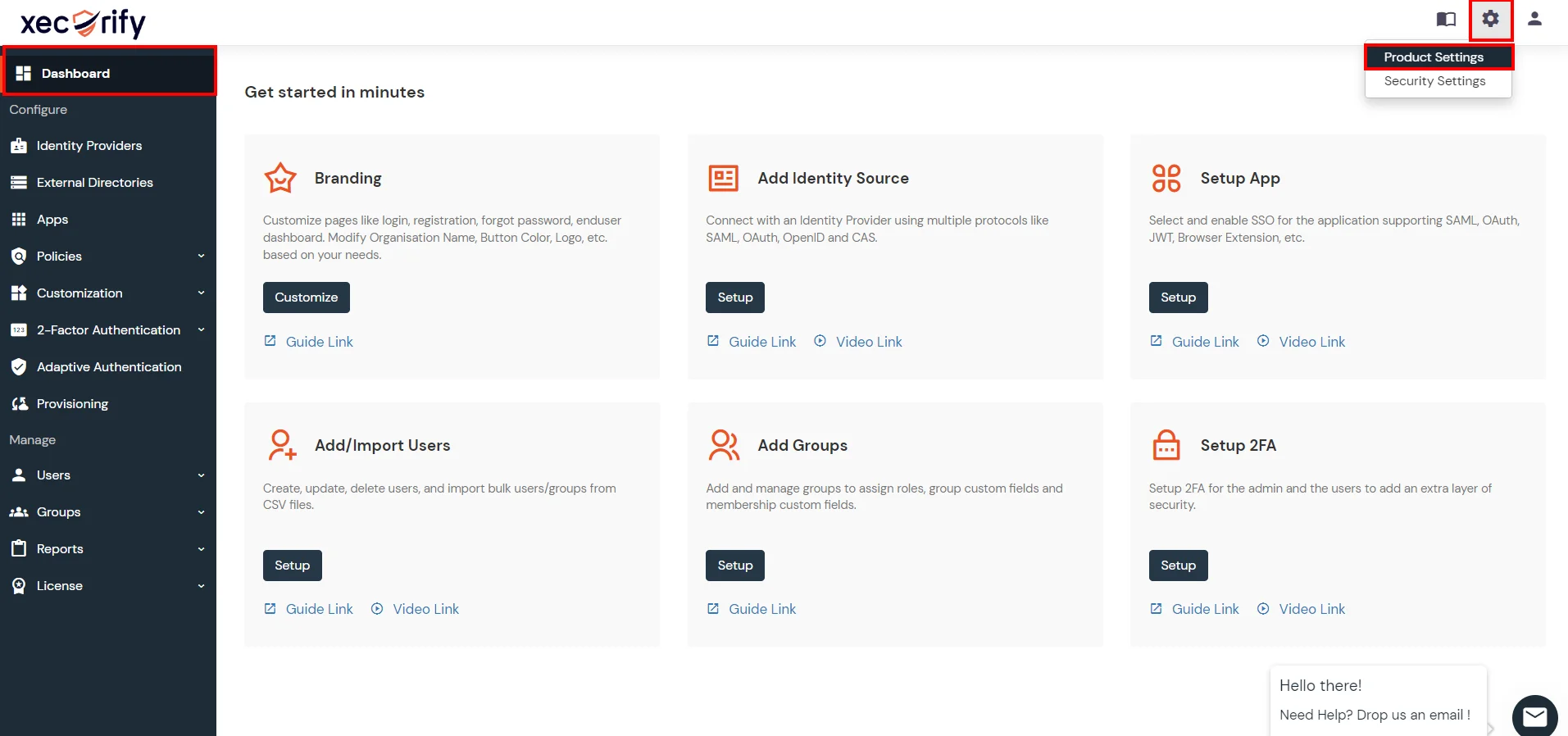
- Go to Settings >> Product Settings in the Customer Admin Account.
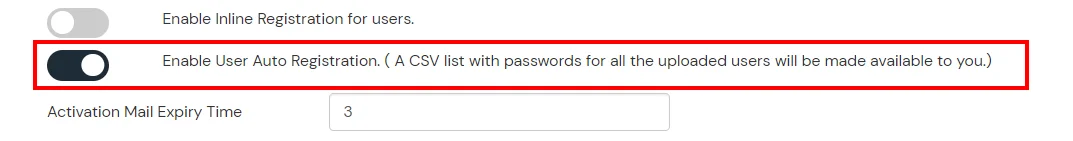
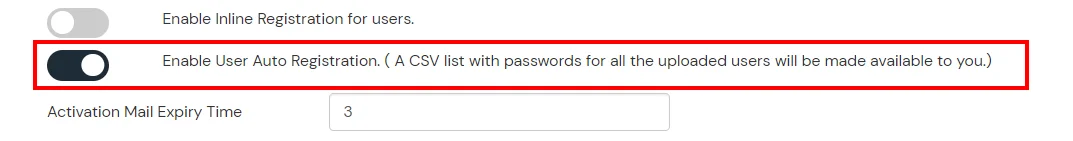
- Enable the "Enable User Auto Registration" option and click Save.
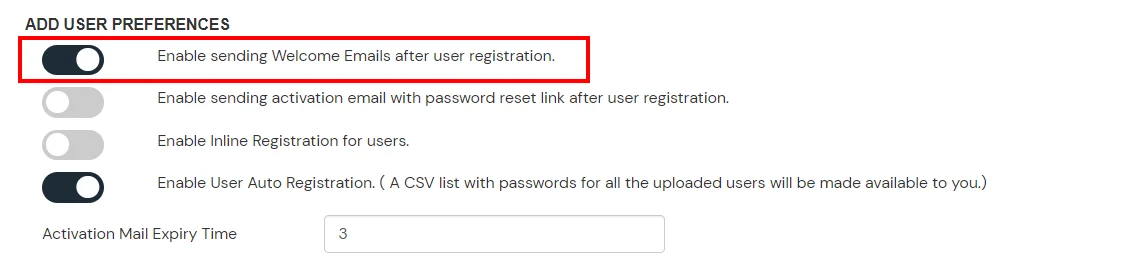
- (Optional) To send a welcome email to all the end users that will be imported, enable the "Enable sending Welcome Emails after user registration" option and click Save.
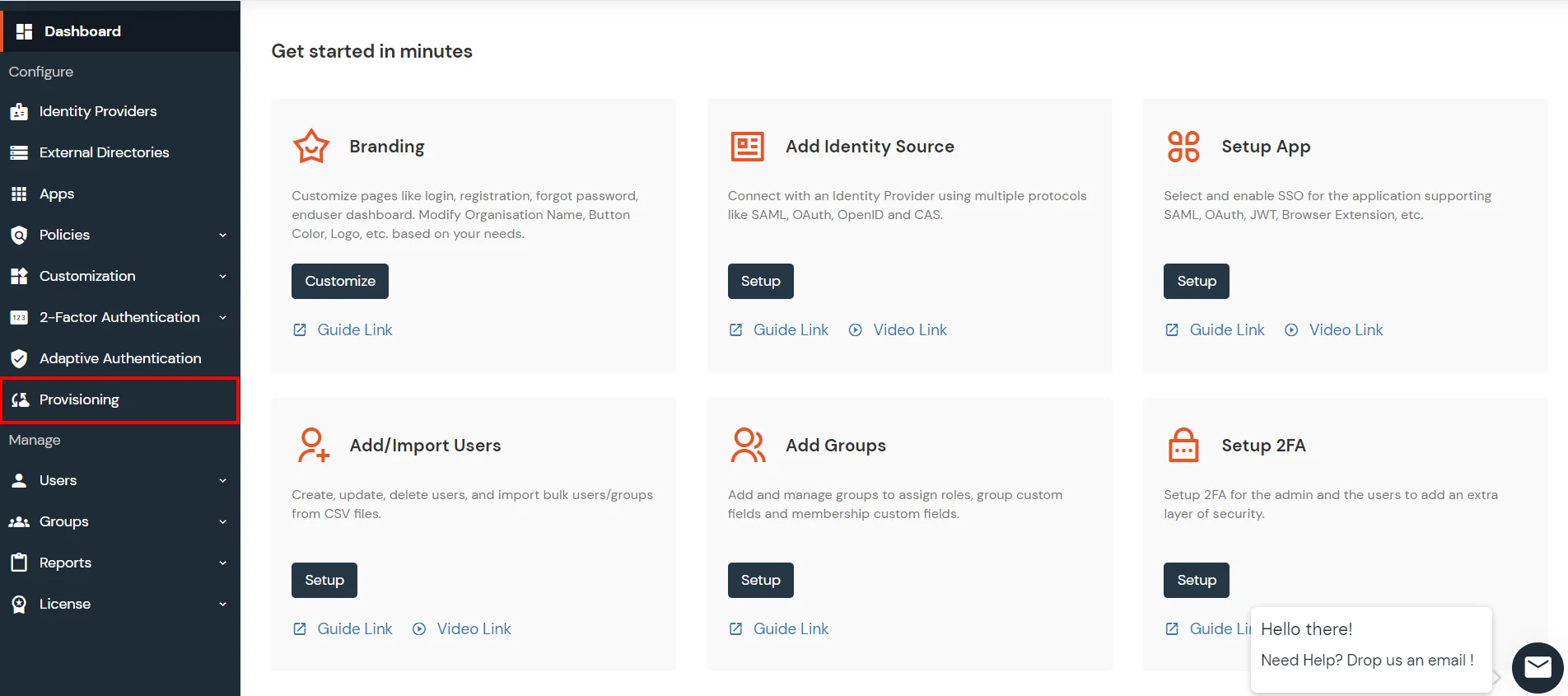
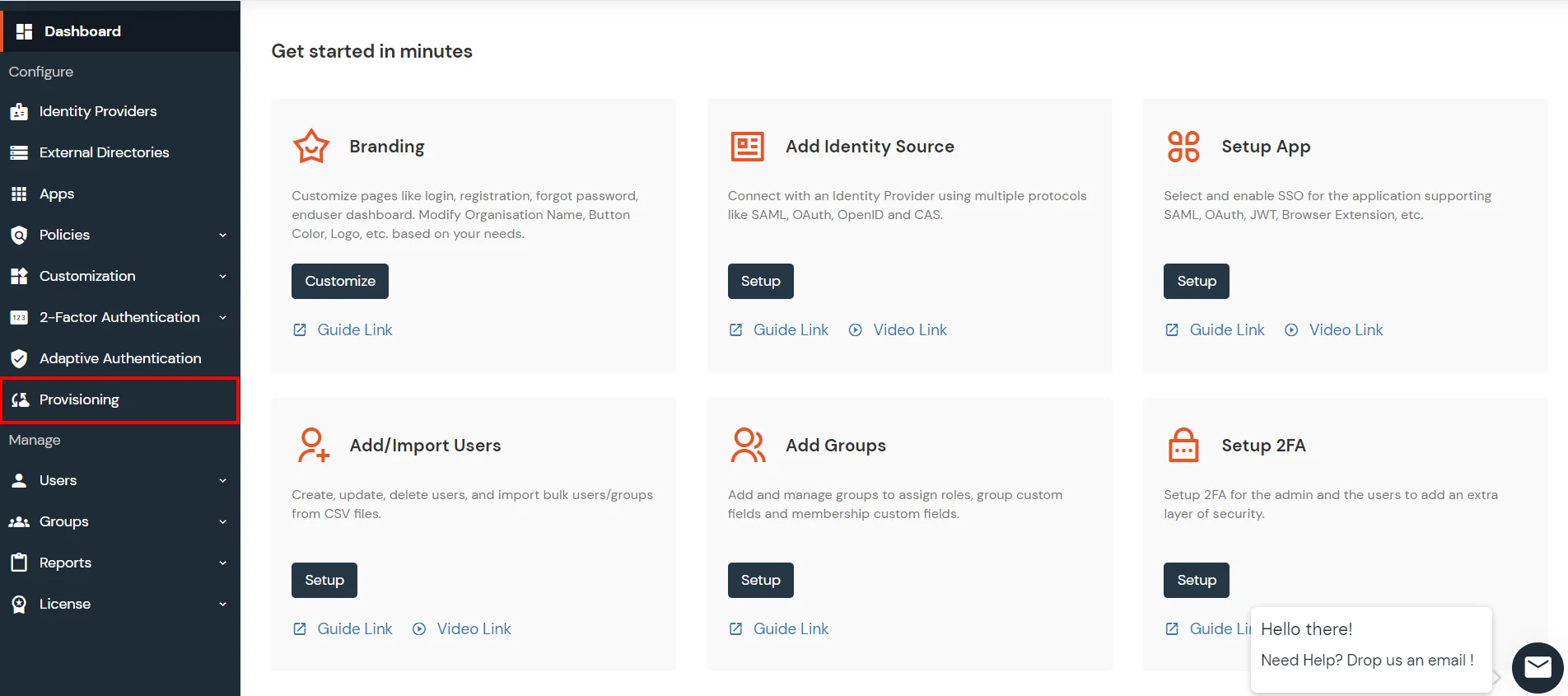
- From the Left-Side menu of the dashboard select Provisioning.
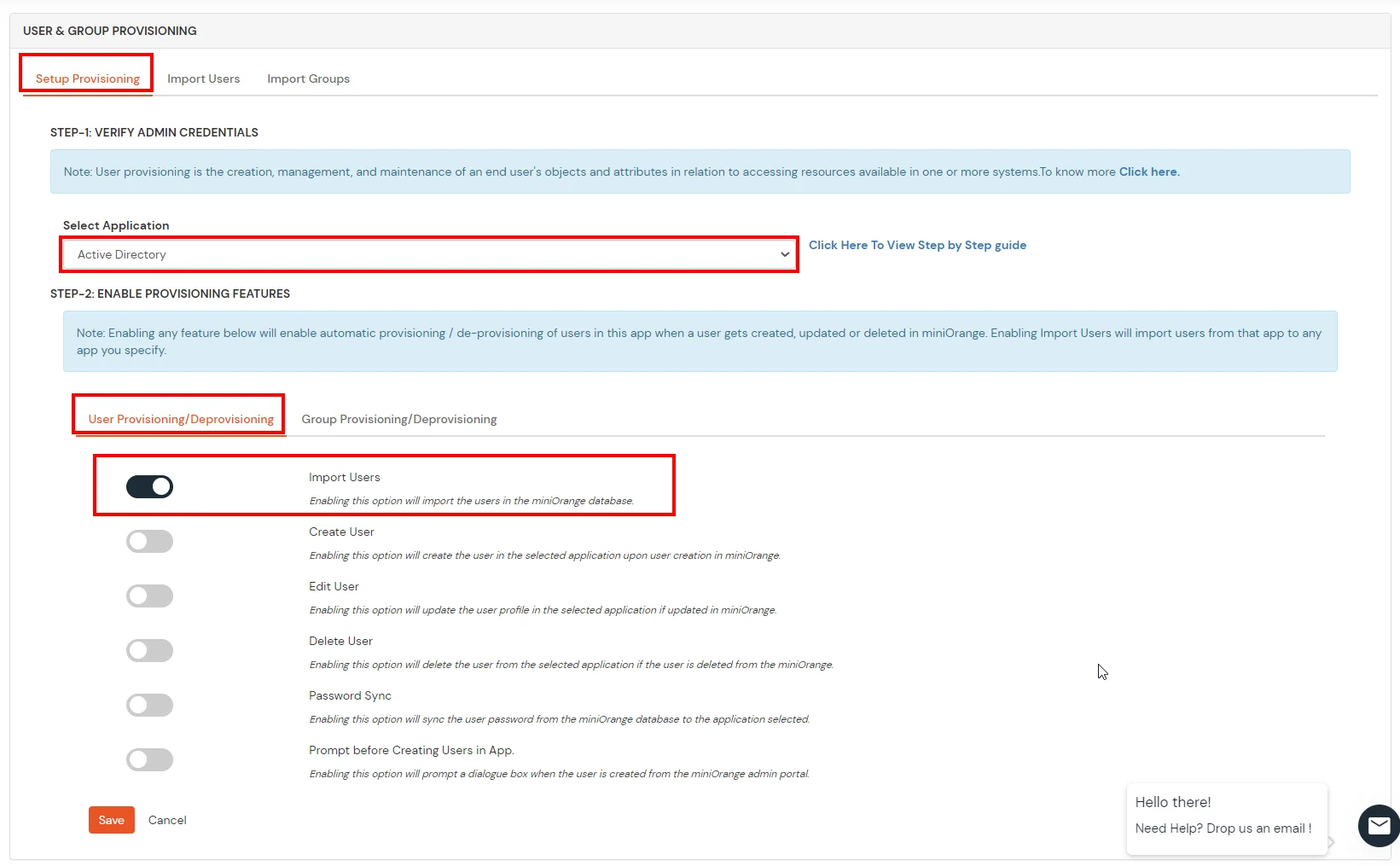
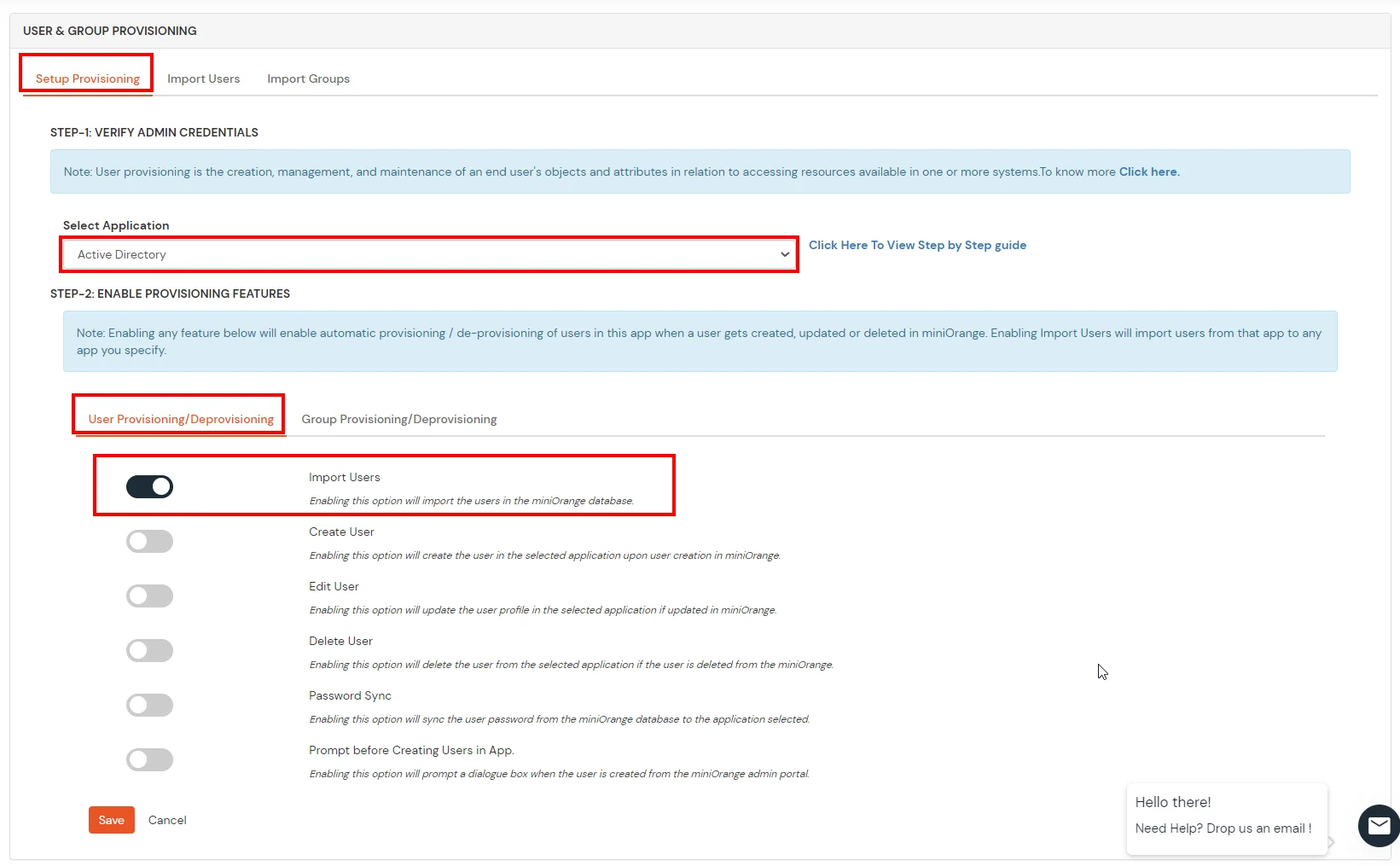
- In Setup Provisioning tab select Active Directory in the Select Application drop-down.
- Toggle the Import Users tab, click on Save button.
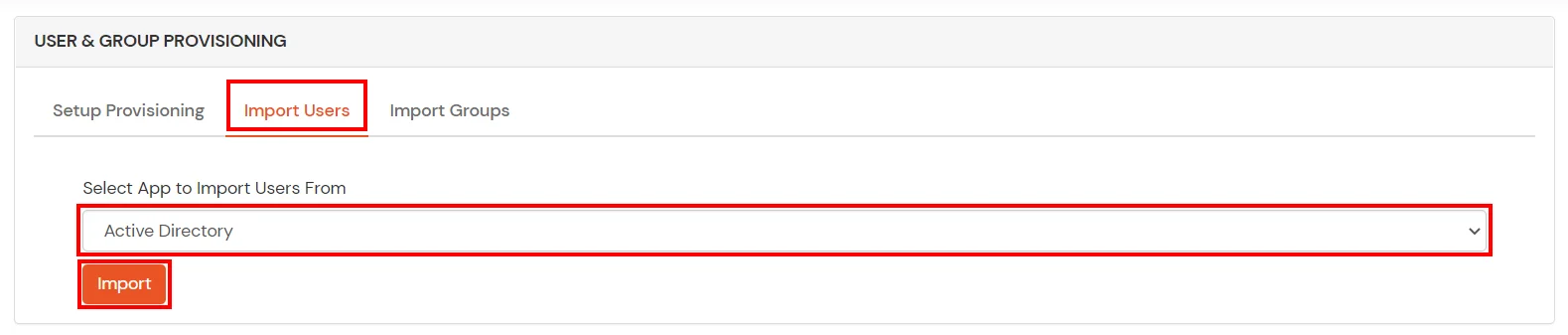
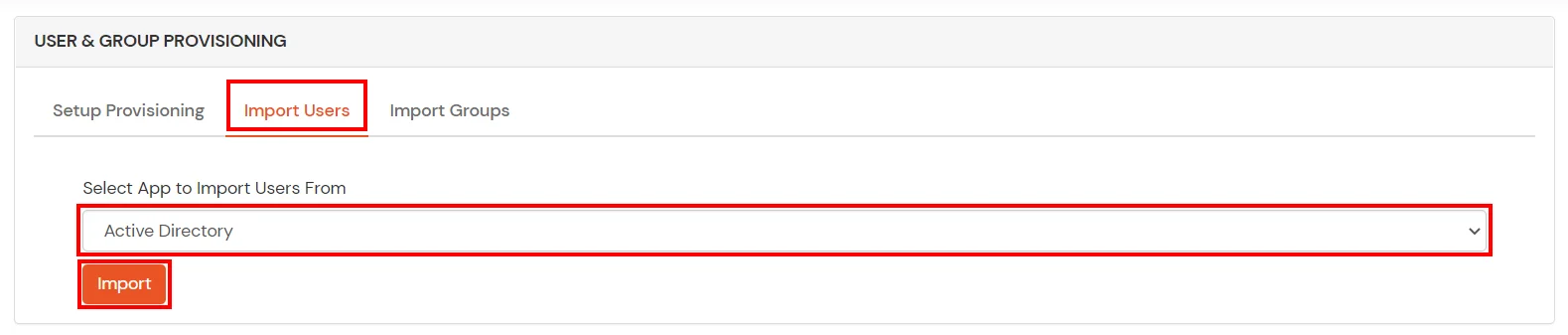
- On the same section, switch to Import Users section.
- Select Active Directory from the dropdown and click on the Import Users tab, to import all the users from Active Directory to miniOrange.
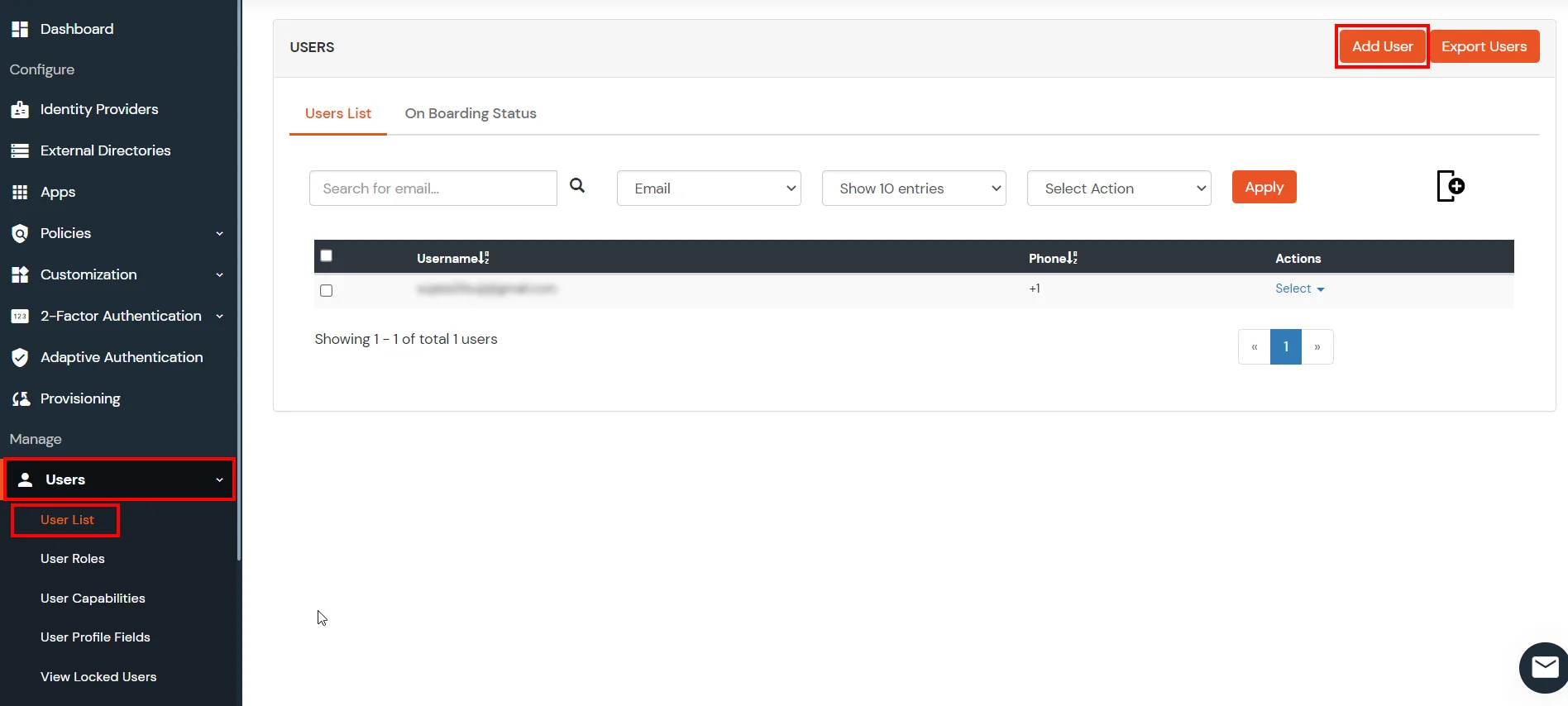
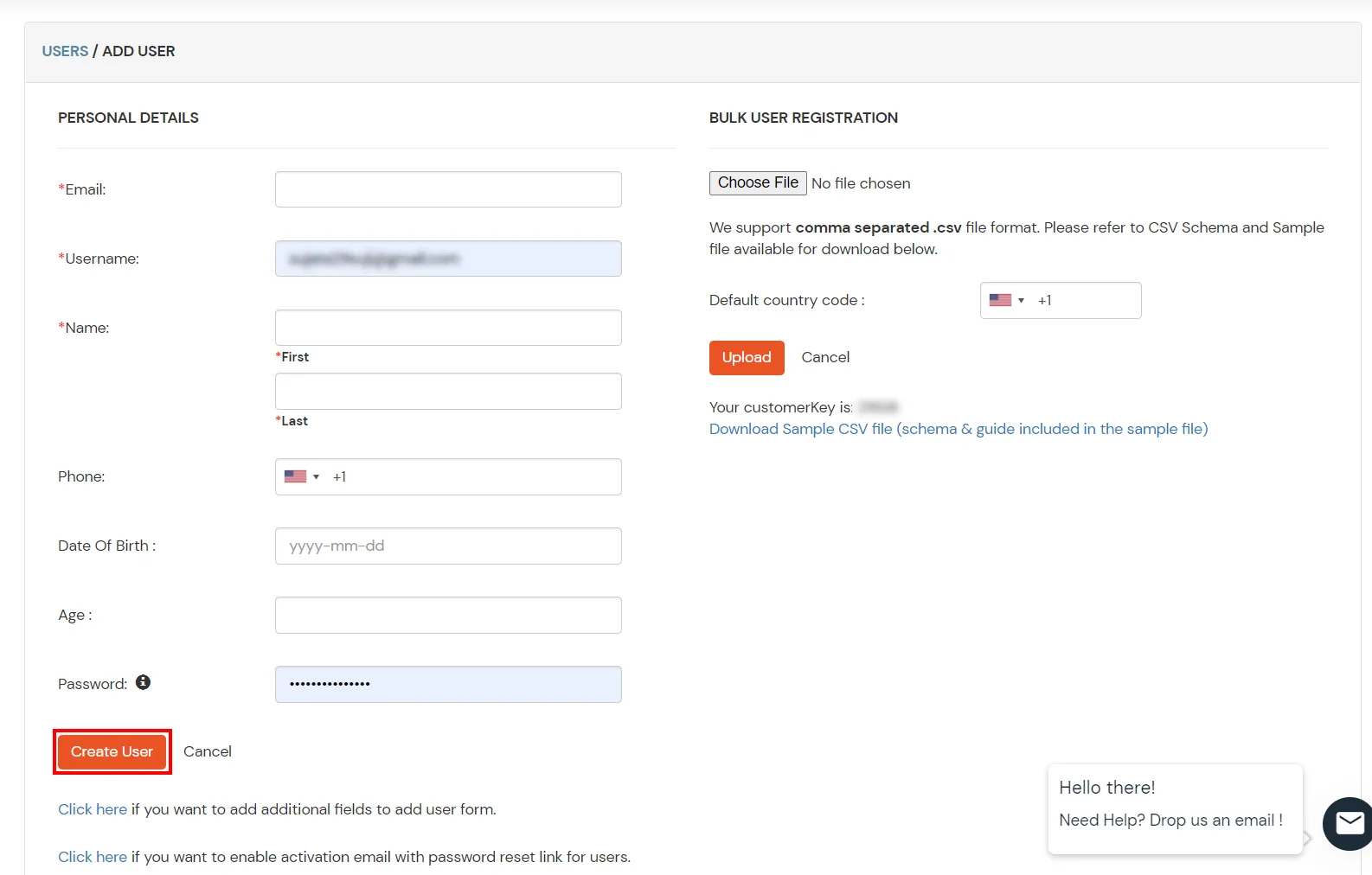
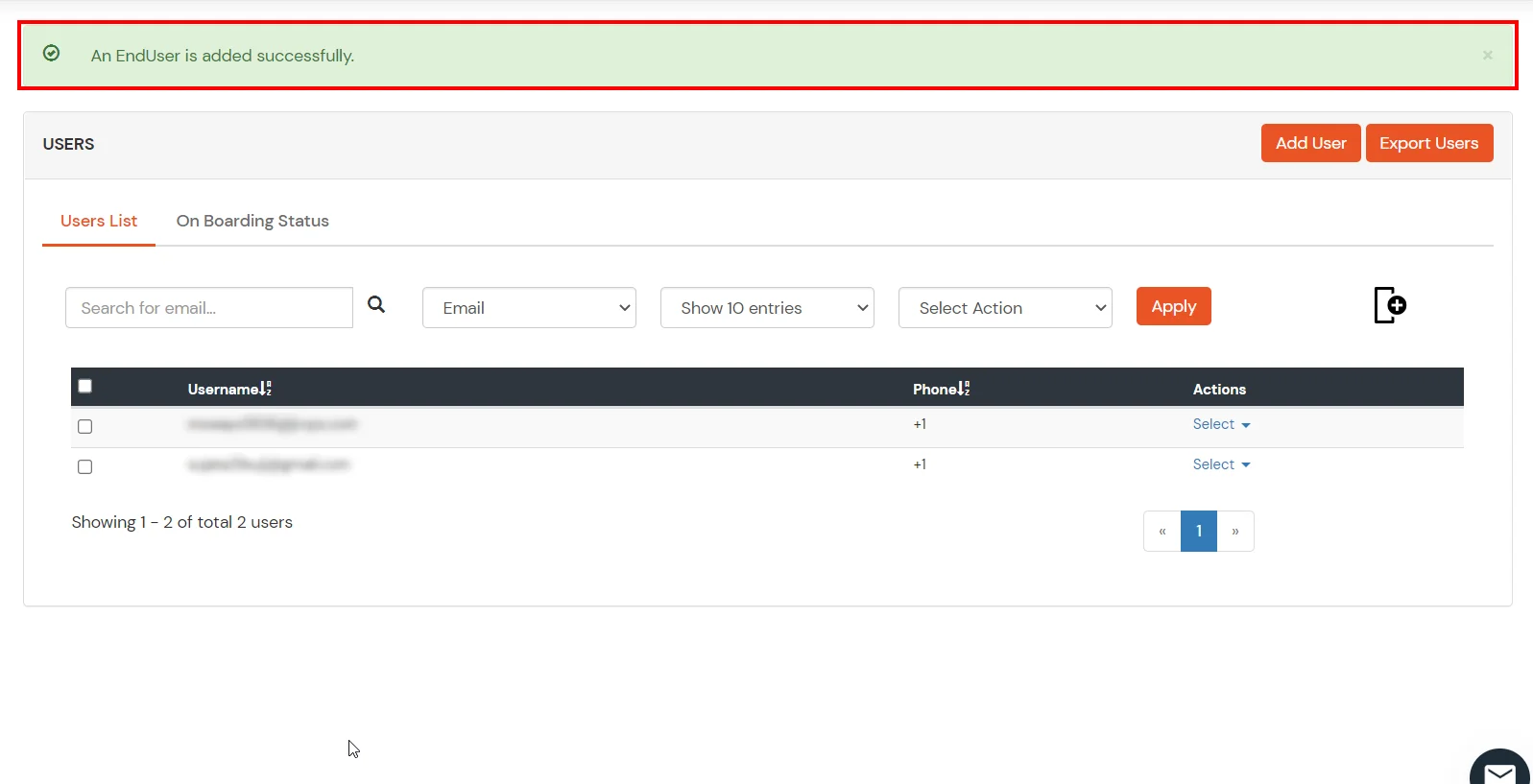
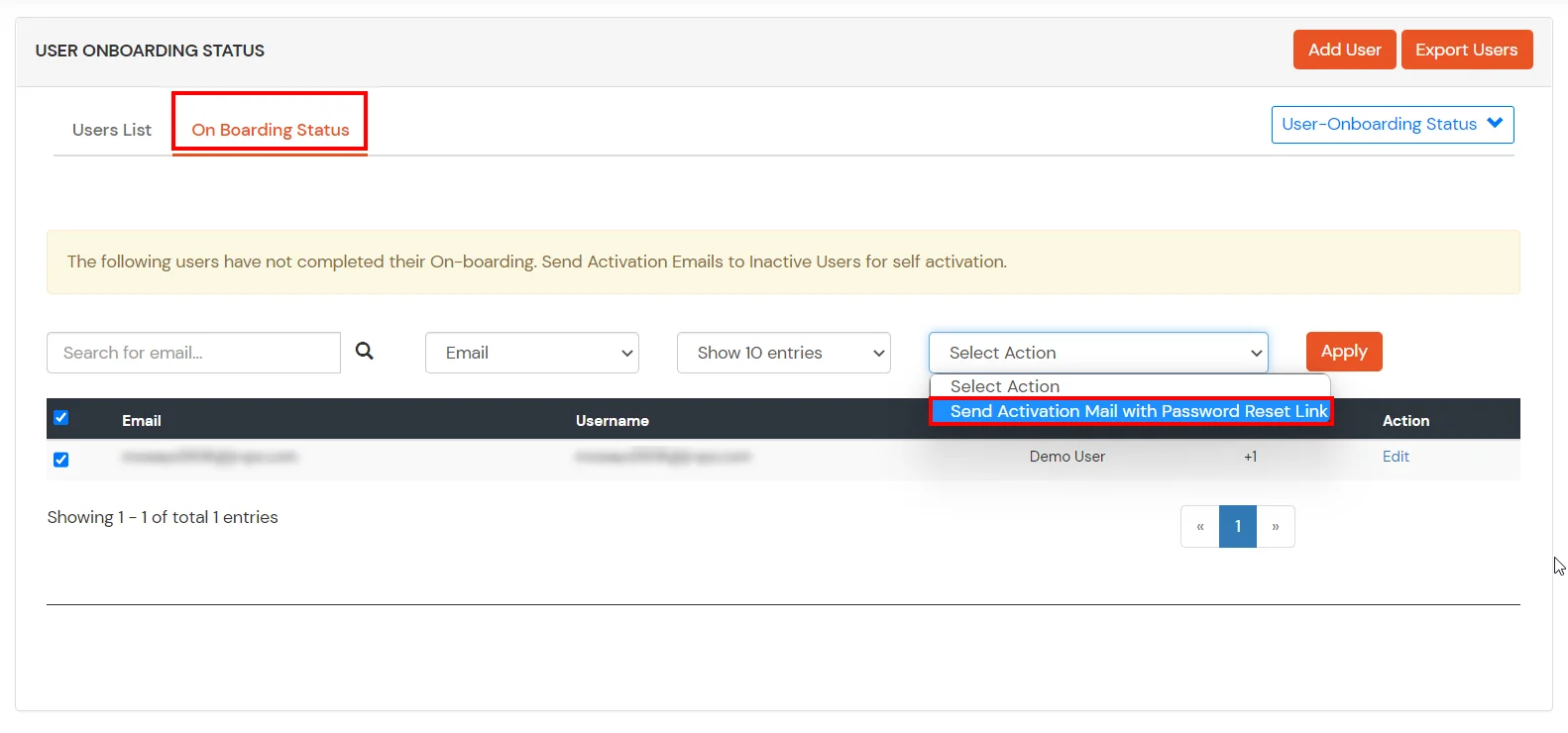
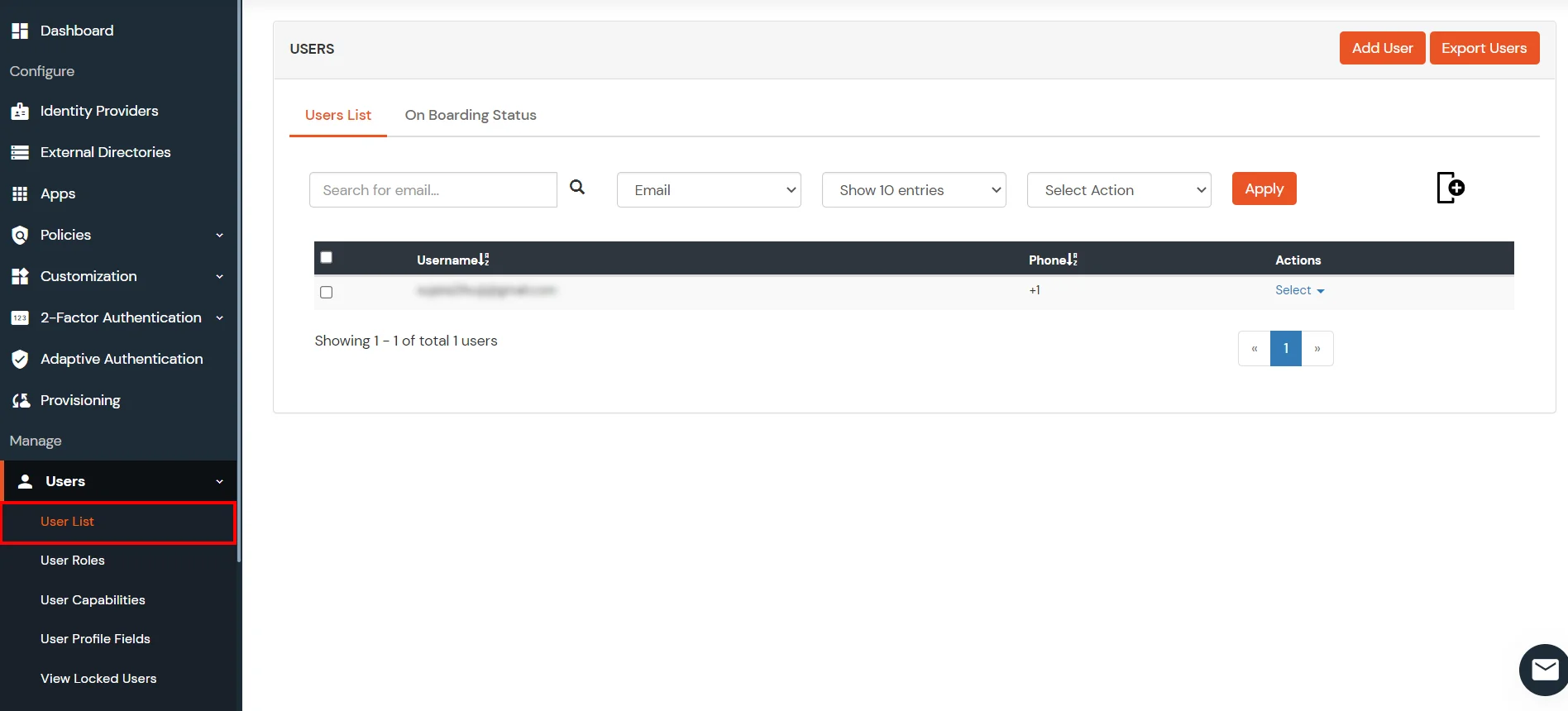
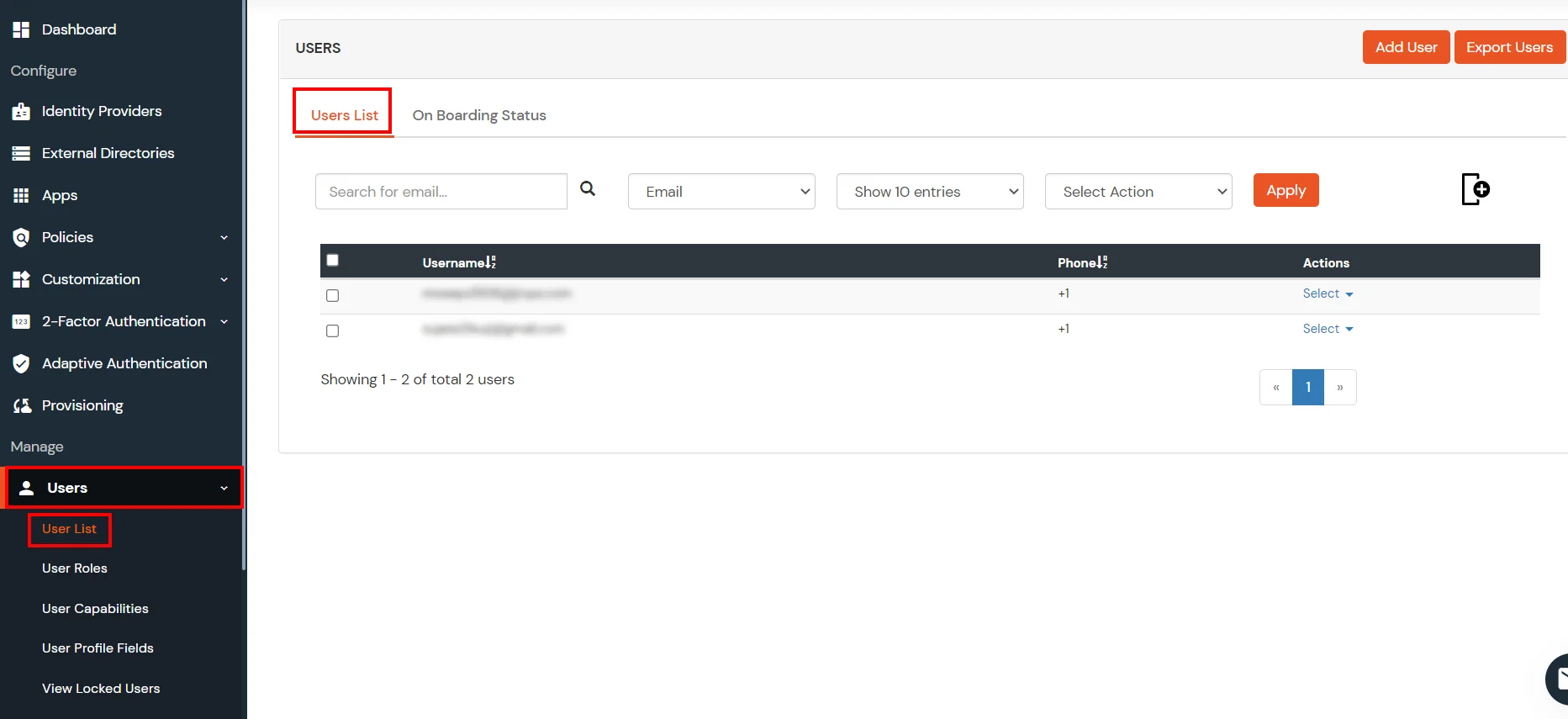
- You can view all the Users you have imports by selecting Users >> User List from Left Panel.
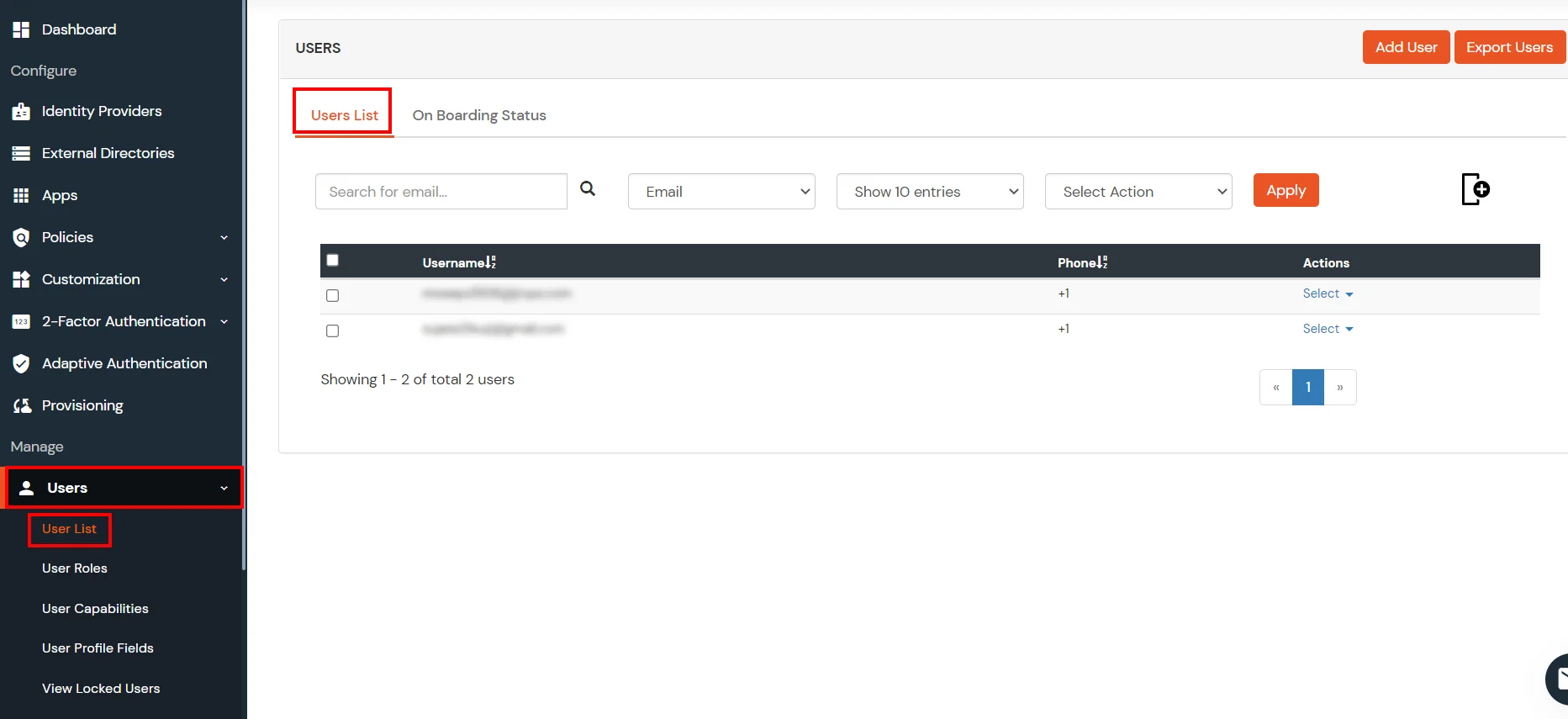
- All the imported users will be auto registered.
- These groups will be helpful in adding multiple 2FA policies on the applications.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
4. Test SSO Configuration
Using SP Initiated Login
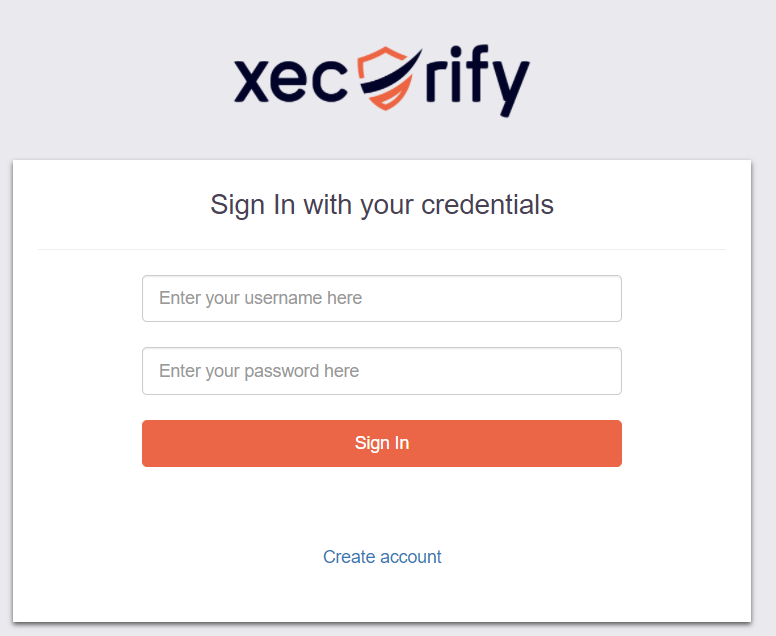
- Lets say you have configured miniOrange as your userstore.
- On accessing the Single sign-On URL as mentioned in the second step, you will be asked for miniOrange credentials.
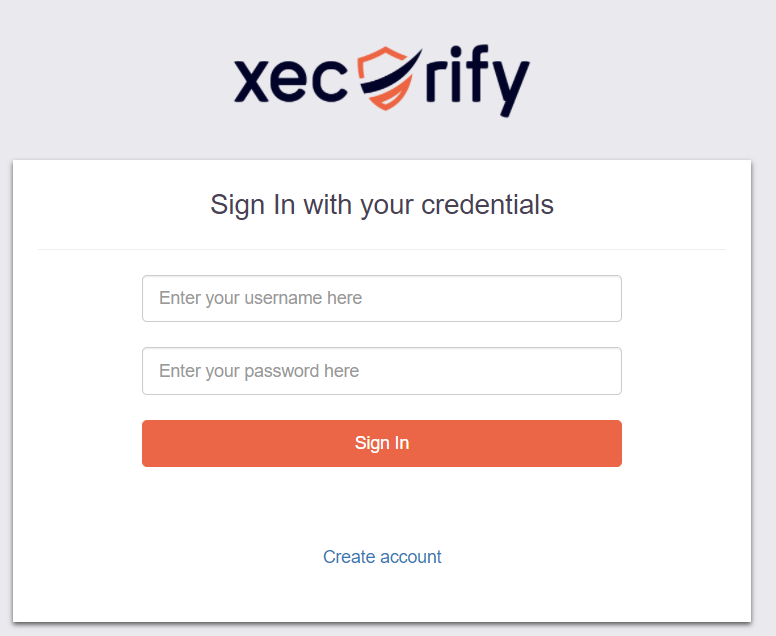
- On entering the valid credentials, you will be successfully logged into Ecwid.
Using IDP Initiated Login
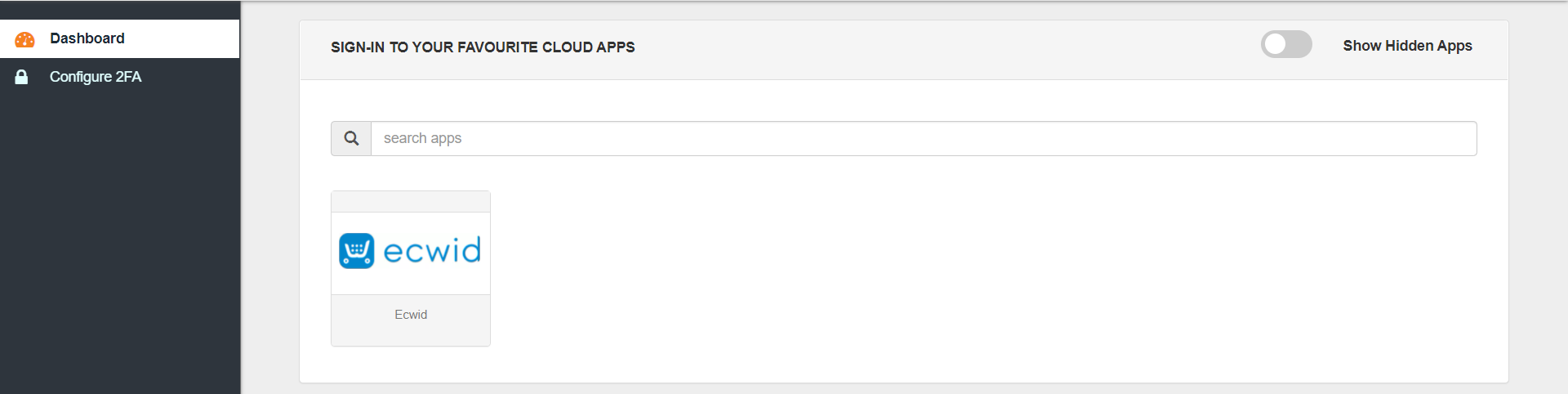
- Log into miniOrange IdP using your credentials.
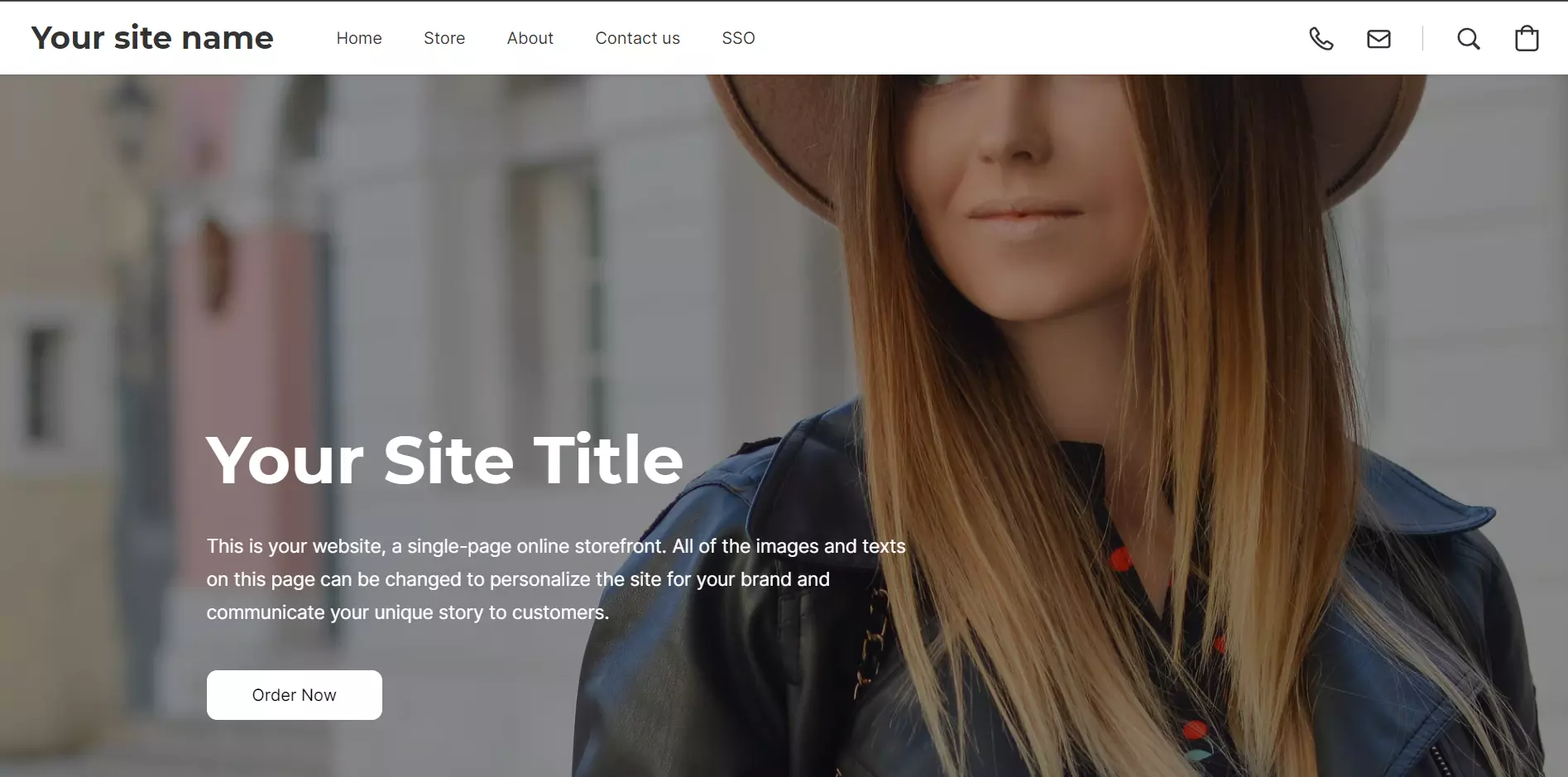
- On the End User-Dashboard, click on the Ecwid application configured, to test the SSO flow.
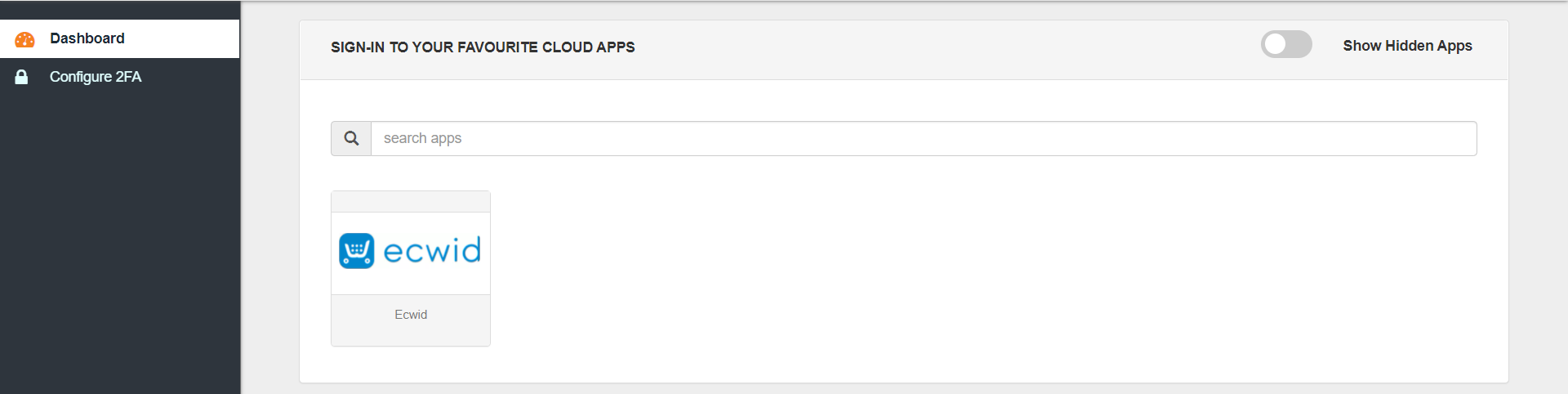
- You will be successfully logged into Ecwid.
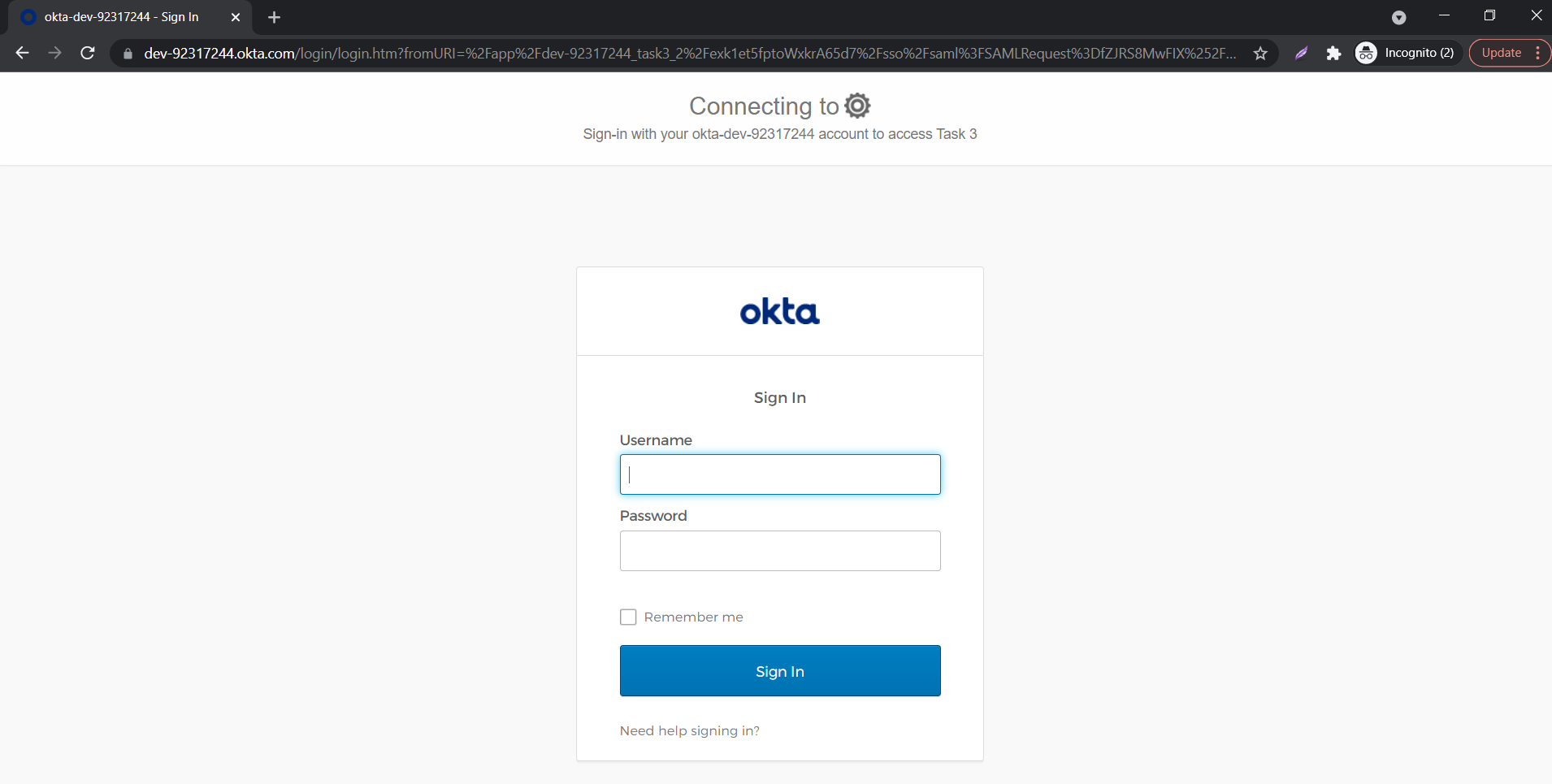
Using SP Initiated Login
- Lets say you have configured Okta as IDP.
- On accessing the Single sign-On URL as mentioned in the second step, you will be asked to enter your Okta credentials.
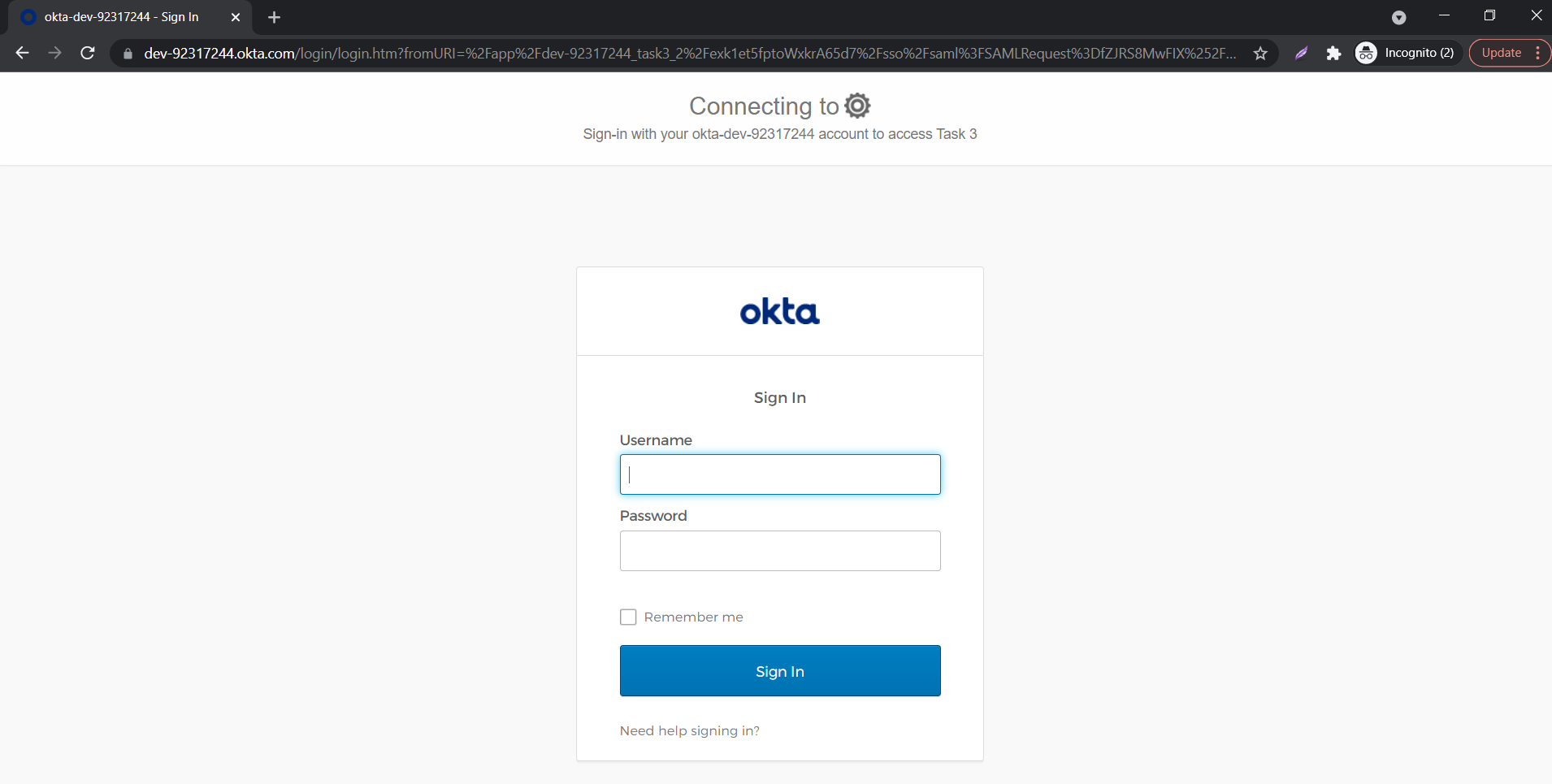
- On entering the valid credentials, you will be successfully logged into Ecwid.
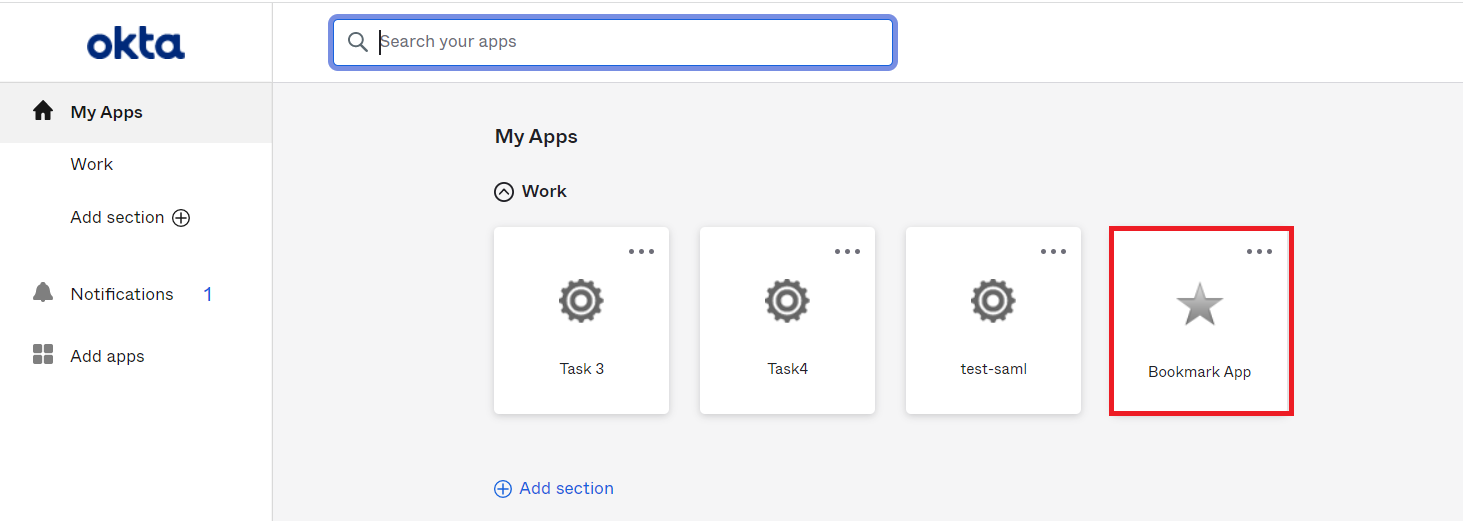
Using IDP Initiated Login
- Log into Okta using your credentials.
- Click on Admin to access the Admin Console, then click on Applications.
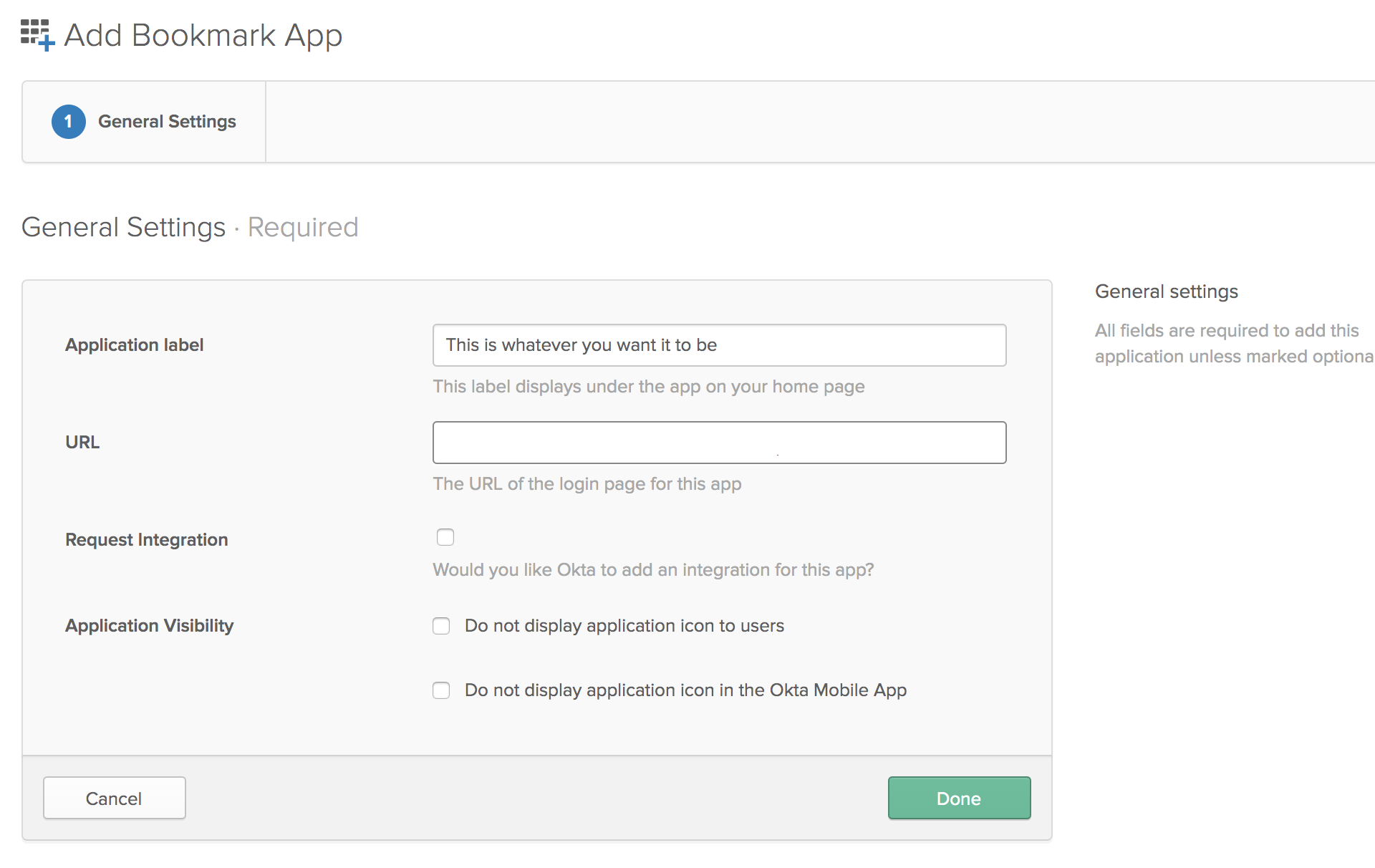
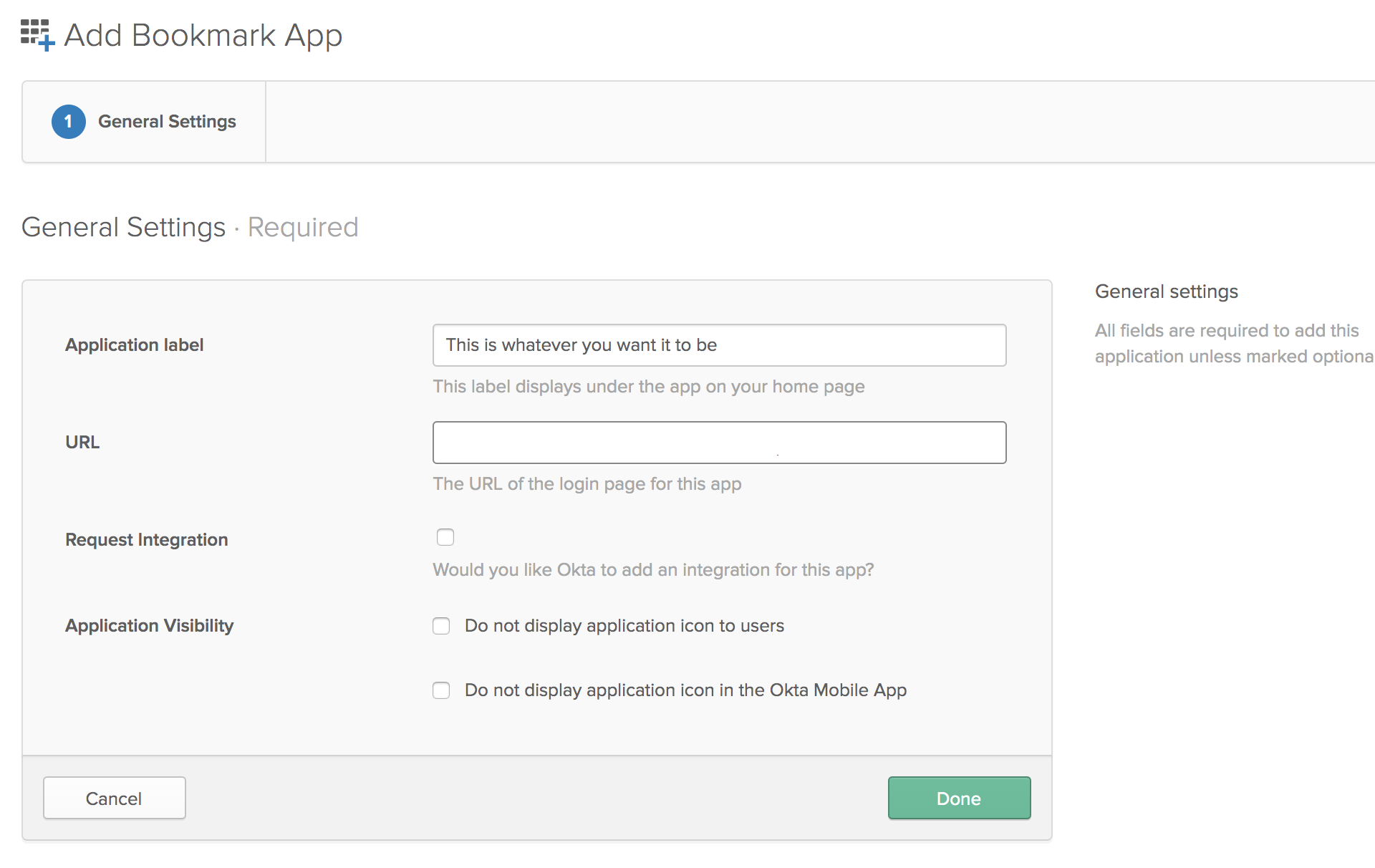
- Click on Add Application and search for "Bookmark App", and Click Add in the left pane.
- Choose an app name of your choice which will be the display name.
- In the URL section, enter the SSO URL that is given in the JWT app.
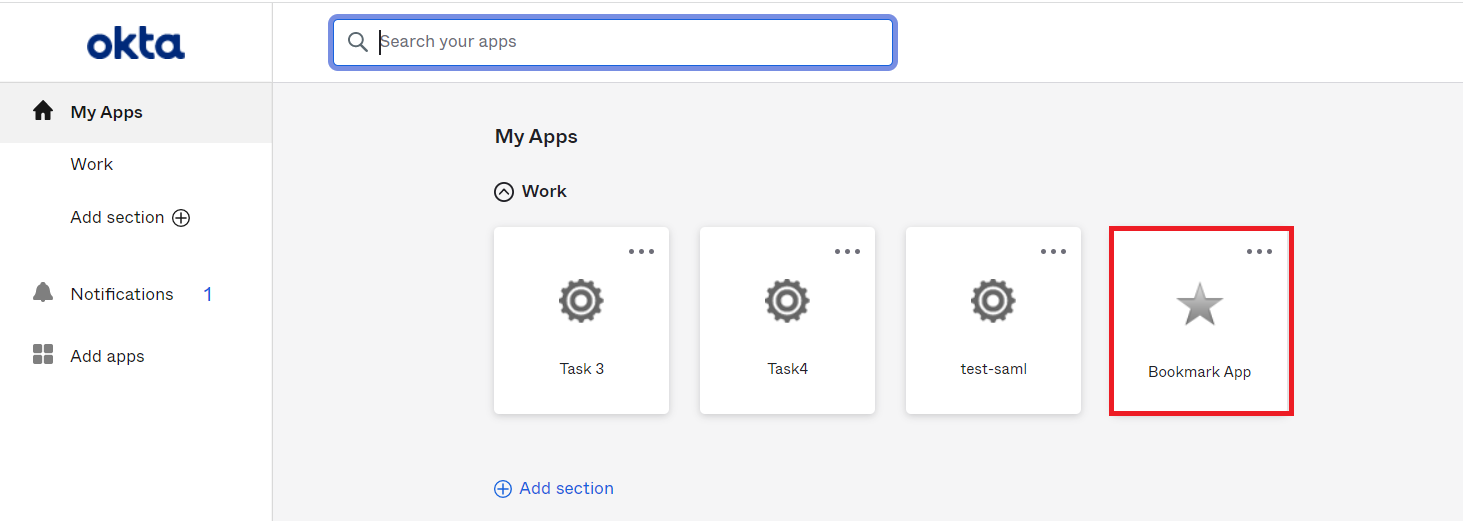
- Click on Save.
- On the End User-Dashboard, click on the Ecwid bookmark application configured, to test the SSO flow.
- You will be successfully logged into Ecwid.
External References